The Threat from Within
advertisement

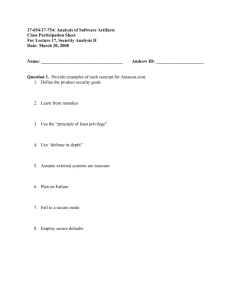
The Threat from Within Anne Oribello Brown University Anne_Oribello@Brown.Edu The Threat from Within • Problems: – departments want to compete with peers at other schools to incorporate technology into their programs – vendors add web based front ends and insist users move to that platform for software support Threat from Within (cont.) – Faculty read about new a technology and obtain it through grant monies or donation – business units within the university want to be more accessible by putting data on the Internet • How many of these activities are being done securely? Issues • Lack of adequate training for some sysadmins • Reliance on vendors to properly configure server • Pressure to roll out a system by a deadline • Lack of funding by departments for security tools Issues (cont.) • Lack of understanding of risks and issues by decision makers • Security had been viewed as an impediment to work • Culture of open access • Lack of sufficient security staff Solutions • Establish realistic policies/guidelines • Educate the user community on evolving technologies • Scan servers • Perform security reviews Establish Policies/Guidelines • Get support from key players • Establish incentives to conform – offer centralized services to reduce their work – establish user groups to develop (human) network • Create viable alternative for violators • Be specific in definition of conformity • Document dissemination effort Educate Community • • • • Face-to-face training for staff Technical updates for decision makers Articles in faculty/staff newsletter Listserv mailings (BBoards seem to have lost “favor”) Scan Servers • Schedule can depend on criticality of server – Internet Security Scaner – hacker tools (i.e. NMAP) • Isolate moving targets (i.e. students) Perform Security Reviews • Offer as a service BEFORE they have an incident • Examine data security in entirety (electronic, printed data, physical) • Ensure that comments aren’t surprises • Allow responses from department • Follow up on progress The Threat from Within • Make security support a service • Give end users the knowledge to have a secure system • Begin to change attitudes • If all else fails, tell them how much it will cost if there is a breach (time, research effort, reputation, money) Helpful URLs • • • • • www.alw.nih.gov/Security/prog-full.html firosoft.com/security/philez/exploits/any-unix/ insecure.org www.rootkit.com (WIN environment) www.sans.org/