Core Concepts of
ACCOUNTING INFORMATION SYSTEMS
Moscove, Simkin & Bagranoff
Developed by:
Marianne Bradford, Ph.D.
Bryant College
John Wiley & Sons, Inc.
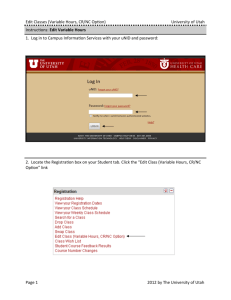
Chapter 8
Controls for Computerized
Accounting Information Systems
•
•
•
•
•
Introduction
General Controls within IT Environments
Application Controls within IT Environments
Database Controls
Controls in the Information Age
Computer Control Procedures
• Computer controls are frequently classified into
two categories:
• General controls ensure that a company’s
control environment is stable and well managed
in order to strengthen the effectiveness of
application controls.
• Application controls are designed to prevent,
detect, and correct errors and irregularities in
transactions as they flow through the input,
processing, and output stages of data processing.
Reasons Why Computers Can
Cause Control Problems
• Effects or errors may be magnified.
• Inadequate separation of duties because of
decreased manual involvement
• Audit trails may be reduced, eliminated,
or exist only for a brief time.
• Changes to data and programs may be
made by individuals lacking knowledge.
• More individuals may have access to
accounting data.
• Accounting data stored in computer-based
systems are oriented to characteristics of
magnetic or optical media.
Objectives of Controls over the
Data Processing Function
To provide reasonable assurance that:
– development of, and changes to, computer
programs are authorized, tested and
approved prior to their usage.
– access to data files is restricted to
authorized users and programs.
• These objectives are
referred to as general
computer control
objectives.
General Controls within IT
Environments
• Personnel Controls
• File Security Controls
• Fault-Tolerant Systems, Backup,
and Contingency Planning
• Computer Facility Controls
• Access to Computer Files
Personnel Controls Separation of Duties
• Separation of duties, which separates
incompatible functions, is a central control
objective when designing a system.
• In IT environments separation of duties should
include:
– separating accounting and information
processing subsystems from other subsystems
– separate responsibilities within the IT
environment
More Personnel Controls
• Companies use separate computer
accounts that are assigned to users on
either a group or individual basis.
– Passwords are checked against a master list.
– Call-back procedures restrict access from
remote terminals.
• An informal knowledge of employees and
their activities can be an important clue
for the detection of fraud.
File Security Controls
• The purpose of file security controls is to
protect computer files from either
accidental or intentional abuse.
Examples:
•
•
•
•
•
External file labels
Internal file labels
Lock-out procedures
File protection rings
Read-only file designations
Risks that Control Procedures
Seek to Reduce
• Control procedures are aimed at
reducing financial risk, the chance that
financial statements are misstated.
• Controls also seek to reduce business
risk, the risk that the viability of the
business is impacted by lack of
control.
Fault-Tolerant Systems
• Fault-tolerant systems are designed to tolerate
faults or errors and are often based on the
concept of redundancy.
• Two major approaches to redundant CPU
processing are consensus-based protocols and
watchdog protocols.
• Disk mirroring (disk shadowing) is a process
used to make disks fault-tolerant.
• Under roll-back processing transactions are
never written to disk until they are complete.
Backup
• All companies should backup their vital
documents, files and programs.
• Grandfather-parent-child procedure is used
during batch processing.
• Through electronic vaulting, data
on backup tapes can be electronically
transmitted to remote sites.
• An uninterruptible power system
(UPS) is an auxiliary power supply
that can prevent the loss of data due
to momentary surges or dips in power.
Contingency Planning
• Contingency planning includes the development of a
formal disaster recovery plan.
• This plan describes procedures to be followed in the
case of an emergency as well as the role of each
member of the disaster recovery team.
• The goal is to recover processing
capability as soon as possible.
• A disaster recovery site can either be a
hot site or cold site.
Computer Facility Controls
• Locate the Data Processing Center in a safe
place.
• Limit employee access.
• Buy insurance.
