Detecting
Anonymous Proxy
Usage
Final Report
Jonathan McKeague - B00443636
BSc Computer Science
School of Computing and Intelligent Systems
Faculty of Engineering
University of Ulster at Magee
Email: mckeague-j1@email.ulster.ac.uk
Date: 11/12/13
Supervisor: Kevin Curran
Abstract
The Internet is built atop the Internet Protocol (IP) which has at its heart a unique
identifier known as an IP address. The IP address serves two principal functions: host
or network interface identification and location addressing. IP addresses by
themselves do not point to specific geographical real-world locations by default but
they will be registered to specific geographical locations and so can be used for crude
or sometimes very accurate geographical location determination. Knowing the
location of an IP address can be very useful in many situations such as for banks to
know if a connection is in progress from online fraud hotspots. There exists a problem
however in that IP addresses can be spoofed. This allows hackers to bypass
geographical IP restrictions and thus render some category of fraud prevention
useless. Anonymous proxies (AP) which act as intermediate relays which disguise the
source IP addresses can play a large role in cybercrime. There is thus a need to
ascertain whether an incoming IP connection is an original source matched IP
address or one being routed through an anonymising proxy. This report concentrates
on various methods used by anonymising proxies, the characteristics of the
anonymous proxies and the potential mechanisms available to detect if a proxy is in
use. It outlines the prototype system specification in addition to future plans and
overall architecture.
1
Acknowledgements
Firstly I would like to thank my project supervisor, Dr. Kevin Curran, his guidance
and support throughout the project has been extremely helpful. He has been an
invaluable mentor to me and has always been very quick to respond to any queries I
had.
My friends and family have been there for me throughout and given me support when
needed, for this I am very grateful and wish to thank them also.
Declaration
I declare that this is all my own work and does not contain unreferenced material
copied from any other source. I have read the University’s policy on plagiarism and
understand the definition of plagiarism. If it is shown that material has been
plagiarised, or I have otherwise attempted to obtain an unfair advantage for myself or
others, I understand that I may face sanctions in accordance with the policies and
procedures of the University. A mark of zero may be awarded and the reason for that
mark will be recorded on my file.
Jonathan McKeague
2
Table of Contents
Abstract .......................................................................................................................... 1
Acknowledgements ........................................................................................................ 2
Declaration ..................................................................................................................... 2
Table of Contents ........................................................................................................... 3
Table of Figures ............................................................................................................. 6
1.
Introduction ............................................................................................................ 8
1.1
Project Aims and Objectives ........................................................................... 9
1.2
Chapter Overview ........................................................................................... 9
2. Literature Review................................................................................................... 11
3.
2.1
PHPProxy ...................................................................................................... 11
2.2
CGIProxy ...................................................................................................... 12
2.3
Glype ............................................................................................................. 13
2.4
Onion Routing and Tor ................................................................................. 14
2.5
SSL Proxy ..................................................................................................... 15
2.6
IP Blocking.................................................................................................... 16
2.7
Access Control Lists...................................................................................... 17
2.8
Geolocation Security ..................................................................................... 17
2.9
Base64 Encoding ........................................................................................... 18
2.10
Snort........................................................................................................... 20
2.11
Wireshark................................................................................................... 21
Requirements Analysis ........................................................................................ 22
3.1
Project Problem Statement ............................................................................ 22
3.2
Project Solution Overview ............................................................................ 23
3.3
Functional Requirements............................................................................... 23
3.3.1 User Requirements ...................................................................................... 23
3.3.2 System Requirements.................................................................................. 24
3
3.4
Non- Functional Requirements ..................................................................... 24
3.5
Hardware Requirements ................................................................................ 26
3.6
Software Requirements ................................................................................. 26
3.7
Development Methodologies ........................................................................ 26
3.7.1
3.8
4.
5.
6.
7.
Selected Methodology ........................................................................... 29
System Structure ........................................................................................... 30
Project Plan .......................................................................................................... 30
4.1
Milestones and Deliverables ......................................................................... 31
4.2
Project Plan ................................................................................................... 31
4.3
Time Management......................................................................................... 33
4.4
Working with Supervisor .............................................................................. 34
4.5
Risk Management .......................................................................................... 35
Design .................................................................................................................. 37
5.1
Monitoring Network Traffic.......................................................................... 37
5.2
Software used ................................................................................................ 38
5.3
System Design ............................................................................................... 38
5.4
Log Files ........................................................................................................ 41
Implementation .................................................................................................... 42
6.1
Wamp Server ................................................................................................. 42
6.2
Network Packet Capturing ............................................................................ 43
6.3
Glype Proxy Detection .................................................................................. 45
6.4
PHPProxy Detection ..................................................................................... 49
6.5
CGI Proxy Detection ..................................................................................... 50
6.6
Tor Browser Detection .................................................................................. 53
6.7
Limiting the result log ................................................................................... 56
Testing.................................................................................................................. 59
7.1
Normal Browsing Test .................................................................................. 59
4
7.2
Glype Proxy Test ........................................................................................... 60
7.3
PHPProxy Test .............................................................................................. 61
7.4
CGI Proxy Test.............................................................................................. 63
7.5
Tor Browser Test ........................................................................................... 65
7.6
Further System Tests ..................................................................................... 67
8.
Evaluation & Reflection ...................................................................................... 70
8.1
Functional Requirements Evaluation ............ Error! Bookmark not defined.
8.2
Non-Functional Requirement Analysis ......... Error! Bookmark not defined.
8.3
Evaluation Summary ..................................... Error! Bookmark not defined.
8.4
Future Work and Enhancements ................................................................... 71
10.
References ......................................................................................................... 73
11.
Appendices ........................................................................................................ 76
Appendix A: Source Code ....................................................................................... 76
Appendix B: Network Packets containing the different proxies ............................. 82
Appendix C: Instruction Set..................................................................................... 98
5
Table of Figures
Figure 1 - PHPProxy Website ...................................................................................... 11
Figure 2 - Tor Browser Usage ..................................................................................... 14
Figure 3 - Base64 index ............................................................................................... 19
Figure 4 - BASE........................................................................................................... 21
Figure 5 - Wireshark .................................................................................................... 22
Figure 6 - Waterfall Development ............................................................................... 27
Figure 7 - Iterative Development ................................................................................. 27
Figure 8 - Spiral Development ..................................................................................... 28
Figure 9 - Rapid Application Development ................................................................. 28
Figure 10 - Use Case Diagram ..................................................................................... 30
Figure 11 - Work Breakdown Structure....................................................................... 32
Figure 12 - Gantt Chart ................................................................................................ 32
Figure 13 - Wireshark Packet Capture ......................................................................... 37
Figure 14 - Network Interfaces .................................................................................... 39
Figure 15 - System Flow .............................................. Error! Bookmark not defined.
Figure 16 - Wamp Server Menu .................................................................................. 42
Figure 17 - Wireshark Capture Screen......................................................................... 43
Figure 18 - Creating Directory and Log ...................................................................... 44
Figure 19 - Scanning for Network Interfaces .............................................................. 45
Figure 20 - Glype Regular Expressions ....................... Error! Bookmark not defined.
Figure 21 - Glype Matching Statement ........................................................................ 47
Figure 22 - Code to print to the console if a Proxy was found .................................... 48
Figure 23 - Glype Proxy Usage Detected .................................................................... 48
Figure 24 - PHPProxy Regular Expression and Matching Statement ......................... 49
Figure 25 - PHPProxy Usage Detected ........................................................................ 50
Figure 26 - CGI Regular Expressions and Matching Statement .................................. 52
Figure 27 - CGI Proxy Usage Detected ....................................................................... 53
Figure 28 - Tor Regular Expression and Matching Statements ................................... 55
Figure 29 - Onion Routing Usage Detected ................................................................. 56
Figure 30 - Code to Check the IP................................................................................. 57
Figure 31 - Print Statement if the IP is already in the log............................................ 57
6
Figure 32 - Pass rate for both the PHPProxy and Glype Proxy ................................... 62
Figure 33 - Pass rate for the SSL CGI Proxy and the Unsecure CGI Proxy................ 64
Figure 34- Full proxy/onion routing results ................................................................. 66
Figure 35 - Pcap error .................................................................................................. 67
Figure 36 - Testing every proxy at once with continuous usage ................................. 68
Figure 37 - CGI Proxy continuous use ........................................................................ 69
Figure 38 - PHPProxy continuous use ......................................................................... 69
Figure 39 - Glype continuous use ................................................................................ 69
Figure 40 - Onion routing continuous use ................................................................... 69
7
1.
Introduction
When the internet was first being developed back in 1958 as a means for
communication, it was inconceivable the success that it would have worldwide
(Mallia, 2013). Over 2.7 billion people now access the Internet daily (ITU, 2013).
When you compare this to the Internet usage in 1990, which was 3 million people
worldwide (SASI, 2006); you can see a stark difference. Whether Internet users are
checking and sending emails, reading an online newspaper, researching, doing online
shopping or online banking, the need for a secure system is a major challenge for
those who develop internet security systems. This is especially true for users that use
the internet to do business, or send private information, as more people are finding
different ways to ‘hack’ into secure servers and exploit vulnerable data. In 2011
alone, the total amount that was stolen from businesses online amounted to $3.4
billion, which was up by $700 million from 2010 (Neustar, 2012). This figure is only
going to increase, with businesses using the internet more to do the majority of their
business. This increase in business activity online could lead to more criminals
targeting online businesses; it is therefore a priority for businesses to invest in
methods to protect themselves against such attacks.
Internet misuse is also a major headache for employers due to the increase in
popularity of websites such as Facebook, YouTube, Twitter and Google+. This has
led to a decrease in the productivity of their employees, which in turn leads to less
profit, and more loss. Network administrators have therefore had to block many of
these websites from being used in the workplace in an attempt to mitigate the
problem. Initially they attempted to simply block the IP of the websites. IP addresses
are registered to specific geographical locations, although they don’t give the exact
area of where the user is located. However it does pinpoint the country that is
accessing the network (Goralski, 2008). IP blocking worked quite well, as anytime a
user tried to access a website that had its IP blocked they would be denied access.
This prompted users to try to find a way around the blocked IP’s.
One simple method was the use of a proxy. A proxy website masks the IP of the
website that you are trying to view, which bypasses the IP blocking method used to
detect the blocked website. Due to an increase in online banking, banks themselves
have had to increase security in their systems and networks; examining IP’s is one
8
method they utilize. If a user is making a transfer online and the IP looks fraudulent,
then the account holder will be contacted before the transfer is verified.
There are thousands of free PHP/CGI proxies to use online, making it a simple way to
bypass this basic security feature. Even if the proxy server that was used was blocked
there are thousands more to choose from, making the task of blocking them difficult
(Lyon, 2009). The code for all of these proxies is open source, it can be downloaded
and setup with ease, which means that anyone with a computer could theoretically
create a proxy server. Another method that can be used to bypass security measures is
Onion Routing (e.g. Tor Browser) which is used to anonymize a user’s traffic on the
internet. This method uses a different port than what is typically used to access
blocked websites. Onion Routing works by routing internet traffic through many
different hosts, encrypting data at each different host (Dingledine et al, 2004).
1.1
Project Aims and Objectives
Once the different anonymous proxies, and some of the methods used to tackle the
security risks in the system have been discussed, a new system called DetectProxy
will be detailed. The system will detect if any proxies are being used in the network
by comparing the characteristics of the different proxies. This will be accomplished
by analysing the packets entering the network using scripts to determine the type of
proxy being used. Once the proxies have been identified, information will be sent to
the network administrator. They will then be able to examine the time the proxy was
in use and will give them the option to block the proxy if the proxy has been
determined to be harmful or not needed on the network. Blocking the proxy will
provide a more secure network for the business or institution.
1.2
Chapter Overview
Chapter two will outline the main proxies that are available to users to access
restricted websites on a network. It will discuss the different methods used to prevent
proxy use on a network. An overview of some of the more useful tools that can be
used will also be provided. Chapter three will discuss the project problem statement
and how this will be overcome; it will also discuss the functional/non-functional
9
requirements of the project, the development methodology, and finally the hardware
and software that will be required to implement the system. A project plan will be
drawn up in chapter four which will outline the different parts of the project that
needs to be completed, as well as a timetable of when each of the different parts
should be completed. Chapter five will provide a conclusion of the topics discussed in
the previous chapters.
10
2. Literature Review
This literature review will be split up into two different sections. The first section will
discuss the different ways people can access networks and systems using anonymous
proxies. The second section will discuss the different ways of stopping or blocking the
anonymous proxies and the different tools used to aid this. Some of the main proxies
or ways to access the Internet anonymously are PHPProxy, CGIProxy, Glype, Onion
Routing/Tor and SSL Proxy.
2.1
PHPProxy
PHPProxy is one of the most commonly used Anonymous Proxy Servers. The code is
written in PHP and can be obtained from SourceForge1. It can run on Windows, BSD
(Berkeley Software Distribution), Solaris and Linux platforms, therefore making it
possible to run on the majority of platforms. When taking a closer look at the statistics
of the amount of times the code has been downloaded, we will see that over the past
year there has been a gradual decrease, with the most downloads being 573 in one
month and the lowest being 243, these statistics can be found on the SourceForge
website2. A sample of a proxy website that uses PHPProxy can be found at http://wbproxy.com/. This website simply allows the user to enter the URL destination that
they would like, once entered it will re-direct the user to their website; this can be
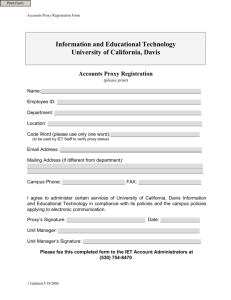
seen in Figure 1.
Figure 1 - PHPProxy Website
1
2
http://sourceforge.net/projects/phpproxy/
http://sourceforge.net/projects/phpproxy/files/stats/timeline?dates=2012-11-12+to+2013-11-12
11
The resulting URL when the user clicks ‘Browse’ is as follows:
http://wb-proxy.com/index.php?q=aHR0cHM6Ly90d2l0dGVyLmNvbS8%3D
The PHPProxy server obfuscates the URL to Base64 encoding; this means than any
network administrators that use keyword analysis methods of blocking websites will
not be able to block this method.
Upon further inspection of the proxy URL, it can be split up into three parts. The first
part is the hostname, which is http://wb-proxy.com, the second part is ‘index.php?q=’
and then the third part, the obfuscated URL, which in this case is
‘aHR0cHM6Ly90d2l0dGVyLmNvbS8%3D’. When the obfuscated URL is put in a
Base64 encoder/decoder3, the outcome is ‘https://twitter.com/’.
Base64 encoding is particularly important when the PHPProxy server is being used, if
it
wasn’t
used,
the
URL
would
be:
‘http://wb-
proxy.com/index.php?q=https://twitter.com/’. This would be easily detected by a
keyword analysis program and blocked.
2.2
CGIProxy
One of the main differences between the PHPProxy and the CGIProxy is the language
used when it is coded; PHPProxy used PHP, while CGIProxy uses PERL. CGIProxy
was created by James Marshall back in 1998 and can be downloaded from his
website4. Another notable difference between PHPProxy and CGIProxy is that the
CGIProxy doesn’t obfuscate the URL unless it is programmed to do so. This means
that the programmer who is setting up the CGIProxy will have to customise the code,
so that it obfuscates the URL. It can be used as a HTTPS, HTTP or FTP Proxy. There
are three main ways to encode the URL, these are: Base64, ROT-13 and Hex. In
PHPProxy, it solely uses Base64. A sample of a CGIProxy website that encodes the
URL is https://scusiblog.org/proxy/nph-proxy.cgi.
When www.twitter.com is entered into the website, the outcome is as follows:
3
4
http://www.motobit.com/util/base64-decoder-encoder.asp
http://www.jmarshall.com/tools/cgiproxy/
12
https://scusiblog.org/proxy/nph-proxy.cgi/0/68747470733a2f2f747769747465722e636f6d2f
From this we can see that the obfuscated URL is completely different from that of a
PHPProxy altered URL. When the URL is split down the ‘-0/’ can be removed from
the
hostname,
leaving
‘68747470733a2f2f747769747465722e636f6d2f’.
This
particular CGIProxy uses hex encoding, therefore entering the string into a hex
decoder5 will leave you with ‘https://twitter.com/’. The two URL’s that are created
by both PHPProxy and CGIProxy are completely different, however the result from
both are exactly the same. The CGIProxy if it had Base64 encoding would be very
similar to that of the PHPProxy.
