Computer Science and Engineering
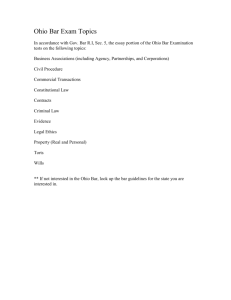
advertisement

Research in Networking Dong Xuan Dept. of Computer Science and Engineering The Ohio State University The Ohio State University Dong Xuan: CSE885 on 11/07/07 1 Outline Group Research Overview Performance - Optimal Deployment in Wireless Sensor Networks Security - Flow Marking in the Internet The Ohio State University Dong Xuan: CSE885 on 11/07/07 2 Group Members Student members: Xiaole Bai, Adam Champion, Sriram Chellappan (to be assistant professor in Univ. of Missouri at Rolla), Boxuan Gu, Wenjun Gu, Thang Le, Zhimin Yang Former members: Sandeep Reddy (M.S., 2004, Microsoft), Lamonte Glove (M.S., 2004, Avaya) and Kurt Schosek (M.S., 2005), Xun Wang (Ph.D, 2007, CISCO) Faculty member: Dong Xuan The Ohio State University Dong Xuan: CSE885 on 11/07/07 3 Research Interests Real-time computing and communications Deterministic and statistic QoS guarantees [ICDCS00, INFOCOM01, RTSS01, ToN04] Voice over IP [RTAS02, TPDS05] Performance Topology control [MOBIHOC06, INFOCOM08] Mobility control [TPDS06, TMC07] Security Internet security • Overlay security [ICDCS04, TPDS06] • Anonymous communications [IPDPS05, SP07, INFOCOM08_mini] • Worm/Malware defense[SECURECOM06, 07, ACSAC06] Wireless network security [IWQoS06, TPDS06] The Ohio State University Dong Xuan: CSE885 on 11/07/07 4 Research Grants ARO: “Defending against Physical Attacks in Wireless Sensor Networks”, (PI, 2007-2010) NSF: “Efficient Resource Over-Provisioning for Network Systems and Services”, (PI, CAREER award, 2005-2010) NSF: “Overlay Network Support to Remote Visualization on Time-Varying Data”, (PI, 20032006) SBC/Ameritech: “Providing Statistic Real-time Guarantees to Multimedia Teleconferences”, (PI, 2002-2003) The Ohio State University Dong Xuan: CSE885 on 11/07/07 5 Performance: Optimal Deployment Patterns in WSNs Xiaole Bai, Santosh Kumar, Dong Xuan, Ziqiu Yun and Ten H. Lai, Deploying Wireless Sensors to Achieve Both Coverage and Connectivity, in ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc), 2006 Xiaole Bai, Ziqiu Yun, Dong Xuan, Ten H. Lai and Weijia Jia, Deploying Four-Connectivity And Full-Coverage Wireless Sensor Networks, in IEEE International Conference on Computer Communications (INFOCOM), 2008 The Ohio State University Dong Xuan: CSE885 on 11/07/07 6 Problem Definition What is the optimal number of sensors needed to achieve p-coverage and q-connectivity in WSNs? An important problem in WSNs: Connectivity is for information transmission and coverage is for information collection Avoid ad hoc deployment to save cost To help design topology control algorithms and protocols other practical benefits Ohio State University TheThe Ohio State University Dong Xuan: CSE885 on 11/07/07 7 p-Coverage and q-Connectivity p-coverage: every point in the plane is covered by at least p different sensors q-connectivity: there are at least q disjoint paths between any two sensors Node C rc rs Node A The Ohio State University Node D For example, nodes A, B, C and D are two connected Node B Dong Xuan: CSE885 on 11/07/07 8 Relationship between rs and rc rc 3rs In reality, there are various values of rc / rs Most existing work is focused on The communication range of the Extreme Scale Mote (XSM) platform is 30 m and the sensing range of the acoustics sensor is 55 m Sometimes even when it is claimed for a sensor to have rc 3rs , it may not hold in practice because the reliable communication range is often 60-80% of the claimed value The Ohio State University Dong Xuan: CSE885 on 11/07/07 9 A Big Picture Research on Asymptotically Optimal Number of Nodes MobiHoc06 INFOCOM 08 [1] R. Kershner. The number of circles covering a set. American Journal of Mathematics, 61:665–671, 1939, reproved by Zhang and