Network Laboratory
advertisement

Laboratory Manual
Network Laboratory
Third Year - Information Technology
Teaching Scheme
Examination Scheme
Theory : - Hrs/Week
Term Work: 25 Marks
Practical : 02 Hrs/Week
Practical : - Marks
Oral : 50 Marks
Prepared By
Prof. Shridevi A. Swami
Department of Information Technology
Vidya Pratishthan’s College of Engineering
Baramati – 413133, Dist- Pune (M.S.)
INDIA
June 2013
Table of Contents
1 TCP/IP Utilities and Commands
1.1 Problem Statement . . . . . . . .
1.2 Pre Lab . . . . . . . . . . . . . .
1.3 Theory . . . . . . . . . . . . . . .
1.3.1 PING . . . . . . . . . . .
1.3.2 ARP . . . . . . . . . . . .
1.3.3 TRACEROUTE . . . . .
1.3.4 IFCONFIG . . . . . . . .
1.3.5 IPCONFIG . . . . . . . .
1.3.6 NETSTAT -NR . . . . . .
1.3.7 NETSTAT -I . . . . . . .
1.3.8 NETSTAT -AT . . . . . .
1.3.9 TCPDUMP . . . . . . . .
1.4 Conclusion . . . . . . . . . . . .
1.5 Post Lab . . . . . . . . . . . . . .
1.6 Viva Questions . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
2
2
2
2
3
3
4
4
5
5
6
7
7
7
7
8
2 Router Configuration
2.1 Problem Statement . . . . . . . . . . .
2.2 Pre Lab . . . . . . . . . . . . . . . . .
2.3 Theory . . . . . . . . . . . . . . . . . .
2.3.1 Boson NetSim . . . . . . . . .
2.3.2 Steps Of Router Configuration
2.3.3 Commands . . . . . . . . . . .
2.4 Conclusion . . . . . . . . . . . . . . .
2.5 Post Lab . . . . . . . . . . . . . . . . .
2.6 Viva Questions . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
9
9
9
9
9
9
11
12
12
12
3 Network Design and Implementation
3.1 Problem Statement . . . . . . . . . . . . . .
3.2 Pre Lab . . . . . . . . . . . . . . . . . . . .
3.3 Theory . . . . . . . . . . . . . . . . . . . . .
3.3.1 CAT 5 Cable . . . . . . . . . . . . .
3.3.2 CAT 6 Cable . . . . . . . . . . . . .
3.3.3 RJ (Registered Jacks) 45 Connector
3.3.4 RJ45 pins . . . . . . . . . . . . . . .
3.4 Conclusion . . . . . . . . . . . . . . . . . .
3.5 Post Lab . . . . . . . . . . . . . . . . . . . .
3.6 Viva Questions . . . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
13
13
13
13
13
13
14
15
16
16
16
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
i
TABLE OF CONTENTS
TABLE OF CONTENTS
4 VLAN
4.1 Problem Statement . . . . . . . . . . . .
4.2 Pre Lab . . . . . . . . . . . . . . . . . .
4.3 Theory . . . . . . . . . . . . . . . . . . .
4.3.1 What is a VLAN (Virtual LAN)?
4.3.2 Establishing VLAN Membership
4.3.3 The purpose of VLANs . . . . .
4.3.4 Advantages of using VLANs . . .
4.4 Conclusion . . . . . . . . . . . . . . . .
4.5 Post Lab . . . . . . . . . . . . . . . . . .
4.6 Viva Questions . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
18
18
18
18
18
19
20
22
23
23
23
5 Protocol Analyzer / Packet Sniffer
5.1 Problem Statement . . . . . . . . . . . .
5.2 Pre Lab . . . . . . . . . . . . . . . . . .
5.3 Theory . . . . . . . . . . . . . . . . . . .
5.3.1 What is Wireshark? . . . . . . .
5.3.2 Some intended use of Wireshark
5.3.3 Features . . . . . . . . . . . . . .
5.3.4 Capturing Live Network Data . .
5.3.5 Protocol Packet Header Format .
5.4 Conclusion . . . . . . . . . . . . . . . .
5.5 Post Lab . . . . . . . . . . . . . . . . . .
5.6 Viva Questions . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
24
24
24
24
24
24
25
25
26
28
28
28
6 Network Simulator-2
6.1 Problem Statement . . . . . . . .
6.2 Pre Lab . . . . . . . . . . . . . .
6.3 Theory . . . . . . . . . . . . . . .
6.3.1 Network Simulator . . . .
6.3.2 Nam (Network Animator)
6.3.3 Network Topology . . . .
6.3.4 TCL Script . . . . . . . .
6.4 Conclusion . . . . . . . . . . . .
6.5 Post Lab . . . . . . . . . . . . . .
6.6 Viva Questions . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
29
29
29
29
29
29
30
30
33
33
33
7 Socket Programming
7.1 Problem Statement . . . . . . . . . . . . . . . .
7.2 Pre Lab . . . . . . . . . . . . . . . . . . . . . .
7.3 Theory . . . . . . . . . . . . . . . . . . . . . . .
7.3.1 Socket . . . . . . . . . . . . . . . . . . .
7.3.2 Types of Sockets . . . . . . . . . . . . .
7.3.3 Types of Internet Sockets . . . . . . . .
7.3.4 SCOKET SYSTEM CALLS . . . . . . .
7.3.5 Connectionless Iterative Server . . . . .
7.3.6 Connection-Oriented Concurrent Server
7.4 Conclusion . . . . . . . . . . . . . . . . . . . .
7.5 Post Lab . . . . . . . . . . . . . . . . . . . . . .
7.6 Viva Questions . . . . . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
34
34
34
34
34
34
35
35
39
40
41
41
41
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
ii
TABLE OF CONTENTS
TABLE OF CONTENTS
8 DNS and DHCP Server
8.1 Problem Statement . . . . . . . . . . . . . . . . . . . .
8.2 Pre Lab . . . . . . . . . . . . . . . . . . . . . . . . . .
8.3 Theory . . . . . . . . . . . . . . . . . . . . . . . . . . .
8.3.1 Domain Name System (DNS) . . . . . . . . . .
8.3.2 Resolution . . . . . . . . . . . . . . . . . . . . .
8.3.3 Types of Resolution . . . . . . . . . . . . . . .
8.3.4 Dynamic Host Configuration Protocol (DHCP)
8.3.5 DHCP State Transition Diagram . . . . . . . .
8.4 Conclusion . . . . . . . . . . . . . . . . . . . . . . . .
8.5 Post Lab . . . . . . . . . . . . . . . . . . . . . . . . . .
8.6 Viva Questions . . . . . . . . . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
42
42
42
42
42
43
43
44
46
46
46
46
9 Internet Information Server
9.1 Problem Statement . . . . .
9.2 Pre Lab . . . . . . . . . . .
9.3 Theory . . . . . . . . . . . .
9.3.1 Introduction . . . .
9.3.2 Use of IIS . . . . . .
9.4 Conclusion . . . . . . . . .
9.5 Post Lab . . . . . . . . . . .
9.6 Viva Questions . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
47
47
47
47
47
48
48
48
48
10 Existing College Network
10.1 Problem Statement . . . . . . . . . . . . . . . .
10.2 Pre Lab . . . . . . . . . . . . . . . . . . . . . .
10.3 Theory . . . . . . . . . . . . . . . . . . . . . . .
10.3.1 Networking Components . . . . . . . . .
10.3.2 Cables . . . . . . . . . . . . . . . . . . .
10.3.3 What is Networking Hardware? . . . . .
10.3.4 Hub . . . . . . . . . . . . . . . . . . . .
10.3.5 Switches . . . . . . . . . . . . . . . . . .
10.3.6 Repeaters . . . . . . . . . . . . . . . . .
10.3.7 Bridge . . . . . . . . . . . . . . . . . . .
10.3.8 Router . . . . . . . . . . . . . . . . . . .
10.3.9 IP Classful Addressing Scheme . . . . .
10.3.10 VPCOE Campus Network . . . . . . . .
10.3.11 VPCOE Campus Network Specification
10.4 Conclusion . . . . . . . . . . . . . . . . . . . .
10.5 Post Lab . . . . . . . . . . . . . . . . . . . . . .
10.6 Viva Questions . . . . . . . . . . . . . . . . . .
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
49
49
49
49
49
50
52
53
54
54
55
55
56
58
58
58
59
59
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
References
.
.
.
.
.
.
.
.