Access to Computer Files
• Password codes and biometric identifications
restrict logical access to data.
• Biometric identification devices identify
distinctive user physical characteristics such
as voice patterns, fingerprints and retina
prints.
Application Controls within
IT Environments
• Application controls pertain directly to the
transaction processing systems.
• The objectives of application controls are to
prevent, detect and correct errors and
irregularities in transactions that are processed
in an IT environment.
• Application controls are subdivided into input,
processing and output controls.
Input Controls
• Input controls attempt to ensure the
validity, accuracy and completeness of
the data entered into an AIS.
• The categories of input controls include 1)
data observation and recording
2) data transcription
3) edit tests
4) additional input controls
Data Observation and
Recording Controls
•
•
•
•
Feedback mechanism
Dual observation
Point-of-sale (POS) devices
Preprinted recording forms
Data Transcription
• Data transcription refers to the
preparation of data for computerized
processing.
• Preformatted screens that
use “masks” are an
important control
procedure.
Edit Tests
• Input validation routines (edit programs) check
the validity and accuracy of input data after
the data have been entered and recorded on a
machine-readable file.
• Edit tests examine selected fields of input data
and reject those transactions whose data fields
do not meet the pre-established standards of
data quality.
• Real-time systems use edit checks during dataentry.
Examples of Edit Tests
Tests for:
• Numeric field
• Alphabetic field
• Alphanumeric field
• Valid code
• Reasonableness
• Sign
• Completeness
• Sequence
• Consistency
Processing Controls
• Processing controls focus on the
manipulation of accounting data after
they are input to the computer system.
• Two kinds:
1) Data-access controls
2) Data manipulation controls
Data-Access Control Totals
•
•
•
•
•
Batch control total
Financial control total
Nonfinancial control total
Hash total
Record count
Data Manipulation Controls
•
•
•
•
•
Once data has been validated by earlier
portions of data processing, they usually must
be manipulated in some way to produce useful
output. Data manipulation controls include:
Software documentation
Compiler
Test Data
System testing
Output Controls
• The objective of output controls is to assure the
output’s validity, accuracy and completeness.
• Activity (or proof) listings provide complete, detailed
information about all changes to master files.
• Forms control is vital for forms associated with
check-writing.
• Prenumbered forms are the most
common type of control utilized with
computer-generated check-writing
procedures.
• Shred sensitive documents
Database Controls
• Database management software
• Layered passwords
• Complete documentation including data
dictionary
• Database administrator
• Security modules
• Authorization and approval of all significant
modifications to software
• Changes made by authorized individuals
Risks Unique to
Micro Environment
• Hardware - microcomputers can be easily
stolen or destroyed
• Data and software - easy to access,
modify, copy or destroy; therefore,
are difficult to control.
Control Procedures for
Microcomputers
•
•
•
•
•
•
Take inventory
Keyboard locks
Lock laptops in cabinets
Software protection procedures
Back-up files
Lock office doors
Additional Controls for
Laptops
• Identify your laptop
• Use nonbreakable cables to attach
laptops to stationary furniture
• Load antivirus software
• Keep laptop information
backed up
Controls for Computer
Network Systems
• Data encryption minimizes the risk of unauthorized
access to data through electronic eavesdropping.
• A checkpoint should be established to facilitate
recovery from a system failure.
• Routing verification procedures help to ensure that no
transactions or messages are routed to the wrong
computer network system address.
• Message acknowledgement procedures are useful in
preventing the loss of part or all of a transaction or
message on a computer network system.
Copyright
Copyright 2001 John Wiley & Sons, Inc. All rights reserved.
Reproduction or translation of this work beyond that permitted in
Section 117 of the 1976 United States Copyright Act without the
express written permission of the copyright owner is unlawful.
Request for further information should be addressed to the
Permissions Department, John Wiley & Sons, Inc. The purchaser may
make backup copies for his/her own use only and not for distribution
or resale. The Publisher assumes no responsibility for errors,
omissions, or damages, caused by the use of these programs or from
the use of the information contained herein.
Chapter 8