Protocols of Ad Hoc Network
advertisement

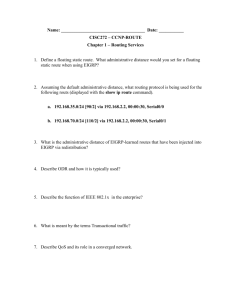
Introduction To Ad Hoc Networks and Routing Protocols Presented By : Karthik Samudram Jayaraman Introduction • What is Ad Hoc Network? • In Latin, ad hoc means "for this," further meaning "for this purpose only.” • All nodes are mobile and can be connected dynamically in an arbitrary manner. • No default router available. • Potentially every node becomes a router: must be able to forward traffic on behalf of others. Two types of wireless networks • Infrastructured network: A network with fixed and wired gateways. When a mobile unit goes out of range of one base station, it connects with new base station. • Infrastructureless (ad hoc) networks: All nodes of these networks behave as routers and take part in discovery and maintenance of routes to other nodes. Why is Ad Hoc hard? • Because of a constantly changing set of nodes – Routing is a major issue! • Security new vulnerabilities, nasty neighbors. • Power running with batteries, little computing power. The Desired Properties of Protocols (For Routing) 1. 2. 3. 4. 5. A routing protocol should be distributed. Assume routes as unidirectional links. Power efficient. Consider its security. Hybrid protocols can be preferred. Two Main categories of Protocols 1. Table Driven Routing Protocols Pro-active, learn the network’s topology before a forwarding request comes in 2. On-Demand Routing Protocols Re-active, become active only when needed Destination Sequenced Distance Vector Algorithm (DSDV) 1. Based on Bellman-Ford Next Hop Routing. 2. Each Node Maintains Tables for : A. Next Hop on Path B. Distance (in hops) to destination. C. Sequence Number ( keep current route) 3. Nodes Exchange Updates With Neighbours • Full Routing Updates • Incremental Updates DSDV contd… ClusterHead Gateway Switch Routing • Adds hierarchical structure having DSDV as • • • underlying routing algorithm. Routing is performed over clusterheads and not individual nodes. Requires Table to maintain cluster Membership, in addition to other routing tables. Cluster heads are selected by a Least Cluster Change Algorithm to minimize routing changes Wireless Routing Protocol • Each node maintains a distance table, a routing table, a link-cost table and a message retransmission list. • Distance table of node i: (matrix) For each destination j and each neighbor of i(k) • Distance to j Wireless Routing Protocol • Routing table of node i is a vector: • The destination’s identifier • The distance to the destination • The predecessor and successor of the chosen shortest path Wireless Routing Protocol • Link-cost Table: • The cost of relaying information through each neighbor • Message retransmission list: • One or more retransmission entries Wireless Routing Protocol • Information Exchanged among nodes: (routing table update messages ) • Identifier of the sending node • A sequence number assigned by the sending node • An update list of updates or ACKs to update message • A response list of nodes that should send an ACK to the update message Wireless Routing Protocol • Each node will communicate with its neighbors reporting any changes in the system • Each node will keep track of which node should send an acknowledgement • Nodes will keep track of the changes in the system by periodic transmission of ‘hello’ messages • This protocol will force nodes to do consistent check of their predecessor hence avoiding countto-infinity problem. DSDV DSDV is based on idea of classical Bellman-Ford Routing Algorithm Each node maintains a routing table listing all available destinations. The attributes of each destination are the next hop, the number of hops to reach to the destination, and a sequence number, which is originated by the destination node. Both periodic and triggered routing updates to maintain table Problems of Distance Vector Pro-active routing based on Distance Vector • Topology changes are slowly propagated • Count-to-infinity problem • Moving nodes create confusion: • they carry connectivity data which are wrong at new place • Table exchange eats bandwidth DSDV How DSDV addresses the problems? • Tagging of distance information: • The destination issues increasing sequence number • Other nodes can discard old/duplicate updates • Changes are not immediately propagated • Wait some setting time • Incremental updates instead of full table exchange What is “on-demand” • The routes are created when required • The source has to discover a route to the destination. • The source and intermediate nodes have to maintain a route as long as it is used. • Routes have to be repaired in case of topology changes. On-Demand Routing Protocols 1. Ad hoc On-demand Distance Vector 2. 3. 4. 