Chapter 7
advertisement
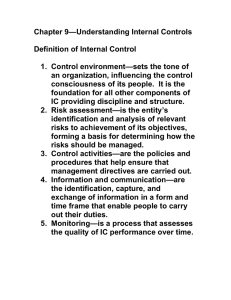
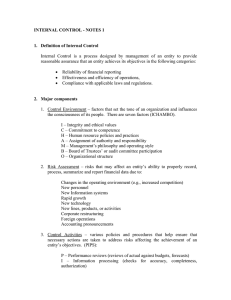
CHAPTER 7 THE EFFECT OF INFORMATION TECHNOLOGY ON THE AUDIT FUNCTION Answers to Review Questions 7-1 Technological changes that are occurring in IT and their implications for the audit functions are as follows. 1. Electronic (Internet) commerce involves individuals and organizations engaging in business transactions, without paper documents, using computers and communications networks. When a client sells products or services over the Internet, the auditor’s main concerns are transaction integrity, protection of information, and unauthorized access to the entity’s network. 2. Distributed data processing organizes and coordinates data processing by decentralizing computer functions and computing power. Distributed data processing places selected information processing capabilities at the divisional or user department level. This can enhance user productivity through easier access to data and computer programs. The auditor's major concerns with distributed data processing are the controls that are used to limit access to the system and telecommunication controls that handle the transmission of data to and from the central computer. 3. Real-time systems provide immediate responses to an inquiry without changing data files. Real-time systems significantly affect how audits are performed. In such systems, there are likely to be fewer source documents in hard-copy form, and there may also be no batch-type controls to ensure completeness. Thus, the concern for controls over access to the system is increased. Another concern relates to the fact that transactions may be authorized by controls included in the programs. 4. Intelligent systems place the knowledge and decision processes of experts into a computer program. The auditor will have to be concerned with the integrity of the knowledge captured in the system and the ways in which the system makes decisions. 5. End-user computing allows user departments to develop their own applications and data files. Control over end-user computing is an important issue for the auditor because weak controls at the user department may allow users to inappropriately access and modify data at the main computer center. 7-2 IT systems can be categorized into three types: low-complexity, mediumcomplexity, and advanced systems. A low-complexity IT system would normally be composed of a stand-alone microcomputer or a small number of microcomputers that are connected to a network. Most of the software used by a low-complexity system would be purchased from vendors with little or no modification. A system of medium complexity would, at a minimum, include a minicomputer or server and might include a number of microcomputers or terminals networked to the minicomputer or server. The types of software used in a medium-complexity system would be more advanced, with utility programs used to enter and change data and purchased software used and modified to meet the entity's needs. An advanced system contains one or more of the following characteristics: telecommunications; extensive database systems; online, real-time 1 processing; distributed data processing; automatic transaction initiation, EDI, and electronic commerce; and no visual audit trail. 7-3 The auditor's knowledge of the entity's computer processing must include the following factors: (1) the extent to which IT is used in each significant accounting application, (2) the complexity of the entity's IT operations, (3) the organizational structure of the IT processing activities, and (4) the availability of data for evidential matter. 7-4 General controls can be classified into five categories: (1) organizational controls, (2) data center and network operations controls, (3) hardware and systems software acquisition and maintenance controls, (4) access security controls, and (5) application systems acquisition, development, and maintenance controls. In a computerized environment, the programs within the system may perform many of the functions (e.g., the initiation of transactions, authorization of transactions, recording of transactions, and custody of assets) that were formerly performed by different individuals. Therefore, it is important to have adequate segregation of duties within the IT Department to compensate for this situation. 7-5 Good controls over program changes prevent programmers and possibly other employees from making unauthorized changes to operational programs that may result in loss of assets or records, or manipulation of financial and operational data. The main controls over program changes are proper authorization, testing, and implementation of the program changes. 7-6 Physical security controls include locating the computer facilities in a separate building or in a secure part of a building. They also include limiting access to the computer facilities through the use of locked doors with authorized personnel being admitted through use of a conventional key, an authorization card, or physical recognition. Controls must also be enforced within the computer facility by not allowing programmers to access the computer room; this restriction will prevent them from making unauthorized modifications to systems and application programs. Finally, there must be adequate protection against events such as fire and water damage, electrical problems, and sabotage. Physical control over programs and data can be maintained by a separate library function that controls the access to and use of files. In advanced computer systems, access controls include physical security over remote terminals, authorization controls that limit access to authorized information, user identification controls such as passwords, and data communication controls such as encryption of data. 2 7-7 Examples and descriptions of data validation controls include: Data Validation Control Description Limit test A test to ensure that a numerical value does not exceed some predetermined value. Range test A check to ensure that the value in a field falls within an allowable range of values. Sequence check A check to determine if input data are in proper numerical or alphabetical sequence. Existence (validity) test A test of an ID number or code by comparing it to a file or table containing valid ID numbers or codes. Field test A check on a field to ensure that it contains either all numeric or alphabetic characters. Sign test A check to ensure that the data in a field have the proper arithmetic sign. Check-digit verification A numeric value computed to provide assurance that the original value was not altered. Turnaround documents are output documents from the application programs that are used as source documents in later processing. The use of a turnaround document reduces data capture and data validation errors since the entity does not have to reenter the data. 7-8 The main difference between authorization procedures in manual and computerized systems is that in a computerized system the authorization procedure may be programmed into the software, while in a manual system an individual is usually responsible for authorizing transactions. 7-9 Generalized audit software (GAS) includes programs that allow the auditor to perform tests on computer files and databases. They were developed so that auditors would be able to conduct similar computer-assisted audit techniques in different computer environments. Custom audit software is generally written by auditors for specific audit tasks. Such programs are necessary when the entity's computer system is not compatible with the auditor's GAS or when the auditor wants to conduct some testing that may not be possible with the GAS. Some functions that can be performed by GAS are: (1) file or database access, (2) selection of transactions that meet certain criteria, (3) performance of arithmetic functions, (4) statistical analyses, and (5) report generation. 3 7-10 The main difference between the test data method and ITF has to do with how the test data are processed. When the test data method is used, the test data are processed separately through the client’s programs. With the ITF technique the test data are run with actual data in a normal application run. Thus, with ITF, the testing takes place under actual operating conditions. 7-11 Audit tasks that can be performed using a microcomputer include: Trial balance and lead schedule preparation. Working paper preparation. Audit program preparation. Performance of analytical procedures. Documentation of internal control. Performance of statistical sampling applications. Answers to Multiple-Choice Questions 7-12 7-13 7-14 7-15 7-16 7-17 7-18 A D C B A D A 7-19 7-20 7-21 7-22 7-23 7-24 A D D C D A 4