60
iii
TABLE OF CONTENTS
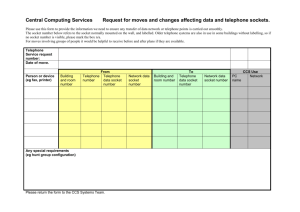
Lab Manual - Network Laboratory
1
VPCOE, Baramati
Assignment 1
TCP/IP Utilities and Commands
1.1
Problem Statement
Study of TCP/IP Utilities and Commands.
1.2
Pre Lab
• Concept of network protocols.
• Concept of troubleshooting.
1.3
Theory
• TCP/IP Commands on LINUX
– Ping
– Ifconfig
– Traceroute
– ARP
– Netstat
• TCP/IP Commands on WINDOWS
– Ping
– Ipconfig
– Tracert
– Route Print
2
TCP/IP Utilities and Commands
1.3.1
PING
”Ping” (Packet INternet Groper) is the best-known network administration tool whose task is to send
packets to check if a remote machine is responding and if it is accessible over the network.
The ping tool is used to diagnose network connectivity using command of the syntax:
ping
name.of.the.machine
name.of.the.machine represents the machine’s IP address, or its name.
How ping works?
Ping relies on the Internet Control Message Protocol (ICMP) protocol, which is used to diagnose
transmission conditions. It uses two types of ICMP protocol messages:
• Type 0, which corresponds to an ”echo request” command, sent by the source machine
• Type 8, which corresponds to an ”echo reply” command, sent by the target machine
So Ping operates by sending ICMP echo request packets to the target host and waiting for an ICMP
response. At regular intervals (by default, every second), the source machine (the one running the ping
command) sends an ”echo request” to the target machine. When the ”echo reply” packet is received,
the source machine displays a line containing certain information. If the reply is not received, a line
saying ”Destination unreachable” or ”request timed out” will be shown.
Ping results
The ping command’s output gives:
• The IP address which corresponds to the name of the remote machine.
• The ICMP Request sequence number.
• The packet’s Time To Live (TTL). The Time To Live (TTL) field shows how many routers the
packet went through as it traveled between the two machines. Each IP packet has a TTL field
with a relatively high value. Each time it goes through a router, the value is reduced. If this
number ever reaches zero, the router interprets this to mean that the packet is going around in
circles, and terminates it.
• The round-trip delay field corresponds to the length of time in milliseconds of a round trip between
the source and target machines. As a general rule, a packet must have a delay no longer than 200
ms.
1.3.2
ARP
On some occasions, it is useful to view or alter the contents of the kernel’s ARP tables, for example
when you suspect a duplicate Internet address is the cause for some intermittent network problem.
Lab Manual - Network Laboratory
3
VPCOE, Baramati
TCP/IP Utilities and Commands
ARP command Displays and modifies the IP-to-Physical address translation tables used by address
resolution protocol(ARP).
For ARP command-line options are:
• arp [-v] [-t hwtype] -a [hostname]
• arp [-v] [-t hwtype] -s hostname hwaddr
• arp [-v] -d hostname [hostname]
All hostname arguments may be either symbolic hostnames or IP addresses in dotted quad notation.
The first invocation displays the ARP entry for the IP address or host specified, or all hosts known if
no hostname is given.
1.3.3
TRACEROUTE
Traceroute is a network diagnostic tool found on most operating systems, which is used for determining
which path a packet has taken. The traceroute command can be used to draw up a map of the routers
found between a source machine and a target machine. Tracert is equivalent command on windows.
The traceroute command is used to discover the routes that packets actually take when traveling to
their destination. The device (for example, a router or a PC) sends out a sequence of User Datagram
Protocol (UDP) datagrams to an invalid port address at the remote host.Three datagrams are sent,
each with a Time-To-Live (TTL) field value set to one. The TTL value of 1 causes the datagram to
”timeout” as soon as it hits the first router in the path; this router then responds with an ICMP Time
Exceeded Message (TEM) indicating that the datagram has expired.Another three UDP messages are
now sent, each with the TTL value set to 2, which causes the second router to return ICMP TEMs.
This process continues until the packets actually reach the other destination. Since these datagrams are
trying to access an invalid port at the destination host, ICMP Port Unreachable Messages are returned,
indicating an unreachable port; this event signals the Traceroute program that it is finished.
Output of a traceroute:A traceroute’s output describes the IP addresses of the chain of routers, each preceded by sequential
number and minimum, average, and maximum response time.
1.3.4
IFCONFIG
The ”ifconfig” command allows the operating system to setup network interfaces and allow the user to
view information about the configured network interfaces.
Ifconfig is used at boot time to set up interfaces as necessary. After that, it is usually only needed when
Lab Manual - Network Laboratory
4
VPCOE, Baramati
TCP/IP Utilities and Commands
debugging or when system tuning is needed.
If no arguments are given, ifconfig displays the status of the currently active interfaces.
Options:interface
up
down
metric N
MTU N
hw class address
broadcast
multicast
address
txqueuelen
1.3.5
The name of the interface. Usually a driver name followed
by a unit number, eth0 = 1st Ethernet interface.
This flag causes the interface to be activated.
This flag causes the driver for this interface to be shut down.
Set the interface metric.
Set the Maximum Transfer Unit (MTU) of an interface.
Set the hardware address of this interface, if the device
driver supports this operation.
Set the broadcast flag on the interface.
Set the multicast flag on the interface.
The IP address to be assigned to this interface.
Set the length of the transmit queue of the device.
IPCONFIG
Ipconfig (internet protocol configuration) in Microsoft Windows is a console application that displays
all current TCP/IP network configuration values.
Ipconfig displays only the IP address, subnet mask, and default gateway values for each adapter.
1.3.6
NETSTAT -NR
Each Linux / UNIX / Windows or any computer that uses TCP/IP need to make routing decision.
Routing table is used to control these decisions. To display routing table netstat -nr command is used
at UNIX / Linux shell prompt. This is equivalent to the route print command under Windows.
The output of the kernel routing table is organized in the following columns:
• Destination: The destination network or destination host.
• Gateway: The gateway address or ’*’ if none set.
• Genmask: The netmask for the destination net; 255.255.255.255 for a host destination and 0.0.0.0
for the default route.
• Flags : Possible flags include
– U (route is up)
– H (target is a host)
– G (use gateway)
Lab Manual - Network Laboratory
5
VPCOE, Baramati
TCP/IP Utilities and Commands
– R (reinstate route for dynamic routing)
– D (dynamically installed by daemon or redirect)
– M (modified from routing daemon or redirect)
– A (installed by addrconf)
– C (cache entry)
– ! (reject route)
• Metric: The distance to the target (usually counted in hops). It is not used by recent kernels, but
may be needed by routing daemons.
• Iface: Interface to which packets for this route will be sent.
• MSS: Default maximum segment size for TCP connections over this route.
• Window: Default window size for TCP connections over this route.
• Irtt: Initial RTT (Round Trip Time). The kernel uses this to guess about the best TCP protocol
parameters without waiting on (possibly slow) answers.
1.3.7
NETSTAT -I
It displays statistics for the network interfaces currently configured. The MTU and Met fields show
the current MTU and metric values for that interface. The RX and TX columns show how many
packets have been received or transmitted error-free (RX-OK/TX-OK) or damaged (RX-ERR/TXERR); how many were dropped (RX-DRP/TX-DRP); and how many were lost because of an overrun
(RX-OVR/TX-OVR). The last column shows the flags that have been set for this interface. These
characters are one-character versions of the long flag names that are printed when you display the
interface configuration with ifconfig:
• B - A broadcast address has been set.
• L-This interface is a loopback device.
• M-All packets are received (promiscuous mode).
• O-ARP is turned off for this interface.
• P-This is a point-to-point connection.
• R-Interface is running.
• U-Interface is up.
Lab Manual - Network Laboratory
6
VPCOE, Baramati
TCP/IP Utilities and Commands
1.3.8
NETSTAT -AT
Netstat provides statistics for the following:
• Proto - The name of the protocol (TCP or UDP).
• Local Address - The IP address of the local computer and the port number being used. The name
of the local computer that corresponds to the IP address and the name of the port is shown unless
the -n parameter is specified. If the port is not yet established, the port number is shown as an
asterisk (*).
• Foreign Address - The IP address and port number of the remote computer to which the socket is
connected. The names that corresponds to the IP address and the port are shown unless the -n
parameter is specified. If the port is not yet established, the port number is shown as an asterisk
(*).