2.3
Glype
Glype is a web proxy that has been coded in PHP. Glype was first released in 2007
and since then there has been over 721,000 downloads of the code6. When looking
through a list of different proxies7, Glype in particular stands out as being one of the
most popular choices for hosting a proxy server. Glype is very similar to PHPProxy, it
uses PHP as its programming language and it uses Base64 to encode the obfuscated
URL. The main difference between the two is the encoded URL; the encoded URL
appears different from that of a PHPProxy encoded URL. An example of a Glype
powered anonymous proxy can be found at https://branon.co.uk/glype/desktop-free/.
As before in the other proxy websites, the user can enter in the website they want to
view and just click ‘Go’, this will bring them straight to their destination webpage.
When www.twitter.com is entered into the website, the resulting URL is as follows:
https://branon.co.uk/glype/desktopfree/browse.php?u=czovL3R3aXR0ZXIuY29tLw%3D%3D&b=1
When you extract the encoded URL that contains the Base64 encoded string and
compare it with the encoded URL from a PHPProxy, you can see the difference.
However upon decoding the URL the result is exactly the same. Decoding
‘L3R3aXR0ZXIuY29tLw’ with a Base64 decoder simply leaves ‘/twitter.com’, the
rest of the data in the encoded URL is just extraneous data.
5
http://www.string-functions.com/hex-string.aspx
http://www.glype.com/
7
http://www.proxysiteslist.net/category.php?id=45
6
13
2.4
Onion Routing and Tor
Onion Routing sends data through a network of nodes/servers, each node encrypts the
data once it receives it, the data goes through a series of different nodes, until it
reaches the exit node (Lee, 2013). When the exit node is reached the data is then
decrypted. The ‘Onion’ part refers to the various layers of encryption that takes place
when moving through the different nodes. As each of the nodes encrypts your data,
this makes the data virtually impossible to trace (Chaabane et al, 2010). Onion routing
also uses several different ports on your computer to access the Internet, this makes it
more difficult for network administrators to monitor traffic, as it will not only be
going through the normal port for internet browsing, which is port 80 (Reed et al,
1998).
The Tor Browser was originally called TOR, which stood for The Onion Router (Li et
al, 2011). The Tor browser is exactly like any other web browser; however the main
difference between it and Chrome/Safari/Opera is that the user can surf anonymously.
The Tor browser was first released in 2002. It was originally developed with the U.S,
Navy in mind, for the purpose of protecting government communications. Originally
this was its main use, however in more recent times; the popularity of the Tor
Browser has steadily grown, with more people growing concerned about their online
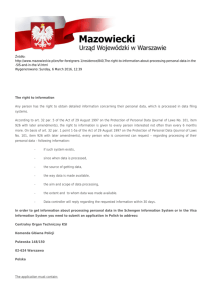
privacy. Figure 2 shows the huge increase in the amount of people using the Tor
Browser, one of the main reasons behind this is the NSA surveillance revelations
(Dredge, 2013).
Figure 2 - Tor Browser Usage8
8
https://metrics.torproject.org/users.html?graph=userstats-relay-country&start=2012-11-14&end=2013-1114&country=all&events=off#userstats-relay-country
14
The Tor Browser bundle is simple to setup and can be downloaded directly from the
Tor website9. Once the bundle has been installed the user is presented with the Vidalia
Control Panel from there they can connect to the Tor Network. While browsing the
Tor Browser, users can access thousands of websites that they cannot view on a
normal web browser. A typical URL on the Tor Browser looks like this:
http://kpvz7ki2v5agwt35.onion/wiki/index.php/Main_Page. If the URL is entered into
Chrome, it will bring up no results. Most of the websites on the Tor Browser use
‘.onion’. The high level of security provided by the Tor Browser may suit some
organisations who want to send data through a secure network, however blocked
websites can also be accessed through the browser, therefore a way of determining
whether someone is using the browser is a must.
2.5
SSL Proxy
A Secure Sockets Layer (SSL) is the standard way to get an encrypted link between a
web browser and a web server10. Whenever a user accesses a SSL Proxy, they will be
using ‘HTTPS’. Since the Proxy is using SSL it will encrypt the URL with 265-bit
encryption, making it virtually impossible to detect in a network. One of the main
problems associated with SSL Proxy’s is the cost. SSL certificates are expensive and
most anonymous web proxies will not pay for them, as they are trying to provide a
free
service.
Some
of
the
SSL
Proxy
sites
that
do
charge
(http://www.slickyproxy.com/ is an example), can be easily blocked by a network
administrator, as it will be a static URL. Even if a free proxy is blocked by a network
administrator, ten new proxies will replace it. The main income that the free SSL
proxies such as thesslprxy.com https://www.thesslproxy.com/ will get is from
advertising. When entering www.twitter.com into the proxy website, the resulting
URL
is:
https://www.thesslproxy.com/browse.php/CiNBfghu/8_2FLToI/
7Me2cWjh/YpqKxM7W/8dVJGzXr/W1/b29/#.UoOc9vm-2m4
In comparison to the other proxies in this paper, we can see that this obfuscated URL
is completely different. This is nearly impossible for a keyword analysis filter to pick
up, however due to the lack of availability of SSL Proxies; many of them can be
blocked, making a SSL proxy an unviable option.
9
https://www.torproject.org/projects/torbrowser.html.en#downloads
http://www.digicert.com/ssl.htm
10
15
2.6
IP Blocking
IP blocking is one of the most common and basic methods of blocking, filtering or
censoring IP addresses that may potentially have a bad effect on the network/server
(Thomas et all, 2011). When using this method of security, a network administrator
can block a single IP or many different IP addresses from accessing the network, or
certain parts of the network, depending on the level of security needed. Whenever the
administrator has a list of blocked IPs in the network identified, anyone on the
network who tries to access any of the IP addresses will be blocked from doing so
(Murdoch & Anderson, 2008). Network administrators can also block IPs from
accessing their network, this means that any IP not in the network that is blocked, will
not be able to access their network. This is very useful if the network administrators
have identified an IP that is trying to cause problems within the network. Companies
such as Yahoo and Joomla have detailed measures in place for IP blocking, for
instance Yahoo has a service for users who have a store set up with them in their
Merchant solutions section11. Within this there is admin tools that are very useful, one
of them is a section where you can enter IP addresses that you would like blocked.
Firstly you have to find the details of the IP you want to block using the DNS lookup,
again provided by Yahoo. This will provide the IP address needed in order for you to
block it. Yahoo allows up to 25 IP addresses to be added to the block list at once,
however it does have its restrictions, one of them is the fact you can only block 150
IPs in total.
Joomla is another company that provides solutions for IP blocking to its customers.
Joomla is a content management system (CMS); they allow users of their product to
build websites and other applications online12. They also have extensions that can be
added onto the websites that are created, some of these include: content restriction,
email authentication, content protection and IP blocking. In the IP blocking section,
they have different types of extensions that can be added to the website, these are:
Country/IP Block, Jban, GeoBlocker, CFBlockCountry, Um Ban, TorlpBlock and Ju
BlockIP13. These extensions can be very useful when combined, for instance, if you
did not want a certain country accessing your network, CDBlockCountry should be
11
http://help.yahoo.com/l/us/yahoo/smallbusiness/store/risk/risk-18.html
http://www.joomla.org/about-joomla.html
13
http://extensions.joomla.org/extensions/access-a-security/site-access/ip-blocking
12
16
used, this extension will filter out any IPs from the country you want blocked and will
not allow access to them. IP Blocking is a simple method of stopping a user from
accessing a network, as it will make sure that the IP that is listed to be blocked is
indeed blocked; however this form of security is easily bypassed with the use of a
proxy.
2.7
Access Control Lists
An Access Control List (ACL) is used by network administrators as a way of allowing
different ports on user’s local machines to be accessed or opened. The ports that are
included in the ACL are called access control entries (ACE) (Microsoft, 2013).
Whenever a user’s port is included in the ACL, they are allowed to access the
network, however any application used by the user will also have to be included in the
ACL, this is due to the security in the ACL being very rigid. When a port that is not
included in the ACL tries to access the network, it will be blocked straightaway.
Although this shows that the ACL is actually working properly, a valid user who is
using a port that is not on the list will find themselves being unable to access the
network, they will have to contact the administrator to add them to the list. This may
take some time, depending if the network administrator is onsite or if it is part of a
major multi-national company. An example of a company that focuses on providing
an ACL service to companies is Cisco. Within their ACL’s, they have different
criteria that has to be met when setting up the lists (Cisco, 2006).
A network
administrator can set up many different ACL’s for different departments within the
one company, for example, if a company has 2 departments (Research &
Development, and Government), a network administrator can specify if a port can
access both of the departments or only just one of them. If the administrator does not
include the port in the list then the access to the two departments will be denied. In
large companies that have many different networks and sub networks, setting up an
ACL can take a lot of time (Lee et al, 2005).
2.8
Geolocation Security
Location Based Services (LBS) such as Parcel Tracking, Indoor Positioning, GPS
Navigation and accessing networks have become a vital occurrence in some people’s
lives. Most if not all new smartphones come with GPS abilities inbuilt in them. People
often track their parcels to have an idea of when they might arrive or to find out what
17
is causing a delay in their delivery. Indoor Positioning systems such as SeniorLab14,
Pole Star15 and IndoorAtlas16 have all become very popular products over the past two
years, as the indoor positioning market has seen a sharp rise, with more shopping
centres, museums and airports using this new technology. Another useful service in
the Location Based Services section is Geolocation Security. Within Geolocation
Security companies can monitor who accesses their networks and sometimes block
certain users from accessing the networks based solely on their location. If a company
was being attacked by a hacker, the network administrator can look at the IP address
of the hacker, find out what country the IP is located in and block the IP addresses
associated with that country for a brief period of time until the attacks stop
(Kibirkstis, 2009).
One of the main companies that supplies software in the field of geolocation security
for online applications is Neustar, formally known as Quova. One of their main
products is IP Intelligence. This product provides the company using it with data on
their customers, where they are and what they are using to connect to the web. Having
access to this information makes it easier for companies to block transactions that
they deem suspicious. Gmail also uses Geolocation Security, Gmail will monitor the
user’s main IP address logins and will then contact the user if a suspicious IP address
has tried to access the account, and this gives the user a chance to change their
password before the hacker can access their email17.
2.9
Base64 Encoding
Base64 encoding takes a string of text data and changes it into ASCII format. One of
the main reasons for changing the text data to ASCII is so that when messages are
being sent through a network that generally deals with text, it can be sent through
securely (Knickerbocker et al, 2009). Base64 encoding is very useful when it comes
to bypassing IP Blocking or blacklist filtering, for example, when you enter
www.twitter.com into a Base64 encoder, you get the following output:
d3d3LnR3aXR0ZXIuY29t. Many proxy websites will use this form of encoding to
bypass any filters on the network.
14
http://www.senionlab.com/
http://www.polestar.eu/en/
16
https://www.indooratlas.com/
17
http://arstechnica.com/security/2010/03/googles-new-gmail-geolocation-feature-aims-to-preventscams/
15
18
To convert text over to Base64 format, firstly you have to change each character to its
equivalent ASCII value. Once the ASCII value is got, it will be changed into 8-bit
binary format. Each 8-bit binary is split into 6-bit binary groups; each 6-bit binary
number is converted into a decimal number. The decimal number is then compared
with the Base64 index table, which is shown in Figure 3.
Figure 3 - Base64 index18
Table 1 shows steps involved in converting ‘www’ to Base64 encoding. The reason
why the binary number is split into 6-bit is so that all the Base64 values can be
represented. The maximum binary value in 6-bit format is 111111, which when
converted to decimal format equals 63, the biggest value in the Base64 index.
Letter
ASCII
Binary
Divided Binary
Decimal
Base64 encoded
W
119
01110111
011101
29
D
W
119
01110111
110111
55
3
W
119
01110111
011101
29
d
110111
55
3
Table 1 - Base64 encoding
A major security risk can be PHP obfuscation; Base64 encoding can be used to do
this. The code in some of the web-based programs can be made extremely difficult for
a human to read if it is converted to Base64, therefore rogue code, or code that can be
harmful can make its way onto the machine without the user or some security
software knowing (Raynal et al, 2012). However changing the code to Base64 can
18
http://janav.files.wordpress.com/2013/05/base64chars.jpg
19
sometimes be quite a tedious task, and mistakes can often occur. In HTML5, there has
been two methods created that has allowed developers change the pages content to
and from Base64 encoding. These two methods are atob() and btoa()19. These two
methods are very useful when looking to change binary to Base64 and vice-versa.
2.10 Snort
Snort is an open source network intrusion detection and prevention system that was
created by Martin Roesch and released in 1998; the Snort program is able to run
quietly in the background, providing real time traffic analysis and packet logging
within networks20. Snort has many useful capabilities in terms of detecting attacks and
probes, some of these include: Stealth port scans, Operating System Fingerprinting
attempts, Server Message Block (SMB) probes, Buffer Overflows and Common
Gateway Interface (CGI) attacks (Stanger et al, 2007). Sourcefire, a company that was
founded by Roesch, currently owns and continues to develop Snort. The program has
had millions of downloads and currently has nearly 400,000 registered users20.
Snort provides three different functions/modes, these are:
1. Sniffer Mode
2. Packet Logger Mode
3. Network Intrusion Detection System (NIDS) Mode
Sniffer mode reads all the packets that are going through the network; it will then
display all the packets that were read from the network on the console. This process
runs continuously until the user turns it off. Packet logger mode like the sniffer mode
will read all the packets going through the network; however it will save the packets
to a disk instead of displaying them continuously on the console. The NIDS mode will
monitor all traffic that moves through the network and will detect any intrusions that
occur. This is the most complex mode of Snort (Sourcefire, 2013). The installation of
the NIDS can be complicated; however there is a step by step guide in order for the
program to be installed correctly. SNORT can be used in conjunction with other
programs in order to analyse the data that is going through the network, an example of
one such program is BASE (Basic Analysis and Security Engine).
19
20
http://www.w3.org/html/wg/drafts/html/master/webappapis.html#atob
http://www.snort.org/
20
Figure 4 - BASE21
Figure 4 shows a simple screenshot of how the BASE system looks when it’s using
Snort. BASE is a web interface that analysis the intrusions that are detected from the
Snort IDS (intrusion detection system), within the program users can also use the
simple web-based setup program for those that might not be comfortable in editing
files22.
2.11 Wireshark
Wireshark is a network protocol analyser that was setup in 1998; it is currently one of
the most popular network protocol analysers in the world and has won many awards23.
The program records all the packets going through the network that is connected to
the local machine. This makes it easier for the user to analyse the different packets
and gain a better understanding of all the different packets.
21
http://base.secureideas.net/images/base-results-0.9.8.png
http://base.secureideas.net/about.php
23
http://www.wireshark.org/about.html
22
21
Figure 5 - Wireshark24
Figure 5 shows an example of a sample packet capture; from this you can see a
timestamp of the packet, the source and destination IP, the different types of Protocols
and some information about the packet. The user can also specify a certain IP or Port
number that they would like to monitor, this can be entered in the filter, for example if
the user entered ip.src==190.61.190.111 && tcp.port==80, this would filter the
program just to show traffic from the IP of 190.61.190.111 and through port 80.
3.
Requirements Analysis
The aim of the requirement analysis is to clearly describe the following in more detail:
The problem associated with the current ways to detect anonymous proxies.
How to improve on the current methods to provide the best solution in order to
detect the anonymous proxies.
The functional and non-functional requirements of the system.
The hardware and software requirements that are needed to create the system.
The different design methodologies available and which one suits the system.
A plan of the system’s structure.
3.1
Project Problem Statement
One of the major problems facing network administrators in organisations is being
able to block websites that are harmful or result in the loss of productivity. As
24
http://screenshots.en.sftcdn.net/en/scrn/34000/34498/wireshark-24.jpg
22
discussed in section 2.6 and 2.7 the main way to do this was through IP Blocking and
Access Control lists. These methods initially were quite successful; however with
more and more proxy URL’s popping up every day, having to continuously update
both these utilities is a burden on the network administrators in relation to the time it
takes, not to mention the company’s resources.