Hou recently. [2] R. Iyengar, K. Kar, and S. Banerjee. Low-coordination topologies for redundancy in sensor networks. MobiHoc2005. The Ohio State University Dong Xuan: CSE885 on 11/07/07 10 Known Results: Triangle Pattern [1] rc 3rs d2 d1 d1 3rs d2 3 rs 2 Notice it actually achieves 1-coverage and 6-connectivity The Ohio State University Dong Xuan: CSE885 on 11/07/07 11 Our Optimal Pattern for 1-Connectivity Place enough disks between the strips to connect them See the paper for a precise expression The number is disks needed is negligible asymptotically Note : it may be not the only possible deployment pattern A d2 d1 d1 min rc , 3rs The Ohio State University d 2 rs r 2 s 2 4 Dong Xuan: CSE885 on 11/07/07 12 Our Optimal Pattern for 2-Connectivity Connect the neighboring horizontal strips at its two ends A Note : it may be not the only possible deployment pattern d2 d1 d1 min rc , 3rs The Ohio State University d 2 rs r 2 s 2 4 Dong Xuan: CSE885 on 11/07/07 13 Our Optimal Pattern for 4-Connectivity rc / rs 2 A Square pattern Note : it may be not the only possible deployment pattern d2 d1 The Ohio State University d1 d 2 rc Dong Xuan: CSE885 on 11/07/07 14 Our Optimal Pattern for 4-Connectivity 2 rc / rs A Diamond pattern Note : it may be not the only possible deployment pattern d2 d1 d1 min rc , 3rs The Ohio State University d 2 d1sin( 2 arcsin rc / 2rs ) Dong Xuan: CSE885 on 11/07/07 15 Workflow of optimality proof (1) Step 1 We lay out the theoretical foundation of the optimality proof: for any collection of the Voronoi polygons forming a tessellation, the average edge number of them is not larger than six asymptotically. • It is built on the well known Euler formula. Step 2 We show that any collection of Voronoi polygons generated in any deployment can be transformed into the same number of Voronoi polygons generated in a regular deployment while full coverage and desired connectivity can still be achieved. • The proof is based on the technique of pattern transformation and the theoretical foundation obtained in Step 1. The Ohio State University Dong Xuan: CSE885 on 11/07/07 16 Workflow of optimality proof (2) Step 3 We prove the number of Voronoi polygons from any regular deployment has a lower bound. Step 4 We show that the number of Voronoi polygons used in the patterns we proposed is exactly the lower bound value. Hence the patterns we proposed are the optimal in all regular deployment patterns. • Based on the conclusion obtained in Step 2, the patterns we proposed are also the optimal among all the deployment patterns. The Ohio State University Dong Xuan: CSE885 on 11/07/07 17 Future Work Research on Asymptotically Optimal Number of Nodes The Ohio State University Dong Xuan: CSE885 on 11/07/07 18 Security: Flow Marking Techniques in the Internet Security Wei Yu, Xinwen Fu, Steve Graham, Dong Xuan and Wei Zhao, DSSS-Based Flow Marking Technique for Invisible Traceback, in Proc. of IEEE Symposium on Security and Privacy (Oakland), May 2007, pp18-32 Xun Wang, Wei Yu, Xinwen Fu, Dong Xuan and Wei Zhao, iLOC: An invisible LOCalization Attack to Internet Threat Monitoring System, accepted to appear in the mini-conference conjunction with IEEE International Conference on Computer Communications (INFOCOM), April 2008. The Ohio State University Dong Xuan: CSE885 on 11/07/07 19 Invisible Traceback in the Internet Internet has brought convenience to our everyday lives However, it has also become a breeding ground for a variety of crimes Network forensics has become part of legal surveillance We study flow marking for a fundamental network-based forensic technique, traceback The Ohio State University Dong Xuan: CSE885 on 11/07/07 20 Problem Definition Sender Network Receiver Suspect Sender is sending traffic through encrypted and anonymous