Moinul Zaber's presentation on TCP/IP security threats
advertisement

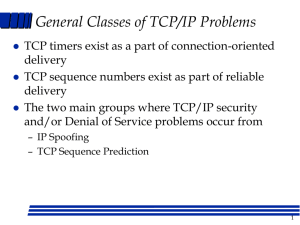
Are you secured in the network ?: a quick look at the TCP/IP protocols Based on: A look back at “Security Problems in the TCP/IP Protocol Suite” by Steven M. Bellovin, AT&T Labs-Research Presented by :Moinul I Zaber, Kent State University What’s on Today! • • • • • • A soft brief on the Network Security Problems that we have inherited ! TCP sequence number Prediction IP spoofing Routing Threats Application layer Threats : E-mails, Finger, FTP Introduction • Internet is a system of interconnected computers. • Layers of communication types and interfaces connects them. • TCP/IP is the dominant Protocol • We will discuss some security problems inherent to this layered protocol. • TCP is the process to process connectivity • IP is the source to destination connectivity A brief on TCP/IP TCP sequence Number Prediction • The normal TCP connection establishment sequence involves a 3-way handshake. The client selects and transmits an initial sequence number ISNc, the server acknowledges it and sends its own sequence number ISNs, and the client acknowledges that. That is, for a conversation to take place, C must first hear ISNS, a more or less random number. Suppose, though, that there was a way for an intruder X to predict ISNS. In that case, it could send the following sequence to impersonate trusted host T: So How to predict the sequence number ? • The initial sequence number variable is incremented by a constant amount once per second and by half that amount each time a connection is initiated. • Thus if one initiates a legitimate connection and observes the ISNs one can calculate the ISNs’ used on the next connection attempt. • The real host T receives the Server S’s ack so Flooding/ DOS attack should be opted against T to S->T message should be lost. • Using ‘netstat’ could be a good option to get the sequence number! Defenses Against Syn Prediction • TCP sepcs requires that this variable be incremented approximately 250,000 times per second. But unfortunately this does not help as RTT Could be easily guessed. • Randomizing the increment of the sequence number. IP Spoofing • In spoofing (fooling, deceiving), an attacker impersonates someone else. • This allows him/her to exploit the access privileges of the spoofed. • IP spoofing is the creation of TCP/IP packets with somebody else's IP address in the header. • Routers use the destination IP address to forward packets, but ignore the source IP address. • The source IP address is used only by the destination machine, when it responds back to the source. • When an attacker spoofs someone’s IP address, the victim’s reply goes back to that address. • Since the attacker does not receive packets back, this is called a one-way attack or blind spoofing. • To see the return packets, the attacker must intercept them. Misconception (IP spoofing) • A common misconception is that via spoofing you can surf the net, chat on line, send/receive email while hiding your identity. • This is not possible since the replies do not go to you. Basic types of IP spoofing attacks • • • • Basic address change Use of source routing to intercept packets Exploitation of trust relationships on UNIX machines • Session Hijacking IP session Hijacking • Here the user’s session is taken over. • Let user on Host A is carrying on a telnet session with host G. Host H is ran by a naughty person. He watches the traffic between A and G and runs a tool which starts to impersonate A to G, and at the same time tells A to shut up. • After a few seconds of this if the attack is successful, the naughty person has hijacked illegitimately. • G knows nothing has happened. Routing!! Routing- Somebody’s Following! • Source Routing • One way for an attacker to see return traffic from a spoofing attack is for him to insert himself in the path the traffic would normally take. • Internet routing is normally dynamic, there is no guarantee that the same route between 2 IPs is always taken. • Source routing can be used to guarantee that a packet follows a set path Routing Information Protocol Attacks How does it work! Loose source routing (LSR): The sender specifies a list of some IP addresses that a packet must go through (it might go through more) An attacker sends a packet to the destination with a spoofed address but specifies LSR and puts his IP address in the list. Defenses against Source Routing Attack • It is rather hard! • The best way to protect against source routing spoofing is to simply disable source routing at your routers. • Gateways into the local net can reject external packets that claim to be from the local net. ( less practical. What will happen to organizations that has two trusted networks connected via a multiorganization backbone ?) • Warning!!!: fire walls don’t defend against insider attacks! RIP attack • Routing Information Protocol (RIP) is used to propagate routing information on local networks, especially broadcast media. • Typically, the information received is unchecked! • This allows an intruder to send bogus routing information to a target host, and to each of the gateways along the way, to impersonate a particular host. Defenses Against RIP attack • Easier to defend! • A paranoid gateway- one that filters packets based on source or destination address- will block any form of host spoofing( including TCP sequence number attacks). ICMP- friends can also become a foe! • Internet control message protocol (ICMP) is the basic network management tool. • ICMP attacks are rather difficult and rare! • ICMP redirect message (used by gateways to advise hosts of better routes). • It can often be abused in the same way the RIP can. • Intruder penetrating a secondary gateway available to the target can do the harm. Defenses against ICMP attacks • Easy! If a host is careful about checking that message rally does refer to a particular connection, most such attacks will not succeed. • Don’t worry! It’s never been real! Application layer • Finger service : this server display useful information about users. • Netstat, tracert, • E-mail: mail server provides no authentication mechanisms. The door is wide open for faked messages! Discussion!!