3.2
Project Solution Overview
The proposed project solution is to produce an intrusion detection system (IDS)
capable of detecting whether an anonymous proxy is being used in a network. Firstly
the system will monitor all the inbound and outbound traffic in the network, to do this
a program such as Wireshark or Snort can be used. Each of the two programs has
abilities to log all the information into a text file, this text file will contain all the data
that the IDS needs when it is running. The IDS will have string sets that will be able
to match up with the proxy server characteristics. The different anonymous proxies
and onion routing browsers will have different characteristics, once all of the
characteristics have been met, the IDS will alert the user that there has been a proxy
detected in the system. It will display what proxy or onion router is being used and
from the timestamp in the text file, the administrator will be able to find out when the
proxy was in use. The administrator will be able to add the proxy to a blacklist once
one has been found. The IDS will be able to run silently in the background, only
alerting the administrator when a threat has been found.
3.3
Functional Requirements
The functional requirements of the system are described below. When developing a
system within Software Engineering sector, the functional requirements are defined as
how the system behaves when it is being used. The functional requirements will be
split up into the user requirements and the system requirements.
3.3.1 User Requirements
This section will describe the user’s requirements, the user’s requirements will show
what the user should be able to achieve from the program. Listed below are the
different tasks the user will be able to do with the system.
Capture all the traffic within the network using Wireshark or Snort.
23
From the resulting text (.txt) file, the user will be able to insert it into the
command line program manually, or just let the program run on its own. The
program will have a real time analysis of all the packets in the network.
Receive feedback from the program if any proxies have been detected.
Be able to locate the exact time the proxy was in use and subsequently ban the
proxy if it is deemed to be used in an unsafe way.
Have an instruction set on how the system works, and how to troubleshoot any
problems.
3.3.2 System Requirements
This section outlines the system requirements; the system requirements outline the
different functionality within the system. These requirements are listed below:
An internet connection will be required for packets to be sent and received
through the network. The packets will then be logged through either
Wireshark or Snort.
The system will be able to accept text files and scan through them looking for
different character strings.
The system will store details of any proxies found, and let the network
administrator know if a proxy is found.
If the user enters an incorrect file into the system a warning message will be
shown.
3.4
Non- Functional Requirements
The non-functional requirements will show the performance characteristics or the
qualities of the system in question. The non-functional requirements of the system are
listed below.
Performance: The proposed IDS will have to run smoothly in the background, it
should be able to monitor the traffic in the system without causing the computer to
slow down. It should perform all the tasks mentioned above in the functional
requirements.
24
Accuracy: The system should expect to have one hundred per cent accuracy. The
system will be expected to show up all the proxies or onion routers that are being used
within the network. Accuracy is a vital requirement for this system.
Reliability: The system will be used on a daily basis by the network administrator;
therefore its reliability and error handling should be a priority. Any errors should be
handled appropriately and the user should be notified of what went wrong. If there is
problem that needs attention the user should have a popup appear to warn them.
Documentation: Each part of the system should be well documented, so the user
knows exactly what is happening when the system is running. There should be an
adequate troubleshooting guide to help the user if anything goes wrong in the
program.
Usability: The system will be quite simple to use, the system will generally be used
by network administrators, and therefore they should have a good technical
knowledge. The user guide will also contain a step by step guide on how to use the
system.
Effectiveness: The main problem is the use of anonymous proxies within a secure
network. The goal is for the system to flag up any proxies that are being used, to
examine where and why they are being used, and to block them if their usage poses a
security risk or it is being used to look at a banned site. The system will aim to detect
one hundred percent of the proxies, if that target is met, the system will be very
effective.
Maintainability: The user will be able to configure the system if it wants to let a
certain proxy through undetected. If a new type of proxy is created, once it’s
discovered how it works, it should be simple to add a script to the existing code in
order to detect it.
Capacity: If the network is very active, i.e. there is a lot of traffic entering/leaving the
network, then the logs from Wireshark/Snort could be quite large. However when the
machine is running normally, it should only store the details of any proxies detected;
therefore the file size should be smaller.
25
Platform Compatibility: The system will be developed on a Windows 7 platform
using the PERL language; it will work on any platform that supports that language.
The platform will also have to be able to support a network analyser.
3.5
Hardware Requirements
This section will show the different hardware that is required to develop and run the
system.
One PC or laptop running Windows 7 or Windows 8 is required to develop the
application; the recommended specification to develop the system is a 2GHz
i5 processor with 4GB ram.
One PC or laptop running Linux to test how effective the system is on other
operating systems.
Network connectivity so users can browse the web using a proxy or an onion
routing web browser.
3.6
Software Requirements
This section will outline the different software that will be used when developing the
system.
Strawberry Perl, this will be the main program used to develop the scripts.
Windows 7, this operating system will be used to develop the system.
PHPProxy Server, CGI Proxy Server, Glype Server, Tor Browser. All these
will be used to test the different types of proxies available.
Wireshark and Snort to analyse the packets that are being sent and received in
the network.
Web Browser to browse different websites when using the proxies.
VMware player to test the system out when using different operating systems.
3.7
Development Methodologies
In software development one of the most important things to consider is the
development methodology that is used. There are many different methodologies to
choose from, each should be looked at carefully before selecting the right one that
suits the system that is being developed. The methodologies structure out the
development of the system, they show how the requirements analysis, the system
26
design, the implementation of the system, the testing and the maintenance all work
together in order for the system to be the best it possibly can be. This section will take
a look at some of the main types of development methodologies, it will then show the
chosen methodology for this project and why that particular methodology was picked.
Waterfall Development
The waterfall development methodology goes through each phase of the project in
sequence; it will not go onto the next part of the project until the current part is
completed. The linear flow can be clearly seen in Figure 6. Once the first stage,
Requirements, is completed, it moves onto the second phase, which is the design
phase. The drop down between the stages is where it gets its waterfall name from.
This method can take quite a bit of time as the developer must make sure each phase
is
fully
completed
before
moving
onto
the
next.
If there are any problems in the initial phases, this could slow down the process in the
latter stages, which in turn might delay the completion of the project.
Figure 6 - Waterfall Development25
Figure 7 - Iterative Development26
Incremental Development
The Incremental Development method is both a linear and iterative methodology. It
goes through each phase in sequence; however it splits them up into smaller parts.
Once the process has gone through one full cycle, it goes back to the planning and
continues this until the system is perfected. This means the developers can analyse
25
26
http://rossgkinney.com/wp-content/uploads/2013/07/Waterfall_model_1.svg_.png
http://agile-development-tools.com/wp-content/uploads/2010/10/iterative-development1.png
27
their mistakes and correct them the next time around. Figure 7 shows all the different
phases involved in the method.
Spiral Development
The spiral development method which can be seen in Figure 8 is split up into 4
different sections, these sections are: Determine objectives, Identify and Resolve
risks, Development and Test and Plan the next iteration. The method iterates through
each phase creating a prototype each time before the operational prototype is created.
After the final prototype is created it goes through rigorous testing before it gets
released. This type of method is suited for a system that requires a lot of planning,
developing and testing, as each prototype is tested before the next one is planned.
Figure 8 - Spiral Development27
Figure 9 - Rapid Application Development28
Rapid Application Development
27
28
http://ultimatesdlc.com/files/2011/08/Boehm-Spiral-Model.jpg
http://www.el-dik.com/images/radd.png
28
The Rapid Application development method concentrates greatly on creating a lot of
prototypes and by splitting the project down into small parts. Figure 9 shows the
different phases involved in the method. The main reason behind splitting the project
into small parts is that if anything needs to be changed, it can be done so without
having too much of an effect on the project. Having many different prototypes is also
a good way to see how the project is developing. If the user is heavily involved in the
project, showing them how the system is progressing can be very useful.
3.7.1 Selected Methodology
The selected methodology for this system is the Waterfall Development
Methodology. The main reason behind the selection is the thoroughness in the design
phase. Any problems have to be solved before the next phase can be started, this
generally avoids any time being wasted in the later phases of the development. The
waterfall method is also a good method for time-keeping, the project at the beginning
can have a strict time-table, and the developer can judge how the system is
progressing. One of major disadvantages of the methodology is the fact that there will
be no prototypes before the final system is released. This can sometimes be
problematic as the developer will not know how the project is performing until the
testing/verification phase.
29
3.8
System Structure
In this section a use-case diagram will show how the system will work and how the
different parts of the system will be linked.
Network Administrator
Proxy Detected
DetectProxy Application
Network
User
Figure 10 - Use Case Diagram
The network administrator runs the DetectProxy Application on the network, when
the user connects to the network, the DetectProxy application scans the packets, if
there is a proxy detected, the details are stored and sent straight to the network
administrator.
4.
Project Plan
A project plan is an essential part of the development of any project. This project plan
is for the development of a system to detect anonymous proxy usage. The plan is split
up into five sections, these are:
Milestones and Deliverables
Project Plan
Time Management
Working with Supervisor
Risk Management
30
4.1
Milestones and Deliverables
Milestones
1. Completion of the Literature Survey
2. Completion of the requirements analysis and the project planning
3. Completion of the design phase and prototype
4. Completion of the testing phase and any further developments
5. Completion of the final project
Deliverables
1. Submission of the Interim report (11th Dec)
2. Submission of final report (2nd May)
3. Demonstration of working project (27th May)
4.2
Project Plan
The first task of a project plan is to create a work breakdown structure (WBS). This
will break the project down into lower levels to see what exactly needs to be done to
complete the project. The WBS of the project can be seen in Figure 11.
31
Figure 11 - Work Breakdown Structure
Figure 11 shows how the project will be broken down. This gives a better overview of
the task that is at hand. Figure 12 is similar to the WBS. It shows the main tasks in the
project that have to be completed. It also shows the length of time that should be spent
on each task.
Figure 12 - Gantt Chart
Tasks
Literature Search - The first part of the Interim report is to research the background of
the technology that will be used
32
Literature Review - Once the initial research is completed a review of the technology
will be carried out
Requirements Analysis - This part of the interim report is to see what the
requirements of the project are
Project planning - This section will create a detailed project plan based on the
requirements of the application. A time management schedule will also be created;
this is to insure the project stays on schedule.
Submit Interim Report - As it shows Figure 12, the Interim report is due on the
11/12/2013.
Design Anonymous Proxy Detection System - This section of the report will take into
consideration the requirements of the project and make a design of the application
Develop Application - Once the application is designed, the development can then
start
Testing - The application will be tested
Analysis - The results obtained from the application will be analysed
Complete Report - Once the results are analysed they can be documented in the report
and the rest of the report can be completed
Submit Final Report - As it shows in Figure 12, the final report is due on the
02/05/13.
Viva - This is a demonstration of the working application
4.3
Time Management
Time management is a vital part of any project. In order for this project to be
completed on time and to a very good standard, an analysis of how I spend my time
and how I should spend my time will be carried out.
The time log in Table 2 was created during a typical day that I have scheduled class.
33
Time
Activity
7.45-8.15
8.15-8.55
Get ready for university
Travel to campus
9.00-2.00
2.00-3.00
3.00-3.30
3.30-4.10
4.10-5.00
5.00-7.30
7.30-8.00
8.00-11.00
11.00-12.00
12.00-7.45
Effectiveness
Comments/ Improvements
70%
90%
Could do it in 15-20 minutes
Unfortunately due to traffic in
the morning, this can’t be
improved
Class
100%
Essential
Lunch
50%
I need to eat, however I could do
it in 30 minutes
Meeting with supervisor
75%
Vital meeting, however it could
be re-arranged to 2pm so I
wouldn’t be wasting time after
class
Travel home
100%
Since I leave before rush hour I
miss most of the heavy traffic
Watch television
20%
It’s good to have breaks,
however I’m also playing
badminton later in the evening
Work on project
70%
Should be spending more time
during the day working on the
project
Eat Dinner
100%
I need to eat dinner.
Play Badminton
50%
Could be limited to 2 hours to
get more rest
Work on project
30%
Too late to get anything
constructive done
Sleep
100%
Sleep is vital
Table 2 - Time Management
Table 2 shows a time log of the activities that I perform in an average day, the
effectiveness of the activities and some comments on the activities. Activities like
attending class are essential; however there are some activities that will need to be
improved. The meeting with the supervisor is vital, however if it was re-arranged it
would free up more time in the evening to work on the project or other assignments. I
usually play badminton 3 nights a week; this will have to be cut back to 2 nights a
week. I will also have to reduce the amount of hours I play each night so I don’t leave
myself too exhausted in the morning. Short breaks in between work are also useful to
keep the mind active, these should be limited.
4.4
Working with Supervisor
I have arranged with my supervisor to have a meeting every week. This meeting is
scheduled for Thursdays after class. The meeting is generally face to face, however if
either of us cannot make it or any major problems arise, we can keep in contact via
email or phone. Each meeting has to be well prepared for in order for me to get the
34
most out of the meeting. The supervisor has set out clear goals that he wants met for
the project. The first part of the project that has to be completed is the interim report.
Table 3 shows what has to be done before, during and after the meeting.
Before Meeting
During Meeting
Make sure all the tasks from
last week’s meeting are
completed
Make a list of any problems
encountered
Discuss possible solutions for Read over notes taken during
any problems encountered
the meeting
After Meeting
Discuss goals/tasks for next Create a list of the
week
goals/tasks required to be
completed
Make a list of any other Take notes throughout the Assess any risks that could
relevant questions
meeting
occur from the goals/tasks
Discuss any other questions
related to the project
Table 3 - Working with Supervisor
Table 3 outlines the main guideline to be taken when having a meeting with the
supervisor; however this can be altered if anything else related to the project occurs.
4.5
Risk Management
Risk management is an important part to any project. To ensure my project is
completed in time I have made a table to analyse the risks involved and to plan the
best way to overcome these risks. The possible risks that could occur in the project
can be seen in Table 4, this table is updated weekly after my supervisor meeting.
Risks
Event type
Classification
Trigger
Alleviate Method
Non-Technical
RAG
Grade
8
PC Failure
EvenDriven
Noticing
irregulariti
es with the
computer
Contingency- Have a backup
PC ready
Loss of work
due to virus
or crash
EventDriven
Non-Technical
10
N/A
Avoidance- Always back-up
work on USB pen and use
Google Drive
Illness
EventDriven
Non-Technical
3
N/A
Avoidance- Try to ensure
work is completed ahead of
35
Family Issue
EventDriven
Non-Technical
3
N/A
Insufficient
technical
ability
Evolving
Technical
15
Falling
behind
on
the project
plan
Evolving
Non-Technical
10
Unfamiliar
with
developme
nt
language
Milestones
taking
longer than
expected
Table 4 - Risk Management
36
schedule
Avoidance- Try to ensure
work is completed ahead of
schedule
Avoidance-Assign time to
complete more tutorials
ContingencyInform
supervisor about difficulties
AvoidanceKeep
monitoring the milestones
and try to get them
completed ahead of schedule
5.
Design
This section will detail the planning and design of the system. Within this section, the
technical details and the different software required for the system will be discussed.
It is important for network administrators to monitor traffic that is entering and
exiting the network. Security is very important therefore it is vital that any proxy or
onion routing applications used can be identified. If a proxy is in use, more often than
not it is not being used for legitimate reasons. There can however be a valid reason for
someone in the company to use a proxy, for instance, if they wanted to block certain
web scripts from being used or if they needed to test an application that is being
mistakenly blocked online, the user should contact the network administrator to allow
the blocked application to be made available, the latter however should not happen.
5.1
Monitoring Network Traffic
The first step in the design of the system is to monitor the network traffic. Programs
such as “Httpfox”, “Snort” or “Wireshark” can be used to monitor the traffic. This
category of program can ‘sniff’ the traffic on a continuous basis, which is ideal for
intrusion detection systems. An example of the data received when Wireshark is
sniffing the network can be seen in Figure 13. Included in the data is the Destination
IP, the Source IP, the Protocol and different information about each packet. All of
these different programs have the ability to save the network packets into a text (.txt)
file; this would make it easier for the IDS to read the packets.
Figure 13 - Wireshark Packet Capture
The first step in the design of the IDS was to examine the network packets and have a
good understanding of the data provided in each of the packets. Being able to
37
determine the relevant information in the packets would greatly reduce the time spent
when finding common sequences within the proxy packets. Therefore Wireshark
would initially be used to monitor the network traffic, with the results from the
monitoring displayed in a text file, this text file will be key to determine how to detect
an anonymous proxy. As the main program being used to ‘sniff’ the network packets
was Wireshark, the initial idea was that it could be used in conjunction with the proxy
detection script. This however meant that the program would not be standalone, which
would not have been ideal. As the IDS’s main purpose is to work on different
platforms as a standalone program, a program wrote in Python was used. This
program examined all the packets coming into and leaving the network. From this it
could be altered to print all the packets to a log file so they could be examined, or run
in the background scanning each of the packets as they entered/exited.