channel, how can Investigators trace who is the receiver? The Ohio State University Dong Xuan: CSE885 on 11/07/07 21 Traffic Confirmation by Flow Marking Investigators want to know if Sender and Receiver are communicating Sender Anonymous Channel Interferer Investigator HQ Receiver Sniffer The investigators know that Sender communicates with Receiver The Ohio State University Dong Xuan: CSE885 on 11/07/07 22 Issues in Flow Marking Traceback accuracy Periodic pattern ok? Traceback secrecy Traceback without conscience of suspects DSSS-based technique for accuracy and secrecy in traceback! The Ohio State University Dong Xuan: CSE885 on 11/07/07 23 Basic Direct Sequence Spread Spectrum (DSSS) A pseudo-noise code is used for spreading a signal and despreading the spread signal Interferer Original Signal dt Sniffer rb tb ct PN Code Spreading The Ohio State University noisy channel dr Recovered Signal cr PN Code Despreading Dong Xuan: CSE885 on 11/07/07 24 Example – Spreading and Despreading Signal dt: 1 -1 DSSS code ct: 1 1 1 -1 1 -1 -1 Spread signal tb=dt.ct=1 1 1 -1 1 -1 -1 -1 -1 -1 +1 -1 1 1 One symbol is “represented” by 7 chips PN code is random and not visible in time and frequency domains Despreading is the reverse process of spreading +1 dt t -1 tb Tc (chip) t +1 ct t -1 NcTc The Ohio State University Dong Xuan: CSE885 on 11/07/07 25 Mark Generation by Interferer 1. Choose a random signal Original Signal dt ct 2. Obtain the spread signal PN Code tb 3. Modulate a target traffic flow by appropriate interference Chip +1: without interference Chip -1: with interference Low interference favors traceback secrecy Flow Modulator tx Internet rx = spread signal + noise The Ohio State University Dong Xuan: CSE885 on 11/07/07 26 Mark Recognition by Sniffer 1. 2. 3. 4. 5. Sample received traffic to derive traffic rate time series Use high-pass filter to remove direct component by Fast Fourier Transform (FFT) Despreading by local DSSS code Use low-pass filter to remove high-frequency noise Make decision Recovered signal == Original signal? The Ohio State University rx = spread signal + noise High-pass Filter rx’ cr rb PN Code Low-pass Filter Decision Rule Dong Xuan: CSE885 on 11/07/07 27 Invisible Location Attack to Internet Monitoring Systems Widespread attackers attempt to evade the distributed monitoring/detection systems We design invisible LOCalization (iLOC) attack which can locate the detection monitors accurately and invisibly. Then the widespread attacks can evade these located monitors. Effectiveness of iLOC attack We implement iLOC attack, carry out experiments and analyze the effectiveness of iLOC attack. The Ohio State University Dong Xuan: CSE885 on 11/07/07 28 Internet Threat Monitoring Systems Global traffic monitoring based Internet Threat Monitor Systems (ITM): Data center - Distributed monitors - Data center Attacker MONITORS’ LOG UPDATE Network B Network A Attacker monitors Network C Internet monitors A vulnerability: location privacy of monitors (ITM only monitors a small part of whole IP address space.) The Ohio State University Dong Xuan: CSE885 on 11/07/07 29 invisible LOCalization Attack Basic idea: Verify attack traffic in traffic report, verify existence of monitors. Embed an attack mark in the attack traffic, which can be recognized by the attacker. Two Stages: The Ohio State University - Attack traffic generating - Attack traffic decoding Dong Xuan: CSE885 on 11/07/07 30 Final Remarks Group research: theorem and implementation Research on Performance Optimal deployment pattern in WSNs Limited mobility WSNs Research Security Flow marking in internet security Worm detection Wireless security The Ohio State University Dong Xuan: CSE885 on 11/07/07 31 Thank you ! Questions? The Ohio State University Dong Xuan: CSE885 on 11/07/07 32