AES Encryption
advertisement

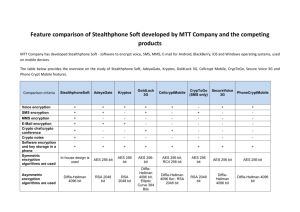
AES ENCRYPTION Kevin Orr JT Schratz OVERVIEW • History • Algorithm • Uses • Brute Force Attack HISTORY • Before AES, the Data Encryption Standard (DES) became the federal standard in 1977 • DES uses a 56-bit key • By the late 1990s, however, it was possible to break DES in a matter of several days • In January 1997, NIST announced a competition for the successor to DES • NIST – National Institute of Standards and Technology • The selected the winner was the Rijndael algorithm in October 2000 • Belgian cryptograhers Joan Daemen and Vincent Rijmen • Formally known as AES – Advanced Encryption Standard ALGORITHM 10 cycles of repetition for 128-bit keys. 12 cycles of repetition for 192-bit keys. 14 cycles of repetition for 256-bit keys. ALGORITHM STEPS - SUB BYTES • each byte in the state matrix is replaced with a SubByte using an 8bit substitution box • bij = S(aij) SHIFT ROWS • Cyclically shifts the bytes in each row by a certain offset • The number of places each byte is shifted differs for each row MIX COLUMNS • Each column is multiplied by the known matrix. For the 128-bit key it is ADD ROUND KEY • Each byte of the state is combined with a byte of the round subkey using the XOR operation USES • Government Standard • AES is standardized as Federal Information Processing Standard 197 (FIPS 197) by NIST • AES is sufficient to protect classified information up to the SECRET level. • TOP SECRET information will require use of either the 192 or 256 key lengths. • Industry • SSL / TLS • SSH • WinZip • BitLocker • Mozilla Thunderbird • Skype BRUTE FORCE ATTACK • Supercomputer: K Computer (Japan, 2011) • Speed: 10.51 Pentaflops= 10.51 x 1015 Flops [Flops = Floating point operations per second] • Flops required per combination = 1000 • Combination checks per second = (10.51 x 1015) / 1000 = 10.51 x 1012 • Seconds in a Year = 31536000 • No. of Years to crack AES with 128-bit Key = (3.4 x 1038) / [(10.51 x 1012) x 31536000] = (0.323 x 1026)/31536000 = 1.02 x 1018 years = 1 billion billion years CONCLUSION • AES has been around for about 12 years and is still a very strong type of encryption • Only uses four transformations to create the encryption • Many programs today that have a need for encryption often use AES due to its strength • The attempted attacks focus on weaknesses or characteristics in specific implementations called “side channel attacks” and not on the algorithm itself • So far it is uncrackable SOURCES • http://luxsci.com/blog/256-bit-aes-encryption-for-ssl-and-tls-maximal-security.html • http://www.technewsworld.com/story/70437.html • http://www.eetimes.com/design/embedded-internet-design/4372428/How-secure-is-AESagainst-brute-force-attacks- • http://en.wikipedia.org/wiki/Advanced_Encryption_Standard QUESTIONS