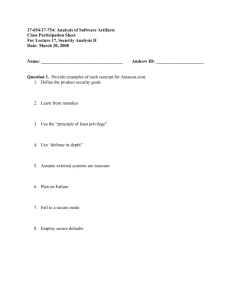
Document
advertisement

Lancope, Inc. 3155 Royal Drive, Bldg. 100 Alpharetta, GA 30022 Presentation to the Georgia Research Alliance June 14, 2002 Chairman - Dr. John Copeland VP Eng. - John Jerrim VP Sales - Barry Fischel VP Op.s - John Balsam CFO - David Cocchiara 30 employees and growing Network Threat Management History Dec. 1999 - Dr. John Copeland discovers preparations for a DDOS involving Mac OS-9 computers. No signatures available. Work starts on a system that will detect network mischief without prior signatures. Aug. 2000 - First StealthWatch system starts running at a NC College. Oct. 2000 - LANcope incorporates, with $1.5M from private investor. Joins ATDC at Georgia Tech. April 2001 - First commercial sales to S-A, Neilsen TV Ratings, Bass Hotels, … May 2001 - GigE System sees Short-Fragment Attack at Weather.com. Code Red seen arriving at Carnival Cruise lines. March 2002 - $5.5M investment from HIG Ventures and GMG Partners allows build up of Sales and Marketing teams. May 2002 - StealthWatch wins PC Magazine/eWeek Award for most innovative product in the Security Area for 2002 Network Threat Management Network Intruders Masquerader: A person who is not authorized to use a computer, but gains access appearing to be someone with authorization (steals services, violates the right to privacy, destroys data, ...) Misfeasor: A person who has limited authorization to use a computer, but misuses that authorization (steals services, violates the right to privacy, destroys data, ...) Clandestine User: A person who seizes supervisory control of a computer and proceeds to evade auditing and access controls. Network Threat Management 3 The Stages of a Network Intrusion Trojan Horse From email, Web, floppy disk 1. Scan the network to: • locate which IP addresses are in use, • what operating system is in use, • what TCP or UDP ports are “open” (being listened to by Servers). 2. Run “Exploit” scripts against open ports 3. Get access to Shell program which is “suid” (has “root” privileges). 4. Download from Hacker Web site special versions of systems files that will let Cracker have free access in the future without his cpu time or disk storage space being noticed by auditing programs. 5. Use IRC (Internet Relay Chat) to invite friends to the feast. Network Threat Management 4 Protection from a Network Intrusion 1. Use a “Firewall” between the local area network and the worldwide Internet to limit access (Chapter 10). 2. Use an IDS (Intrusion Detection System) to detect Cracker during the scanning stage (lock out the IP address, or monitor and prosecute). 3. Use a program like TripWire on each host to detect when systems files are altered, and email an alert to Sys Admin. 4. On Microsoft PC’s, a program like Zone Alarm is easier to install than learning how to reset default parameters to make the system safe. Network Threat Management 5 Protection from a Network Intrusion Network Traffic Monitoring Systems, such as SteathWatch (SW) can be placed at various points in a network - using taps, repeating hubs, or monitoring ports on an Ethernet switch. Network Threat Management Statistical Anomaly-Based Intrusion Detection High statistical variation in most measurable network behavior parameters results in high false-alarm rate False Alarms Undetected Intrusions Detection Threshold Network Threat Management 7 Distributed Host-Based IDS Highly recommended for critical servers Modules must be installed and configured on hosts. Network Threat Management 8 Signature-Based IDS Data Packets are compared to a growing library of known attack signatures. These include port numbers or sequence numbers that are fixed in the exploit application, and sequences of characters that appear in the data stream. Packet streams must be assembled and searched, which reduces the maximum possible data rate on the link being observed. Network Threat Management Six “Signatures” from the Snort Database www.snort.org alert tcp $EXTERNAL_NET