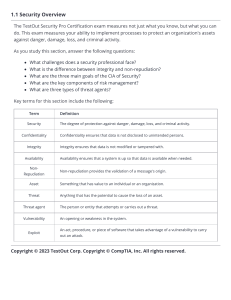
The foremost goal of the information security function should be to
advertisement
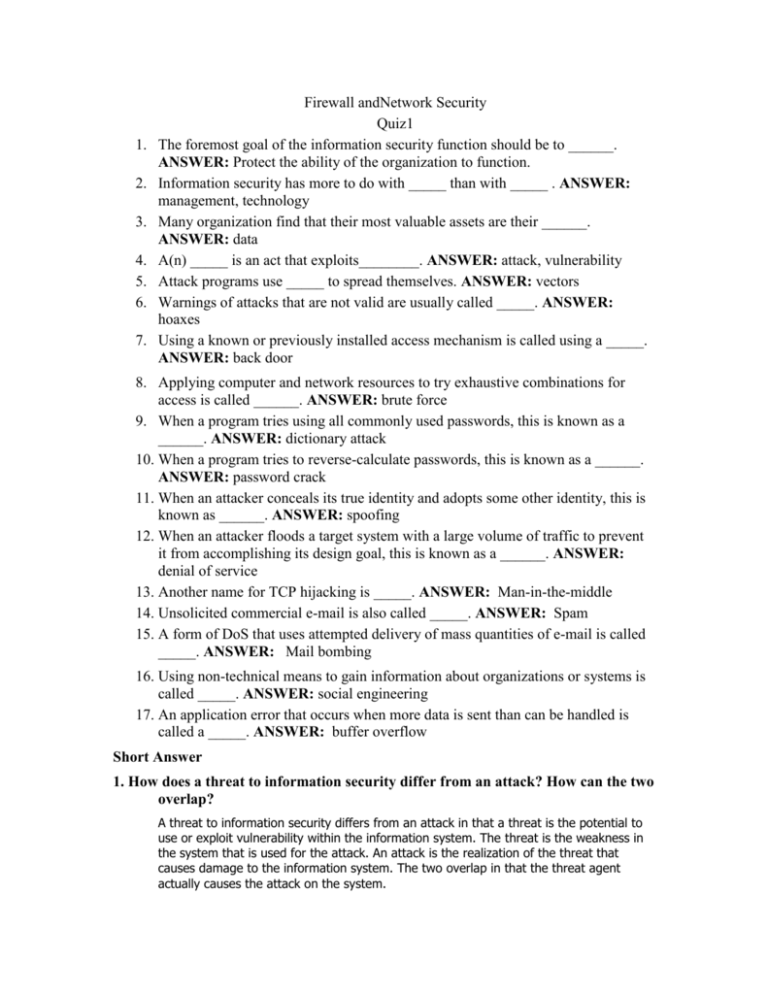
1. 2. 3. 4. 5. 6. 7. Firewall andNetwork Security Quiz1 The foremost goal of the information security function should be to ______. ANSWER: Protect the ability of the organization to function. Information security has more to do with _____ than with _____ . ANSWER: management, technology Many organization find that their most valuable assets are their ______. ANSWER: data A(n) _____ is an act that exploits________. ANSWER: attack, vulnerability Attack programs use _____ to spread themselves. ANSWER: vectors Warnings of attacks that are not valid are usually called _____. ANSWER: hoaxes Using a known or previously installed access mechanism is called using a _____. ANSWER: back door 8. Applying computer and network resources to try exhaustive combinations for access is called ______. ANSWER: brute force 9. When a program tries using all commonly used passwords, this is known as a ______. ANSWER: dictionary attack 10. When a program tries to reverse-calculate passwords, this is known as a ______. ANSWER: password crack 11. When an attacker conceals its true identity and adopts some other identity, this is known as ______. ANSWER: spoofing 12. When an attacker floods a target system with a large volume of traffic to prevent it from accomplishing its design goal, this is known as a ______. ANSWER: denial of service 13. Another name for TCP hijacking is _____. ANSWER: Man-in-the-middle 14. Unsolicited commercial e-mail is also called _____. ANSWER: Spam 15. A form of DoS that uses attempted delivery of mass quantities of e-mail is called _____. ANSWER: Mail bombing 16. Using non-technical means to gain information about organizations or systems is called _____. ANSWER: social engineering 17. An application error that occurs when more data is sent than can be handled is called a _____. ANSWER: buffer overflow Short Answer 1. How does a threat to information security differ from an attack? How can the two overlap? A threat to information security differs from an attack in that a threat is the potential to use or exploit vulnerability within the information system. The threat is the weakness in the system that is used for the attack. An attack is the realization of the threat that causes damage to the information system. The two overlap in that the threat agent actually causes the attack on the system.