Hall & Singleton
advertisement

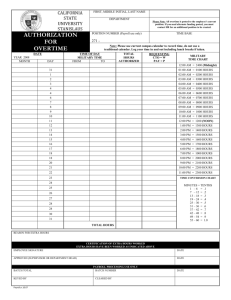
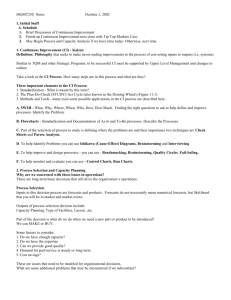
Chapter 10: Auditing the Expenditure Cycle IT Auditing & Assurance, 2e, Hall & Singleton PURCHASES: BATCH PROCESSING Step 1: Data processing department – inventory control Step 2: Data processing department – P.O. Receiving Department Step 3: Data processing department – batch update of inventory Purchasing Department Accounts Payable Step 4: Data processing department – validates vendors CASH DISBURSEMENT: BATCH PROCESSING Step 5: Data processing department – scans for items due and prints checks for items received Step 6: Cash disbursements department – reconciles checks, submits checks to management for signature Step 7: Accounts payable – matches copies of checks with open vouchers, closes them and files documents Concludes expenditure cycle CASH DISBURSEMENT: REENGINEERED—FULLY AUTOMATED Data processing steps performed automatically: 1. 2. 3. 4. 5. 6. 7. Inventory file scanned for items and reorder points Purchase requisition record for all items needing replenishment Consolidate requisitions by vendor Retrieve vendor mailing information P.O. prepared and sent to vendor (EDI) Open P.O. record added for each transaction List of P.O. sent to purchasing department CASH DISBURSEMENT: REENGINEERED– FULLY AUTOMATED Goods arrive at receiving department Quantities received entered per item CASH DISBURSEMENT: REENGINEERED—FULLY AUTOMATED Data processing steps performed automatically: 1. 2. 3. 4. 5. Quantities keyed matched to open P.O. record Receiving report file record added Update inventory subsidiary records G.L. inventory updated Record removed from open P.O. file and added to open A.P. file, due date established CASH DISBURSEMENT: REENGINEERED—FULLY AUTOMATED Each day, due date filed of A.P. are scanned for items where payment is due CASH DISBURSEMENT: REENGINEERED—FULLY AUTOMATED Data processing steps performed automatically: 1. 2. 3. 4. 5. Checks are printed, signed and distributed to mailroom (unless EDI/EFT) Payments are recorded in check register file Items paid are transferred from open A.P. to closed A.P. file G.L.- A.P. and cash accounts are updated Appropriate reports are transmitted to A.P. and cash disbursements departments for review CASH DISBURSEMENT: REENGINEERED—FULLY AUTOMATED Control implications General in nature Similar to those of Chapter 9 BATCH AUTOMATED SYSTEM VS. MANUAL BATCH Improved inventory control Better cash management Less time lag Better purchasing time management Reduction of paper documents REENGINEERED SYSTEM VS. BATCH AUTOMATED SYSTEM Segregation of duties Accounting records and access controls PAYROLL PROCEDURES Drawbacks to using regular A.P. and cash disbursements systems to do payroll General expenditure procedures that apply to all vendors will not apply to employees Writing checks to employees requires special controls General expenditure procedures are designed to accommodate relatively smooth flow of transactions REENGINEERED PAYROLL SYSTEM Often integrated with H.R. Differs from previous automate system Operations departments transmit transactions to D.P. electronically Direct access to files are used for data storage Many processes are now performed in real time REENGINEERED PAYROLL SYSTEM Personnel Cost accounting Timekeeping Data processing 1. 2. 3. 4. 5. 6. 7. Labor costs are distributed to accounts Online labor distribution summary Online payroll register Employee records are updated Payroll checks are prepared and signed Disbursement system generates check to fund the payroll imprest account G.L. updated EXPENDITURE CYCLE AUDIT OBJECTIVES Input controls Data validation controls Testing validation controls Batch controls Testing batch controls Purchases authorization controls Testing purchases authorization controls Employee authorization Testing employee authorization procedures EXPENDITURE CYCLE AUDIT OBJECTIVES Process controls File update controls Sequence check control Liability validation control Valid vendor file Testing file update controls Access controls Warehouse security Moving assets promptly when received Paying employees by check vs. cash Risks • • • • Employees with access to A.P. subsidiary file Employees with access to attendance records Employees with access to both cash and A.P. records Employees with access to both inventory and inventory records Testing access controls EXPENDITURE CYCLE AUDIT OBJECTIVES Process controls Physical controls Purchase system controls Segregation of inventory control from warehouse Segregation of G.L. and A.P. from cash disbursements Supervision of receiving department • • • Payroll System controls • • • • Inspection of assets Theft of assets Reconciliation of supporting documents: P.O., receiving report, supplier’s invoice Verification of timecards Supervision Paymaster Payroll imprest account Testing of physical controls EXPENDITURE CYCLE AUDIT OBJECTIVES Process controls Output controls A.P. change report Transaction logs Transaction listing Logs of automatic transactions Unique transaction identifiers Error listing Testing output controls EXPENDITURE CYCLE SUBSTANTIVE TESTS Risks and audit concerns Understanding data Inventory file Purchase order file Purchase order line item file Receiving report file Disbursement voucher file File preparation procedures EXPENDITURE CYCLE SUBSTANTIVE TESTS Testing accuracy and completeness assertions Review disbursement vouchers for unusual trends and exceptions Accurate invoice prices Testing completeness, existence, rights and obligations assertions Searching for unrecorded liabilities Searching for unauthorized disbursement vouchers Review of multiple checks to vendors Auditing payroll and related records Additional Cybercrime Info The following slides are not in the text! Incident Response Mandates Gramm-Leach-Bliley Financial Institutions must … Establish incident response capability Perform prompt and reasonable investigation when sensitive customer info is accessed Notify customers if misuse of info has or is likely to occur Incident Response Requirements ISO 17799 ISO 17799 is international standard for IS best practices Security framework must contain an effective incident response approach In 2002, 22% companies with sales over $500 million had implemented ISO 17799 Must collect information for three purposes … Internal problem analysis Use as evidence Negotiation for compensation from software/service vendors Incident Response Requirements ISO 17799 Response procedures should cover … Analysis and identification of cause of incident Planning and implementation of remedies Collection of audit trails and similar evidence Communication with those affected or involved with recovery Reporting the action to the appropriate authority Best Practices Imaging hard drive of employees who resign or are terminated (proactive) Avoid “patch and proceed” response Implement network forensics analysis with tools like EnCase Focus on insider threats Companies face increasing cyberliability claims stemming from security breaches Chapter 10: Auditing the Expenditure Cycle IT Auditing & Assurance, 2e, Hall & Singleton