Cryptography
advertisement
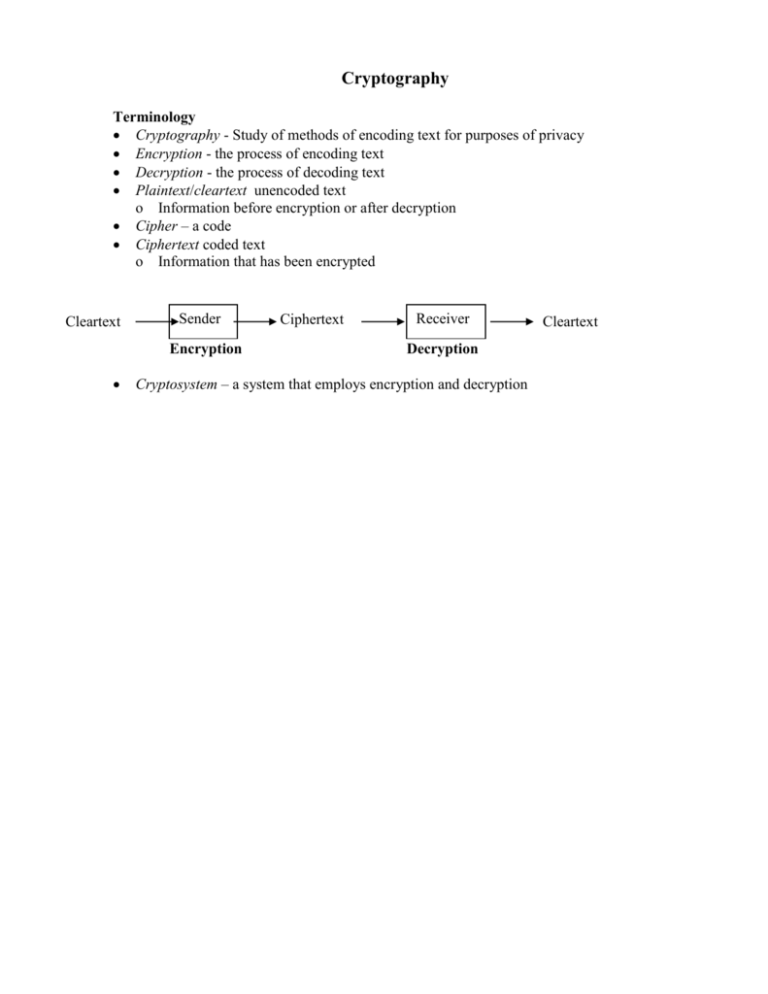
Cryptography Terminology Cryptography - Study of methods of encoding text for purposes of privacy Encryption - the process of encoding text Decryption - the process of decoding text Plaintext/cleartext unencoded text o Information before encryption or after decryption Cipher – a code Ciphertext coded text o Information that has been encrypted Cleartext Sender Encryption Ciphertext Receiver Decryption Cryptosystem – a system that employs encryption and decryption Cleartext Conventional / Symmetric Key / Single Key Encryption Simple algorithm is used to encrypt / decrypt (transform) the text Same key is used in encryption and decryption Secret is primarily in the key An Example - Substitution cipher Symmetric Key System Simple algorithm is used to encrypt / decrypt (transform) the text o Each letter is replaced with a different letter or symbol Caesar’s method o Replace every letter with letter 3 away in alphabet A -> D B -> E C -> F … W -> Z X -> A Y -> B Z -> C Back to Symmetric Key / Single Key Encryption Both parties need same key How to send securely key to receiver o Separate messenger o Key book One-time pads Public Key / Asymmetric Key Cryptosystems Two keys are used- public and private Distribute public key; keep private key…private (duh!) A Bit on How This Could Work What two numbers when multiplied produce 143? Such numbers are called factors Now multiply 13 and 23 Which process took longer? Why? Similar to a one-way screw http://myword.info/images/ow_drive_1b.gif http://www.phxiron.com/images/Products/One%20Way%20Lag%20Screw.jpg o Can drive it in, but difficult to remove it Also, a trap-door o Again, easy to go in, but difficult to come out Idea is to have a function that is easy to calculate in one direction, but not the other o Encryption uses the easy function Involves using the public key o Decryption requires the hard function unless you have the private key How to use it o Freely distribute public key Put it on Web page, for example o Someone sending message encrypts with public key Standard programs (see below) that accepts public key and message and perform the encryption o Receiver uses private key to decrypt message Digital Signatures Public key systems also allow you to digitally sign your messages The message is signed with your private key You end up with a new message consisting of the original message and what appears to be an encoded version To verify that the message is authentic, the receiver supplies your public key The public key is applied to the signed message and checks that the original message and the encoded match Any changes to the original message will cause a mismatch during the verification process http://en.wikipedia.org/wiki/File:Digital_Signature_diagram.svg Digital Certificates Solves the problem of public key authenticity Public key is verified by a well-known entity that verifies the authenticity of the key http://www.youdzone.com/signature.html Well-known Public Key Systems RSA - invented by Ron Rivest, Adi Shamir and Leonard Adleman DSA - Digital Signature Algorithm by David Kravitz Pretty Good Privacy - PGP - uses both conventional and public-key cryptography The RSA Public Key System RSA - invented by Ron Rivest, Adi Shamir and Leonard Adleman Some symbols o o o o o M – message (cleartext) C – ciphertext e – public exponent (power) d – private exponent n - very large (128 bits) number – product of two primes Then: o The message is encrypted by … o … and decrypted by C=Me %n M=Cd %n where n = p * q , p and q are prime numbers Where d = e -1 mod ((p-1)*(q-1)) Notice that to decrypt you need to know d o d can be obtained from e, which is public. However o the calculation is infeasible must find all factors of n determine which are prime must try all pairs of primes to find p and q PGP Pretty Good Privacy Sending message o PGP compresses message Increases security and reduces transmission time o PGP creates session key to be used only once. Randomly created (uses keystrokes and randomly selected mouse movements) o Session key is used to conventionally (symmetric key) encrypt message o Receiver’s public key is used to encrypt session key o Encrypted message and encrypted session key are sent to receiver Receiving message o Private key is used to decrypt session key o Session key is used to decrypt message o Message is decompressed Advantages o Convention encryption is much faster than public key (10,000 times faster) Only using public key on relatively small text (session key) o One time session key prevents trying to decode previous messages to break cipher