On the Impact of Security Protocols on the Performance of SNMP
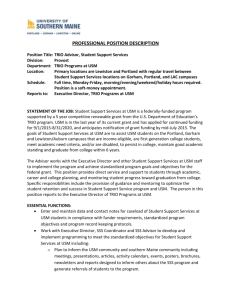
advertisement

On the Impact of Security Protocols on the Performance of SNMP Group 6 KHAN, Taimur KONG, Jing SHIH, Min SUN, Mengti YU, Chenglin J. Schonwalder and V. Marinov IEEE Transactions on Network and Service Management, 2011, pp.52-64 http://dx.doi.org/10.1109/TNSM.2011.012111.00011 24 slides 1 Summary Question: How can SSH, TLS, DTLS be used to address limitations in SNMPv3/USM? Answer this question by Analyzing impact and performance between the various options to secure SNMP 2 Outline • • • • • • • Background SNMP Architecture Message-based Security Session-based Security Performance Evaluation Key Findings Guidelines for Choosing Solutions 3 Background SNMPv1 has no cryptographic security && the engineered solution on SNMPv2 is too complex USM (User- based Security Model) on SNMPv3 SNMPv3 and USM have to deploy another user and key management infrastructure high cost SSH, TLS, DTLS are introduced which can take advantage of already deployed key management infrastructures 4 SNMP Architecture ASIs are the interfaces between subsystem Ref. RFC3414(USM), 3584(CSM), 5591(TSM), 5592(SSHTM), 6353(TLSTM) 5 Message-based Security • CSM (SNMPv1, SNMPv2c) – Plain-text community string which provides very little security. • USM (SNMPv3) – noAuthNoPriv (nn) • no authentication, no encryption – authNoPriv (an) • message authentication, message integrity, timeliness checking • no encryption – authPriv (ap) • message authentication, message integrity, timeliness checking • encryption of the payload of SNMP messages 6 TSD for Message-based Security 7 Session-based Security • Transport Security Model – Negligible costs on passing existing information • SSH Transport Model – Many methods for authentication • TLS Transport Model for TLS – Session resumption mechanism – X.509 certificates for authentication • TLS Transport Model for DTLS (over datagram) 8 TSD for Session-based Security 9 Performance Evaluation • • • • • Session Establishment Latency without Packet Loss Bandwidth Usage Latency with Packet Loss Impact of Bulk Retrieval 10 Session Establishment PERFORMANCE OF A SINGLE SNMPGET REQUESTS (SYSDESCR.0) 11 Slow machine Fast machine USM/ap ≈ USM/an ≈ USM/nn little benefit in removing auth/priv 12 Latency without Packet Loss (II) USM/ap ≈ TSM/SSH ≈ TSM/(D)TLS difference of protocols do not have much impact on delays if using similar hash functions and encryption transformations 13 For v3/USM/ap, v3/USM/nn, v2/CSM over UDP ≈ over TCP UDP ≈ TCP in a fast reliable network 14 USM/ap > USM/an > USM/nn > SNMPv2/TCP >SNMPv2/UDP 15 TSM/TLS > TSM/SSH > USM > TSM/DTLS 16 Latency with Packet Loss • TCP's retransmission algorithm clearly outperforms simple non-adaptive SNMP retransmission algorithm PACKET SIZES FOR ALL SECURITY MODEL / TRANSPORT / SECURITY LEVEL COMBINATIONS 17 Impact of Bulk Retrieval ↑ max-repetitions parameter (r) In the best case, r reduces ↓ number of interaction needed the number of interactions to 1/r. But not the same ↓ overall latency 18 factor for latency Key Findings • TLS session resumption feature significantly reduces the session reestablishment costs. – The resumption mechanism for SSH has yet to be standardised • The difference between USM, SSH, TLS and DTLS in terms of latency is small after the session is established. • The non-adaptive SNMP retransmission algorithm is outperformed by TCP algorithms in packet loss networks. • The usage of GetBulk dramatically reduces the number of requests sent over the network, resulting in much better overall performance. 19 Guidelines for Choosing Solutions (SNMPv3/TSM/SSH) • • • • • • • Good AAA Integration Easy derivation of securityName Efficient message encoding × Large session establishment overhead × Lack of session resumption mechanisms TCP Supports large messages better than UDP TCP retransmission algorithms work well 20 Guidelines for Choosing Solutions (SNMPv3/TSM/TLS) • • • • • • • Same pros and cons of using TCP as SSHTM TLS session resumption Less session startup overhead than SSH × Less efficient in message encodings than SSH × Complicated derivation of securityName × Lack of good AAA integration × X.509 infrastructure must be in place 21 Guidelines for Choosing Solutions (SNMPv3/TSM/DTLS) • • • • Shares most of the pros and cons of TLSTM Smaller framing overhead over UDP Applications have control over retransmissions Although application retransmission timers are to be coordinated with DTLS retransmission timers 22 Guidelines for Choosing Solutions (SNMPv3/USM/UDP) • Separate key management infrastructure – Ensures the availability of security regardless of the presence of other infrastructures – × Expensive to deploy • Works efficiently if interactions are sporadic • Applications have full control over retransmissions. • SNMP/UDP may suffer from IP fragmentation 23 Related work • Session resumption for the secure shell protocol http://dx.doi.org/10.1109/INM.2009.5188805 Thank you! Question? 24