5.2
Software used
Python was used as IDS is run on multiple platforms as the network administrator
may be using more than Windows. One of the main libraries’ used in the Python
script is the Pcapy python library. Pcapy can be defined as follows “Pcapy is a Python
extension module that interfaces with the libpcap packet capture library. Pcapy
enables python scripts to capture packets on the network”29. The Pcapy library will be
used alongside other libraries in the script to produce the IDS. One of the other main
libraries is the ‘re’ library30. The ‘re’ library provides support for regular expressions
which will be used frequently within the script; these regular expressions will be used
to match different key words against words in the network packets.
5.3
System Design
The main flow can be viewed in Figure 15. The network administrator will start the
program running; they can do so by running it on the command line or using a python
program such as IDLE31, IDLE is the python IDE, it’s a multi-platform IDE with a
multi window text editor, it also has a python shell window, where the network
administrator can interact with the program. Once the program is started, a list of all
the available network interfaces is presented.
29
http://corelabs.coresecurity.com/index.php?module=Wiki&action=view&type=tool&name=Pcapy
http://www.regular-expressions.info/python.html
31
http://docs.python.org/2/library/idle.html
30
38
Figure 14 - Network Interfaces
Each of the available network interfaces is listed with a number, so the administrator
can select the interface they require, Figure 14 shows the list of interfaces that are
available to be selected. Unfortunately the list that is printed to the console is
unreadable, and can only be found through the Registry Editor. However as each of
the interfaces are listed in order, the administrator can go to ‘Control Panel\Network
and Internet\Network Connections’ and view each of the different network interfaces
available, the administrator can then count over and find the one that represents the
interface they require.
Once the interface is selected, the IDS starts scanning the network packets
continuously. When the script has started a new directory is created. This directory
stores all the log files that are created when the IDS is in use. Along with a directory
being created, a log file is created to store any proxies found when it is running. A
new log file is created each time the program is restarted, to differentiate between the
logs a date and time is supplied within the log file name. A list of common
characteristic strings that each of the different proxies has when the network packets
are traversing the network is necessary. Each of the proxies or onion routing
applications have their own unique characteristics which make them different from a
39
normal web browsing network packet. As each proxy has its own unique
characteristics, this however does not mean if one of the characteristics is found then
it is definitely a proxy. Each of the proxies have to match two or more of the
characteristics before they are flagged up to the administrator and printed to the log
file. As the program is designed to work in large networks, there could be many
different proxies or onion routing applications being used at the same time. Matching
the different characteristics and printing the result to the log is vital. As the program is
running continuously, each packet containing the matched characteristics will be
printed to the log, providing the type of proxy, the date and time each packet went
through the network and all the different information contained in the packet. This
information that is contained in the packet will allow the administrator to track down
the computer using the proxy and disable the access or query the usage of the proxy.
The time it takes from a proxy entering the network and it being logged should ideally
only be a few seconds; this enables the administrator to quickly find the proxy user.
Administrator starts
Enters the number of the network
the system
interface that they want to scan
System
scans the
network
User
No
presses
exit
No
Proxy
Found?
Yes
Print proxy to log
Is user
finished?
Figure 15 - System Flow
40
Exit
Yes
System
5.4
Log Files
As the system runs on a local machine the use of a database is not necessary. The IDS
stores each proxy found in a text file which is similar to the output received when
Wireshark is used to examine the network packets. However the size of the text file is
greatly reduced depending on how many proxies are in use on the network. The file is
designed with the user in mind and only the necessary details are printed to it. The
details that are printed to the log can be viewed in Table 5.
-Proxy Name
-Destination MAC
-Protocol
-IP Header Length
-Source IP Address
-Source Port
-Sequence Number
-TCP Header Length
-Host
-Accept (html, xml, etc.)
-Accept Encoding
-Cookie
-Date and Time of Proxy Usage
-Source MAC
-Version
-Time to Live (TTL)
-Destination IP Address
-Destination Port
-Acknowledgment
-Data
-User Agent
-Accept-Language
-Referrer
-Connection Type
Table 5 - Network Packet Details
A number of the packets may not contain all of the details that are listed in Table 5.
However they will contain the majority. The most important details contained in the
network packets are the Proxy Name, the Date and Time of Proxy Usage, the
Destination MAC, Source MAC, both the Source and Destination IP Addresses and
the Source and Destination Port. All this information should give the network
administrator enough details to track down the proxy usage.
Due to the large amount of network packets, if there is prolonged proxy usage without
the network administrator addressing the situation then the log file could become very
large and may take a while to open, therefore it is a good idea to monitor the program,
and restart it if the file is getting too big. Restarting the program will simply create a
new log file with a new timestamp.
41
6.
Implementation
This section of the report will look at the program in more detail; each of the different
parts discussed in the design phase will be documented, giving a more thorough
understanding of how the system works.
6.1
Wamp Server
As the proxies had to be hosted on a web server, a server had to be sourced. WAMP
v2.4 was the version used. It contains Apache 2.4.4, MySQL 5.6.12 and PHP 5.4.12.
Figure 16 - Wamp Server Menu
The wamp server menu can be seen in Figure 16, one of the main sections of wamp is
the www directory, and this directory is where each of the different proxies is stored.
Different versions of Apache and PHP can be downloaded and installed by selecting
the Apache folder/PHP folder then selecting the version. Selecting a different version
can be necessary for older versions of the proxy that may not be able to use the
newest version of PHP. To make sure the wamp server is working correctly, open a
web browser and in the address bar type in http://localhost, if the wamp server
homepage appears, the wamp server is working correctly.
When the WAMP server is functioning correctly, the proxies can be downloaded and
placed in the server, the Tor Browser can also be downloaded; however it does not
need to be placed within the server. The Tor browser can be downloaded directly
from the tor project website32. The download contains a Vidalia Control Panel and the
Tor web browser itself. Each of the three web scripts were downloaded next,
32
https://www.torproject.org/projects/torbrowser.html.en
42
PHPProxy33, Glype34 and CGIProxy35, all of the proxies were available to download
as a ZIP file, which can be extracted into the www directory on the wamp server. The
files however have to be edited before they can be used properly on the server. Perl
has to be downloaded before the CGI Proxy can be used; CGI functionality also has to
be enabled. PHP functionality has to be enabled before the PHPProxy and Glype web
scripts can be used. Whenever these steps are performed each of the web scripts can
be used to browse the internet anonymously. Free proxies can also be found online
that enable you to test the system and also to compare the network packets, there are
many lists that contain these proxies, a sample of the list can be found at
http://list.glype.com/.
6.2
Network Packet Capturing
When the proxies are running the network packets have to be captured, to do this
Wireshark had to be downloaded and installed36. The network protocol analysers
download package comes with WinPcap, which is needed for the live capture of
packets.
Figure 17 - Wireshark Capture Screen
After the download and installation was completed the program can be used straightaway. Figure 17 shows a list of the different connections that can be selected, for this
project the Wireless Network Connection was selected as the computer used was a
33
http://sourceforge.net/projects/poxy/?source=recommended
https://www.glype.com/download.php
35
http://www.jmarshall.com/tools/cgiproxy/
36
http://www.wireshark.org/download.html
34
43
laptop which was not connected to a wired network. Wireshark provides many
different options for when it is capturing the packets, as there can be hundreds of
packets coming into the system every few seconds, this can be very hard to read when
they are exported to a text file, therefore changing some of the options to limit the
packets captured is vitally important.
Wireshark was used to capture samples of packets from each of the different proxies
and also from the Tor browser. While doing this a Python program was acquired, this
code was also used to sniff for network packets. The code initially printed all the
packets out to the command line or to IDLE, as the code was open source it could be
edited which made using the code very convenient. It was decided to continue to use
the Python network analysis code as part of an integral part of the IDS. This meant the
use of Wireshark was no longer needed, as the desired outcome of the IDS was to be a
standalone system.
As the code just printed to the command line, this made it difficult to read the packets
and often caused the command line to freeze due to the large amount of packets in the
network. The first step was to get it to print the code to a log file. This was done by
creating a directory to store the log files in.
textTime = time.strftime("%H-%M-%S")
textToday = time.strftime("%d-%m-%Y")
directory = "C:\ProxyTempLogs"
log = open(directory + '\log_' + textToday + '_' + textTime + '.txt',
'w')
def main(argv):
if not os.path.exists(directory):
os.makedirs(directory)
Figure 18 - Creating Directory and Log
Once the directory was created it would be checked each time the program is run, just
to make sure it exists, if it doesn’t it will create it. The log file is the next item that is
created each time the program is started, this however is different from the directory
as it is not always static, the log file created will have the date and the time that it was
44
created in its unique name. Figure 18 shows the completed code that was used to
create the directory and the log files.
After the log file code was finished, selecting the network interface that needed to be
scanned had to be coded. The original code had the function to search for the network
devices, however selecting the devices when they were printed was time consuming.
devices = pcapy.findalldevs()
# No interfaces found
if len(devices) == 0:
raise RuntimeError, "Error: no available network interfaces,
or you don't have enough permissions on this system."
# A single interface was found
if len(devices) == 1:
interface = devices[0]
# Multiple interfaces found
else:
print "Available network interfaces:"
for i in xrange(len(devices)):
print '\t%i - %s' % (i + 1, devices[i])
print
while 1:
choice = raw_input("Choose an interface: ")
try:
i = int(choice)
if i == 0:
interface = None
break
interface = devices[i-1]
break
except Exception:
pass
# Return the selected interface
print "Sniffing device " + interface
Figure 19 - Scanning for Network Interfaces
The code in Figure 19 would simply scan through all the network devices and print
them to the console, giving each a number so the network administrator would be able
to select them easily, this saved a lot of time compared to having to write the device
you wanted to copy each time the program ran. Once these steps were completed the
network packets could be ‘sniffed’ and printed out to a log file for analysis.
6.3
Glype Proxy Detection
For each of the different proxies there were four different logs created to compare
each of the packets to find similarities within them that could be used to prove that
they are in fact a proxy. If any of the similarities are also contained in normal web
45
browsing packets then it may throw off the results, therefore getting the similarities to
be unique is a must. A sample of the network packets created by a Glype proxy is the
following:
“Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length
: 5 TTL : 128 Protocol : 6 Source Address : 192.168.1.100 Destination Address : 74.50.112.6Source Port : 25192
Dest Port : 80 Sequence Number : 515223919 Acknowledgement : 3525628824 TCP header length : 5Data : GET
/browse.php?u=%2FsytI4GTjHWo83ivVDOuRefK1x3c&b=29&f=norefer HTTP/1.1
Host: proxyserver.com
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:14.0) Gecko/20100101 Firefox/14.0.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://proxyserver.com/
Cookie: rbm8vrpt=XxmdVoc2ZEPzt8wx2hDaMDJmiVWg5Aw%3D;
__utma=231926494.1698960749.1393858908.1393858908.1393947133.2;
__utmz=231926494.1393947133.2.2.utmcsr=list.glype.com|utmccn=(referral)|utmcmd=referral|utmcct=/;
_referrer_og=http%3A%2F%2Flist.glype.com%2F; _jsuid=2791830717; __atuvc=3%7C10;
s=tg5ne8nbia564p5caugekb7pa3; __utmb=231926494.1.10.1393947133; __utmc=231926494; _first_pageview=1;
_eventqueue=%7B%22heatmap%22%3A%5B%7B%22type%22%3A%22heatmap%22%2C%22href%22%3A%2
2%252F%22%2C%22x%22%3A471%2C%22y%22%3A191%2C%22w%22%3A1024%7D%2C%7B%22type%2
2%3A%22heatmap%22%2C%22href%22%3A%22%252F%22%2C%22x%22%3A822%2C%22y%22%3A201%
2C%22w%22%3A1024%7D%5D%2C%22events%22%3A%5B%5D%7D
DNT: 1
Connection: keep-alive”
There are a few important things that can be seen from this packet. In comparison to a
normal web browsing network packet, there are a few common occurrences, one
being the destination port, which is port number 80. This is the port that is used for
most of the network packets, if the packets that are going through the network are
secure, then it would be going through port 443. Each of the packets viewed when the
Glype proxy was being run contained the command “GET”, and the protocol used
was “HTTP” the command and the protocol were contained within the data in the
packet. Another difference noticed in the packet was the use of “browse.php?u=”, in
particular ‘.php?u=’ was identified, this is mainly because the ‘browse’ can be called
anything as that is just the index page, therefore this may differ between the different
proxy servers. Once the three characteristics had been identified they could be used to
detect the Glype proxy.
46
The first action that had to be taken was to add the three different characteristics to a
list.
glypeStrings = (".*\.php\?u=.*(?i)\s", ".*GET.*(?i)\s",
".*HTTP.*(?i)\s")
Figure 20 - Glype Regular Expressions
To be able to search the proxies entering the system, after some research it was
decided it would be best to use Regex. To get started with regex, ‘import re’, was
added to the globals in the IDS code. Then the regex strings were created, these
strings were specifically created so they would ignore case sensitivity and also
whitespace. Figure 20 contains the criteria for the Glype string.
glype = [False, False, False]
glype[0] = re.match(glypeStrings[0], str(packet1)) # Search packet
for regex
glype[1] = re.match(glypeStrings[1], str(packet1)) # Search
packet for regex
glype[2] = re.match(glypeStrings[2], str(packet1)) # Search
packet for regex
if (glype[0]
and glype[1]
and glype[2]) :
result = 1
print >>log,
str("GLYPE: " + logTime + "\n" + packet1 +
"\n")
Figure 21 - Glype Matching Statement
After the regex list was completed it could be used to match against the network
packets. The regex will go through each different characteristic and try to match it
against
the
packet,
this
can
be
seen
from
the
line
‘glype[0]
=
re.match(glypeStrings[0], str(packet1))’, the string .php\?u=’ will be matched against
packet1. The code will then go through an IF statement, if all three characteristics are
found within the packet then it will make the result equal to 1, it will also print
‘GLYPE’ followed by the time the proxy was found and then the packet that the
47
proxy was found in to the log. The result will then be brought through another
function, which can be viewed in Figure 22.
while(1) :
time.sleep(0.05)
(header, packet) = cap.next()
parsedPacket = parse_packet(packet)
# Parse packet for suspect proxy data
result = isProxy(parsedPacket)
# Inform user if packet contained suspect data
if result == 0 :
# OK
#print(“No proxy detected”)
a = 1
elif result == 1 :
# GLYPE proxy
print("Glype usage detected")
Figure 22 - Code to print to the console if a Proxy was found
The result is passed through the loop, if it equals 1, then “Glype usage detected”
would be printed to the console. Figure 23 shows the messages appearing in IDLE as
the Glype proxy server is being used, each of the packets would be printed to the log.
Figure 23 - Glype Proxy Usage Detected
48
6.4
PHPProxy Detection
The detection method of PHPProxy is very similar to the detection of Glype. One
sample of the network packet when a PHPProxy is being used is as follows:
‘Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.144Source Port :
28271 Dest Port : 80 Sequence Number : 882310268 Acknowledgement : 2522902821 TCP header length : 5Data
: GET /index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20v HTTP/1.1
Host: proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.146 Safari/537.36
Referer: http://proxyanonymizer.net/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8’
The protocol used in the packet is ‘HTTP’ and the command is ‘GET’, the only
difference between the 3 characteristics of Glype is the third characteristic. In the
packet ‘index.php?q=aHR0c’ is the common occurrence in the different log files.
Again, the ‘index’ part of the string can be dropped as it can vary between the
different proxy servers, this leaves the detection string as ‘.php?q=aHR0c’.
phpStrings = (".*\.php\?q=aHR0c.*(?i)\s", ".*GET.*(?i)\s",
".*HTTP.*(?i)\s")
php = [False, False, False]
php[0] = re.match(phpStrings[0], str(packet1)) # Search
packet for regex
php[1] = re.match(phpStrings[1], str(packet1)) # Search
packet for regex
php[2] = re.match(phpStrings[2], str(packet1)) # Search
packet for regex
if (php[0]
and php[1]
and php[2]) :
result = 2
print >>log, str("PHPProxy: " + logTime + "\n" +packet1 +
"\n")
Figure 24 - PHPProxy Regular Expression and Matching Statement
Figure 24 contains the regex for the three characteristics that have to be matched
before a PHPProxy is flagged up as being in use. The only difference from the
49
PHPProxy code and the Glype code is the detection string in the regex. The result if a
proxy is detected will be ‘2’, which would result in “PHPProxy Usage Detected”
being printed to the console; this can be seen in Figure 25.
