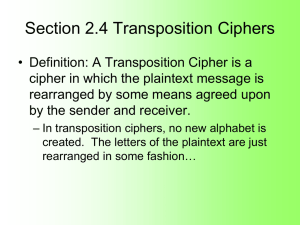
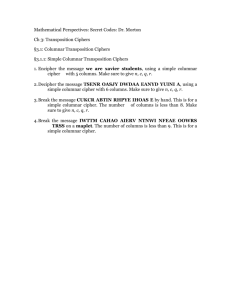
Transposition Ciphers
advertisement
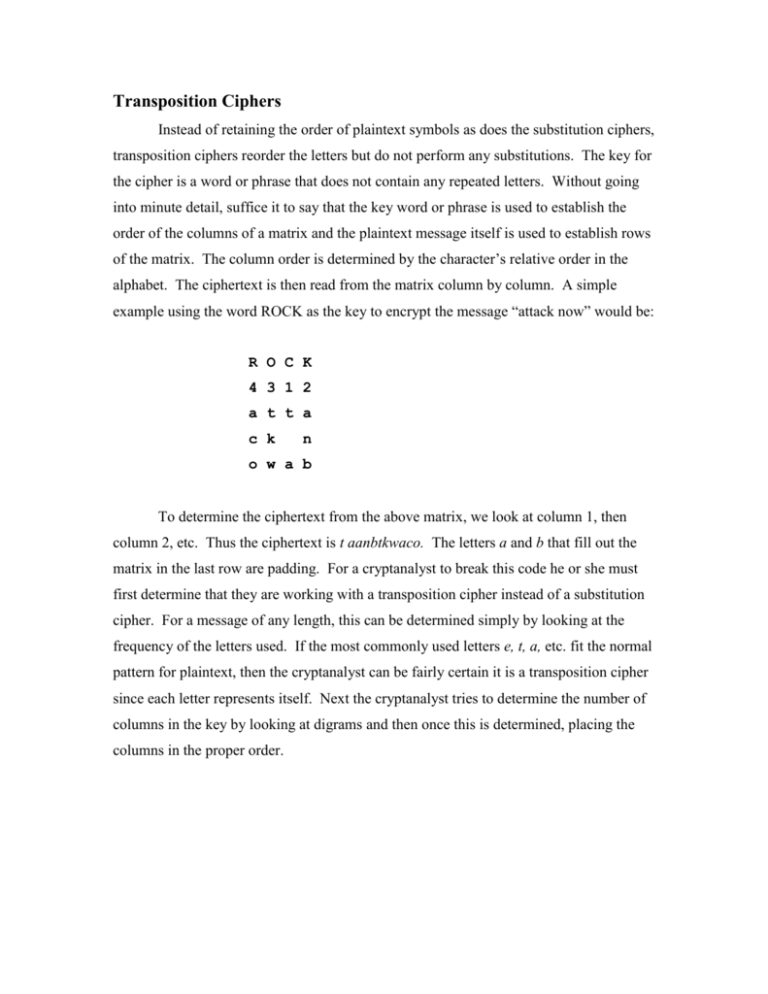
Transposition Ciphers Instead of retaining the order of plaintext symbols as does the substitution ciphers, transposition ciphers reorder the letters but do not perform any substitutions. The key for the cipher is a word or phrase that does not contain any repeated letters. Without going into minute detail, suffice it to say that the key word or phrase is used to establish the order of the columns of a matrix and the plaintext message itself is used to establish rows of the matrix. The column order is determined by the character’s relative order in the alphabet. The ciphertext is then read from the matrix column by column. A simple example using the word ROCK as the key to encrypt the message “attack now” would be: R O C K 4 3 1 2 a t t a c k n o w a b To determine the ciphertext from the above matrix, we look at column 1, then column 2, etc. Thus the ciphertext is t aanbtkwaco. The letters a and b that fill out the matrix in the last row are padding. For a cryptanalyst to break this code he or she must first determine that they are working with a transposition cipher instead of a substitution cipher. For a message of any length, this can be determined simply by looking at the frequency of the letters used. If the most commonly used letters e, t, a, etc. fit the normal pattern for plaintext, then the cryptanalyst can be fairly certain it is a transposition cipher since each letter represents itself. Next the cryptanalyst tries to determine the number of columns in the key by looking at digrams and then once this is determined, placing the columns in the proper order.