• State - Indicates the state of a TCP connection. The possible states are as follows: CLOSE WAIT,
CLOSED, ESTABLISHED, FIN WAIT 1, FIN WAIT 2, LAST ACK, LISTEN, SYN RECEIVED,
SYN SEND, and TIME WAIT.
1.3.9
TCPDUMP
Tcpdump is a common packet analyzer that runs under the command line. It allows the user to intercept and display TCP/IP and other packets being transmitted or received over a network to which the
computer is attached.
Tcpdump works on Linux where, tcpdump uses the libpcap library to capture packets. The port of
tcpdump for Windows is called WinDump; it uses WinPcap, the Windows port of libpcap.
Example:
To print traffic between 172.16.0.110 and 172.16.237.23 the command will be:
tcpdump
1.4
host 172.16.0.110
and
172.16.237.23
Conclusion
Thus we have studied and learnt how to use TCP/IP commands for troubleshooting network problems.
1.5
Post Lab
Following objectives are met
Lab Manual - Network Laboratory
7
VPCOE, Baramati
TCP/IP Utilities and Commands
• Learn to use TCP/IP commands for troubleshooting network problems.
1.6
Viva Questions
1. List the Linux based commands.
2. List the Windows based commands.
3. What is the use of ping command?
Lab Manual - Network Laboratory
8
VPCOE, Baramati
Assignment 2
Router Configuration
2.1
Problem Statement
Configure a router (Ethernet and Serial Interface) using router commands on any network simulator.
2.2
Pre Lab
• Concept of RIP network protocol.
2.3
2.3.1
Theory
Boson NetSim
The Boson NetSim Network Simulator is an application that simulates Cisco Systems networking hardware and software and is designed to aid the user in learning the Cisco IOS command structure.
This simulator works in following modes
1. User Mode
2. Configuration Mode
3. Privileged Mode
2.3.2
Steps Of Router Configuration
You want to test your network so building a Lab Network. Host A (on the left) should be setup with
an IP address of 192.168.101.2/24 and default gateway of 192.168.101.1. Host B (on the right) should
be setup with an IP address 192.168.100.2/24 and a default gateway of 192.168.100.1. The Ethernet
9
Router Configuration
Interface of router1 (on the left) should use an IP address 192.168.101.1/24 and serial interface of
Router1 should use an IP address of 192.168.1.1/24. The Ethernet interface of Router2 (on the right)
should use an IP address 192.168.100.1/24 and Serial Interface of Router2 (on the right) should use an
IP address 192.168.1.1/24. You have a DCE cable connected to Router1. The serial link should have
speed of 64K. Configure the routers with RIP so that all devices can ping any other device.
Configuring Router R1:R1:
Hostname R1
interface ethernet0
ip address 192.168.101.1 255.255.255.0
no shut
interface serial0
ip address 192.168.1.1 255.255.255.0
clock rate 64000
no shut
router rip
network 192.168.101.0
network 192.168.1.0
Configuring Router R2:R2:
Hostname R2
interface ethernet0
ip address 192.168.100.1 255.255.255.0
no shut
Lab Manual - Network Laboratory
10
VPCOE, Baramati
Router Configuration
interface serial0
ip address 192.168.1.2 255.255.255.0
no shut
router rip
network 192.168.100.0
network 192.168.1.0
Configuring Host A:Host A:
Ipconfig /IP 192.168.101.2 255.255.255.0
Ipconfig /DG 192.168.101.1
Configuring Host B:Host B:
Ipconfig /IP 192.168.100.2 255.255.255.0
Ipconfig /DG 192.168.100.1
2.3.3
Commands
1
2
3
4
5
6
7
En
conf t
hostname <hostname>
no shut
router rip
clock rate 64000
show interface
8
9
show ip route
debug ip rip
10
no debug all
To enter privileged mode
To enter configuration mode
Configure host name
Enable an interface
Enters into the RIP routing protocol configuration mode.
Set the clock rate for a router with a DCE cable to 64K
To view interfaces, status, and statistics for an interface. If u
doesn’t list a specific interface, all of the interfaces on the router
are listed.
Used to show the router’s routing table.
This command enables RIP debugging messages. The debugging
shows RIP updates that are being sent and received.
Switch all debugging off
Lab Manual - Network Laboratory
11
VPCOE, Baramati
Router Configuration
2.4
Conclusion
Thus we have configured a router with Ethernet and Serial Interface using router commands on Boson
NetSim network simulator.
2.5
Post Lab
Following objectives are met
• Learn to configure router using network simulator.
2.6
Viva Questions
1. Which layer of the OSI model router is associated with?
2. What is a metric?
3. Which is the most widely used routing protocol in internet?
4. What is the difference between RIPv1 and RIPv2?
Lab Manual - Network Laboratory
12
VPCOE, Baramati
Assignment 3
Network Design and Implementation
3.1
Problem Statement
Network design and implementation for small network using actual physical components.
3.2
Pre Lab
• Concept of network devices.
• Concept of network cables.
3.3
3.3.1
Theory
CAT 5 Cable
Cat-5 cable, sometimes called Ethernet cable, is short for Category 5 cable, a current industry standard
for network and telephone wiring. Cat-5 cable is unshielded wire containing four pairs of 24-gauge
twisted copper pairs, terminating in an RJ-45 jack. The actual Cat 5 standard describes specific electrical
properties of the wire, but Cat 5 is most widely known as being rated for its Ethernet capability of 100
Mbit/s. Category 5 cable comes with three twists per inch of each twisted pair of 24 gauge copper wires
within the cable. The twisting of the cable helps to decrease electrical interference and crosstalk.
3.3.2
CAT 6 Cable
CAT6 is an Ethernet cable standard defined by the Electronic Industries Association and Telecommunications Industry Association (commonly known as EIA/TIA). CAT6 cable contains four pairs of copper
wire like the previous generation CAT5. Unlike CAT5, however, CAT6 fully utilizes all four pairs. CAT6
13
Network Design and Implementation
Figure 3.1: CAT 6
supports Gigabit Ethernet speed up to 1 gigabit per second (Gbps) and supports communications at
more than twice the speed of CAT5e, the other popular standard for Gigabit Ethernet cabling. An
enhanced version of CAT6 called CAT6a supports up to 10 Gbps speeds. Cat 6 cables are generally
terminated with RJ-45 electrical connectors. The performance of the signal path will be limited to
that of the lowest category if components of the various cable standards are intermixed. The maximum
length of one Cat 6 cable segment is 220 meters; a repeater needs to be installed to send data over
longer distances or data loss may occur. The maximum allowed length of a CAT6 cable is 100 metres
when used for 10/100/1000baseT and 37 metres when used for 10GbaseT. This applies for UTP cables
only. Shielded (FTP) CAT6 cables are capable of 10GbaseT up to 100m.
3.3.3
RJ (Registered Jacks) 45 Connector
RJ45 is a standard type of connector for network cables. RJ45 connectors are most commonly seen with
Ethernet cables and networks.RJ45 connectors feature eight pins to which the wire strands of a cable
interface electrically. Standard RJ-45 pinouts define the arrangement of the individual wires needed
when attaching connectors to a cable.
Industry standard RJ-type jacks for receiving mating modular plugs have become extremely common
and are found in virtually every telecommunications and data communications system worldwide. The
RJ-series connector, such as the RJ-11 and RJ-45 connectors, represents such a standard connector.
The standard RJ-series modular connector includes a plug or contact block and a jack or socket having
a certain number of mating contacts. The plug includes a small block shaped body typically having
pressure activated blades which can be crimped on to a cable. RJ-45 connectors were originally developed
to terminate flat telephone cable and are very well suited to that application.
An RJ-45 cable is typically available having an RJ-45 connector attached to each end. A modular
jack assembly, known as an RJ-45 connector assembly or an RJ-11 connector assembly, comprises a
plug connector and a mating receptacle connector. An RJ-45 connector assembly used for a network
communication has dimensions larger than those of an RJ-11 connector assembly which is used for a
Lab Manual - Network Laboratory
14
VPCOE, Baramati
Network Design and Implementation
telephone. The RJ-45 connector has a larger width dimension than the RJ-11 and is configured to
facilitate eight connections. The RJ-11 is configured for four connections but has a form factor to
accommodate six. RJ-45 sockets are mounted in ports or interfaces in electrical appliances such as
computers to connect signals transported electric wires to the appliance. The socket can be integrated
into a circuit board and can be accessed through a port in the housing or enclosure of associated
equipment or can be molded directly into an enclosure and wired to a circuit board. The interior
surface of the socket includes a receiving notch for accepting the retention clip of the plug so as to
mechanically secure the plug within the socket. Once the retention clip has snapped into place within
the receiving notch through a flexing action of the retention clip away from the body of the plug, the
plug is firmly held in place providing secure mechanical and electrical coupling.