Figure 25 - PHPProxy Usage Detected
6.5
CGI Proxy Detection
The CGI Proxy differs from the previous two proxy servers. The previous two proxies
use port 80 when transferring packets, while the CGI script uses a secure server and
goes through port 443. A sample of a network packet from a CGI proxy web script is
as follows:
‘Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8 Version : 4 IP Header Length
: 5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 74.125.24.94 Source Port : 19516
Dest Port : 443 Sequence Number : 2955026867 Acknowledgement : 210236496 TCP header length : 5
Data :
÷
„•ÅëU
M
ö×[~ƒ.:‡ÜU/H\¦˜QÉ–
»§µ‚m3S-Bÿ¥¬b>b´TÙ•Â$š7FñË϶å«<Ä•ÿ2`gM$+É?.)úC=O¡Ÿ¬ÍÞ˜™t$ £‹©¡¶ƒ™3ךWÔ‹2Ÿ^mé=ŒùŽßÍ€Ô
}ÎÅý
}`Ü!s1s]8˜ØyÆ™Ü×2Mß:`ìãÀ›I F@
FÛ-())M=£ÚÈÍ,4*¡—•@ßq^’'Ðæà÷›¡®Ï#‰Öÿbjæª-šc7q£¨²d ê”èœ'•ÛÕ¦i"hŠº¨ù
ÔUã$ê:Ðã’êViöîÕÊÔ$Žäê,¨5ÈGÿ¯ßæ TðB÷«,wƒ9-‰MED—
‚~ðÚ´Hª%L0ToŸ"9"ãyI•Ë­µ¦À¡)ë5n±Ah',™¡@ÂöÑ~íB·œP B³9ó$Шº•ùÿ º€Ç‰hæ”û:Šköçjf
qZòïÑ%bÔUûºy†>³>xå‹:~#*¦`Ž¨/úUÛò 1¨ó#‰~ õŒ˜ßö¯Ð–
ŒÍGA†{°ŸÜ!¼’bè€\VŽÜ´î©®æ#€˜z<ÊKÇØã~˜OKJíÔþ½˜Zµ‹É’
50
The data received in the network packet is encrypted as it goes through a secure
server using the Secure Socket Layer (SSL) protocol; this makes it extremely difficult
to find the characteristics needed to determine if it is in fact a CGI proxy which is
being used. Decrypting the data without the use of an encryption key would take
many years; this unfortunately means it is impossible to provide the criteria necessary
to detect the CGI proxy. The only visible data that can be used from the network
packets is the protocol and the port number, which is used by a number of different
websites that use ‘https’, including Gmail, Facebook and all banking websites.
When testing different CGI proxies that are available online it was noted that they all
use SSL. 100% of the CGI proxies viewed online charged a subscription fee, which
could cost up to €120 a year, or if paid on a monthly basis, €20 per month; due to this
fee, they are not as common as Glype or PHPProxy, with both offering their services
for free. This however only applies to the proxies using SSL, the CGI proxy can also
be used without SSL, though it is highly recommended on the CGI webpage37 that it
should be used on a secure server.
Since the CGI script can be implemented on an unsecure server, the packets would
then be readable. A sample of a packet that is produced by a CGI proxy script running
on an unsecure server is:
“Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length
: 5 TTL : 128 Protocol : 6 Source Address : 192.168.1.103 Destination Address : 193.200.150.125Source Port :
8065 Dest Port : 80 Sequence Number : 705234219 Acknowledgement : 1875896103 TCP header length : 5Data :
GET /cgi-bin/anon-www.cgi/http://static.guim.co.uk/sysimages/Books/Pix/pictures/2013/3/12/1363108898432/Sheryl-Sandberg-COO-Faceb-003.jpg HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk/business
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; _cb_ls=1; noticebar_cookie=2; eas_uid=81395255058502723820; ASP.NET_SessionId=zi1ventn2riib5r4gdkubmg0; SERVERID=web_111_121-3138;
_chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395255062698.0000000000000001; _chartbeat_uuniq=2;
fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf4-83876450-6204-de6a37
http://www.jmarshall.com/tools/cgiproxy/
51
0a0d4%22%2C%22to%22%3A4.1%2C%22c%22%3A%22http%3A%2F%2Fanonymouse.org%2Fcgibin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%2Fmoney%22%2C%22pv%22%3A2%2C%22lc%
22%3A%7B%22d0%22%3A%7B%22v%22%3A2%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C
%22sd%22%3A0%2C%22f%22%3A1395255063699%7D; _p__cb_cp=l0betj8frczgu1l0;
_p__chartbeat4=t=l0betj8frczgu1l0&E=2&ad=Top%3D2%3A%3A211%3A%3A50%3A%3A940%3A%3A101%
3A%3A%3A%3A&x=0&c=0.02&y=3403&w=667; _cb_cp=r4kjxazsqhiwnda1;
_chartbeat4=t=r4kjxazsqhiwnda1&E=1&x=0&c=0.02&y=3403&w=667;
NSC_MC_WT_172.25.9.184_80=ffffffffaf1114dd45525d5f4f58455e445a4a423660; NSC_MC_W”
The CGI proxies’ main difference from the previous two proxies is the use of .cgi
instead of .php. The proxy protocol is ‘HTTP’ and the command used is ‘GET’, it also
uses port 80. Therefore the 4 characteristics used to determine the usage of an
unsecure CGI proxy script are: HTTP, GET, .cgi and Dest Port : 80.
cgiStrings = (".*\.cgi.*(?i)\s", ".*GET.*(?i)\s", ".*HTTP.*(?i)\s",
".*Dest Port : 80.*(?i)\s",)
cgi = [False, False, False, False]
cgi[0] = re.match(cgiStrings[0], str(packet1)) # Search packet for
regex
cgi[1] = re.match(cgiStrings[1], str(packet1)) # Search packet for
regex
cgi[2] = re.match(cgiStrings[2], str(packet1)) # Search packet for
regex
cgi[3] = re.match(cgiStrings[3], str(packet1)) # Search packet for
regex
if (cgi[0]
and cgi[1]
and cgi[2]
and cgi[3]) :
result = 4
print >>log, str("CGIProxy: " + logTime + "\n" +packet1 + "\n")
Figure 26 - CGI Regular Expressions and Matching Statement
Figure 26 shows the format of the code, which is similar to the other two proxies, the
only difference being the extra matching string. If each of the characteristics are
matched in the network proxy the result will be printed to the log firstly then the
console. The result printed to the console can be seen in Figure 27.
52
Figure 27 - CGI Proxy Usage Detected
6.6
Tor Browser Detection
The code for the Tor Browser was the last to be implemented. The detection
characteristics compared to the other three proxies are completely different. This is
mainly due to the randomness of the network packets when the Tor Browser is being
used. The Tor Browser uses many different ports when sending and receiving packets,
the different ports are: 9001, 9002, 9003, 9004, 9030, 9031, 9032, 9033, 9150, 9151,
it also uses port 80 which is used for all normal web browsing that doesn’t use SSL
and also port 443, which is used for secure browsing. The main two ports the Tor
Browser uses are port 80 and 443, these two ports however cannot be used to identify
the onion routing application, as all normal web browsing would also be flagged up as
using the browser, therefore the other ports listed have to be used to identify it. This
unfortunately means the Tor Browser could be used for many minutes before it is
flagged up on the screen.
A sample of a network packet from the Tor Browser is the following: “Destination MAC :
ac:72:89:8e:4a:9f Source MAC : 70:72:3c:db:c3:19 Protocol : 8Version : 4 IP Header Length : 5 TTL : 48 Protocol
: 6 Source Address : 131.188.40.188 Destination Address : 192.168.1.101Source Port : 80 Dest Port : 22518
Sequence Number : 1739336269 Acknowledgement : 1073756582 TCP header length : 5Data :
r
Ó
53
òÙÈê9"ú­dE¾bÍìøi‘§™ÎekvW‰KAqT®AF”}¦ëG§ô¦ö¢³ž¤¤€ö@Â!#X‡c¾)×N꟧ú‚õŸUV5¶Ì·UÕé•“æ
ÜΓÊd>•‘+}Ô~Û‡•™UøäKÏúAm"{‰k:{ø4ÄT£;¬çŒdߢ¢ÑG£1ºžÌ•J•q
•HO%YÁI’¿NÙÆÖE]a᢫ž‘†Ã±ygqDÄ%KŒý‡âod‘sb³¿a6wŸ†¾î?å,ý/¶o
¸Ò‚vìË‘G(ÐBƒ‡R†WªS“Ã/6…”#—’4ûO(•g,Ë÷³{ÂZ‹œÔ¿·ÃDÓ˜ïý
:_µòO™§çýÔìÉã?GtÛø·É±Æt±»Ó¦%‡FÜ7¡^áoêU>ògõ?ÑV¥‡./ŠkÑÆ)ˆ¦žDŸº½Ÿ€ºîJ/â§ÕhȵÖ-Ñ•ªŽVÇ¡™œIfüg觡¦«ZúkJe-TP(‡•.l•s%jAä·yþ˜>x§Ó_
Ü1T2vfžùlb‹[TP•2ã=ˆ¨†Ý7•u¾ ÌÌ.È¢ÏÔ•8^Ó1ùƒµQÅxã·ãD-Q>µ^Òéø(_Ù:ågA¬±YçË•¦'Ô-k®ù'´0[•y=ÄC·e•åÓ¸¹B…ÅKÖ#'†×îM²>
c¨9ƒÝ»·tkZLŠßk 'Iq´³Æ°@'„Mfžò
rQ€‰}¥£s)
“©¥æÀƒZ·z‚ ¥¹½REÖƒ*1óÿä=ØP²j‰bge‰kÊâ‚ë.Á¨¯ûk;•ù}½Öî^¸¥á”û¶!Ð+þ˜¡P—
*Àìã¡×'sªBAMS üžãsÖõxò0âV!ˆA>hÇGRÔ¼H)MP•÷ÎIºÝ<¿ÛÞ•&VlÈÁw³ntø}ÊÿŽnÈ9±õ
‚×™vãTÌ›¤b¨ÌÏúhhOg×1=¿Ú›‰…#'dCŠ³F6´ã˜5dSδ+÷gÉó‚M‚e²Ãº60—
taø>Ú\½Õ-/5pWŠƒlS“pXFƒœ¢+Z±÷ôU,–
4m@G÷=¥Ð³‹ŽÞSŠ^?%ö쀮÷šÛÄžòÚ¶:,biч6¹ÁPh>:ô­pöÙ®Þ,Ã}à"|•¨ýG\•_æéj3¤
‚ÿâD•’«B•âסŒºý¹$jõ©;[˜l›ì5VZÅ•xäçÌs@Ø{K˜'
Ø•Èé\]t;Ã#q+uñ¬ë#
GˆcÅ÷
µ¹±Ð1qˆ5-
«à/çŠJ¾V85bŒÖÊvAD•™5rjø‰v…††Yˆ©uP…¢Ð>Ã;±ÅsŒ•˜OZZ,ùÄc…–—
ZCž½•6ê=á’œ5•P ña(ðâ@óxK£ªÖú¿•‚ ´¨xè%¢cí1ÊeUû¡†•k•˜¨ßìOÚf©Á»ûP1µƒ_Èå6+O¼öAù
JïkpOØ‚R@ÐÅN.£©•Ý²à ƒ:6פßÏÚù•X…8“;‡ž{#‰u¹™qéXQq[”|·ñJ,j±Û1_eši‡©34(
Ak­žÌ#•¾'5ÏuP:³ê•çOOàÛT„•ï•zêùZe}ÉGÏ)[••®J½Û¦!ûó°Î7WγÊÉk°£‡én*úÔ•nõiŸ¹ª²µyÍaµ&Ù¡ë`p?ÝÅæR
µ-$UêŶéÝ¥\kxP•ÃÕãˆM]ßÄLKÓ¶Ô}:ÁêÛ”0[xÄRþ<ØŸ+ð».ô•ÈF-X}>á-äºc$WÞ­åÞœuÕíMÊÿµÜçxyàwæ
B8=mà‡[ja”
When examining the packet there were a few interesting bits of data that could be
seen, firstly the port that was used was port 80, this generally means the data that is in
the network packet can be viewed, however the data in the packet in this instance is
encrypted and therefore no details can be taken from it. The second thing noticed in
the packet was the Source Address, which was 131.188.40.188. When searching for
the IP it was found within a list of known Tor nodes, this verified that it was indeed a
packet from the Tor Browser. The source address is useful to verify that it is the Tor
browser; however due to the large amount of IP addresses in the Tor network it is not
possible to add them to the characteristics. This leaves the only way to identify them
is through the ports listed above, due to this the accuracy of the data may not always
be 100% correct.
54
torStrings = (".*Dest Port : 9001.*(?i)\s", ".*Dest Port :
9002.*(?i)\s", ".*Dest Port : 9003.*(?i)\s", ".*Dest Port : 9004.*(?i)\s",
".*Dest Port : 9030.*(?i)\s", ".*Dest Port : 9031.*(?i)\s", ".*Dest Port :
9032.*(?i)\s", ".*Dest Port : 9033.*(?i)\s", ".*Dest Port : 9150.*(?i)\s",
".*Dest Port : 9151.*(?i)\s")
tor = [False, False, False, False, False, False, False, False, False,
False]
tor[0] = re.match(torStrings[0], str(packet1)) # Search packet for
regex
tor[1] = re.match(torStrings[1], str(packet1)) # Search packet for
regex
tor[2] = re.match(torStrings[2], str(packet1)) # Search packet for
regex
tor[3] = re.match(torStrings[3], str(packet1)) # Search packet for
regex
tor[4] = re.match(torStrings[4], str(packet1)) # Search packet for
regex
tor[5] = re.match(torStrings[5], str(packet1)) # Search packet for
regex
tor[6] = re.match(torStrings[6], str(packet1)) # Search packet for
regex
tor[7] = re.match(torStrings[7], str(packet1)) # Search packet for
regex
tor[8] = re.match(torStrings[8], str(packet1)) # Search packet for
regex
tor[9] = re.match(torStrings[9], str(packet1)) # Search packet for
regex
if
or
or
or
or
or
or
or
or
or
(tor[0]
tor[1]
tor[2]
tor[3]
tor[4]
tor[5]
tor[6]
tor[7]
tor[8]
tor[9]) :
result = 3
print >>log, str("Onion Routing: " + logTime + "\n" +packet1 +
"\n")
Figure 28 - Tor Regular Expression and Matching Statements
One of the main differences in the code is the use of the operator ‘or’ instead of ‘and’,
this is because the system doesn’t have to match 3 or 4 different characteristics, it
only has to match one of them to flag it up on the console.
55
Figure 29 - Onion Routing Usage Detected
Figure 29 shows the outcome on the IDLE console when Onion Routing has been
detected, the network administrator can then view the log and make sure the IP is in
fact on the list of known Tor Nodes.
Another port that the Tor Browser uses is port 9100, this port however is used often
by wireless printers and using this port would create a lot of false positive results, it
was decided that due to the large amount of false positive results leaving that port out
of the detection string would be the best action to take.
6.7
Limiting the result log
The main part of the system was to be able to detect the different web based proxies
and the Tor Browser on a continuous basis, this meant that if there was heavy proxy
usage within the system the log file created would be very large. This could become
problematic especially if it takes the file a long time to open.
There were a few methods that could be used to limit the amount of network packets
used:
Scan the IP’s in the packets, if it has already been printed to the log then don’t
re-print it.
56
Scan the MAC address in the packet; if it has already been printed to the log
then don’t re-print it.
Only print to the log every 60 seconds.
As the system could be used within a large network, only printing every 60 seconds
might let some of the proxy network packets slip through undetected. Therefore
limiting the packets by either the IP or MAC address was more desirable.
