CRYPTOGRAPHY
advertisement
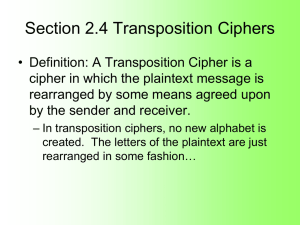
CRYPTOGRAPHY Lecture 2 Course structure • Format: Part lecture, part group activities • HW: – Daily assignments, some in-class and some take home. Keep these in a portfolio. – One 7-10 page essay on a related topic of your choice. Final project and presentation (you propose the topic and format) – Final grade will be determined by portfolio of work including the above. Expectations • Most work should be typed. Even work done in class should (usually) be typed and added to portfolio. • Attendance is mandatory. • Respectful behavior to your peers. • Your day is devoted to this class. General Rules • When decrypting or deciphering, all tools are fair. You may do anything legal to obtain the information you want. • However, you must disclose the methods you used. In unusual cases, you can keep some technique secret from your peers, with my approval, for a limited amount of time. Cryptography The aim is to hide the meaning of the message rather than its presence. This can be done by scrambling the letters around. Transposition Ciphers Make an anagram according to a straightforward system (404 BCE): The sender winds a piece of cloth or leather on the scytale and writes the message along the length of the scytale. Then unwinds the strip, which now appears to carry a list of meaningless letters. The messenger would take the leather strip (sometime wearing it as a belt) and when he arrives at his destination, the receiver winds the strip back on a scytale of the same diameter. Transposition Ciphers Rail fence transposition: Round and round the mulberry bush the monkey chased the weasel r u d n r u d h m l e r b s t e o k y h s d h w a e o n a d o n t e u b r y u h h m n e c a e t e e s l Becomes: rudnrudhmlerbsteokyhsdhwaeonadonteubryuhhmneca eteesl Simple Transposition • Simple Columnar Transposition • The key information is the number k of columns. • Encipherment: Plaintext is written in lines k letters wide and then transcribed column by column left to right to produce ciphertext. This and the next few slides copied from: http://www.rhodes.edu/mathcs/faculty/barr/Math103CUSummer04/TranspositionSlides.pdf Simple Transposition: example “April come she will When streams are ripe and swelled with rain” Convert to a transposition cipher using k=10 Simple Transposition: example 1234567890 APRILCOMES HEWILLWHEN STREAMSARE RIPEANDSWE LLEDWITHRA IN AHSRL PEIIE NIOWS WRSNE IPETI LNRWR EDLLA AWCLM DTMHA SHEER EA Simple Transposition • Decipherment: If n is the length of the ciphertext,it is written column by column left to right down in a k ×(n DIV k )rectangular array with a “tail ” of length n MOD k as shown. Transcribing row by row produces plaintext. M E S S A G E The message is n=37 A N D M O R E letters long. It is set up A N D S T I L in k=7 columns. So there L M O R E U N are T I L I T E N 37 DIV 7 = 5 rows and the tail is D S 37 mod 7 = 2 HW#2a 1. Given the message NNDATEAOIIOTINHRNNODTHSGAECSUIHEMENI ECSTIWORSGAISYNOROINNETGREUNODNUILDS CRCTP with k=8: Decipher it. HW#2a 2. Encipher 3 messages with with some value of k. Now the groups swap messages and are given the value of k. Decipher the messages. 3. Encipher a message with a value of k between 2 and 10 and swap ciphers. Now swap messages, without sharing the value of k. Now decipher the message . . . Transposition Ciphers A double transposition offers more security: rudnrudhmlerbsteokyhsdhwaeonadonteubryuhhmnecaeteesl Becomes unuhlrsekhdwendnebyhmeatelrdrdmebtoyshaoaoturuhncees Column Transposition A G A M E M N O N 1 4 2 5 3 6 7 9 8 key phrase convert to numbers ABCDEFGHIJKLMNOPQRSTUVWXYZ AEGMNO delete the letters not used 134579 assign them numbers 2 68 according to how they appear Example from http://hem.passagen.se/tan01/transpo.html Column Transposition A 1 s r e r G 4 e e a s A 2 n d d j M 5 d c q * E 3 a a u * M 6 r r a * N 7 m t r * O 9 o o t * N 8 u h e * key phrase convert to numbers The code is then Srer-nddj-aau-eeas-dcq-rra-mtr-uhe-oot Double Column Transposition M 5 s j s m o Y 7 r a d t t C 2 e a c r E 3 r u q u N 6 n e r h A 1 d e r e E 4 d a a o key phrase convert to numbers The code is then DEREE ACRRU QUDAA OSJSM ONERH RADTT Transposition Grille Example from http://hem.passagen.se/tan01/transpo.html Transposition Grille We need more machine gun ammunition fast xx Transposition Grille Transposition How do you get back to where you started? Reverse the process. Secure transmission Steganography cryptography Transposition Substitution HW #2b • Use each of the transposition ciphers we talked about today to encode your own messages. Now swap them and (without sharing the key, or even the method of encryption) try to decipher them. http://math.ucsd.edu/~crypto/java/EARLYCIPHERS/RectTran.html Don’t feel bad if you can’t decipher. It is hard, that’s the point! • Look online for tools to help decipher transposition cipher and use them.