3.3.4
RJ45 pins
Figure 3.2: RJ45 Pin Diagram
There are basically two crimping types.
1. A straight through cable, which is used to connect different devices.
Example - Hub and switch, Router and computer, Hub and computer.
2. A cross over cable, which is used to operate in a peer-to-peer fashion without a hub/switch.
Lab Manual - Network Laboratory
15
VPCOE, Baramati
Network Design and Implementation
Straight Cabling Color Codes (Both Ends are same):
Pin no
1
2
3
4
5
6
7
8
Side 1
White Orange
Orange
White Green
Blue
White Blue
Green
White Brown
Brown
Side 2
White Orange
Orange
White Green
Blue
White Blue
Green
White Brown
Brown
Cross Cabling Color Codes (Both Ends are Opposite):
Pin no
1
2
3
4
5
6
7
8
3.4
Side 1
White Orange
Orange
White Green
Blue
White Blue
Green
White Brown
Brown
Side 2
White Green
Green
White Orange
Blue
White Blue
Orange
White Brown
Brown
Conclusion
Thus with the help of CAT 5/6 cables and RJ 45 Connector we have designed small network to study
cross and straight cabling.
3.5
Post Lab
Following objectives are met
• How to use straight cabling for connecting different devices.
• How to use cross cabling for connecting similar devices.
3.6
Viva Questions
1. Define IP address.
2. Define straight and cross cabling.
Lab Manual - Network Laboratory
16
VPCOE, Baramati
Network Design and Implementation
3. List the different types of topology.
4. Which transmission media used in star topology?
5. Define a protocol?
6. What is subnet mask?
7. Concept of subnetting.
Lab Manual - Network Laboratory
17
VPCOE, Baramati
Assignment 4
VLAN
4.1
Problem Statement
Study of VLAN Implementation.
4.2
Pre Lab
• Concept of LAN.
• Collision and Broadcast Domain.
4.3
Theory
4.3.1
What is a VLAN (Virtual LAN)?
VLAN is a set of workstations within a LAN that can communicate with each other as though they
were on a single, isolated LAN. A VLAN acts like an ordinary LAN, but connected devices don’t have
to be physically connected to the same segment.
In Virtual Local Area Network:• Broadcast packets sent by one of the workstations will reach all the others in the VLAN.
• Broadcasts sent by one of the workstations in the VLAN will not reach any workstations that are
not in the VLAN.
• Broadcasts sent by workstations that are not in the VLAN will never reach workstations that are
in the VLAN.
18
VLAN
• The workstations can all communicate with each other without needing to go through a gateway.
For example, IP connections would be established by ARPing for the destination IP and sending
packets directly to the destination workstation-there would be no need to send packets to the IP
gateway to be forwarded on.
• The workstations can communicate with each other using non-routable protocols.
In computer networking, virtual local area network, virtual LAN or VLAN is a concept of partitioning a physical network, so that distinct broadcast domains are created. This is usually achieved on
switch or router level. Simpler devices only support partitioning on a port level (if at all), so sharing
VLANs across devices requires running dedicated cabling for each VLAN. More sophisticated devices
can mark packets through tagging, so that a single interconnect (trunk) may be used to transport data
for various VLANs.
Grouping hosts with a common set of requirements regardless of their physical location by VLAN can
greatly simplify network design. A VLAN has the same attributes as a physical local area network
(LAN), but it allows for end stations to be grouped together more easily even if not on the same network switch. VLAN membership can be configured through software instead of physically relocating
devices or connections. Most enterprise-level networks today use the concept of virtual LANs (VLAN).
Without VLANs, a switch considers all interfaces on the switch to be in the same broadcast domain.
4.3.2
Establishing VLAN Membership
The two common approaches to assigning VLAN membership are as follows:
• Static VLANs
• Dynamic VLANs
Static VLANs are also referred to as port-based VLANs. Static VLAN assignments are created by
assigning ports to a VLAN. As a device enters the network, the device automatically assumes the VLAN
of the port. If the user changes ports and needs access to the same VLAN, the network administrator
must manually make a port-to-VLAN assignment for the new connection.
Dynamic VLANs are created through the use of software. With a VLAN Management Policy
Server (VMPS), an administrator can assign switch ports to VLANs dynamically based on information
such as the source MAC address of the device connected to the port or the username used to log onto
that device. As a device enters the network, the switch queries a database for the VLAN membership
of the port that device is connected to.
Thus we can say, VLAN divides a LAN into multiple logical LANs with each being a broadcast domain.
Lab Manual - Network Laboratory
19
VPCOE, Baramati
VLAN
Hosts in the same VLAN can communicate with each other like in a LAN. However, hosts from different
VLANs cannot communicate directly. In this way, broadcast packets are confined to a single VLAN, as
illustrated in the following figure.
4.3.3
The purpose of VLANs
The basic reason for splitting a network into VLANs is to reduce congestion on a large LAN. Initially
LANs were very flat-all the workstations were connected to a single piece of coaxial cable, or to sets of
chained hubs. In a flat LAN, every packet that any device puts onto the wire gets sent to every other
device on the LAN. As the number of workstations on the typical LAN grew, they started to become
hopelessly congested; there were just too many collisions, because most of the time when a workstation
tried to send a packet, it would find that the wire was already occupied by a packet sent by some other
device.
There are three solutions for this congestion that were developed:
1. Using routers to segment LANs
2. Using switches to segment LANs
3. Using VLANs to segment LANs
1. Using routers to segment LANs
The early solution to this problem was to segment the network using routers. This would split
the network into a number of smaller LANs. There would be less workstations on each LAN, and
Lab Manual - Network Laboratory
20
VPCOE, Baramati
VLAN
so less congestion. Of course, routable data being sent between LANs would have to be routed,
so the layer 3 addresses would have to be organized so that each LAN had an identifiable set of
addresses that could be routed to-such as an IP subnet. Non-routable protocols would have to be
bridged, which is not quite so congestion-reducing, because bridges forward all broadcasts. But,
at least for unicast packets, a bridge only forwards packets if it knows that the destination address
is not in the originating LAN.
2. Using switches to segment LANs
As switches became more available, there was a move from chained hubs to a set of hubs connected
to a switch. A switch only sends traffic to a given port if the traffic has to go to that port. So,
switches have the effect of reducing congestion at workstations, by stopping the workstations from
seeing all the traffic from the other ports of the switch. A simple switched network, still needs
routers to set the boundaries of where broadcasts are sent (referred to as ”broadcast containment”).
So, the typical LAN was set up as shown in the following figure:
Domain terminology:- The above figure introduces the concept of a LAN segment. This is also
referred to as a collision domain, because when a device is trying to send a packet, it can only
collide with packets sent by other devices on the same segment. Each LAN segment consists of
all the devices attached to a single switch port-the switch stops packets from different ports from
colliding with each other.
The LAN itself is referred to as a broadcast domain, because if any device within the LAN sends
out a broadcast packet, it will be transmitted to all devices in that LAN, but not to devices beyond
the LAN.
3. Using VLANs to segment LANs As LANs became larger, data rates became faster, and users
Lab Manual - Network Laboratory
21
VPCOE, Baramati
VLAN
desired greater flexibility, the routers in a network started to become a bottleneck. This is because:
• Routers typically forward data in software, and so are not as fast as switches
• Splitting up a LAN using routers meant that a LAN typically corresponded to a particular
physical location. This became limiting when many users had laptops, and wanted to be
able to move between buildings, but still have the same network environment wherever they
plugged in.
So, switch vendors started implementing methods for defining ”virtual LANs”-sets of switch ports,
usually distributed across multiple switches, which somehow interacted as though they were in a
single isolated LAN. This way, workstations could be separated off into separate LANs without
being physically divided up by routers.
So, the layout of the LAN has become more like:
So, instead of the LANs corresponding to physical areas divided from each other by routers, there
are virtual LANs distributed across the network. For example, all the devices in the various areas
labeled ”VLAN A” all belong to a single virtual LAN-i.e. a single broadcast domain.
4.3.4
Advantages of using VLANs
1. Performance:Routers that forward data in software become a bottleneck as LAN data rates increase. Doing
away with the routers removes this bottleneck.