The code in Figure 30 matches the source IP addresses in the packets, it however does
not have full functionality therefore it is not included in the working system.
def ipCheck(packet2) :
ipSource = (".*Source Address : .*(?i)\s", ".*[0-9]*/.[0-9]*/.[09]*/.[0-9].*(?i)\s")
ip = [False, False]
resultIP = 0
ip[0] = re.match(ipSource[0], str(packet2))
ip[1] = re.match(ipSource[1], str(packet2))
if (ip[0]
and ip[1]) :
resultIP = 1
return resultIP
Figure 30 - Code to Check the IP
The regex code gets the IP address, then it matches it against the packet, if the IP
matches then the resultIP will be equal to 1. The ipCheck function will then be used
around the isProxy function, and if the IP already exists within the packet then “IP
already found” will be printed to the console.
if(ipCheck(log)) :
# Parse packet for suspect proxy data
result = isProxy(parsedPacket)
print >>log, str("IP already found")
Figure 31 - Print Statement if the IP is already in the log
The code unfortunately printed the statement every time the system scanned the
network, and as it scans it on a continuous basis, the console was flooded with the
statement. To overcome this nothing was printed using a simple ‘print None’.
57
The ipCheck function does limit the log size, however it doesn’t check for different
proxies. If an IP uses a Glype proxy and a CGI proxy then it will not report the second
proxy, due to this flaw the code wasn’t functioning as it should be. Another check
should be placed in the code to check the IP and the proxy it used, if that has already
been printed then it shouldn’t be printed again, if the IP then uses another proxy, then
it should then be printed to the log.
58
7.
Testing
This section will document the thorough testing that was performed on the system to
ensure the system is performing the tasks that was detailed in the previous sections
and that it is performing them to a high standard. It is important that any errors or
unexpected crashes are found and fixed before the end product is finalized.
Each of the different proxies and onion routing applications were tested thoroughly by
performing a series of Internet activities that may be carried out on a daily basis by an
average Internet user. The activities are listed in Table 6.
Test
1
2
3
4
5
6
7
8
9
10
11
12
Activity
Browse the Guardian news website and view videos
Log into Gmail and send an email
Log into Twitter and view some tweets
Browse Amazon and make a purchase
Log into Facebook and browse multiple pages
Visit the BBC Sports section and post a comment in the comments section
Listen to iRadio on their live radio stream
Upload an image to Imgur or Photobucket
Select a Youtube video from your account
Download a ZIP file from a reliable source
Perform a search using a Search Engine such as Google or Bing
Go to Miniclip and play a game
Table 6 - Regular Internet Browsing Tasks
The IDS will be given 5 minutes per test to monitor the network and to verify that it is
detecting each of the proxies. The websites were accessed by firstly entering the URL
into the proxy start page or from the start page in the Tor Browser. The program was
also tested when the user was not using any proxy or the Tor Browser, just to verify
that it wasn’t flagging up any proxies when they were not in use. Altogether there
were 60 log files created in total to test the program.
7.1
Normal Browsing Test
Before any of the proxies and onion routing applications could be tested, the IDS was
tested while the user was browsing the internet normally without the use of a proxy.
The web browser used for all the tests apart from the Tor Browser was Google
Chrome. Only one tab was open at any one time, with all other internet related
activities such as Skype, Dropbox and Google drive closed so the tests would be
precise.
59
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
No Proxy usage detected
Table 7- Normal browsing test results
Table 7 shows the results when there is no proxy usage in the network, there was
nothing printed to the console, therefore no proxy was found in the 5 minutes the IDS
was running for each of the twelve individual tests. These results are exactly what was
expected from the program, if a proxy or onion routing application had been found,
the system would be flagging up false positive results.
7.2
Glype Proxy Test
The first proxy to be tested was the Glype proxy. It was decided that since the
availability of proxies online was very high, it would be best to test a proxy that was
currently available online. The web based proxy used to test the Glype proxy was
‘www.proxyserver.com’. This proxy was found within a list of available proxies on
the Glype website38, the list also contained many other different proxies which were
used to test the other proxies.
The first thing to do was to start to the program running. All other web pages were
closed to make sure it was just the proxy being used in the network. The IDS was then
started to sniff the network packets. The results that were printed onto the console
when the program was running during each of the tests are shown in Table 8.
38
http://list.glype.com/
60
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Glype Proxy usage detected
Table 8 - Glype Proxy Test
As can be seen in Table 8, the results show that the IDS is working as it should when
a Glype proxy is being used in the network. Each test was detected, with the statement
‘Glype Proxy usage detected’ being printed multiple times. The network packets were
also printed out to the log showing the 3 different characteristics used to detect the
proxies contained within them.
Another Glype proxy was also tested; this proxy can be found at
‘http://yourfastproxy.com/’. The results from the proxy were identical to those in
Table 8, proving that the characteristics are correct and that the IDS has a 100%
succession rate when a Glype proxy is in use.
7.3
PHPProxy Test
The second proxy that was tested was the PHPProxy. The same format as the previous
test was used to test the proxy. The proxy that was used can be found at
‘http://proxyanonymizer.net/’.
The results from the different tests can be seen in Table 9. There were problems with
using the proxy. While logging into a secure website such as Gmail, the Gmail
services blocked the login as the location was completely different from where the
email is usually accessed. The IDS however still picked up the use of the proxy, as
there were 3 different pages accessed while performing the test.
61
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
PHPProxy usage detected
Table 9 - PHPProxy usage test
Once again the results from the IDS proved to be successful, with 100% of the tests
being detected by the system. This proved that the 3 characteristics, ‘GET’, ‘HTTP’
and ‘.php?q=aHR0c’ were being picked up in every network packet that was being
created by the PHPProxy. A second PHPProxy was tested to verify the results, the
proxy can be found at: ‘http://proxy-up.net/’. Again the results returned 100%
accuracy.
Tests
PHPProxy
Tests
Glype
0
4
8
12
16
20
24
Figure 32 - Pass rate for both the PHPProxy and Glype Proxy
So far testing both proxies returned a 100% success rate, with 48 tests performed, 24
for the Glype proxy and 24 for the PHPProxy.
62
7.4
CGI Proxy Test
The CGI proxy was the third proxy to be tested, as it was previously noted, due to the
use of SSL in the proxy, the characteristics could not be found and therefore the proxy
could not be detected. This meant that the results for the test of the CGI proxy would
be a 100% fail rate, this only applied to the proxy when it was using SSL. The proxy
however can also be used without SSL and due to this, the characteristics were found.
Table 10 verifies the results as expected when the CGI proxy is using SSL, each of
the tests failed to show any proxy usage within the network. The proxy used was
found at ‘https://morphium.info/’.
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
No Proxy detected
Table 10 - CGI Proxy using SSL
After the SSL CGI proxy was tested, a CGI proxy that does not run on a secure server
was tested. This proxy’s URL is: ‘http://anonymouse.org/’. One of the main
differences that stand out between the two CGI Proxies URL’s is the first one contains
‘https’ in the URL and in the second CGI proxy, it has ‘http’ in the URL, this shows
that the second one doesn’t use a secure server.
The results from the testing of the unsecure CGI proxy can be seen in Table 11.
63
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
CGI Proxy usage detected
Table 11 - Unsecure CGI proxy test
Tests
Unsecure CGI Proxy
Tests
SSL CGI Proxy
0
2
4
6
8
10
12
Figure 33 - Pass rate for the SSL CGI Proxy and the Unsecure CGI Proxy
The results between the two are stark, with the IDS catching 100% of the unsecure
CGI Proxies and the SSL CGI proxy evading detection completely.
64
7.5
Tor Browser Test
The final proxy/onion routing application to be tested was the Tor Browser. Up until
now the results from each of the previous tests have been straightforward, with the
results returned as expected. This however was not the case for the Tor Browser, as
the characteristics for it did not include two ports, from which most of the traffic
flowed through.
The results from the Tor Browser testing can be seen in Table 12. With the twelve
tests completed, eight of them passed, with ‘Onion Routing usage detected’ being
printed to the console. Four of them resulted in nothing being printed to the console,
therefore the IDS did not detect the use of the Tor Browser.
Test
1
2
3
4
5
6
7
8
9
10
11
12
Result
Onion Routing usage detected
No Onion Routing usage detected
No Onion Routing usage detected
Onion Routing usage detected
No Onion Routing usage detected
Onion Routing usage detected
Onion Routing usage detected
Onion Routing usage detected
Onion Routing usage detected
Onion Routing usage detected
No Onion Routing usage detected
Onion Routing usage detected
Table 12 - Tor Browser test
As these tests were carried out during a five minute period, it is not always guaranteed
that the IDS will miss the detection of the Tor Browser. If for instance it had ten
minutes per test, the program may have picked it up. As the program is meant to pick
up each of the proxies/onion routing applications almost instantaneously using ten
minutes to test it would not be feasible.
While having a closer look at the results gained from the Tor Browser tests, we can
see it failed to detect the browser in tests 2, 3, 5 and 11. These tests involve using
Gmail, Twitter, Facebook and Google respectively, one thing in common that each of
them share is the use of ‘https’ for secure browsing. Taking a closer look at the
network packets while browsing each of the websites shows that each of them use
65
port 443 for all of the packets, due to this, the IDS will not detect them. Amazon also
uses ‘https’ when the consumer is purchasing an item, this only applies when they are
logging into their account to pay for the item. Before this point, amazon uses a regular
‘http’ connection, so the network packets can go through any of the ports in the
characteristics and also port 80.
In Figure 34, the results of all the tests can be seen. Three out of the five that were
tested had a success rate of 100%, with the Tor Browser having a 66% success rate
and the Secure CGI proxy having a 0% success rate.
Tests
12
10
8
6
Tests
4
2
0
Glype
PHPProxy
Secure CGI
Proxy
Unsecure CGI
Proxy
Tor Browser
Figure 34- Full proxy/onion routing results
The results from each of the tests were as expected, when the proxy or onion routing
application was using an unsecure server the IDS picked up its usage every time,
when the proxy was using a secure server it evaded the IDS’s detection.
The result unfortunately came to the same outcome when other SSL proxies were
tested, the IDS did not detect any of them. When using Wireshark to take a closer
look at the packets each of them used port 443 and the TCP protocol, as the packets
are very similar to those of a regular SSL connection that does not use a proxy there is
little that can be done to fix the IDS without creating a lot of false positive results.
66
7.6
Further System Tests
As the system is to run on a continuous basis, the system should be run for 24 hours
non-stop to make sure there are no un-expected stoppages or un-expected results.
There did not have to be any internet activity while the system was running, as this
test was to just make sure the system did not throw any errors over a long period of
time.
The first run resulted in an error showing up, and as the system was not monitored,
the exact time of the error was not discovered; the error can be seen in Figure 35.
Figure 35 - Pcap error
After researching the error and debugging through the code it was found that if the
program was not getting network packets it would cause the error. This meant if the
network dropped for a certain period of time the program would crash. This
unfortunately was not ideal and a solution for this was sought. To fix this error a ‘try’
and ‘continue’, was added into the code surrounding the ‘(header, packet) = cap.next()
line. If the network was not receiving any packets it would continue to look for them
without crashing the program. Once this had been implemented it could then be tested
to make sure it was working correctly. A test was carried out, once the system was
running, the network connection was stopped. Previously the system would crash,
however now the system continues to search for the network packets, this meant the
previous test could now be carried out again.
The test was resumed and the program was left running for 24 hours. The system was
still running after the 24 hours, with no results printed on the console. This validated
it was running correctly and that there were no false positive results noted within the
time allocated.
Another error noted when testing the system was when the system was being closed
while it was still running. Unfortunately due to the console closing down at the exact
67
time, a preview of the error could not be captured. This error did not affect the log file
or the system; however a more reliable way to close the program would be ideal. One
solution would be to give the network administrator an option to press ‘esc’ if they
want to close the system, this should close down the system properly without any
errors showing. Another option was to control the error when the system was closed,
as the user can just press ‘x’ to close the system this was a more feasible plan.
Therefore a ‘keyboardInterrupt’ exception was used in the main function.
The final test that was performed on the system was to determine if the system could
perform as it should when there are many different proxies being used at once on the
system. To do this test, firstly all 3 of the proxies were opened up along with the Tor
Browser. The program then was started, to monitor the network packets. In each of
the proxies, the website ‘www.guardian.co.uk’ was opened up and used for five
minutes. Figure 36 shows a snippet of the data that was printed to the console, as can
be seen each of the different proxies and the onion routing application’s usage was
detected correctly without any problems occurring in the system.
Figure 36 - Testing every proxy at once with continuous usage
When taking a closer look at the log created by the system, each of the packets was
printed out successfully and in order. A snippet of each of the packets can be seen in
Figure 37, Figure 38, Figure 39 and Figure 40.
68
Figure 37 - CGI Proxy continuous use
Figure 38 - PHPProxy continuous use
Figure 39 - Glype continuous use
Figure 40 - Onion routing continuous use
As can be seen in the snippets, the date and time is beside the proxy name, this shows
the exact time the proxy is found and printed to the file. Between the different
proxies, there are only milliseconds of a difference; this is the same throughout the
log file. Appendix B contains a more thorough sample of the log file created when all
the proxies were being run, due to the logs size, only a quarter of the file was
included. The most notable part of the log file is the time difference between each of
the proxies, this information is very useful to a network administrator as they know
exactly when the proxy was being used and which proxy it was. They can also see
each of the IP’s within the packet, and therefore can make the decision if it is a threat
to the networks security or allow its usage.
69
8.
Evaluation & Reflection
One of the main aims of the project was to firstly examine the packets in the network
to see how each of the different packets looked and what was contained therein. Once
a good grasp of the data in the packets was obtained, the proxies would then be used
to compare the difference. Any noticeable difference contained therein could then be
used to determine if a proxy was being used and what type of proxy it was. This was
successfully done in four out of the five tests, with the SSL CGI proxy being the only
downfall. Again the program didn’t have a 100% success rate in determining the Tor
Browser, however the differences in the network packets was noticeable in most of
them. This criterion in the packets was put into regex strings to be compared with
each inbound and outbound packet, in turn successfully determining the different
proxies.
When the project was first started there was a need for a system that would be able to
detect the use of anonymous proxies, security is a major field in Information
Technology and the sector is increasing at a fast rate. This system fills that need, it
can successfully detect Glype, PHPProxy, Unsecure CGI proxy and the Tor Browser
which in turn provides a more stable and secure environment for the
company/organisation to perform its everyday tasks. Overall the project would be
very useful to a network administrator in terms of monitoring the network packets to
determine if there is a proxy in use or if the Tor browser is in use. This system,
although it doesn’t pick up every single proxy, would be an important system to any
company that has high security measures.
The system was hoped to have 100% accuracy in detecting anonymous proxies. This
however could not be achieved as the data travelling through a SSL proxy or pages
that use ‘https’ on Tor generally use port 443, and thus the data in the network packets
was encrypted. The system however did achieve 100% accuracy when detecting the
Glype, PHPProxy and the unsecure CGI proxy. Also in testing it had 66.67%
accuracy in finding the Tor browser.
The system’s effectiveness can be debatable; it all depends on the type of proxy being
used. The system does not detect 100% of proxies, it does however detect 100% of 3
different proxies and 66% of the Tor Browser, and therefore it can be quite effective
70
when detecting those. However it is not effective when it is detecting SSL proxies and
due to this, this requirement was not fully met.
8.1
Future Work and Enhancements
Although the program does detect most of the common proxies available on the
internet there are some minor improvements that could be made to the system.
1. Limit the log size
If the network has a heavy proxy usage within it the log file is going to
increase its size very quickly and if it is not monitored often this could be
problematic when the administrator goes to open it. A file size limit should be
put in place in order to stop this. When the limit is reached a new file should
be created without stopping and restarting the program.
2. IP/Proxy Check
A check should be put in place to limit the amount of packets printed out to
the log, the check should grab the IP from the packet and also the proxy that
was in the packet, and if it has already been printed to the log then there is no
need to reprint. This check would greatly reduce the size of the log, however it
would also leave the network administrator with only one network packet to
determine the use of the proxy.
3. Pause/Restart Function
A function should be integrated into the system to allow the user the ability to
pause or restart the project without having to close the program and start it up
again.
4. Increase the amount of proxies detected
As a lot of the main proxies have been detected, there are some proxies
available that do not fall under the main categories. Determining the
characteristics of these proxies and adding them to the code would be a useful
addition.
5. Proxy Counter
A proxy counter could be utilized to count the amount of proxies detected
within the network in a given time. The counter should be able to distinguish
between the different proxies and give a daily report of the proxy usage. This
71
could then be used to determine how successful the system is, especially if the
network administrator is blocking the proxies as they find them.
6. File Upload
As the program was to be run on a continuous basis, the need for a function
for the user to upload a packet file to check if it contains a proxy or not was
not the priority for this program, therefore it was not implemented. It could
however be implemented in the future, as it would be a useful feature to be
able to scan saved packet files.