any -> $HOME_NET 7070 (msg: "IDS411 RealAudio-DoS"; flags: AP; content: "|fff4 fffd 06|";) alert udp $EXTERNAL_NET any -> $HOME_NET any (msg: "IDS362 - MISC Shellcode X86 NOPS-UDP"; content: "|90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90|";) alert tcp $EXTERNAL_NET any -> $HOME_NET any (msg:"IDS359 OVERFLOW-NOOP-HP-TCP2";flags:PA; content:"|0b39 0280 0b39 0280 0b39 0280 0b39 0280|";) alert tcp $EXTERNAL_NET any -> $HOME_NET any (msg:"IDS345 OVERFLOW-NOOP-Sparc-TCP";flags:PA; content:"|13c0 1ca6 13c0 1ca6 13c0 1ca6 13c0 1ca6|";) alert udp $EXTERNAL_NET any -> $HOME_NET any (msg:"IDS355 OVERFLOW-NOOP-Sparc-UDP2"; content:"|a61c c013 a61c c013 a61c c013 a61c c013|";) alert tcp $EXTERNAL_NET any -> $HOME_NET any (msg: "IDS291 - MISC Shellcode x86 stealth NOP"; content: "|eb 02 eb 02 eb 02|";) Network Threat Management Signature-Based Intrusion Detection Systems May Not Detect New Types of Attack Back Orifice Land Attack Win Nuke IP Blob Trino Attacks with Names Attacks without Names (not analyzed yet) Alarm on Activities in these areas. Network Threat Management Flow-Based Technology - An approach that recognizes normal traffic can detect new types of intrusions. Back Orifice Land Attack FTP Web Win Nuke IP Blob NetBIOS Trino Email Attacks with Names Attacks without Names (not analyzed yet) Normal Network Activities Alarm on Activities in this areas. Network Threat Management Flow-based Analysis FlowStatistics Counters FlowStatistics Counters Number of Packets A “Flow” is the stream of packets from one host to another related to the same service (e.g., Web, email, telnet, …). Data in packet headers is used to build up counts (leads to high speed). After the flow is over, counters are analyzed and a value is derived for the probability that the flow was crafted, perhaps for probing the network for vulnerabilities or for denial of service. Number of Total Bytes Number of Data Bytes Start Time of Flow Stop Time of Flow Duration of Flow Flag-Bit True-False Combo Fragmentation Bits ICMP Packet Responses to UDP Packets Counters Network Threat Management Port Profiling (as in StealthWatch) Detecting “Ugly” that otherwise looks “Good” Network Threat Management 14 Zone Profiling (as in StealthWatch) Detecting “Ugly” that otherwise looks “Good” Network Threat Management “Port Locking” will not alarm if the FTP Client and Server App.s are in the Hosts’ Port Profiles Internet “Zone Locking” will alarm if the FTP Client and Server App.s are not in the same Zone and cross-zone is not permitted FTP Server FTP Server FTP Client FTP Client Finance Subnet Engineering Subnet Network Threat Management IDS Solutions Should be Combined Host-Based Can detect misuse of OS access and file permissions. Signature-Based Can detect attacks embedded in network data -if signature is known Anomaly-Based On host or network. Can detect new types, but high false alarm rate. Flow-Based Can detect new types of attacks by network activity. Should be used with Host-Based and/or Signature Based Network Threat Management The Stages of a Network Intrusion Trojan Flow-based "CI”, ”Port-Lock”, and/or “Zone-Lock”; signature-based? 1. Scan the network to: • locate which IP addresses are in use, • what operating system is in use, • what TCP or UDP ports are “open” (being listened to by Servers). 2. Run “Exploit” scripts against open ports Signature-based, if Known exploit 3. Get access to Shell program which is “suid” (has “root” privileges). Host-based 4. Download from Hacker Web site special versions of systems files that will let Cracker have free access in the future without his cpu time or disk storage space being Host-based noticed by auditing programs. Flow-based "Port-Locking” & ”Zone-Locking” 5. Use IRC (Internet Relay Chat) to invite friends to the feast. Flow-based "Port-Locking” & “Port-Locking”, Host-based Network Threat Management 18 Examples of “Bad” that have been seen At 8 p.m. on a Sunday evening, a T1 Internet is completely jamming for 45 minutes because 120 hosts start