2. Formation of virtual workgroups:Because workstations can be moved from one VLAN to another just by changing the configuration
on switches, it is relatively easy to put all the people working together on a particular project all
into a single VLAN. They can then more easily share files and resources with each other.
Lab Manual - Network Laboratory
22
VPCOE, Baramati
VLAN
3. Greater flexibility:If users move their desks, or just move around the place with their laptops, then, if the VLANs
are set up the right way, they can plug their PC in at the new location, and still be within the
same VLAN. This is much harder when a network is physically divided up by routers.
4. Ease of partitioning of resources:If there are servers or other equipment to which the network administrator wishes to limit access,
then they can be put off into their own VLAN. Then users in other VLANs can be given access
selectively.
5. VLANs help to reduce the cost.
4.4
Conclusion
Virtual LAN or ”VLAN” is a logical subdivision of a Layer 2 network that makes a single Layer 2
infrastructure operate as though it were multiple, separate Layer 2 networks. This is accomplished by
adding a numeric tag field to each data packet as it leaves a Layer 2 switch which identifies the VLAN
number to which the packet belongs. Other VLAN-enabled switches honor the VLAN numbering scheme
to segregate the network into logical, virtual networks. Also VLANs address issues such as scalability,
security, and network management.
4.5
Post Lab
Following objectives are met
• Students are able to understand how LAN is different than VLAN.
4.6
Viva Questions
1. What is VLAN?
2. What are the advantages of VLAN over LAN?
Lab Manual - Network Laboratory
23
VPCOE, Baramati
Assignment 5
Protocol Analyzer / Packet Sniffer
5.1
Problem Statement
Network analysis as well as packet header study with the help of any protocol analyzer/ packet sniffer.
5.2
Pre Lab
• Packet Header format of all protocols.
• Concept of connection establishment and release.
5.3
5.3.1
Theory
What is Wireshark?
Wireshark is a network packet analyzer. A network packet analyzer will try to capture network packets
and tries to display that packet data as detailed as possible. We can say that a network packet analyzer
is a measuring device used to examine what’s going on inside a network cable.
Wireshark is perhaps one of the best open source packet analyzers available today.
5.3.2
Some intended use of Wireshark
1. Network administrators use it to troubleshoot network problems
2. Network security engineers use it to examine security problems
3. Developers use it to debug protocol implementations
4. People use it to learn network protocol internals
24
Protocol Analyzer / Packet Sniffer
5.3.3
Features
Wireshark provides following features:
1. Available for UNIX and Windows.
2. Capture live packet data from a network interface.
3. Display packets with very detailed protocol information.
4. Open and Save packet data captured.
5. Import and Export packet data from and to a lot of other capture programs.
6. Filter packets on many criteria.
7. Search for packets on many criteria.
8. Colorize packet display based on filters.
9. Create various statistics.
5.3.4
Capturing Live Network Data
Capturing live network data is one of the major features of Wireshark.
The Wireshark capture engine provides the following features:
1. Capture from different kinds of network hardware (Ethernet, Token Ring, ATM ...).
2. Stop the capture on different triggers like: amount of captured data, captured time, captured
number of packets.
3. Simultaneously show decoded packets while Wireshark keeps on capturing.
4. Filter packets, reducing the amount of data to be captured
5. Capturing into multiple files while doing a long term capture, and in addition the option to form
a ringbuffer of these files, keeping only the last x files, useful for a ”very long term” capture The
capture engine still lacks the following features:
6. Simultaneous capturing from multiple network interfaces (however, you can start multiple instances
of Wireshark and merge capture files later).
7. Stop capturing (or doing some other action), depending on the captured data.
Windows Packet Capture (WinPcap):WinPcap is the Windows version of the libpcap library; it includes a driver to support capturing packets.
Wireshark uses this library to capture live network data on Windows.
Lab Manual - Network Laboratory
25
VPCOE, Baramati
Protocol Analyzer / Packet Sniffer
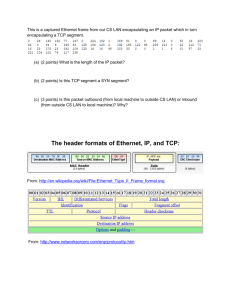
5.3.5
Protocol Packet Header Format
1. ARP
2. RARP
Lab Manual - Network Laboratory
26
VPCOE, Baramati
Protocol Analyzer / Packet Sniffer
3. IPv4
4. TCP
Lab Manual - Network Laboratory
27
VPCOE, Baramati
Protocol Analyzer / Packet Sniffer
5. UDP
5.4
Conclusion
With the help of Wireshark we have performed network analysis as well as packet header study.
5.5
Post Lab
Following objectives are met
• Learn to use wireshark for packet header study.
• Learn to use wireshark for network analysis.
5.6
Viva Questions
• What is wireshark?
• Which library is responsible for capturing the traffic?
• Name the TCP/IP command which is similar to wireshark in functioning.
• Draw and explain the packet header format of any protocol discussed above.
• Can a protocol analyzer be used as a hacking tool?
Lab Manual - Network Laboratory
28
VPCOE, Baramati
Assignment 6
Network Simulator-2
6.1
Problem Statement
Installation of NS-2. Test network animation on Network Simulator2 (NS2).
6.2
Pre Lab
• Concept of Simulation and Animation.
6.3
6.3.1
Theory
Network Simulator
NS or Network Simulator (also popularly called ns-2, in reference to its current generation) is a discrete
event network simulator. NS is popularly used in the simulation of routing and multicast protocols,
and is heavily used in ad-hoc networking research. NS supports an array of popular network protocols,
offering simulation results for wired and wireless networks alike.NS is an object oriented simulator,
written in C++, with an OTcl interpreter as a front end.
6.3.2
Nam (Network Animator)
Nam is a Tcl/TK based animation tool for viewing network simulation traces and real world packet
traces. It supports topology layout, packet level animation, and various data inspection tools.
29
Network Simulator-2
6.3.3
Network Topology
Figure 6.1: Network Topology
6.3.4
TCL Script
This script for NS simulates a simple topology to learn how to set up nodes and links, how to send data
from one node to another, how to monitor a queue and how to start nam from your simulation script
to visualize your simulation.
How to start (Creating a template that can be used by all the programs in NS2)
• Write a ’template’ that can be used for all of the first Tcl scripts. For writing Tcl scripts use any
text editor like available in Linux and save the file in /usr/local/ns-allinone-2.26/bin folder with
.tcl extension.
• Create a simulator object. This is done with the command
set ns [new Simulator]
• Now we open a file for writing that is going to be used for the nam trace data.
set nf [open out.nam w]
$ns namtrace-all $nf
The first line opens the file ’out.nam’ for writing and gives it the file handle ’nf’. In the second
line we tell the simulator object that we created above to write all simulation data that is going
to be relevant for nam into this file.
• The next step is to add a ’finish’ procedure that closes the trace file and starts nam.
Lab Manual - Network Laboratory
30
VPCOE, Baramati
Network Simulator-2
proc finish {}
{
global ns nf
$ns flush-trace
close $nf
exec ./nam out.nam &
exit 0
}
• The next line tells the simulator object to execute the ’finish’ procedure after 5.0 seconds of
simulation time.
$ns at 5.0 ”finish”
You probably understand what this line does just by looking at it. ns provides you with a very
simple way to schedule events with the ’at’ command.
• The last line finally starts the simulation.
$ns run
To create nodes and links
• Syntax to create a node in NS2
set name-of-the-node [$ns node]
A new node object is created with the command ’$ns node’.
e.g. To create two node n0 and n1 use the following code
set n0 [$ns node]
set n1 [$ns node]
The above code creates two nodes and assigns them to the handles ’n0’ and ’n1’.
Insert the code in this section before the line ’$ns run’, or even better, before the line ’$ns at 5.0
”finish”’
• The next line connects the two nodes.
$ns duplex-link $n0 $n1 1Mb 10ms DropTail
This line tells the simulator object to connect the nodes n0 and n1 with a duplex link with the
bandwidth 1Megabit, a delay of 10ms and a DropTail queue.
Sending data between the two nodes
• In ns, data is always being sent from one ’agent’ to another. So the next step is to create an agent
object that sends data from node n0, and another agent object that receives the data on node n1.
