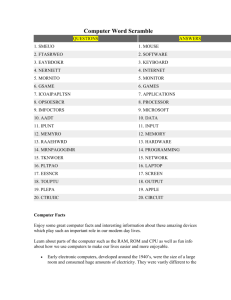
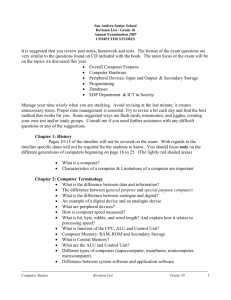
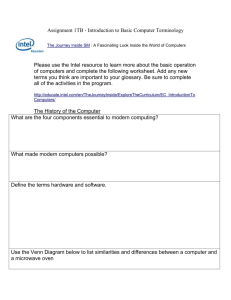
Module 1: Computer Maintenance, Troubleshooting and Repair
advertisement

Computer Lab Manager Training Course Zambia Pacific Trust Module 1: Maintenance, Troubleshooting and Repair Summary This module covers topics relating to keeping computers in good condition, troubleshooting computer problems and performing basic repairs on computers. The online instruction portion of this module includes concepts related to computer parts, software, viruses and basic maintenance. The face-toface training involves hands-on sessions with troubleshooting and repair. If practical, both laptop and desktop computers will be used for these sessions. While these materials were primarily designed for users of Windows operating systems, open source operating systems are also discussed. 1 Module 1: Computer Maintenance, Troubleshooting and Repair Resource Book Author: Heidi Neff, Consultant to Zambia Pacific Trust, heidihneff@gmail.com First Edition – May 2010 More information about Heidi Neff and Zambia Pacific Trust is found at the end of this module. Acknowledgements The Computer Lab Manager Training Course resource books were made possible due to the efforts and encouragement provided by a variety of people around the world. Special thanks are due to two pioneering organizations working on computers in education in Zambia who provided advice and materials: Computers for Zambian Schools and Crescent Future Kids. Three international development aid organizations: Camara, VVOB and IICD, also deserve special recognition for their contributions to this document and the efforts they are making to use ICT as a tool for development and education in Zambia and elsewhere. Many individuals also contributed their time, expertise and advice to the crafting of this module. Key among them are Bornwell Mwewa, Anne Johnson, Nick Lew, Rachel Muchenje, Lumai Mubanga and Annel Silungwe. In addition, none of Zambia Pacific Trust’s work toward improving computer education at schools in Lusaka, Zambia would have been possible without the support, advice and equipment provided by Seattle Academy in Seattle, Washington, USA. The five pictures found in section 5.7.3 are used with permission of FonerBooks.com. Licensing This work is licensed under the Creative Commons Attribution-Noncommercial-Share Alike 3.0 United States License. To view a copy of this license, visit http://creativecommons.org/licenses/by-ncsa/3.0/us/ or send a letter to Creative Commons, 171 Second Street, Suite 300, San Francisco, California, 94105, USA. Zambia Pacific Trust welcomes and encourages organizations to use any of the modules of the Computer Lab Manager Training Course in a manner they deem appropriate, excluding making a profit from the sale or distribution of the material. Organizations are welcome to use portions of these modules in other documents, but they should attribute the material that is used to Zambia Pacific Trust. Zambia Pacific Trust also appreciates knowing who is benefiting from this material, and requests that individuals and organizations please email Bornwell Mwewa (bornwellmwewa@gmail.com), Heidi Neff (heidi.h.neff@gmail.com) and Zambia Pacific Trust (info@zptrust.org) and describe how the material is being used. 2 Module 1 Table of Contents 1. Introduction 1.1. Introduction to the Computer Lab Manager Training Course 1.2. Importance of Practical Learning 1.3. Importance of Self Study 1.4. Introduction to Module 1 1.5. Assignments/Activities 2. Basic Computer Technical Knowledge 2.1. How a Computer Works 2.2. Hardware 2.3. Software 2.4. Assignments/Activities 3. Computer Maintenance 3.1. Why Maintain? 3.2. Updating Software 3.3. Virus and Malware Prevention and Removal 3.4. Computer Hardware Maintenance 3.5. Peripheral Hardware Use and Maintenance 3.6. Assignments/Activities 4. Setting Up or Customizing a Computer 4.1. When a Computer Arrives 4.2. Partitioning a Hard Drive 4.3. Installing Operating Systems 4.4. Installing and Uninstalling Other Software 4.5. Setting Up User Accounts 4.6. Assignments/Activities 5. Computer Troubleshooting and Repair Basics 5.1. Improving Slow Performance 5.2. Stepwise guides for Common Problems 5.3. Understanding Error Messages 5.4. How to Search for Information 5.5. How to Distinguish a Software Issue from a Hardware Issue 5.6. Fixing Software Problems 5.7. Fixing Hardware Problems 5.8. Troubleshooting and Repairing Printers 5.9. Managing E-Waste 5.10. Assignment/Activities 6. Overall Assignments/Activities 7. List of Internet Resources 8. Bibliography 3 Module 1 Text 1. Introduction 1.1. Introduction to the Computer Lab Manager Training Course The Computer Lab Manager Training Course was developed by Zambia Pacific Trust in collaboration with a variety of organizations working on IT related development projects in Zambia. While these projects are in several different sectors (health, education, agriculture and community), all of the organizations recognized the need to increase the number of people who have training in computers past the standard level of a computer user. A particular need that was identified was for individuals who could maintain dynamic and well functioning computer labs and other centers for IT use within a particular project. Therefore, a multifaceted training course was developed to meet these needs including both the “hard skills” of