Abstract - Best IEEE Projects
advertisement
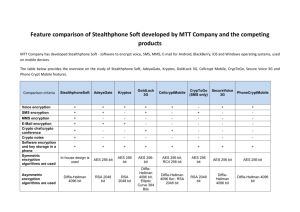
A Novel Error-Tolerant Method in AES for Satellite Images ABSTRACT: This paper uses one of the security algorithms like the Advanced Encryption Standard (AES) in Earth Observation small Satellites. Commercial security in Earth observation satellite images is in need to protect valuable data transmitted from the satellite. In November 2001 NIST published Rijndael as the proposed Algorithm for AES (Advanced Encryption Standard), it provides the highest level of security by utilizing the newest and strongest 128 bit AES encryption algorithm to encrypt and authenticate the data. At the same time while encryption process immunity of encryption is taken into the account. Five modes of AES have been used to perform security on satellite data. The different modes are ECB, CBC, OFB, CFB and CTR. All the above techniques except OFB lead to fault during data transmission to ground because of noisy channels. It is due to Single Event Upsets (SEU). In order to avoid data corruption due to SEU’s a novel fault tolerant model of AES is presented which is based on the Hamming error correction code. This reduces the data corruption and increases the performance. As a result we can identify the error and also we can encrypt the image as color. Thus the data corruption due to Single Event Upset can be avoided and the performance was increased. Key-Words: Single Event Upsets, Hamming Error code detection, Earth Observation satellite, Output Feedback Mode, AES INTRODUCTION: An Earth observation (EO) satellites are satellites specifically designed to observe Earth from orbit, similarly reconnanissance satellites but intended for non-millitary uses such as environmental monitoring meterology, map making etc. This Earth Observation satellite takes images on earth using image sensors. Geostationary Operational Environmental Satellites, Himawari, Misc ets are some of the earth observation satellites [11]. Earth Observation satellites were used more effectively in disaster management support. Today meterological satellites are widely used to detect and track severe stroms and to support other wheatherdriven events. However, operational of data from these and other EOsatellites to support management of other types of disasters (e.g., soil, spills, harmful algae blooms, earthquakes, forest fires). BLOCK DIAGRAM: The AES is a symmetric key algorithm, in which both the sender and the receiver use a single key for encryption and decryption. AES defines the data block length to 128 bits, and the key lengths to 128, 192, or 256 bits [3]. It is an iterative algorithm and each iteration is called a round. The total number of rounds, Nr, is 10, 12, or 14 when the key length is 128, 192, or 256 bits, respectively. Each round in AES, except the final round, consists of four transformations: VEDLABS, #112, Oxford Towers, Old airport Road, Kodihalli, Bangalore-08 Page 1 SubBytes, ShiftRows, MixColumns, and AddRoundKey. The final round, does not have the MixColumns transformation as shown in Fig. 1 and Fig. 2. The decryption flow is simply the reverse of the encryption flow and each operation is the inverse of the corresponding one in the encryption process. Fig. 1. Block diagram of AES encryption Fig. 2. Block diagram of AES decryption HARDWARE AND SOFTWARE REQUIREMENTS: Software Requirement Specification: Operating System: Windows XP with SP2 Synthesis Tool: Xilinx 12.2. Simulation Tool: Modelsim6.3c. VEDLABS, #112, Oxford Towers, Old airport Road, Kodihalli, Bangalore-08 Page 2 MATLAB Hardware Requirement specification: Minimum Intel Pentium IV Processor Primary memory: 2 GB RAM, Spartan III FPGA Xilinx Spartan III FPGA development board JTAG cable, Power supply REFERENCES: [1] Gussenhoven, M. S., and Mullen, E. G. Space radiation effects program: An overview. IEEE Transactions on Nuclear Science, 40, 2 (Apr. 1993), 221—227. [2] Kastensmidt, F. L., Carro, L., and Reis, R. Fault-Tolerance Techniques for SRAM-Based FPGAs. [3] Daemen, J., and Rijmen, R. The Design of Rijndael: AES–The Advanced Encryption Standard. New Yrok: Spriger-Verlag, 2002.New York: Springer, 2006. [4] [20] Burr, W. E. Selecting the advanced encryption standard. Security & Privacy Magazine, 1, 2 (Mar.—Apr. 2003), 43 [5] Wicker, S. B. Error-correction coding for digital communication and storage. Upper Saddle River, NJ: Prentice-Hall, Jan. 1995. [6] Luby, M. G., Mitzenmacher, M., Shokrollahi, M. A., and Spielman, D. A. Efficient erasure correcting codes. IEEE Transactions on Information Theory, 47, 2 (Feb. 2001), 569—583. VEDLABS, #112, Oxford Towers, Old airport Road, Kodihalli, Bangalore-08 Page 3