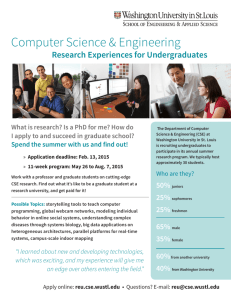
software - Department of Computer Science and Engineering
advertisement

CSE CHAMPS Initiative Constructing High-Assurance Mobile and Pervasive Systems Department of Computer Science and Engineering Michigan State University Computer Science and Engineering, July 21, 2004 Goal • Identify and nurture an “umbrella” research theme for CSE Department that: – Leverages and creates synergy among current and emerging CSE research strengths – Sets CSE apart from other computer science programs (e.g., Georgia Tech model) – Is important to advances in many disciplines across campus – Helps MSU play a unique role in information technology and its applications in science, engineering, business, … Computer Science and Engineering, July 21, 2004 CSE Research • Established strength areas – Networking and pervasive computing – Software engineering and formal methods – Intelligent systems • Emerging strength areas – – – – Digital Evolution Computational Linguistics Cybersecurity Bioinformatics Computer Science and Engineering, July 21, 2004 Networking and Pervasive Computing Computer Science and Engineering, July 21, 2004 Networking Research • Internet challenges: Real-time interaction, wireless edge, security and privacy • Internet Tele-operation (Mutka) E. Lansing Japan – Real-time robot control/feedback • Anonymous Communication (Shapiro) – Internet privacy, Internet commerce • Overlay Networks (Xiao, McKinley) – Virus early warning systems, P2P apps • Secure Mobile Computing (Mutka, McKinley) • Funding: NIH, NSF, ONR • Discovering party Collaborators: Dept. of Surgery, Telecomm, ECE, ME, Chemistry/BioChemistry, Mathematics, Ohio State, William and Mary, U. Helsinki, Siemens Computer Science and Engineering, July 21, 2004 Service provider Trust – Battlefield computing, emergency services Pervasive Computing • Removing traditional boundaries for how, where and when humans and computers interact • Augmented reality (Owen) • Autonomic computing (McKinley, Kulkarni, Cheng, Dillon, Stirewalt) • Example: Critical Infrastructure Protection – Adaptive auditing to prevent cascading failures – Detect and respond to security threats • Funding: ONR, NSF, Microsoft • Collaborations: Siemens, Cisco, Lucent, MIND Lab, Dept. Advertising • Emerging collaborations: Business School, Entomology, Cyclotron Computer Science and Engineering, July 21, 2004 Sensor Networks • A special case of pervasive computing • Inexpensive MEMS devices deployed in large quantity to remote, hazardous, or denied areas • Self-organizing control and data gathering • Topics: – Self-configuring networks (Kulkarni, Mutka) – Energy management (McKinley) – Software adaptation (Kulkarni) • Example: DARPA NEST project • Applications: – Battlefield, homeland security – Ecosystem monitoring – Smart structures • Collaborators: Entomology, Ohio State, U. Iowa Computer Science and Engineering, July 21, 2004 Software Engineering and Formal Methods Computer Science and Engineering, July 21, 2004 SE for High Assurance: Systematic development of software that requires critical properties –Safety; Security; Real-time; Fault Tolerance • Related Areas: – – – – – – Code Generation Automated Verification Component-Based Development Embedded Systems Fault Tolerance Security (Stirewalt, Cheng, Chung) (Dillon, Stirewalt, Cheng) (Stirewalt, Dillon, Cheng) (Cheng, Kulkarni) (Kulkarni, Cheng) (Wojcik, Dyksen, Cheng, Chung, Enbody, Jain, McKinley, Mutka, Shapiro, Stirewalt, Xiao) • Funding sources: – • NSF, DARPA, ONR, Automotive Industries, Siemens, APP&R Collaborators: – – Telecomm, Business School, Medical School, Criminal Justice, Motorola, Detroit Diesel, NASA/JPL, Texas Instruments, Boeing Computer Science and Engineering, July 21, 2004 Software Engineering for High Assurance SW Adaptive Cruise Control Automotive Software ElectronicallyControlled Steering Transportation Systems (Signaling/Automation) Patient Monitoring System Manufacturing Software Computer Science and Engineering, July 21, 2004 Temptations and Challenges for Software Development Ideas for Software • Ad hoc techniques • Difficult to gain assurance • Acceptable for some application domains ``Design at the keyboard’’ Code ``Testing’’ ``Hacking’’ ``Debugging’’ •High Assurance systems: – Errors are “expensive” – Demand rigorous SE – Must be formally verifiable – Automation Computer Science and Engineering, July 21, 2004 Reality Check… Question: Would you ride the airplane that uses your software? Boeing 777 Fly-by-wire Computer Science and Engineering, July 21, 2004 Bridge the Gap Between Informal and Formal Methods Informal specifications, • graphical models, • easy for humans to formulate, •may be inconsistent and incomplete. Apply Formalization Framework Object-Oriented “Blueprints” Formal Representations Objective: • formal (mathematical-based) specifications • executable code • that can be verified for correctness and completeness Benefits: •Automated Analysis •Consistency, completeness •Rapid Prototyping •Behavior Simulation • Design Transformations •Test Case generation Intelligent Systems Computer Science and Engineering, July 21, 2004 Intelligent Systems “Design and engineer systems