Asymmetric-Key (Public-Key) Algorithms
advertisement

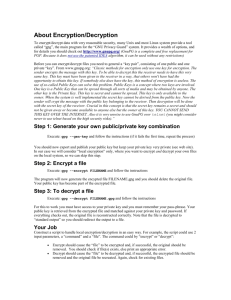
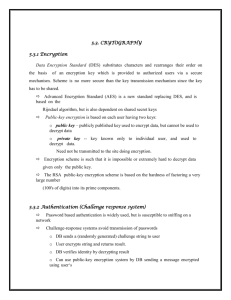
Asymmetric-Key (Public-Key) Algorithms While AES certainly seems to be a very secure encryption system, the main weakness of it and all other symmetric-key encryption systems is the distribution of the keys. This certainly limits the usefulness of symmetric-key encryption by itself in a public environment like the Internet. This fact led two researchers at Stanford University in 1976 to propose a new approach to cryptography. One in which the encryption key is different from the decryption key. The encryption key is made publicly available which leads to the name Public-Key Encryption. The decryption key is kept private and is known only to the recipient of the public-key encrypted message. To establish a secure communication channel between two computers on the Internet, user A employs user B’s public key to encrypt a request message destined for user B. User B upon receiving user A’s request uses his private key to decrypt the message. Since user B is the only one with knowledge of the correct decryption key, user B is the only one who can successfully decrypt user A’s request. To reply to user A’s request, user B employs user A’s public key to encrypt the reply and user A then uses his private decryption key to decrypt the reply from user B. Thus, a secure communication channel has been established between the two users. The trick is to find an algorithm that allows us to decrypt a message using a different key than the one used to encrypt the message, an algorithm that makes it almost impossible to determine the private key given the public key, and an algorithm that can’t be broken with a plaintext attack.