Module H
advertisement

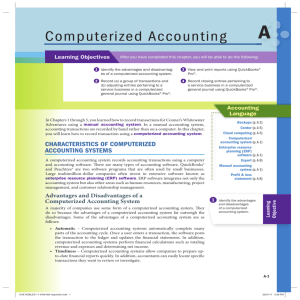
• Module H: Auditing in a Computerized Environment "To err is human, but to really foul things up you need a computer.“ Paul Ehrlich, Technology commentator • Module H Objectives 1. Identify how the use of a computerized processing system impacts the audit examination. 2. Provide examples of general controls and understand how these controls relate to transaction processing in a computerized processing system. 3. Provide examples of automated application controls and understand how these controls relate to transaction processing in a computerized processing system. 4. Describe how the audit team assesses control risk in a computerized environment. 5. Identify how audit teams perform tests of controls in a computerized environment. 6. Describe the characteristics and control issues associated with end-user and other computing environments. 7. Define and describe computer fraud and the controls that can be used to prevent it. • Issues Introduced in a Computerized Environment 1. Input errors 2. Systematic vs. random processing errors 3. Lack of an audit trail 4. Inappropriate access to computer files and programs 5. Reduced human involvement in processing transactions 1 • Impact of Computerized Processing on the Evaluation of Internal Control Phase Effect(s) Understanding Understand and document controls related to computerized processing of transactions Assessment Consider controls related to computerized processing of transactions in preliminary assessment of control risk Testing Identify , test, and evaluate degree of compliance of controls related to computerized processing of transactions • Types of Computer Controls – – • General Controls • Relate to all applications of a computerized processing system (pervasive) • Deficiencies will affect processing of various types of transactions Automated Application Controls • Relate to specific business activities • Directly address management assertions Categories of General Controls 1. Hardware controls 2. Program development controls 3. Program change controls 4. Computer operations controls 5. Access to programs and data controls • Hardware Controls – Provide reasonable assurance that data are not altered or modified as transmitted through system – “Built into” equipment by computer manufacturer – Examples 2 • • • Parity check • Echo check • Preventative maintenance on equipment Program Development Controls – Acquisition and development of new programs is properly authorized and conducted with organization policies – Appropriate users participate in process – Programs and software are tested and validated prior to use – Programs and software have appropriate documentation Systems Development Life Cycle [diagram] • • Program Change Controls – Modifications to existing programs are properly authorized and conducted with entity policies – Appropriate users participate in process – Programs are tested and validated prior to use – Programs have appropriate documentation – Additional controls related to “emergency” change requests and migrating new programs into operations Computer Operations Controls – Relate to processing of transactions and backup and recovery of data – Processing environments • Batch processing: Similar transactions collected and processed simultaneously • Real-time processing: Transactions processed as they occur without delay 3 • Examples of Computer Operations Controls – Methods of resolving processing failures – Separation of duties – • • Systems analysts • Programmers • Computer operators Files and data • Labels to ensure use of appropriate file • Storage in remote, protected locations (disaster recovery) • Grandfather-father-son Access to Programs and Data Controls – Relate to restricting use of programs and data to authorized users – Examples • Passwords • Automatic terminal logoff • Review access rights and compare to usage (through logs) • Report and communicate security breaches 4 • General Controls and Assertions Assertion Explanation Examples Accuracy Ensure accuracy of data and testing computer programs prior to implementation • Hardware controls • Program development controls • Program change controls • Computer operations controls • Computer operations controls • Access to programs and data controls Occurrence • Automated Application Controls Input controls Processing controls Output controls Input Controls – • Restricting inappropriate access reduces probability of fictitious transactions Provide reasonable assurance that input is properly authorized and accurately entered for processing • All transactions input • Transactions input once and only once • Transactions input accurately Examples of Input Controls – Data entry and formatting – Authorization and approval controls – Check digits 5 • – Record counts – Batch totals – Hash totals – Valid character tests – Valid sign tests – Missing data tests – Sequence tests – Limits and reasonableness tests – Error correction and resubmission Summary of Input Controls Input accurate Data entry and formatting X Check digits X Record counts All transactions entered Transactions entered only once X X Batch totals X X X Hash totals X X X Valid character test X Valid sign tests X Missing data tests X Sequence tests X Limit and reasonableness tests X Error correction and resubmission X 6 • Processing Controls – – • • Transactions are processed accurately • All transactions are processed • Transactions are processed once and only once Examples • Test processing accuracy of programs • File and operator controls • Run-to-run totals • Control total reports • Limit and reasonableness tests • Error correction and resubmission Output Controls – – I. Provide reasonable assurance that Provide reasonable assurance that • Output reflects accurate processing • Only authorized persons receive output or have access to files generated from processing Examples • Review of output for reasonableness • Control total reports • Master file changes • Output distribution limited to appropriate person(s) Tests of Computer Controls • Forming an Assessment of Control Risk 1. Identify specific control objectives 7 2. Identify points where misstatements could occur 3. Identify control procedures designed to prevent or detect misstatements – General controls and automated application controls 4. Evaluate design of control procedures – • Are tests of controls cost-effective? Auditing in a Computerized Environment – – Auditing “around” the computer • Reconcile input with output produced by computer processing • Do not directly evaluate operating effectiveness of computer controls Auditing “through” the computer • • Evaluate operating effectiveness of computer controls and logic of computer processing When to Use Each Approach? “Around” the computer “Through” the computer Complexity of processing Computer used for relatively simple calculations Computer applications are more complex in nature Implementation of computer controls Less extensive More extensive Existence of source documents and audit trail Existence of “hard copy” (paper) source documents or audit trail Source documents exist in electronic format 8 Results of one stage of computerized processing are used as inputs in subsequent stages of processing • Testing Computer Controls – – • • • Testing controls • Inquiry • Observation • Inspect documentary evidence • Reperformance Evaluating computer processing and programs • Test processing of actual transactions • Test processing of simulated transactions Techniques Using Actual Transactions – Audit team evaluates controls by “observing” processing of actual transactions through computerized system in a typical processing run – Program-embedded techniques: Special modules coded into computer programs • Tagging transactions • Embedded audit modules • Snapshot • Monitoring systems activity • Program analysis techniques Techniques Using Actual Transactions – Parallel Simulation – Special programs prepared by audit team (CAATs) – Make sure actual transactions processed are representative of client transactions Techniques Using Simulated Transactions – Test data: Tested in a separate processing run by client – Integrated test facility: Simulated data processed along with actual data 9 • • Benchmarking – Audit team tests operating effectiveness of automated application controls to establish baseline – Can continue to rely on automated application controls if: Test general controls related to program changes, access to programs and data, and computer operations • General controls continue to operate effectively • Automated application controls have not changed since the baseline End-User Environments – – • • Control issues • Lack of separation of duties • Lack of physical security • Lack of documentation and testing • Limited computer knowledge of personnel Implications • Limit concentration of functions and increase supervision • Access to program and data controls are critical Computer Abuse/Fraud – Use of computer technology by perpetrator to achieve gains at the expense of a victim – Controls • Preventative: Stop fraud from entering system • Detective: Identify fraud when it enters system • Damage-limiting: Reduce monetary impacts of fraud and control to specified levels 10