data-security
advertisement
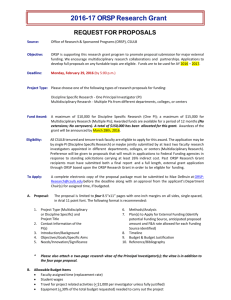
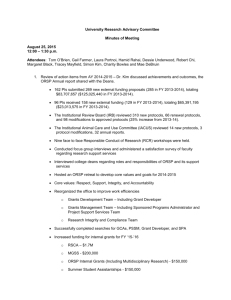
Data Security Overview ORSP Staff AT Desktop Service Team November 18th, 2014 Objectives ORSP staff will be able to: • Recognize confidential data • Understand the risks of exposing confidential data • Facilitate a dialog within ORSP for increasing security of confidential data 2 Why Data Security? 3 What Is Confidential Data? • Passwords, credentials, or PIN’s • Social Security Number and Name • Birth date + four digits of SSN and Name • Credit Card Numbers • Tax ID + Name • Driver’s License, State ID, Passport • Health Insurance Information • Medical or Psychological Counseling Records • Bank Account or Debit Card + access code • More…. 4 What Does It Look Like? Scanned ID for Travel Budget Spreadsheets (pre-2009) Invoices (Tax ID) 5 Why Bother? • Ethical: we care about the privacy of the records we handle on behalf of faculty, staff, and students • Trust and Prestige: the University is entrusted with personal information; ORSP granting authority • Disruption: when data is lost, lots of paperwork must be completed, processes changed • Financial: security Breaches are calculated as a cost per record (sample cost = $64 per record) Think about the institutions you transact with (banking, medical, etc.). How do you want your personal data handled? 6 ORSP and Risk Liability • 763,000 Social Security Numbers • 4,000 are Credit Card Numbers • 200 passwords (unanalyzed findings from sensitive data scan) Example cost: 50,000 SSN’s X $64 = $3,200,000 7 ORSP and Confidential Data If you’ve worked for ORSP for more than five years, you have confidential data in your file storage. • Payroll: SSN’s for faculty, staff, student employees, contractors, etc. • Fiscal: Vendor payment vouchers include Tax ID and business name • Travel: Passports, CaDL, State ID • Passwords: spreadsheets or text files with passwords to University system (or personal systems) 8 How Can I Protect My Work at ORSP? • Recognize confidential data • Remove unused/inactive confidential data files • Stop using confidential data files • Secure workstation, network, storage (AT Desktop) • Be cautious of email phishing • Do not leave workstation unattended while logged into sensitive systems 9 11 ORSP Next Steps 1. Reduce the amount of old or unneeded data in ORSP storage (and by proxy, reducing the amount of confidential data) 2. Identify where ORSP uses confidential data in its workflow (where it currently uses it, where it can cease to use it) 12 Reduce Inactive Data Review existing share folders to identify non-active folders/files and those that are no longer needed 13 Where Does We Use Confidential Data? • What ORSP work processes generated the confidential data? • Are those processes still required? 14 More Resources… CSU Skillport Training (will be replacing former ESIP training) 1.Visit https://ds.calstate.edu/?svc=skillsoft&org=sfsu 2.Select "San Francisco" 3.Login with your SF State ID and password 4.Select "My Plan" For FERPA training: * Find "FERPA" and click "Launch" For Data Security & Privacy Training * Find "Data Security & Privacy" and click "Launch" 15 For Questions, Contact: AT Desktop Service Phone: 415-405-5562 Email: at_desk@sfsu.edu Ticket: http://service.sfsu.edu 16