Lab Manual - Network Laboratory
31
VPCOE, Baramati
Network Simulator-2
#Create a UDP agent and attach it to node n0
set udp0 [new Agent/UDP]
$ns attach-agent $n0 $udp0
# Create a CBR traffic source and attach it to udp0
set cbr0 [new Application/Traffic/CBR]
$cbr0 set packetSize 500
$cbr0 set interval 0.005
$cbr0 attach-agent $udp0
These lines create a UDP agent and attach it to the node n0, then attach a CBR traffic generate
to the UDP agent. CBR stands for ’constant bit rate’. The packetSize is being set to 500 bytes
and a packet will be sent every 0.005 seconds (i.e. 200 packets per second).
• The next lines create a Null agent which acts as traffic sink and attach it to node n1.
set null0 [new Agent/Null]
$ns attach-agent $n1 $null0
• Now the two agents have to be connected with each other.
$ns connect $udp0 $null0
• And now we have to tell the CBR agent when to send data and when to stop sending.
Note: It’s probably best to put the following lines just before the line ’$ns at 5.0 ”finish”’.
$ns at 0.5 ”$cbr0 start”
$ns at 4.5 ”$cbr0 stop”
• Save the file and start the simulation again. When you click on the ’play’ button in the nam
window, you will see that after 0.5 simulation seconds,node 0 starts sending data packets to node
1.
Lab Manual - Network Laboratory
32
VPCOE, Baramati
Network Simulator-2
6.4
Conclusion
Thus we have studied Installation of NS-2 and Test network animation.
6.5
Post Lab
Following objectives are met
• How to use nam for network animation.
• How to use TCL script for network animation.
6.6
Viva Questions
1. What is NS2?
2. What is tcl script?
3. What is nam?
4. How to create node?
5. What is CBR traffic?
6. What is droptail queue?
7. What is agent and types of agent?
Lab Manual - Network Laboratory
33
VPCOE, Baramati
Assignment 7
Socket Programming
7.1
Problem Statement
Socket Programming in C Language on Linux.
1. TCP Client , TCP Server
2. UDP Client , UDP Server
7.2
Pre Lab
• Concept of socket.
• Concept of TCP and UDP.
• Concept of C on Linux.
7.3
Theory
7.3.1
Socket
Socket is the end point for communication used as interface between an application layer and transport
layer. The application process can send/receive messages to/from another application process (local or
remote)via a socket.
7.3.2
Types of Sockets
1. Internet Socket
2. unix socket
34
Socket Programming
3. X.25 socket
7.3.3
Types of Internet Sockets
1. Stream Sockets (SOCK STREAM)
• Connection oriented
• Rely on TCP to provide reliable two-way connected communication
2. Datagram Sockets (SOCK DGRAM)
• Rely on UDP
• Connection is unreliable
Figure 7.1: Socket Types
7.3.4
SCOKET SYSTEM CALLS
1. socket Function
The socket function is used by a process to create a socket.
Syntax:
int socket ( int famil ,int type, int protocol );
Description:
family: Specifies the protocol family (AF_INET for TCP/IP)
type: Indicates communications semantics
Lab Manual - Network Laboratory
35
VPCOE, Baramati
Socket Programming
SOCK_STREAM stream socket TCP
SOCK_DGRAM datagram socket UDP
SOCK_RAW raw socket protocol: Set to 0 except for raw sockets
Returns on success: Socket descriptor (a small nonnegative integer)
Returns on error: -1
2. connect Function
The connect function is used by a process to establish an active connection to a remote process.
Syntax:
int connect(int sockfd, const struct sockaddr *servaddr, socklen_t addrlen);
Description:
sockfd: Socket descriptor returned by the socket function
*servaddr: Pointer to a socket address structure
addrlen: Size of the socket address structure
The socket address structure must contain the IP address and the port number for the connection.
In TCP, connect initiates a three-way handshake.
Returns on success: 0
Returns on error: -1
3. bind Function
The bind function binds a socket to a local socket address by adding the local socket address to
an already created socket.
Syntax:
int bind(int sockfd, const struct sockaddr myaddr, socklen_t addrlen);
Description:
bind assigns a local protocol address to a socket.
protocol address: 32 bit IPv4 address and a 16 bit TCP or UDP port number.
sockfd: Socket descriptor returned by the socket function.
*myaddr: Pointer to a protocol-specific address.
addrlen: Size of the socket address structure.
Servers bind their well-known port when they start.
Returns on success: 0
Returns on error: -1
Lab Manual - Network Laboratory
36
VPCOE, Baramati
Socket Programming
4. listen Function
Syntax:
Int listen (int sockfd, int backlog);
Description:
Listen is called only by a TCP server and performs two actions:
1. Converts an unconnected socket into a passive socket.
2. Specifies the maximum number of connections that the kernel should queue for this socket.
Listen is normally called before the accept function.
Returns on success: 0
Returns on error: -1
5. accept Function
Syntax:
int accept(int sockfd, struct sockaddr *cliaddr, socklen_t *addrlen);
Description:
Returns on success: Socket descriptor
Returns on error: -1
6. sendto Function
Syntax:
ssize_t sendto(int sockfd, const void *buf, size_t buflen, int flags,
const struct sockaddress *toaddr, socklen_t toaddrlen);
Description:
Returns on success: No of bytes sent
Returns on error: -1
7. recvfrom Function
Syntax:
ssize_t recvfrom(int sockfd, void *buf, size_t buflen, int flags,
struct sockaddress *fromaddr, socklen_t * fromaddrlen);
Lab Manual - Network Laboratory
37
VPCOE, Baramati
Socket Programming
Description:
Returns on success: No of bytes received
Returns on error: -1
8. read Function
Syntax:
ssize_t read(int sockfd, void *buf, size_t buflen);
Description:
Returns on success: No of bytes read
Returns on error: -1
9. write Function
Syntax:
ssize_t write(int sockfd, const void *buf, size_t buflen);
Description:
Returns on success: No of bytes written
Returns on error: -1
10. close Function
Syntax:
int close(int sockfd);
Description:
Returns on success: 0
Returns on error: -1
Lab Manual - Network Laboratory
38
VPCOE, Baramati
Socket Programming
7.3.5
Connectionless Iterative Server
Figure 7.2: Socket interface for connectionless iterative server
Lab Manual - Network Laboratory
39
VPCOE, Baramati
Socket Programming
7.3.6
Connection-Oriented Concurrent Server
Figure 7.3: Socket interface for connection-oriented concurrent server
Lab Manual - Network Laboratory
40
VPCOE, Baramati
Socket Programming
7.4
Conclusion
Thus we have studied socket programming for both UDP and TCP communication.
7.5
Post Lab
Following objectives are met
• Concept of socket as a end point for communication.
• UDP client server communication.
• TCP client server communication.
7.6
Viva Questions
1. What is socket?
2. What are types of socket?
3. Which socket is used for TCP communication?
4. Which socket is used for UDP communication?
5. Write system calls with the syntax.
Lab Manual - Network Laboratory
41
VPCOE, Baramati
Assignment 8
DNS and DHCP Server
8.1
Problem Statement
Installation and configuration of DNS and DHCP server.
8.2
Pre Lab
• Concept of DNS.
• Concept of DHCP.
8.3
8.3.1
Theory
Domain Name System (DNS)
To identify an entity, TCP/IP protocols use the IP address, which uniquely identifies the connection of
a host to the Internet. However, people prefer to use names instead of numeric addresses. Therefore,
we need a system that can map a name to an address or an address to a name.
When the Internet was small, mapping was done using a host file. The host file had only two columns:
name and address. Every host could store the host file on its disk and update it periodically from a
master host file. When a program or a user wanted to map a name to an address, the host consulted
the host file and found the mapping.
Today, however, it is impossible to have one single host file to relate every address with a name and
vice versa. The host file would be too large to store in every host. In addition, it would be impossible
to update all the host files every time there is a change.
One solution would be to store the entire host file in a single computer and allow access to this centralized
42
DNS and DHCP Server
information to every computer that needs mapping. But we know that this would create a huge amount
of traffic on the Internet.
Another solution, the one used today, is to divide this huge amount of information into smaller parts
and store each part on a different computer. In this method, the host that needs mapping can contact
the closest computer holding the needed information. This method is used by the Domain Name System
(DNS).
8.3.2
Resolution
Mapping a name to an address or an address to a name is called name-address resolution.
Resolver:DNS is designed as a client server application. A host that needs to map an address to a name or a
name to an address calls a DNS client called a resolver. The resolver accesses the closest DNS server
with the mapping request. If the server has the information, it satisfies the resolver; otherwise, it either
refers the resolver to other servers or asks other servers to provide the information.
After the resolver receives the mapping, it interprets the response to see if it is a real resolution or an
error, and finally delivers the result to the process that requested it.