72
10.
References
Chaabane, A., Pere Manils, P. & Kaafar, M. (2010) Digging into Anonymous Traffic:
A Deep Analysis of the Tor Anonymizing Network, 4th International Conference on
Network and System Security, vol. 1, no. 1, pp. 167
Cisco. (2006) Cisco IOS Security Configuration Guide, Release 12.2, Access Control
Lists:
Overview
and
Guidelines.
Available
at:
http://www.cisco.com/en/US/docs/ios/12_2/security/configuration/guide/scfacls.html
Dingledine, R., Mathewson, N. & Syverson, P. (2004) Tor: the second-generation
onion router, Proceedings of the 13th conference on USENIX Security Symposium,
August 2004.
Dredge, S. (2013) What is Tor? A beginner’s guide to the privacy tool, The Guardian,
November
2013,
Available
at:
http://www.theguardian.com/technology/2013/nov/05/tor-beginners-guide-nsabrowser
Goralski, W. (2008). The Illustrated Network: How TCP/IP Works in a Modern
Network. San Francisco, CA, USA: Morgan Kaufmann Publishers Inc.
International Telecommunication Union. (2013) The World in 2013 ICT Facts and
Figures.
February
2013,
Available
at:
http://www.itu.int/en/ITU-
D/Statistics/Documents/facts/ICTFactsFigures2013.pdf
Kibirkstis, A. (2009) Intrusion Detection FAQ: What is Geolocation and How Does it
Apply
to
Network
Detection,
Available
at:
http://www.sans.org/security-
resources/idfaq/geolocation-network-detection.php
Knickerbocker, P., Yu, D. & Li,J. (2009) Humboldt: A distributed phishing disruption
system, in Proc. IEEE eCrime Researchers Summit, Tacoma, USA, 2009, pp. 1-12.
Lee, J. (2013) What is Onion Routing, Exactly?. MakeUseOf, May 2013, Available at:
http://www.makeuseof.com/tag/what-is-onion-routing-exactly-makeuseof-explains/
Lee, K., Jiang, Z., Kim, S., Kim, S. & Kim, S. (2005) Access Control List Mediation
System for Large-Scale Network, 6th Int
Computing, vol. 1, no. 1, pp. 483-487.
73
Conf on Parallel and Distributed
Li, B., Erdin, E., Gunes, M., Bebis, G. & Shipley, T. (2011) An Analysis of
Anonymity Usage, Traffic Monitoring and Analysis: Third International Workshop,
TMA 2011, Vienna, Austria. Springer-Verlag, pp 113-116
Lyon, D. (2009) Nmap Network Scanning: The Official Nmap Project Guide to
Network Discovery and Security Scanning. United States: Insecure.
Mallia, D. (2013) When was the Internet Invented. History News Network, October
2013, Available at: http://hnn.us/article/142824
Microsoft. (2013) Parts of the Access Control Model. Access Control Lists, October
2010.
Available
at:
http://msdn.microsoft.com/library/windows/desktop/aa374872(v=vs.85).aspx
Murdoch, S. & Anderson, R. (2008) Tools and Technology of Internet Filtering,
Access Denied: The Practice and Policy of Global Internet Filtering, vol. 1, no. 1, pp.
58.
Neustar. (2012) Neustar® Insights: Online Fraud Prevention: Three Who Stood Their
Ground,
Available
at:
http://www.banktech.com/whitepaper/download/showPDF?articleID=191705583
Raynal, F. Ahmad, M., Shaikhli, I. & Ahmad, H. (2012) Protection of the Texts Using
Base64 and MD5, Journal of Advanced Computer Science and Technology Research,
vol. 2, no. 1, pp. 22-34.
Reed, M.G., Syverson, P.F., Goldschlag, D.M.(1998) Anonymous connections and
onion routing, IEEE Journal on Selected Areas in Communications, , vol.16, no.4,
pp.482-494.
SASI. (2006) Internet Use 1990, Poster of Internet usage, Available at:
http://www.worldmapper.org/posters/worldmapper_map335_ver5.pdf
Sourcefire. (2013) Snort User’s Manual 2.9.5, The Snort Project , May 2013.
Available at: http://s3.amazonaws.com/snort-org/www/assets/166/snort_manual.pdf
74
Stanger, J., Krishnamurthy, M., Seagren, E., Alder, R., Bayles, A., Burke, J., Carter,
S. & Faskha, E. (2007) How to Cheat at Securing Linux. Introducing Intrusion
Detection and Snort. United States of America: Syngress, pp 126-140.
Thomas, K., Grier, C., Ma, J., Paxson, V. & Song, D. (2011) Monarch: Providing
real-time URL spam filtering as a service, in Proc. IEEE Symposium on Security and
Privacy, Oakland, California, USA, 2011, pp 447-462.
75
11.
Appendices
Appendix A: Source Code
IDS.py
'''
Packet sniffer in python using the pcapy python library
Project website
http://oss.coresecurity.com/projects/pcapy.html
'''
import socket
from struct import *
from datetime import datetime
import pcapy # Import pcapy for the ability to scan network packets
import sys
import re # Import regex for parsing packets for suspect proxy
traffic
import time
import os
import signal
# Globals
# creates the time so it can be used for the log filename and also
within the log
textTime = time.strftime("%H-%M-%S")
# creates the date so it can be used for the log filename and also
within the log
textToday = time.strftime("%d-%m-%Y")
# The directory for the log files to be stored, this can be changed
to suit
directory = "C:\ProxyTempLogs"
# opens a log with the date and time in the logs filename
log = open(directory + '\log_' + textToday + '_' + textTime + '.txt',
'w')
def main(argv):
# checks to make sure the directory doesn't exist
if not os.path.exists(directory):
# make the directory
os.makedirs(directory)
# list all devices
devices = pcapy.findalldevs()
'''
open device
# Arguments here are:
#
device
#
snaplen (maximum number of bytes to capture _per_packet_)
#
promiscious mode (1 for true)
#
timeout (in milliseconds)
'''
76
# No interfaces found
if len(devices) == 0:
raise RuntimeError, "Error: no available network interfaces,
or you don't have enough permissions on this system."
# A single interface was found
if len(devices) == 1:
interface = devices[0]
# Multiple interfaces found
else:
print "Available network interfaces:"
for i in xrange(len(devices)):
print '\t%i - %s' % (i + 1, devices[i])
print
while 1:
choice = raw_input("Choose an interface: ")
try:
i = int(choice)
if i == 0:
interface = None
break
interface = devices[i-1]
break
except Exception:
pass
# Return the selected interface
print "Sniffing device " + interface
cap = pcapy.open_live(interface , 65536 , 1 , 0)
# start sniffing packets
while(1) :
time.sleep(0.05)
try:
(header, packet) = cap.next()
# print ('%s: captured %d bytes, truncated to %d bytes'
%(datetime.datetime.now(), header.getlen(), header.getcaplen()))
parsedPacket = parse_packet(packet)
######################
# Parse packet for suspect proxy data
result = isProxy(parsedPacket)
# Inform user if packet contained suspect data
if result == 0 :
# OK
# This can be uncommented if the user wants to make
sure there are no proxies, OK will be printed constantly
#print("OK")
a = 1
elif result == 1 :
# GLYPE proxy
print("Glype usage detected")
elif result == 2 :
# PHPProxy
print("PHPProxy usage detected")
elif result == 3 :
77
# Tor Browser
print("Onion Routing usage detected")
elif result == 4 :
# CGI Proxy
print("CGI Proxy usage detected")
else :
# INVALID
print("INVALID RESULT")
sys.stdout.write("")
sys.stdout.flush()
# handle the pcapy error if the network drops
except pcapy.PcapError:
continue
# Convert a string of 6 characters of ethernet address into a dash
separated hex string
def eth_addr (a) :
b = "%.2x:%.2x:%.2x:%.2x:%.2x:%.2x" % (ord(a[0]) , ord(a[1]) ,
ord(a[2]), ord(a[3]), ord(a[4]) , ord(a[5]))
return b
def isProxy(packet1) :
logTime = str(datetime.now())
# Regex for Glype
glypeStrings = (".*\.php\?u=.*(?i)\s", ".*GET.*(?i)\s",
".*HTTP.*(?i)\s")
# Regex for PHPProxy
phpStrings = (".*\.php\?q=aHR0c.*(?i)\s", ".*GET.*(?i)\s",
".*HTTP.*(?i)\s")
# Regex for the Tor Browser
torStrings = (".*Dest Port : 9001.*(?i)\s", ".*Dest Port :
9002.*(?i)\s", ".*Dest Port : 9003.*(?i)\s", ".*Dest Port :
9004.*(?i)\s", ".*Dest Port : 9030.*(?i)\s", ".*Dest Port :
9031.*(?i)\s", ".*Dest Port : 9032.*(?i)\s", ".*Dest Port :
9033.*(?i)\s", ".*Dest Port : 9150.*(?i)\s", ".*Dest Port :
9151.*(?i)\s")
# Regex for CGI Proxy
cgiStrings = (".*\.cgi.*(?i)\s", ".*GET.*(?i)\s",
".*HTTP.*(?i)\s", ".*Dest Port : 80.*(?i)\s",)
glype = [False, False, False]
php = [False, False, False]
tor = [False, False, False, False, False, False, False,
False, False, False]
cgi = [False, False, False, False]
result = 0 # Whether packet is a proxy, or not
# Search
glype[0]
glype[1]
glype[2]
packet for regex
= re.match(glypeStrings[0], str(packet1))
= re.match(glypeStrings[1], str(packet1))
= re.match(glypeStrings[2], str(packet1))
# If each of the regex strings match the print out the result
and the packet to the log
if (glype[0]
and glype[1]
and glype[2]) :
result = 1
78
print >>log,
str("GLYPE: " + logTime + "\n" + packet1 +
"\n")
# Search
php[0] =
php[1] =
php[2] =
packet for regex
re.match(phpStrings[0], str(packet1))
re.match(phpStrings[1], str(packet1))
re.match(phpStrings[2], str(packet1))
# If each of the regex strings match the print out the result
and the packet to the log
if (php[0]
and php[1]
and php[2]) :
result = 2
print >>log, str("PHPProxy: " + logTime + "\n" +packet1 +
"\n")
# Search
tor[0] =
tor[1] =
tor[2] =
tor[3] =
tor[4] =
tor[5] =
tor[6] =
tor[7] =
tor[8] =
tor[9] =
packet for regex
re.match(torStrings[0],
re.match(torStrings[1],
re.match(torStrings[2],
re.match(torStrings[3],
re.match(torStrings[4],
re.match(torStrings[5],
re.match(torStrings[6],
re.match(torStrings[7],
re.match(torStrings[8],
re.match(torStrings[9],
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
str(packet1))
# If any of the regex strings match the print out the result
and the packet to the log
if (tor[0]
or tor[1]
or tor[2]
or tor[3]
or tor[4]
or tor[5]
or tor[6]
or tor[7]
or tor[8]
or tor[9]) :
result = 3
print >>log, str("Onion Routing: " + logTime + "\n"
+packet1 + "\n")
# Search
cgi[0]
cgi[1]
cgi[2]
cgi[3]
packet for regex
= re.match(cgiStrings[0],
= re.match(cgiStrings[1],
= re.match(cgiStrings[2],
= re.match(cgiStrings[3],
str(packet1))
str(packet1))
str(packet1))
str(packet1))
# If each of the regex strings match the print out the result
and the packet to the log
if (cgi[0]
and cgi[1]
and cgi[2]
and cgi[3]) :
result = 4
79
print >>log, str("CGIProxy: " + logTime + "\n" +packet1 +
"\n")
return result
# function to parse a packet
def parse_packet(packet) :
# parse ethernet header
eth_length = 14
packetStr = ""
eth_header = packet[:eth_length]
eth = unpack('!6s6sH' , eth_header)
eth_protocol = socket.ntohs(eth[2])
packetStr += 'Destination MAC : ' + eth_addr(packet[0:6]) + '
Source MAC : ' + eth_addr(packet[6:12]) + ' Protocol : ' +
str(eth_protocol)
# Parse IP packets, IP Protocol number = 8
if eth_protocol == 8 :
# Parse IP header
# take first 20 characters for the ip header
ip_header = packet[eth_length:20+eth_length]
# now unpack them :)
iph = unpack('!BBHHHBBH4s4s' , ip_header)
version_ihl = iph[0]
version = version_ihl >> 4
ihl = version_ihl & 0xF
iph_length = ihl * 4
ttl = iph[5]
protocol = iph[6]
s_addr = socket.inet_ntoa(iph[8]);
d_addr = socket.inet_ntoa(iph[9]);
packetStr += 'Version : ' + str(version) + ' IP Header Length
: ' + str(ihl) + ' TTL : ' + str(ttl) + ' Protocol : ' +
str(protocol) + ' Source Address : ' + str(s_addr) + ' Destination
Address : ' + str(d_addr)
# TCP protocol
if protocol == 6 :
t = iph_length + eth_length
tcp_header = packet[t:t+20]
# now unpack them :)
tcph = unpack('!HHLLBBHHH' , tcp_header)
source_port = tcph[0]
dest_port = tcph[1]
sequence = tcph[2]
acknowledgement = tcph[3]
doff_reserved = tcph[4]
tcph_length = doff_reserved >> 4
packetStr += 'Source Port : ' + str(source_port) + ' Dest
Port : ' + str(dest_port) + ' Sequence Number : ' + str(sequence) + '
80
Acknowledgement : ' + str(acknowledgement) + ' TCP header length : '
+ str(tcph_length)
h_size = eth_length + iph_length + tcph_length * 4
data_size = len(packet) - h_size
# get data from the packet
data = packet[h_size:]
packetStr += 'Data : ' + data
# ICMP Packets
elif protocol == 1 :
u = iph_length + eth_length
icmph_length = 4
icmp_header = packet[u:u+4]
# now unpack them :)
icmph = unpack('!BBH' , icmp_header)
icmp_type = icmph[0]
code = icmph[1]
checksum = icmph[2]
packetStr += 'Type : ' + str(icmp_type) + ' Code : ' +
str(code) + ' Checksum : ' + str(checksum)
h_size = eth_length + iph_length + icmph_length
data_size = len(packet) - h_size
# get data from the packet
data = packet[h_size:]
packetStr += 'Data : ' + data
# UDP packets
elif protocol == 17 :
u = iph_length + eth_length
udph_length = 8
udp_header = packet[u:u+8]
# now unpack them
udph = unpack('!HHHH' , udp_header)
source_port = udph[0]
dest_port = udph[1]
length = udph[2]
checksum = udph[3]
packetStr += 'Source Port : ' + str(source_port) + ' Dest
Port : ' + str(dest_port) + ' Length : ' + str(length) + ' Checksum :
' + str(checksum)
h_size = eth_length + iph_length + udph_length
data_size = len(packet) - h_size
# get data from the packet
data = packet[h_size:]
packetStr += 'Data : ' + data
81
# some other IP packet like IGMP
else :
packetStr += 'Protocol other than TCP/UDP/ICMP'
# print(packetStr)
return packetStr
if __name__ == "__main__":
try :
main(sys.argv)
# Handle any exceptions caused when exiting the program
except KeyboardInterrupt:
pass
Appendix B: Network Packets containing the different proxies
PHPProxy: 2014-03-25 13:23:47.036000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26283 Dest Port : 80 Sequence Number : 1658923766 Acknowledgement : 2029579901 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L3VzbmV0d29ya2Zyb250Ly4uL3dlYXRoZXIvaW1hZ2VzL2ljb25zL
3NtYWxsLzIyLmdpZg%3D%3D HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
82
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0as
PHPProxy: 2014-03-25 13:23:47.244000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26284 Dest Port : 80 Sequence Number : 3242172098 Acknowledgement : 757510173 TCP header length : 5Data
: GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9pbWFnZXMvYnRuX2JhY2suZ2lm HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2Xm2gayUywZEeC8GphSAeubJJgXT5S0rqZsH
PHPProxy: 2014-03-25 13:23:47.513000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26285 Dest Port : 80 Sequence Number : 2307755332 Acknowledgement : 471632617 TCP header length : 5Data
: GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
83
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9pbWFnZXMvYnRuX3BhdXNlLmdpZg%3D%3D
HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2Xm2gayUywZEeC8GphSAeubJJgXT
CGIProxy: 2014-03-25 13:23:47.861000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26288 Dest Port : 80 Sequence Number : 3521889381 Acknowledgement : 2371556275 TCP header length :