5. Routing Dynamic Source Routing Protocol Temporally Ordered Routing Algorithm Associativity Based Routing Signal Stability Routing Ad Hoc On-demand Distance Vector Routing • AODV includes route discovery and route maintenance. • AODV minimizes the number of broadcasts by creating routes on-demand • AODV uses only symmetric links because the route reply packet follows the reverse path of route request packet. • AODV uses hello messages to know its neighbors and to ensure symmetic links. The source broadcasts a route packet The neighbors in turn broadcast the source RREQ packet till it reaches the destination destination RREP Reply packet follows the reverse path of route request packet recorded in broadcast packet The node discards the packets having been seen Route Maintenance • If the source node moves, it reinitiates the route discovery. • If intermediate node moves, its upstream node sends a RREP to the source. The source restarts the route discovery. Dynamic Source Routing Protocol • A node maintains route caches containing the routes it knows. • Include route discovery and route maintenance. Route discovery • The source sends a broadcast packet which contains source address, destination address, request id and path. • If a host saw the packet before, discards it. • Otherwise, the route looks up its route caches to look for a route to destination, If not find, appends its address into the packet, rebroadcast, • If finds a route in its route cache, sends a route reply packet, which is sent to the source by route cache or the route discovery. source broadcasts a packet containing address of source and destination source (1,4) 1 4 The destination sends a reply packet to source. 8 (1,3) destination 3 7 2 (1,2) (1,4,7) The node discards the packets having been seen 5 (1,3,5) 6 (1,3,5,6) The route looks up its route caches to look for a route to destination If not find, appends its address into the packet How to send a reply packet • If the destination has a route to the source in its route cache, use it • Else if symmetric links are supported, use the reverse of route record • Else if symmetric links are not supported, the destination initiates route discovery to source Route maintenance • Whenever a node transmits a data packet, a route reply, or a route error, it must verify that the next hop correctly receives the packet. • If not, the node must send a route error to the node responsible for generating this route header • The source restart the route discovery Add entries into route cache • The Source and destination in route discovery • Intermediate hosts in route discovery • The hosts receiving any broadcast Temporally Order Routing Algorithm • Creating Routes: query/reply • QRY packet is flooded through network • UPD packet propagates back if route exist • Maintaining Routes: link-reversal • UPD packets re-orient the route structure • Erasing Routes • CLR packet is floodthrough network to erase invalid routes The source broadcasts a QRY packet with height(D)=0, all others NULL (0,0,0,3,a) (-,-,-,-,a) source a (-,-,-,-,d) (0,0,0,2,d) QRY d Only the non-NULL node (destination) responds with a UPD packet. QRY QRY (-,-,-,-,c) (0,0,0,4,c) UPD h Dest. (0,0,0,0,h) c g (-,-,-,-,g) (0,0,0,1,g) b (-,-,-,-,b) (0,0,0,4,b) e (-,,-,-,-e) (0,0,0,3,e) f (0,0,0,2,f) (-,-,-,-,f) A node receiving a UPD sets its height to one more than UPD Source receives a UPD with less height TORA: Height metric • Each node contains a quintuple • Logical time of a link failure • Unique ID of the node that defined the new reference level • Reflection indicator bit • A propagation ordering parameter, height • Unique ID of the node Route Maintenance and Erasing • No reaction necessary if all nodes still have downstream links. • A new reference level is defined if a node loses its last downstream link. • Synchronized clock is important, accomplished via GPS or algorithm such as Network Time Protocol. • CLR packet to be flooded to clear the invalid packet. Link failure with no reaction (0,0,0,3,a) (0,0,0,2,d) a d h c Dest. (0,0,0,0,h) (0,0,0,4,c) g (0,0,0,1,g) b (0,0,0,4,b) e f (0,0,0,2,f) (0,0,0,3,e) Re-establishing route after link failure (1,d,0,-2,s) (0,0,0,4,s) s A new reference level is defined (1,d,0,-1,a) (0,0,0,3,a) (1,d,0,0,d) UDP (0,0,0,2,d) a d UDP h c Dest. (0,0,0,0,h) (0,0,0,4,c) g (0,0,0,1,g) b (0,0,0,4,b) e f (0,0,0,2,f) (0,0,0,3,e) Associativity Based Routing • Each route keeps a associativity table • A high value of associativity tick indicates a low state of node mobility • A route is selected based on associativity states of nodes, finds the high value of associativity tick (low mobility routes) Associativity table • All nodes generate periodic beacons • When a neighbor node receives a beacon, it increases its associativity