8.3.3
Types of Resolution
• Recursive Resolution
The client (resolver) can ask for a recursive answer from a name server. This means that the
resolver expects the server to supply the final answer. If the server is the authority for the domain
name, it checks its database and responds. If the server is not the authority, it sends the request
to another server (the parent usually) and waits for the response. If the parent is the authority, it
responds; otherwise, it sends the query to yet another server. When the query is finally resolved,
the response travels back until it finally reaches the requesting client.
Figure 8.1: Recursive Resolution
Lab Manual - Network Laboratory
43
VPCOE, Baramati
DNS and DHCP Server
• Iterative Resolution
If the client does not ask for a recursive answer, the mapping can be done iteratively. If the server
is an authority for the name, it sends the answer. If it is not, it returns (to the client) the IP
address of the server that it thinks can resolve the query. The client is responsible for repeating
the query to this second server. If the newly addressed server can resolve the problem, it answers
the query with the IP address; otherwise, it returns the IP address of a new server to the client.
Now the client must repeat the query to the third server. This process is called iterative because
the client repeats the same query to multiple servers.
Figure 8.2: Iterative Resolution
8.3.4
Dynamic Host Configuration Protocol (DHCP)
Bootstrap Protocol (BOOTP) is not a dynamic configuration protocol. It is a client server protocol
designed to overcome the two deficiencies of the RARP protocol.
First, since it is a client server program, the BOOTP server can be anywhere in the Internet.
Second, it can provide IP address, subnet mask of computer,IP address of router,IP address of name
server.
To provide the four pieces of information described above, it removes all restriction about the RARP
protocol. BOOTP, however, is a static configuration protocol. When a client requests its IP address,
the BOOTP server consults a table that matches the physical address of the client with its IP address.
This implies that the binding between the physical address and the IP address of the client already
exists. The binding is predetermined.
But there are some situations in which we need a dynamic con?guration protocol. For example, when
a host moves from one physical network to another, its physical address changes. As another example,
there are occasions when a host wants a temporary IP address to be used for a period of time. BOOTP
cannot handle these situations because the binding between the physical and IP addresses is static and
Lab Manual - Network Laboratory
44
VPCOE, Baramati
DNS and DHCP Server
fixed in a table until changed by the administrator.
The Dynamic Host Configuration Protocol (DHCP) has been devised to provide static and dynamic
address allocation that can be manual or automatic.
• Static Address Allocation
In this capacity, a DHCP server has a database that statically binds physical addresses to IP
addresses.
• Dynamic Address Allocation
DHCP has a second database with a pool of available IP addresses. This second database makes
DHCP dynamic. When a DHCP client requests a temporary IP address, the DHCP server goes
to the pool of available (unused) IP addresses and assigns an IP address for a negotiable period
of time.
When a DHCP client sends a request to a DHCP server, the server ?rst checks its static database.
If an entry with the requested physical address exists in the static database, the permanent IP
address of the client is returned. On the other hand, if the entry does not exist in the static
database, the server selects an IP address from the available pool, assigns the address to the
client, and adds the entry to the dynamic database.
The dynamic aspect of DHCP is needed when a host moves from network to network or is connected
and disconnected from a network (for example, a subscriber to a service provider). DHCP provides
temporary IP addresses for a limited period of time. The addresses assigned from the pool are
temporary addresses. The DHCP server issues a lease for a speci?c period of time. When the
lease expires, the client must either stop using the IP address or renew the lease. The server has
the choice to agree or disagree with the renewal. If the server disagrees, the client stops using the
address.
Lab Manual - Network Laboratory
45
VPCOE, Baramati
DNS and DHCP Server
8.3.5
DHCP State Transition Diagram
Figure 8.3: DHCP Transition Diagram
8.4
Conclusion
We have installed and configured the DNS and DHCP server on windows server2003 and demonstrated
the working of DNS and DHCP.
8.5
Post Lab
Following objectives are met
• How to install DNS and DHCP.
• How to use DHCP for configuring the host dynamically.
8.6
Viva Questions
1. What is DNS
2. What is DHCP?
3. How DHCP configures the host dynamically?
Lab Manual - Network Laboratory
46
VPCOE, Baramati
Assignment 9
Internet Information Server
9.1
Problem Statement
Installation and configuration of IIS.
9.2
Pre Lab
• Concept of web site.
• Introduction to HTML.
9.3
9.3.1
Theory
Introduction
Internet Information Services (IIS) formerly called Internet Information Server is a web server software
application and set of feature extension modules created by Microsoft for use with Microsoft Windows.
IIS 7.5 supports HTTP, HTTPS, FTP, FTPS, SMTP and NNTP. It is an integral part of the Windows
Server family of products , as well as certain editions of Windows XP, Windows Vista and Windows 7.
IIS is not turned on by default when Windows is installed. The IIS Manager is accessed through the
Microsoft Management Console or Administrative Tools in the Control Panel. All versions of IIS prior
to 7.0 running on client operating systems supported only 10 simultaneous connections and a single web
site.
47
Internet Information Server
9.3.2
Use of IIS
Internet Information Services is used to make your computer a web server. If we want to have a web
server for developing dynamic website or want to publish website on our own server then we install the
IIS. IIS is used on windows plate form. For other plate form we have different web servers.
Internet Information Server (IIS) is a place where you can put your web application or Website and can
access it with intranet or with the help of internet.
9.4
Conclusion
Thus we have studied how to install IIS and configure it for creating web application which can be
accessed on local as well as remote machine.
9.5
Post Lab
Following objectives are met
• Become familiar with IIS.
• Know how to create web application.
9.6
Viva Questions
1. What is IIS?
2. What is virtual directory?
3. What is web server?
Lab Manual - Network Laboratory
48
VPCOE, Baramati
Assignment 10
Existing College Network
10.1
Problem Statement
Case Study of existing College network with IP Address Scheme.
10.2
Pre Lab
• Concept of network cable.
• Concept of network hardware.
• Concept of IP address.
10.3
Theory
10.3.1
Networking Components
1. Cables
2. Hubs
3. Repeaters
4. Bridges
5. Switches
6. Routers
49
Existing College Network
10.3.2
Cables
What is Network Cabling?
Cable is the medium through which information usually moves from one network device to another.
There are several types of cable which are commonly used with LANs. The type of cable chosen for a
network is related to the network’s topology, protocol, and size.
The types of cables used in networks:• Unshielded Twisted Pair (UTP) Cable
• Shielded Twisted Pair (STP) Cable
• Coaxial Cable
• Fiber Optic Cable
Unshielded Twisted Pair (UTP) Cable:Twisted pair cabling comes in two varieties i.e. shielded and unshielded. Unshielded twisted pair
(UTP) is the most popular and is generally the best option for school networks. The quality of UTP
Figure 10.1: UTP Cable
may vary from telephone-grade wire to extremely high-speed cable. The cable has four pairs of wires
inside the jacket. Each pair is twisted with a different number of twists per inch to help eliminate
interference from adjacent pairs and other electrical devices. The tighter the twisting, the higher the
supported transmission rate and the greater the cost per foot. The EIA/TIA (Electronic Industry
Association/Telecommunication Industry Association) has established standards of UTP and rated six
categories of wire.
Unshielded Twisted Pair Connector:The standard connector for unshielded twisted pair cabling is an RJ-45 connector. This is a plastic
connector that looks like a large telephone-style connector. A slot allows the RJ-45 to be inserted only
one way. RJ stands for Registered Jack, implying that the connector follows a standard borrowed from
the telephone industry. This standard designates which wire goes with each pin inside the connector.
Lab Manual - Network Laboratory
50
VPCOE, Baramati
Existing College Network
Figure 10.2: RJ-45 connector
Shielded Twisted Pair (STP) Cable:Although UTP cable is the least expensive cable, it may be susceptible to radio and electrical frequency
interference. Shielded cables help to extend the maximum distance of the cables.
Shielded twisted pair cable is available in three different configurations:• Each pair of wires is individually shielded with foil.
• There is a foil or braid shield inside the jacket covering all wires (as a group).
• There is a shield around each individual pair, as well as around the entire group of wires referred
to as double shield twisted pair.
Coaxial Cable:Coaxial cabling has a single copper conductor at its center. A plastic layer provides insulation between
the center conductor and a braided metal shield. The metal shield helps to block any outside interference.
Although coaxial cabling is difficult to install, it is highly resistant to signal interference. In addition,
it can support greater cable lengths between network devices than twisted pair cable.
