Simple and Secure User Authentication for Mobile Banking
advertisement

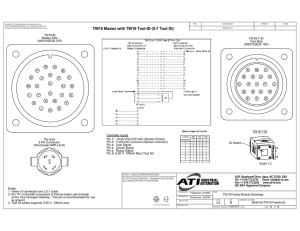
Usably Secure, Low-Cost Authentication for Mobile Banking* Saurabh Panjwani, Ed Cutrell Microsoft Research India * Many thanks to Anupam Varghese (EKO India Financial Services Ltd.). Thanks also to Aishwarya Ratan, Indrani Medhi, Prasad Naldurg, Raghav Bhaskar (Microsoft Research) Mobile Banking • Over 1 billion people in the world with mobile phones but no bank accounts • Banks say, “Let’s use phones to serve these people!” • Several mobile banking services exist today – M-PESA (Kenya), Wizzit (S.A.), GCash (Philippines) – > 100 million dollars transacted per day How does it work? • A network of human agents mediate transactions – Run small businesses: mobile recharge, pharmacy etc – Commissioned by m-banking provider Courtesy: CKS M-banking outlet in Delhi Courtesy: CKS An m-banking agent sends an SMS to the bank for a deposit transaction How does it work? Hari deposits 100/- “Credit Hari’s a/c with 100/-” Agent Bank “Hari’s a/c credited” Hari How does it work? Hari withdraws 100/- “Agent’s a/c credited” Agent Bank “Credit agent’s a/c with 100/-” Hari Benefits • Benefit to customers: – Low-cost, low-effort savings (often, there’s interest) – A new remittance channel – Others that evolve contextually (m-payments) • Benefit to agents: – A second source of income • Note: different from mobile banking for the rich • There, the goal is convenience; here, it is access. Security Issues • Phones can be lost or stolen. Banks must authenticate users. Is this really Hari? Bank “Credit agent’s a/c with 100/-” Hari Challenges • How do we authenticate via a phone like this? • No GPRS, • Can’t install software • Typical m-banking user’s phone Courtesy: EKO • … while also ensuring • A simple interface (want low-literate users to use it) • Low cost (want it to scale) Current Practice • Most banks use PINs to authenticate users • For good security, PINs must be protected • Can’t rely on GSM security – Network-layer protection only + several known attacks • Then how do banks protect PINs? – Some don’t care! – Others protect them, but don’t tell you how! Our work • Partnered with EKO, m-banking service in India – 1.5 years in operation, 70K customers, partners of SBI – Support from Gates Foundation • EKO uses PINs + security tokens for authentication Endorsed by Verisign Inc. • Our contribution: – Find a flaw in EKO’s scheme – Propose a new solution – Test it with real users EKO locations EKO’s Authentication Solution • Every user has a PIN & holds a unique codebook – Appends a “signature” to each transaction message – A fresh signature each time Our Finding: Given 7 such signatures from a user, the PIN can be recovered. Each entry is a 10-digit string with a 6-digit one-time password and 4 gaps, denoted ♦ Example: If PIN = 6391, OTP = ♦♦32♦6090♦, then, Signature = 6332960901. Implications • The PIN is redundant in EKO’s scheme – Security rests on codebook and phone, not on PIN • PIN loss could have other bad consequences – Users use same PIN across different accounts; loss of PIN could damage other accounts they hold The New Scheme* • Like EKO’s scheme, uses one-time passwords, but each OTP is a 10-digit random number 0 1 2 3 4 5 6 7 8 9 4 5 8 3 2 1 9 0 8 7 Example: PIN = 2340, signature is: 8324 • Variant of the well-known one-time pad scheme • Caveat: Need PINs with distinct digits * Developed in collaboration with EKO India Financial Services Ltd. How do they compare? New scheme is more secure than plain PIN entry and EKO’s scheme Method Plain PIN Secure against Secure against PIN impersonation recovery Secure against impersonation, given booklets Secure against man-in-themiddle forgeries NO NO NO NO EKO YES NO NO NO Ours YES YES YES (Ongoing work) How do they compare? New scheme is more usable than EKO’s scheme. (Based on a usability study with 34 current and potential mbanking customers in Delhi, Bihar*) 65% of participants found the new scheme easier to use than EKO’s. (10% were neutral.) * Thanks to CKS India Pvt. Ltd. for helping us conduct the study. What do users say? • Users reported several advantages of new scheme: – “new scheme is easy as it involves typing only 4 digits” – “only matching of numbers needs to be done, which is easy” – “everything is given in the booklet, just needs to be looked up” • Offered interesting cognitive explanations – “.. need to lay less stress on my brain and more on my eyes, which is why it is easier to handle.” • Pro-actively spoke about security benefits – “the PIN is mixed up here and not written in plain, which means it is more secure’’ – “new scheme is more easy to use: it is more secure, therefore it is more easy” Beyond Mobile Banking • PIN-entry using our scheme provides better security than PIN-entry at ATMs – Secure against skimming attacks. (Skimming attacks caused a loss of > $1 billion in 2009.) – Reasonably secure against shoulder-surfing attacks • Similar solution is used for online-banking by some European banks – Drawback: phishing attacks. • Caveat: Decreased usability (users need to carry tokens) Conclusion • Cryptanalyzed EKO’s authentication scheme • Proposed a new authentication solution – More secure, more usable! – Easy to deploy (no software installation, no changing network protocol) – Potentially applicable beyond mobile banking • Future work – Get rid of the codebook, can we?