that exhibit intelligence” Autonomous agents, human computer interaction, knowledge discovery • Natural Language Understanding (Joyce Chai*, John Hale* +) • Robotics (John Weng) • Machine Learning (Rong Jin*, John Weng) • Computer Vision (George Stockman, Anil Jain, Aude Oliva*# , John Weng) • Pattern Recognition (Anil Jain) • Data Mining (Pang-Ning Tan* and Anil Jain) • Information Retrieval (Joyce Chai* and Rong Jin*) * Hired in the last two years # Dept. of Psychology + Dept. of Linguistics Computer Science and Engineering, July 21, 2004 Research Projects • Biometric Recognition (NSF, DHS) • Question answering system for multimedia information (ARDA) • Handwritten document understanding (Microsoft) • Data clustering (ONR) • Smart airbags (Eaton) • Developmental learning and humanoid robots (DARPA, SAIC, Zyvex) • Office presence (status of human presence in office) (Microsoft) • Multimodal conversational system (NSF) • 3D sensing, modeling and movement (Army) • Facial expression analysis and HCI (NSF) Computer Science and Engineering, July 21, 2004 Biometric Recognition • Biometrics: A measurable, physical characteristic or personal behavioral trait used to recognize the identity, or verify the claimed identity, of an enrollee • Biometric recognition: Personal recognition based on “who you are or what you do” as opposed to “what you know” (password) or “what you have” (ID card) • Advantages: Eliminates fraud; enhances security; cannot be easily transferred, forgotten, lost or copied; eliminates repudiation claims; user convenience • Applications: Cybersecurity, border control, driver license, cellular phones, ATM Computer Science and Engineering, July 21, 2004 Developmental Learning • Autonomous Mental development; NSF/DARPA Workshop on Development and Learning, MSU 2000 (Science, Jan. 2001) • Designed and constructed Dav: the only mobile and untethered humanoid robot in US • Press reports by UPI, BBC, KRN, 30 US newspapers, Technology Review. • Created ICDL conference series: 2nd ICDL (MIT’02), 3rd ICDL (San Diego’04), 4th ICDL (Japan’05) • Created a new journal: Int’l J. of Humanoid Robotics • Created IEEE NNS AMD Technical Committee Computer Science and Engineering, July 21, 2004 Face Capture HMD* HMD wearer will see faces of others on the glass OR projected on the wall, etc. Small mirrors and cameras allow user’s facial expressions to be communicated to remote colleagues. * designed by Biocca (MSU) and Rolland (UCF) Computer Science and Engineering, July 21, 2004 Emerging Interdisciplinary Research Bioinformatics (Pramanik and Torng, in conjunction with Chemistry, Biochemistry, and Microbial Ecology) Computational Linguistics (Chai, Jin, and Hale, in conjunction with Linguistics and Psychology) Cyber-Security (Dyksen, Enbody, Tan, and Wojcik, in conjunction with Criminal Justice, Telecommunications, Business, the Law School, and the Medical School) Digital Evolution (Ofria, Punch, and Torng, in conjunction with Biochemistry, Electrical and Computer Engineering, Fisheries and Wildlife, Microbiology and Molecular Genetics, Microbial Ecology, Zoology, Plant Biology, Philosophy) And others: Network Economics (Shapiro), Augmented Reality (Owen), Human-Computer Interaction (Chai) Computer Science and Engineering, July 21, 2004 Emerging Cyberinfrastructure Secure Information Systems Digital Supply Chain • • • • • • Remote Safety-critical Real-time All the above Privacy Adaptable NetworkCentric Battlefield Ecosystem Monitoring Disaster Relief Homeland Security Computer Science and Engineering, July 21, 2004 Cyberinfrastructure Research • First Generation (proof-of-concept) – – – – Driven by applications in science and engineering Advanced sensor hardware Efficient systems software, network protocols Understanding issues, brittle prototypes • Second Generation (sustainable infrastructure) – – – – – – Driven by applications in science and engineering Advanced sensor hardware Efficient systems software, network protocols High-assurance (generated) adaptable software and protocols Intelligent systems that can learn how to respond and adapt Designing and building robust, self-healing (autonomic) systems for deployment Computer Science and Engineering, July 21, 2004 CHAMPS • Constructing High-Assurance Mobile and Pervasive Systems – Research to enable a sustainable, pervasive cyberinfrastructure – Key ingredients: robust, self-managing and self-healing software • Research theme that draws upon combination of CSE strengths – – – – • Adaptive networking, augmented reality, secure mobile computing, sensor networks Rigorous software engineering, autonomic systems, fault tolerance Biometrics, embodied intelligence, autonomous robots, data mining Bioinformatics, human computer interaction, computational linguistics Wide range of applications and collaborations – Agriculture and ecosystem monitoring, remote scientific experimentation – Tele-medicine, digital supply chain, secure/robust information systems – Battlefield and surveillance, infrastructure protection, homeland security • An area where CSE (and via interdisciplinary collaborations, MSU) is poised for national leadership. Computer Science and Engineering, July 21, 2004