The two types of coaxial cables are used i.e. Thin coaxial cable and Thick coaxial cable.
Thin coaxial cable is also referred to as thinnet. 10Base2 refers to the specifications for thin coaxial
cable carrying Ethernet signals. The 2 refers to the approximate maximum segment length being 200
meters. In actual fact the maximum segment length is 185 meters.
Thick coaxial cable is also referred to as thicknet. 10Base5 refers to the specifications for thick coaxial
cable carrying Ethernet signals. The 5 refers to the maximum segment length being 500 meters. Thick
coaxial cable has an extra protective plastic cover that helps keep moisture away from the center conductor. This makes thick coaxial a great choice when running longer lengths in a linear bus network.
Lab Manual - Network Laboratory
51
VPCOE, Baramati
Existing College Network
Figure 10.3: Coaxial Cable
Fiber Optic Cable:Fiber optic cabling consists of a center glass core surrounded by several layers of protective materials.
It transmits light rather than electronic signals eliminating the problem of electrical interference. This
makes it ideal for certain environments that contain a large amount of electrical interference.
Fiber optic cable has the ability to transmit signals over much longer distances than coaxial and twisted
pair. It also has the capability to carry information at vastly greater speeds. This capacity broadens
communication possibilities to include services such as video conferencing and interactive services.
There are two common types of fiber cables i.e. single mode and multimode. Multimode cable has a
larger diameter; however, both cables provide high bandwidth at high speeds. Single mode can provide
more distance, but it is more expensive.
Figure 10.4: Fiber Optic Cable
10.3.3
What is Networking Hardware?
Networking hardware includes all computers, peripherals, interface cards and other equipment needed
to perform data-processing and communications within the network.
Figure 10.5: Networking hardware
Lab Manual - Network Laboratory
52
VPCOE, Baramati
Existing College Network
10.3.4
Hub
A hub is a small rectangular box, often made of plastic, which receives its power from an ordinary wall
outlet. A hub joins multiple computers (or other network devices) together to form a single network
segment. On this network segment, all computers can communicate directly with each other. Ethernet
hubs are by far the most common type, but hubs for other types of networks such as USB also exist.
A hub includes a series of ports that each accepts a network cable. Small network hubs contain four or
Figure 10.6: Hub
sometimes five ports, the fifth port being reserved for ”uplink” connections to another hub or similar
device. Larger hubs contain eight, 12, 16, and even 24 ports.
Key Features of Hubs:Hubs classify as Layer 1 devices in the OSI model. At the physical layer, hubs can support little in
the way of sophisticated networking. Hubs do not read any of the data passing through them and are
not aware of their source or destination. Essentially, a hub simply receives incoming packets, possibly
amplifies the electrical signal, and broadcasts these packets out to all devices on the network - including
the one that originally sent the packet.
Three different types of hubs exist:• Passive
• Active
• Intelligent
Passive hubs do not amplify the electrical signal of incoming packets before broadcasting them out to
the network.
Active hubs do perform this amplification, as does a different type of dedicated network device called
a repeater.
Intelligent hubs add extra features to an active hub that are of particular importance to businesses.
An intelligent hub typically is stackable (built in such a way that multiple units can be placed one on
Lab Manual - Network Laboratory
53
VPCOE, Baramati
Existing College Network
top of the other to conserve space). It also typically includes remote management capabilities via SNMP
and virtual LAN (VLAN) support.
10.3.5
Switches
A concentrator is a device that provides a central connection point for cables from workstations, servers,
and peripherals.
In a star topology, twisted-pair wire is run from each workstation to a central
switch/hub. Most switches are active, that is they electrically amplify the signal as it moves from
one device to another. Switches no longer broadcast network packets as hubs did in the past, they
memorize addressing of computers and send the information to the correct location directly.
Switches are:
• Usually configured with 8, 12, or 24 RJ-45 ports
• Often used in a star or tree topology
• Sold with specialized software for port management
• Usually installed in a standardized metal rack that also may store netmodems, bridges, or routers
Figure 10.7: Switch
10.3.6
Repeaters
Since a signal loses strength as it passes along a cable, it is often necessary to boost the signal with a
device called a repeater. The repeater electrically amplifies the signal it receives and rebroadcasts it.
Repeaters can be separate devices or they can be incorporated into a concentrator. They are used when
the total length of your network cable exceeds the standards set for the type of cable being used.
A good example of the use of repeaters would be in a local area network using a star topology with
unshielded twisted-pair cabling. The length limit for unshielded twisted-pair cable is 100 meters. The
most common configuration is for each workstation to be connected by twisted-pair cable to a multi-port
Lab Manual - Network Laboratory
54
VPCOE, Baramati
Existing College Network
active concentrator. The concentrator amplifies all the signals that pass through it allowing for the total
length of cable on the network to exceed the 100 meter limit.
Figure 10.8: Repeater
10.3.7
Bridge
A bridge is a device that allows you to segment a large network into two smaller, more efficient networks.
If you are adding to an older wiring scheme and want the new network to be up-to-date, a bridge can
connect the two.
A bridge monitors the information traffic on both sides of the network so that it can pass packets of
information to the correct location. Most bridges can ”listen” to the network and automatically figure
out the address of each computer on both sides of the bridge. The bridge can inspect each message and,
if necessary, broadcast it on the other side of the network.
The bridge manages the traffic to maintain optimum performance on both sides of the network. You
might say that the bridge is like a traffic cop at a busy intersection during rush hour. It keeps information
flowing on both sides of the network, but it does not allow unnecessary traffic through. Bridges can be
used to connect different types of cabling, or physical topologies. They must, however, be used between
networks with the same protocol.
Figure 10.9: Bridge
10.3.8
Router
A router translates information from one network to another; it is similar to a superintelligent bridge.
Routers select the best path to route a message, based on the destination address and origin. The router
can direct traffic to prevent head-on collisions, and is smart enough to know when to direct traffic along
Lab Manual - Network Laboratory
55
VPCOE, Baramati
Existing College Network
back roads and shortcuts. While bridges know the addresses of all computers on each side of the network,
routers know the addresses of computers, bridges, and other routers on the network. Routers can even
”listen” to the entire network to determine which sections are busiest – they can then redirect data
around those sections until they clear up. If you have a school LAN that you want to connect to the
Internet, you will need to purchase a router. In this case, the router serves as the translator between
the information on your LAN and the Internet. It also determines the best route to send the data over
the Internet.
Routers can:
• Direct signal traffic efficiently
• Route messages between any two protocols
• Route messages between linear bus, star, and star-wired ring topologies
• Route messages across fiber optic, coaxial, and twisted-pair cabling
Figure 10.10: Router
10.3.9
IP Classful Addressing Scheme
The address space of IPv4 is 232 In classful addressing, the address space is divided into five classes: A,
B, C, D, and E.
Identifying class in binary notation
Figure 10.11: Binary Notation
Lab Manual - Network Laboratory
56
VPCOE, Baramati
Existing College Network
Identifying class in decimal notation
Figure 10.12: Decimal Notation
Netid and Hostid
Figure 10.13: Netid and Hostid
Lab Manual - Network Laboratory
57
VPCOE, Baramati
Existing College Network
10.3.10
VPCOE Campus Network
Figure 10.14: VPCOE Campus Network Diagram
10.3.11
VPCOE Campus Network Specification
1. Class B IP address scheme
2. Static routing
3. Param server HardDisk size 146 X 2 GB
4. Param server OS Windows server 2003
5. Software server HardDisk size 1 TB
6. Software server OS Windows server 2008
7. WiFi AP range 100m
8. WiFi AP constists of inbuilt 8DB antenna
10.4
Conclusion
Thus we have studied existing college network which uses different kinds of network cables and hardwares
with class B IP address scheme.
Lab Manual - Network Laboratory
58
VPCOE, Baramati
Existing College Network
10.5
Post Lab
Following objectives are met
• Study of network cables and hardware.
• Study of IP address scheme.
10.6
Viva Questions
1. Who is ISP of your college?
2. What is bandwidth of lease line?
3. How many routers are their in your college? Give the IP address?
4. List out different network cables used in campus.
5. List out different network devices used in campus.
Lab Manual - Network Laboratory
59
VPCOE, Baramati
References
[1] Behrouz A. Forouzan, ”TCP-IP protocol suite”, Tata McGraw Hill Edition, 2nd edition, 2003,
ISBN: 978007060004
[2] S. Tanenbaum, ”Computer Networks”, PHI Publication, 4th edition, ISBN:8178087855
60