7 components of a network
advertisement

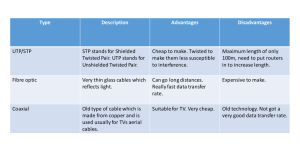
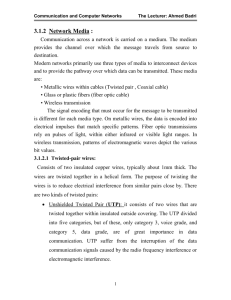
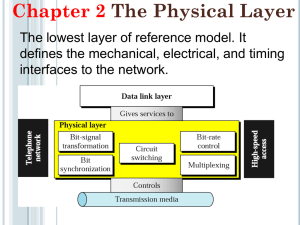
TYPES OF NETWORKS PROTOCOLS NETWORK CONFIGURATIONS /TOPOLOGIES TRANSMISSION MEDIA By B. Vialva Networks can be classified according to the geographical area they occupy. LAN – Local Area Network MAN - Metropolitan Area Network WAN – Wide Area Network Confined to a single building or site – the hardware and communications equipment is contained in one building or site. Ownership of the communications equipment – the organization actually owns all the communications equipment (such as wiring, etc.) that links the terminals. A metropolitan area network (MAN) covers a city or a region of a city. MANs have very high transfer speeds MANs support high-speed disaster recovery systems real-time transaction backup systems interconnections between corporate data centers and internet service providers, and government, business, medicine, and education high-speed interconnections. Almost exclusively fiber optic systems The biggest advantage is communication with other people and the biggest disadvantage would be security. MANs are very often a ring topology Hardware is spread over a wide geographical area – devices (computers, point of sale terminals, storage, etc.). The devices spread over multiple buildings and sites. Third party telecommunications equipment is used – hardware in a WAN is situated in many sites, which can be in different countries. Telephone radio and satellite communications are needed, which are supplied by a third party. The organization with the WAN has to rent these services from a telecommunications supplier. Internet – a huge group of networks joined together. Each of these networks consists of lots of smaller networks. The internet and the WWW is not the same thing. World Wide Web – is a means of accessing information contained on the internet. It is an information sharing model that is built on top of the internet. The www uses HTTP(hypertext transfer protocol), which is one of the languages used over the internet to transmit information. The www makes use of browser software used to access documents called web pages. INTRANET EXTRANET It is a private internal network which allows employees of an organization to access and share information and resources. It uses the same technology as that used by the internet for sending of messages across the network. The concepts of client and server are used for the computers in an intranet along with the same protocols (HTTP, FTP and e-mail) as used by the internet. The main feature of the intranet is that only employees of the organization are able to use it. NOTE: it is still possible for people on an intranet to access the internet; they are not confined to the intranet site. These are intranets opened to selected groups of users outside the company such as customers, suppliers, as well as employees of the organization. It is not accessible to the general public and this is ensured by the use of usernames and passwords. Because the people who need access to the information are not on the same site, data needs to be sent using third party telecommunication lines. Data can be sent via the internet or it can be sent using the more expensive private communication lines which offer more security and performance. If the internet is used for the sending of the data in an extranet, the following security measures have to be put in place: Gateways – is used to link together different types of networks. Firewalls- hardware and/or software that work in a network to prevent communication that is not allowed from one network to another. Encryption – coding data whilst it is being sent over a network so that only the true recipient is able to decode it. Should the data be intercepted by a hacker, then the data will be in a code that is totally meaningless. User authentication – having to supply a valid username with matching password. A set of standards or rules that allows the transmission of data between computers (or different devices) on a network. When I.T. devices are linked together they must be able to communicate. Even though the hardware or the software is not the same, the communications link between them have to be compatible, therefore modern computer networks set PROTOCOLS (rules) so that data sent from one computer can be understood by another computer. Different types of protocols: IP – Internet Protocol TCP – Transmission Control Protocol FTP – File Transfer Protocol HTTP – Hypertext Transfer Protocol Networks can be arranged in various ways depending on the number of computers and how they are going to be used. The way the network is arranged is called the TOPOLOGY. Bus/line Star Ring Have one long cable, known as the BACKBONE with everything else attached along it. Each connection point is called a NODE. Every computer along the line receives each signal sent. If there is a lot of traffic or a large number of computers, the communication can be slow. It is cheap since it does not use much cabling. If there is a break between the backbone and a computer then only that computer is affected. If there is a break in the backbone then the whole network will stop working. If there is a lot of traffic or a large number of computers, the communication can be slow. The computers are linked together by cables in a circle. The data only flows in one way around the network. it is suitable for a small number of computers (15). It is relatively cheap and fast. No file server needed. If one computer breaks down the network stops working Can become slow if there is a lot of traffic It is difficult to add or remove computers Each computer has its own separate connection to the file-server Faster than a bus network If one cable fails, it does not affect the other computers, meaning the network is more fault tolerant. The layout makes it easy to add or remove individual computers. Are more expensive because more cabling is required The material which forms the connection between the computers or devices in a network. E.g. air (in the case of wireless), metal wire, optical fiber. This can be wired or wireless. Wires add considerably to the cost of a network, especially the cost of installing them. The main forms of data transfer are: Metal wires Fiber optic cables Wireless Offer a high transmission speed Expensive to buy and install Can suffer from interference / data corruption There are three different types: Unshielded twisted pair: (telephone line) Shielded twisted pair (cable tv) Unshielded Twisted Pair (UTP) Ordinary telephone wire Cheapest thin wires are twisted to help cancel out interference but it still suffers from external EM interference, Thin wires mean easier installation, Only suitable for small networks. Shielded Twisted Pair (STP) Metal braid or sheathing that reduces interference which protects the data signals from outside interference/corruption, More expensive than unshielded twisted pair Harder to handle (thick, heavy) Greater transmission speeds than unshielded twisted pair Unshielded Twisted Pair cable is currently the most popular method of implementing an Ethernet LAN (Local area network). It is far easier to manipulate than coaxial cable The data being passed is encoded as pulses of light through a very thin glass fiber. Bundles of fibers are used to carry the data to and from the network. Speed- the data travels much faster, Small size – a hug amount of data can travel in a very small cable, Lack of electrical interference Cost – the devices needed to connect the cables and the cable itself are more expensive Can be bent around corners The data transfer medium is the air Uses radio waves Allows you to connect anywhere there is a radio signal. A region where internet can be accessed wirelessly using Wi-Fi. There are many public places where the internet can be accessed wirelessly using a person’s laptop or PDA. Wi-Fi – a trademark for the certification of products that meet certain standards for transmitting data over wireless networks. benefit of this particular type of network is the affordability of setting up a private network by tunnelling through the Internet practically free, hence being most costeffective but secure.