downloading 1.2 MB files from a CAI FTP server. At 11 am. on Saturday morning external host on the same Class C subnet start sucking down 100’s of Megabytes of data from every Web server on campus. One week-end before Napster was reportedly going out of business, two hosts jam the T1 Internet connection by downloading Gigabytes of data from peerto-peer servers. A host appears to be repeatedly scanning the network for servers on a halfdozen different port numbers. A host in Europe repeatedly scans the U.S. division’s network for UDP servers on dozens of high-number ports. A host sends 25 packets per second for hours to a NetBIOS port on another host, all of which receive ICMP Port Unavailable responses. A broadcast server that consumes a good fraction of a network’s bandwidth operates at 10% efficiency (90% of the bytes are header bytes). Network Threat Management Examples of “Ugly” that have been seen A host at a U.S. college starts scanning networks in the UK and France using SYN-FIN packets, while reporting the results of the scans by a Telnet connection to a host in Slovinia. At 6 p.m. on a Friday before Spring Break at a U.S.college, a host starts scanning networks in Korea at the rate of almost one million per hour. This continues for days, causing one sniffer to fail just because of the high rate of short packets. An interactive Internet game server open for world-wide participation is discovered operating deep within a supposedly secure network. A half-dozen hosts have active SubSeven Trojans operating. A rapid rate of short fragmented packets brings down a top-ten Web site for half a day. Logs reveal the attacker was experimenting with different types of crafted fragmented packets. Network Threat Management Detection of the “Mac Attack” DDoS Plan Type "A" Probes (detected by Dr. John Copeland – Lancope Founder - in Dec. 1999) The first three UDP probes, which started my investigation, had a single character in the data field, an 'A'. The UDP port numbers were identical, 31790->31789. They stimulate the 1500-byte ICMP Echo-Request packet and the normal 58-byte ICMP Destination_Unreachable-Port Packets. The Echo-Request is never answered. Date Time EST Source IP (Place) Destination (Place) 1999-12-28 18:40 151.21.82.251 (Italy) to 24.88.48.47 (Atlanta, GA) 1999-12-10 18:28 152.169.145.206 ( AOL ) to 24.88.48.47 (Atlanta, GA) 1999-12-16 03:34 212.24.231.131 (Saudi Arabia) to 24.88.48.47 (Atlanta, GA) UDP packets with an empty data field, like those generated by the "nmap" scan program, do not stimulate the 1500-byte ICMP packets from an OS-9 Macintosh. 21 Network Threat Management 2nd Generation, “Mac Attack” Scanning "Double-zero" Probes (James Bond, "00" -> "license to kill"), detected in Dec. 1999. We have now seen 3 UDP type "00" probes, and had another "00" probe reported from Kansas. These probes use a single UDP packet, two bytes of data (ascii zeroes) and identical UDP port numbers, 60000->2140. They stimulate the 1500-byte ICMP Echo-Request packet and the normal 58-byte ICMP Destination_Unreachable-Port Packets. The Echo-Request is never answered. 1999-12-20 07:04 195.229.024.212 (Arab Emirates*) to 24.88.48.47 (Atlanta, GA) 1999-12-21 08:04 195.229.024.213 (Arab Emirates*) to 24.88.48.47 (Atlanta, GA) *DNS name: cwa129.emirates.net.ae 1999-12-25 09:39 212.174.198.29 (Turkey) to 24.94.xxx.xxx (Wichita, Kansas) *DNS: none 1999-12-31 05:35 195.99.56.179 (Manchester, UK*) to 14.88.xx.xx (Atlanta, GA) *DNS name: manchester_nas11.ida.bt.net 2000-01-04 05:08 24.94.80.152 (Road Runner, Hawaii) to 24.94.xxx.xxx (Wichita, Kansas) *DNS name: a24b94n80client152.hawaii.rr.com 2000-01-06 04:48 195.44.201.41 (cwnet, NJ) to 24.88.xx.xxx (Atlanta, GA) *DNS name: ad11-s16-201-41.cwci.net Network Threat Management 22 2nd Generation, “Mac Attack” Scanning Drawing from Atlanta JournalConstitution article, Dec. 1999. Full details at www.csc,gatech. edu /macattack/ Network Threat Management Web - www.Lancope.com Sales - 678 566-4751 Network Threat Management