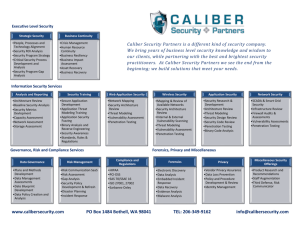
Security Training
advertisement
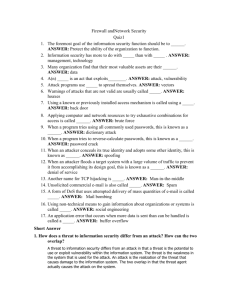
Security Training Lunch ‘n Learn Agenda Threat Analysis Legal Issues Threat Mitigation User Security Mobile Security Policy Enforcement Threat Analysis Information security is the responsibility of everyone who works with it Security is a process not a product Threats can be both internal and external Vendor contracts need privacy clauses Threat Analysis • Packet sniffing – Collects sensitive data including passwords – Even encrypted passwords can be cracked • Code exploits – Buffer overflows – Remote executable • Malware – Collection of sensitive data – Distributed Denial of Service attack Threat Analysis • Social Engineering – Phishing websites, emails, IMs – Hacker may pose as someone else to gain password • Intellectual Property Theft – Research data needs to be secured • Identity Theft – Social security numbers and financial information must be secured Malicious Software • Virus – Self replicating code that infects a host file – Requires file sharing to spread across network • Worm – Stand alone, does not require host – Self propagating through email or IM Malicious Software • Trojan horse – Installed along with other software – Opens backdoor or sends sensitive data back to source • Spyware – Collects personal information and browsing habits • Adware – Creates popups Malicious Software • ActiveX/Java applets • Bundled with freeware as part of Terms of Agreement • Only download from trustworthy sources • Peer to Peer filesharing – Can unknowingly share sensitive information – Can accidentally download copyrighted material Legislation • Family Educational Rights and Privacy Act (FERPA) – Protects a student academic record – Defines when academic record or directory information can be released without consent • Gramm-Leach Bliley Act (GLBA) – Protects the financial information of a person – Consumer must be provided privacy note on yearly basis Legislation • Sarbanes-Oxley Act (SOX) – Deals with the accuracy and reliability of a companies financial information • Health Insurance Portability and Accountability Act (HIPAA) – Privacy of medical records Legislation • New York’s Education Law (Article 1 S-2b) – Restricted use of SSN • New York’s Information Security Breach and Notification Act – Individual must be notified if sensitive personal information is compromised Legislation • Why are these important? – External auditors have told us to adhere to as many regulations as possible – Many financial regulations are in the process of being applied to higher ed – Our Board of Trustees have insisted on it • Information Security Policy • Information Security Procedures/Standards Threat Mitigation • Access control – Physical security – Authentication, authorization, and accounting – Access control lists – Firewalls – Network Access Control • Patch management – Network devices – Servers Threat Mitigation • Encryption – SSH, SSL, file level encryption • VPN – Creates secure tunnel between external address and internal network – Secures all wireless traffic • Barracuda Spam Filter • Proper disposal of information – Shredders, DoD level hard disk formatting Desktop Security • Separate machine for work and home – Child/spouse may compromise data • Strong passwords – Combination of lower case, caps, numbers, and symbols – Do no share password with anyone – Change passwords frequently • Always lock machine when not using it – Automated screen saver password Desktop Security • Antivirus – Up to date definitions – Real time monitoring • Spyware removal tools – Up to date definitions – Frequent scans • Personal firewall – Only open ports to necessary services Desktop Security • Use Firefox over Internet Explorer if at all possible – Popup blockers • Only install software from trusted sources – This includes any ActiveX/Java applets • Keep up to date with the latest security patches • Ensure screen is not visible to outsiders Mobile Security • Try not to store sensitive data locally on mobile machines – Data can be compromised by loss or theft – Encrypt sensitive data that needs to be stored locally • Users should cable lock laptops when not in presence – Even in cars, hotel rooms, etc… Mobile Security • Never leave a PDA unattended • Remote wipe software • Encrypt data on portable media Policy Enforcement • Our goal is not to punish you for misdeeds but to keep the network clean and the information secure • Punitive actions can promote cover ups, denials, and prolongs detection • Please contact us immediately if anything appears suspicious • Feel free to come to me with any questions Conclusion • • • • Questions? Comments? Compliments? Complaints? • http://infosecurity.marist.edu/ • Justin.Bassignani@marist.edu