tick with respect to the sending node in associativity table • Associativity ticks are reset when the neighbors of a node or the node itself move out of proximity Route Discovery • The source broadcast a QRY message • Each intermediate node appends its address and associativity ticks to QRY, • The destination can examine the associativity ticks to select route. If the multiple paths have the same overall degree of stability, select the minimum number of hops Route Erasing • If the the route is no longer desired, the source may not be aware of any route node changes because partial reconstruction. • The source node initiates a route delete (RD) broadcast to erase the invalid route. Conclusion • DSR has lower routing load than AODV Because AODV has to depend on route discovery more often, DSR limits the overhead by using route cache • TORA is higher because its overhead is the sum of neighbor discovery plus routing creating and maintenance • DSR and AODV perform well than TORA, delivering over 95% packet regardless of mobility rate. • TORA is lower because the link-reversal process fails in the routing maintenance. • TORA has a better performance in the less sources. Advantage and Disadvantage • The overhead of TORA is worst. It has a better delivery ratio in less sources. • DSR is good at all mobility rate and movement speed. Its performance is poor in a higher load. • AODV performs almost as well as DST at all mobility rates and movement. It depends more on route discovery which may increase overhead in • network Overview On-Demand Overall complexity Overhead Loop-free Beaconing requirements Multiple route support Routes maintained in Route reconfigurati on methodology Routing metric AODV Medium DSR Medium TORA High ABR High SSR High Low Yes No Medium Yes No Medium Yes No High Yes Yes High Yes Yes No Yes Yes No No Route table Route cache Route table Route table Route table Erase route; notify source Erase route; notify source Link reversal; route repair Localized broadcast query Erase route; notify source Freshest and shortest path Shortest path Shortest path Associativity and shortest path and others Associativity and stability Reference 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Routing Protocols for Ad Hoc Mobile Wireless Networt by Padmini Misra, ftp://ftp.netlab.ohio-state.edu/pub/jain/courses/cis78899/adhoc_routing/index.html#CBRP A Comparison of On-Demand and Table Driven Routing for Ad-Hoc Wireless Networks, by Jyoti Raju and J.J. Garcia-Luna-Aceves, http://www.soe.ucsc.edu/~jyoti/paper2/ A New Routing Protocol for the Reconfigurable Wireless Networks, Zygmunt J Hass Caching strategies in on-demand routing protocols for wireless ad hoc networks, by Yih-chun hu and Divid B. Johnson, http://monarch.cs.cmu.edu Highly Dynamic Destination-Sequenced Distance-Vector Routing for Mobile Computers, Pravin Bhagwat, Charles E. Perkins Dynamic source routing in ad hoc wireless networks, by David B. Johnson and David A. Maltz, http://www1.ics.uci.edu/~atm/adhoc/paper-collection/johnson-dsr.pdf A Performace Comparison of Multi-Hop Wireless Ad Hoc Network Routing Protocols, Josh Broch etc An Efficient Routing Protocol for Wireless Netwrok, Shree Murthy etc Temporally-Ordered Routing Algorithm (TORA) Version 1 Funtional Specification, by V. Park, S. Corson, http://www1.ics.uci.edu/~atm/adhoc/papercollection/corson-draft-ietf-manet-tora-spec-00.txt Ad Hoc On Demand Distance Vector (AODV) Routing, by Charles Perkins, http://www1.ics.uci.edu/~atm/adhoc/paper-collection/perkins-draft-ietf-manet-aodv00.txt Reference (cont.) 7. 8. 9. 10. 11. 12. 13. 14. An Introduction to Mobile Ad Hoc Network, by Ming Yu Jiang, http://kiki.ee.ntu.edu.tw/mmnet1/adhoc/ Scalable Routing Strategies for Ad hoc Wireless Network, by Atsushi Iwata , ChingChuan Chiang etc. A Performance Comparison of Multi-Hop Wireless Ad Hoc Network Routing Protocols, by Josh Broch, David A. Maltz, David B. Johnson, Yih-Chun Hu, Jorjeta Jetcheva, http://www1.ics.uci.edu/~atm/adhoc/paper-collection/johnsonperformance-comparison-mobicom98.pdf Fisheye State Routing: A Routing Schema for Ad Hoc Wireless Networks, by guangyu Pei, Mario Gerla, Tsi-Wei Chen A review of current Routing protocols for ad-hoc Mobile Wireless Networks, by Elizabeth M. Royer and C-K Toh http://www.cs.ucsb.edu/~vigna/courses/CS595_Fall01/royer99review.pdf CEDAR: a Core-Extraction distributed Ad Hoc Routing Algorithm, Prasun Sinha, Vaduvur Nharghavan, etc Mobile computing today & in the future, by M.J. Fahham and M.K. Hauge. http://www.doc.ic.ac.uk/~nd/surprise_95/journal/vol4/mjf/report.html Performance Comparison of On-demand Routing Protocols in Ad Hoc Network by Sohela Kaniz http://fiddle.visc.vt.edu/courses/ecpe6504wireless/projects_spring2000/pres_kaniz.pdf