5Data : GET /cgi-bin/anon-www.cgi/http://www.theguardian.com/uk HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/anonwww.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf4-
84
83946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
PHPProxy: 2014-03-25 13:23:47.964000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26287 Dest Port : 80 Sequence Number : 4004651678 Acknowledgement : 2096568533 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL2ludGVyYWN0aXZlc3RvcmUvMjAxMy83LzkvM
TM3MzM4NjY2Njg1OS83NzM4NDkvRGlzY3Vzc2lvbldpZGdldC9pbmRleC5odG1s&nf=1 HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2-Xm
PHPProxy: 2014-03-25 13:23:48.068000
85
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26286 Dest Port : 80 Sequence Number : 3702080011 Acknowledgement : 2032671020 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9pbWFnZXMvYnRuX2ZvcndhcmQuZ2lm HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2Xm2gayUywZEeC8GphSAeubJJgXT5S0r
PHPProxy: 2014-03-25 13:23:48.476000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26291 Dest Port : 80 Sequence Number : 2956997255 Acknowledgement : 694983607 TCP header length : 5Data
: GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9zdHlsZXMvaW1hZ2VzL2Fycm93X2Rvd25fMzMzLn
BuZw%3D%3D HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
86
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2-Xm2gayUywZE
PHPProxy: 2014-03-25 13:23:48.640000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26292 Dest Port : 80 Sequence Number : 974407291 Acknowledgement : 3139660890 TCP header length : 5Data
: GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N5cy1pbWFnZXMvR3VhcmRpYW4vUGl4L3Bp
Y3R1cmVzLzIwMTQvMy8yNS8xMzk1NzExNzIzNDQxL1VTLXBob25lLWRhdGEtMDA2LmpwZw%3D%3D
HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
87
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2Xm2gayUywZEeC8GphSAeubJ
PHPProxy: 2014-03-25 13:23:49.163000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26294 Dest Port : 80 Sequence Number : 3310501737 Acknowledgement : 3854717743 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L3pvbmVzL25ld3Mvc3R5bGVzL2ltYWdlcy9jcnVtYl8xLnBuZw%3
D%3D HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2-Xm2gayUywZEeC8G
88
CGIProxy: 2014-03-25 13:23:53.961000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26297 Dest Port : 80 Sequence Number : 1446137055 Acknowledgement : 2383677921 TCP header length :
5Data : GET /cgi-bin/anonwww.cgi/http://static.guim.co.uk/static/68eea4bb5b8dc7a534c91cc328385fd1795612d7/common/styles/networkfront-grid.css HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
CGIProxy: 2014-03-25 13:23:54.020000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26298 Dest Port : 80 Sequence Number : 1155047647 Acknowledgement : 2390378000 TCP header length :
5Data : GET /cgi-bin/anonwww.cgi/http://static.guim.co.uk/static/68eea4bb5b8dc7a534c91cc328385fd1795612d7/zones/news/styles/zoneaccent.css HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
89
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
CGIProxy: 2014-03-25 13:23:54.074000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26299 Dest Port : 80 Sequence Number : 577388679 Acknowledgement : 2392481751 TCP header length : 5Data
: GET /cgi-bin/anonwww.cgi/http://static.guim.co.uk/static/68eea4bb5b8dc7a534c91cc328385fd1795612d7/zones/news/styles/gridzone-accent.css HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
CGIProxy: 2014-03-25 13:23:54.128000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
90
26300 Dest Port : 80 Sequence Number : 3856089961 Acknowledgement : 2387605545 TCP header length :
5Data : GET /cgi-bin/anonwww.cgi/http://combo.guim.co.uk/68eea4bb5b8dc7a534c91cc328385fd1795612d7/common/styles/basetypography+common/styles/carousel+common/styles/commercial-partners+common/styles/default-adplaceholders+common/styles/grid-pixies+common/styles/grid/editable-trailblock+common/styles/header-localinfo+common/styles/news-trails+common/styles/r3-component+common/styles/simple-newsdirect+common/styles/sublink-liveblog+common/styles/ticker+common/styles/topnavigation+common/styles/ventures-slot-machine+common/styles/weather-header.css HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22
CGIProxy: 2014-03-25 13:23:54.443000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26301 Dest Port : 80 Sequence Number : 3425872127 Acknowledgement : 2388131805 TCP header length :
5Data : GET /cgi-bin/anon-www.cgi/http://combo.guim.co.uk/68eea4bb5b8dc7a534c91cc328385fd1795612d7/m482~public/css/jobs-box-4.css HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf4-
91
83946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
PHPProxy: 2014-03-25 13:23:55.839000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26296 Dest Port : 80 Sequence Number : 2347257817 Acknowledgement : 3158127227 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL2ludGVyYWN0aXZlc3RvcmUvMjAxMy83LzkvM
TM3MzM4NjY2Njg1OS83NzM4NDkvRGlzY3Vzc2lvbldpZGdldC9jc3MvcmVzZXQuY3Nz HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer:
http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL2ludGVyYWN0aX
Zlc3RvcmUvMjAxMy83LzkvMTM3MzM4NjY2Njg1OS83NzM4NDkvRGlzY3Vzc2lvbldpZGdldC9pbmRleC5o
dG1s&nf=1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl
PHPProxy: 2014-03-25 13:23:55.944000
92
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26295 Dest Port : 80 Sequence Number : 3712091893 Acknowledgement : 1042119672 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL2ludGVyYWN0aXZlc3RvcmUvMjAxMy83LzkvM
TM3MzM4NjY2Njg1OS83NzM4NDkvRGlzY3Vzc2lvbldpZGdldC9jc3Mvc3R5bGVzLmNzcw%3D%3D
HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer:
http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL2ludGVyYWN0aX
Zlc3RvcmUvMjAxMy83LzkvMTM3MzM4NjY2Njg1OS83NzM4NDkvRGlzY3Vzc2lvbldpZGdldC9pbmRleC5o
dG1s&nf=1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN
PHPProxy: 2014-03-25 13:23:56.407000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26303 Dest Port : 80 Sequence Number : 73398181 Acknowledgement : 3042444661 TCP header length : 5Data :
GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9zdHlsZXMvaW1hZ2VzL3VzZXJfaWNvbl9ub2JnLmd
pZg%3D%3D HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
93
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2-Xm2gayUywZE
PHPProxy: 2014-03-25 13:23:56.512000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26302 Dest Port : 80 Sequence Number : 4165027379 Acknowledgement : 2097379172 TCP header length :
5Data : GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N5cy1pbWFnZXMvR3VhcmRpYW4vUGl4L3Bp
Y3R1cmVzLzIwMTQvMS8yNy8xMzkwODQyMzA1ODAwLzNiZWI3OGIxLTYyY2UtNDFjZS1iY2VhLTg3Z
DRiNmEzYmQ5My0xNDB4ODQucG5n HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
94
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0as
PHPProxy: 2014-03-25 13:24:03.119000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 199.217.117.140Source Port :
26305 Dest Port : 80 Sequence Number : 396864397 Acknowledgement : 183236442 TCP header length : 5Data :
GET
/index.php?q=aHR0cDovL3N0YXRpYy5ndWltLmNvLnVrL3N0YXRpYy82OGVlYTRiYjViOGRjN2E1MzRjO
TFjYzMyODM4NWZkMTc5NTYxMmQ3L2NvbW1vbi9zdHlsZXMvaW1hZ2VzL2ljb25fYnVsbGV0LnBuZw%
3D%3D HTTP/1.1
Host: www.proxyanonymizer.net
Connection: keep-alive
Cache-Control: max-age=0
Accept: image/webp,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://www.proxyanonymizer.net/index.php?q=aHR0cDovL3d3dy50aGVndWFyZGlhbi5jb20vdXM%3D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: COOKIE%253Bmc%253B%252F%253B.quantserve.com=530373a8-73f54-dba6b-9d388%253B;
COOKIE%253BV5%253B%252F%253B.imrworldwide.com=AStfNx46Mh4GMQsMIDojIyElOBYSK1InHlKcr
g__%253B;
COOKIE%253BIMRID%253B%252F%253B.imrworldwide.com=UwNzqdSbxhUAAHQpypI%253B;
COOKIE%253Bid%253B%252F%253B.doubleclick.net=22e752c582020012%257C%257Ct%253D1392735179
%257Cet%253D730%257Ccs%253D002213fd483eb1b6d3122347b2%253B;
COOKIE%253BHSID%253B%252F%253B.google.com=AYbrgmSl3t6EYOOO8%253B;
COOKIE%253BSSID%253B%252F%253B.google.com=AWn7w9Y2gSG26BcPq%253BSecure;
COOKIE%253BAPISID%253B%252F%253B.google.com=OOIQZ2yjrpeyQbT%252FAztS_S3Id0es5l27_%253B;
COOKIE%253BSAPISID%253B%252F%253B.google.com=9v_cLVDMPhab99e8%252FAecGGMzHsvRUi5X_
u%253BSecure;
COOKIE%253BACCOUNT_CHOOSER%253B%252F%253Baccounts.google.com=AFx_qI5N2Aj9-kYd4BnQinJchNUmvaTk6OwCN92hWI0cl5DgXiUuXbBdWCFmRGDE4PwV1O9Ch0asHOr2-Xm2gayUywZEeC8G
CGIProxy: 2014-03-25 13:24:03.835000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26311 Dest Port : 80 Sequence Number : 520056534 Acknowledgement : 2397837889 TCP header length : 5Data
: GET /cgi-bin/anon-
95
www.cgi/http://static.guim.co.uk/static/68eea4bb5b8dc7a534c91cc328385fd1795612d7/common/styles/shame.css
HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
CGIProxy: 2014-03-25 13:24:03.887000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 193.200.150.137Source Port :
26312 Dest Port : 80 Sequence Number : 1644790001 Acknowledgement : 2387609490 TCP header length :
5Data : GET /cgi-bin/anon-www.cgi/http://ajax.googleapis.com/ajax/libs/jquery/1.8.1/jquery.min.js HTTP/1.1
Host: anonymouse.org
Connection: keep-alive
Cache-Control: max-age=0
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer: http://anonymouse.org/cgi-bin/anon-www.cgi/http://www.theguardian.com/uk
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: __qca=P0-1151656657-1392741294427; noticebar_cookie=2; _cb_ls=1; eas_uid=61395746946466380812; fsr.s=%7B%22v2%22%3A-2%2C%22v1%22%3A1%2C%22rid%22%3A%22d445cf483946616-bf12-e194664d1%22%2C%22ru%22%3A%22http%3A%2F%2Fanonymouse.org%2Fanonwww.html%22%2C%22r%22%3
A%22anonymouse.org%22%2C%22st%22%3A%22%22%2C%22to%22%3A3%2C%22c%22%3A%22http%3A
%2F%2Fanonymouse.org%2Fcgi-bin%2Fanonwww.cgi%2Fhttp%3A%2F%2Fwww.theguardian.com%2Fuk%22%2C%22pv%22%3A1%2C%22lc%22%3A%7
B%22d0%22%3A%7B%22v%22%3A1%2C%22s%22%3Atrue%7D%7D%2C%22cd%22%3A0%2C%22sd%22
96
%3A0%7D; _chartbeat2=f6n7i50i5c7nt01g.1392741314017.1395746958286.0000000001000101;
_chartbeat_uuniq=2
If-Modified-Since: Tue, 04 Sep 2012 17:57:57 GMT
GLYPE: 2014-03-25 13:24:03.990000
Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f Protocol : 8Version : 4 IP Header Length :
5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination Address : 74.50.112.6Source Port : 26309
Dest Port : 80 Sequence Number : 2410139483 Acknowledgement : 2879662378 TCP header length : 5Data : GET
/browse.php?u=6AgaxvFYBW6j0E6KXRzXpl%2BQhnyCEeo%2Bw8Tg13bjj9vc3fhiDES0yf92aJ2L22khyCtVt1
CwTMV9Du1syCrB1hGXmWIjtlFzoFCHuiGbQ09Sz1fu8itlrP5kglPYj8nGuFpAb5ve7uKT&b=29 HTTP/1.1
Host: proxyserver.com
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer:
http://proxyserver.com/browse.php?u=6AgawvJOX3Oom06KVQOdrFHQ3XTCD7EqxA%3D%3D&b=29
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Cookie: _jsuid=1665540709;
optimizelySegments=%7B%22172123993%22%3A%22none%22%2C%22172233718%22%3A%22false%22%2
C%22172284779%22%3A%22gc%22%2C%22172368238%22%3A%22direct%22%7D;
optimizelyEndUserId=oeu1392840168231r0.8635799209587276; optimizelyBuckets=%7B%7D; __qca=P01455934236-1392840171913; noticebar_cookie=1; rbm8vrpt=EDXVqN4Vq8g6sSilZMN3ayE1F4Dqhg0%3D;
s=h4ukf5v26qeordn5bgpdn0t0d7; _referrer_og=http%3A%2F%2Flist.glype.com%2F;
__utma=231926494.1052874444.1392644316.1395746892.1395753733.27;
__utmb=231926494.1.10.1395753733; __utmc=231926494;
__utmz=231926494.1395746892.26.15.utmcsr=list.glype.com|utmccn=(referral)|utmcmd=referral|utmcct=/;
_first_pageview=1; __atuvc=10%7C9%2C6%7C10%2C2%7C11%2C4%7C12%2C2%7C13;
_eventqueue=%7B%22heatmap%22%3A%5B%5D%2C%22events%22%3A%5B%5D%7D
GLYPE: 2014-03-25 13:24:04.044000Destination MAC : 70:72:3c:db:c3:19 Source MAC : ac:72:89:8e:4a:9f
Protocol : 8Version : 4 IP Header Length : 5 TTL : 128 Protocol : 6 Source Address : 192.168.1.101 Destination
Address : 74.50.112.6Source Port : 26307 Dest Port : 80 Sequence Number : 1357729599 Acknowledgement :
2377642980 TCP header length : 5Data : GET
/browse.php?u=6AgaxvFYBW6j0E6KXRzXpl%2BQhnyCEeo%2Bw8Tg13bjj9vc3fhiDES0yf92aJ2L22khyCtVt1
CwTMV9Du1syCrB1hGXmWIjr1FwqEzG%2BzeYSQxEyAHs8iw9pP5myxjQj8nXuFxRZZqe%2Bb%2BDw5A
%3D&b=29 HTTP/1.1
Host: proxyserver.com
Connection: keep-alive
Cache-Control: max-age=0
Accept: text/css,*/*;q=0.1
97
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)
Chrome/33.0.1750.154 Safari/537.36
Referer:
http://proxyserver.com/browse.php?u=6AgawvJOX3Oom06KVQOdrFHQ3XTCD7EqxA%3D%3D&b=29
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Appendix C: Instruction Set
Instruction Set - For Windows 7
1. Download and install Python 2.5.6 from here:
https://www.python.org/download/releases/2.5.6/. IDLE is also part of the package, it
will be used in a later stage.
2. Open the IDS.py with IDLE
3. Locate ‘directory = "C:\ProxyTempLogs"’, this is the set directory for storing the
log files; this can be edited to suit the user needs.
4. Start the program by selecting Run -> Run Module, or press f5.
5. A list of the available interfaces will appear. To find out which one to use, open the
control panel -> Network and Internet -> Network Connections. Then locate the one
you want to scan, if it is the 3rd one in the list, select it in IDLE.
6. This will start the program searching the network for proxies.
7. If any proxies are found, they will be located in the directory under the file
containing the date and the time the program was started.
98
Instruction Set - For Linux (BackTrack was used in this example)
1. Open up the command line and type in the following: svn checkout
http://pyrit.googlecode.com/svn/trunk/ pyrit_svn
2. Once that has completed type in the following: apt-get install libssl-dev
3. Next step is to type in the following: apt-get install scapy
4. Once that is done type in this: apt-get install python-dehow to install
5. Following this go to: cd pyrit_svn/pyrit
6. Then do the build: python setup.py build
7. And install it with: python setup.py install
8. They are the steps to install Python on Backtrack, once that is completed the
program can be started.
9. To run the program, open up a terminal and type: python IDS.py, this will start the
program running and the user can select the interface they want to scan
99
 0
0
advertisement
Related documents
Download
advertisement
Add this document to collection(s)
You can add this document to your study collection(s)
Sign in Available only to authorized usersAdd this document to saved
You can add this document to your saved list
Sign in Available only to authorized users