computer maintenance, repair, and networking and the “soft skills” of management, leadership, communication and instruction. Readers may find more emphasis shown on educational projects, since that is the area of Zambia Pacific Trust’s experience. However, most topics discussed apply equally well in the other sectors where IT is used. The resource books for these modules are designed to be used as a part of an instructor-led four module course, with each course including both a distance (online) instruction component and a one week face-to-face workshop. This resource book is written to accompany the first of the four modules listed below. Module 1: Computer Maintenance, Troubleshooting and Repair Module 2: Management and Leadership Module 3: Instruction, Facilitating IT Use and IT in Education Module 4: Networking, Communication and Web 2.0 The target audience for this training course is adult learners who already have intermediate computer user skills and significant experience using computers. Ideally, participants are already employed as computer lab managers, computer project coordinators or Internet café managers. While the course is tailored to those working in educational or community organizations, the course is still valuable for those working in a similar capacity in the private sector. These learning materials are also valuable for people who are not involved in a formal course, but instead are studying independently to become computer lab managers or improve their skills as computer lab managers. Learners who are using these materials for self study are encouraged to make the training as hands-on as possible, performing as many of the assignments and activities as they can practically achieve. 4 1.2. Importance of “Hands-On” Learning Throughout the computer lab manager training course, a strong emphasis is placed on practical learning. Learners will find that theoretical topics are covered quite briefly and more attention is paid to topics that relate to activities that the learners will perform in their computer labs. In the distance learning portion of each module, the majority of the assignments require the learners to think and then act. This includes using a local computer lab (both the computers and the community of people found there) as an opportunity to try out skills, test out ideas and implement improvements. The face-to-face workshops also will emphasize active learning. Learners are asked to participate in discussions and role plays, and are given many opportunities to learn and practice technical skills using the available computers. 1.3. Importance of Self Study Every participant in this course is going to have a different “starting point” of skills and knowledge. Perhaps one participant has strong computer user skills and already has some knowledge of computer hardware maintenance and repair, but has little skill in management and leadership. Another participant may have significant experience in management, but not in an IT setting. In addition, some course participants will have a high level of formal education (such as completion of a university degree) and others will not have had formal training past the level of grade 12. Therefore, it is important for a learner to be self aware of his or her strengths and weaknesses, and to work hard to overcome deficiencies due to lack of previous training or experience. There are some areas where lab managers in Zambia and other developing countries are likely to need more training compared to their counterparts in countries where individuals have had more experience using computers and reading and writing in English. These three areas are listed below: Touch typing – including proper typing posture, home keys, knowing which fingers press which keys, using capital letters and punctuation, typing without looking, and significant speed-building practice English Reading and Writing – including reading comprehension, proper spelling, grammar and punctuation, communicating clearly in writing, and formulating/organizing letters, essays and other documents. Computer User Skills – Including significant skill and practice with use of an operating system, file management, and standard office software (word processing, spreadsheets and presentation software) Learners are encouraged to identify their own strengths and weaknesses in these areas and self study to improve as needed. Participants in the course will be provided with suggested resources to assist their learning (via instructors or the assignments at the end of this chapter). 1.4. Introduction to Module 1: Computer Maintenance, Troubleshooting and Repair Imagine that a community committee plans and implements a new computer lab at a youth resource center. When the lab opens, everyone is proud of their efforts and excited for 5 the future. The computers are new and fast, and everything is working perfectly. When the committee assembles two months later for a meeting at the center, though, it is apparent that there are a few problems. Not only is the room dusty and hot, but there are already some signs of equipment problems. The computers are significantly slower, and one has stopped working altogether. The committee is now discouraged and wonders if all of the effort and funds were well spent. No one likes to see scenarios such as the one described above, but sadly this sort of situation is very common in new computer projects. If the computers are not well maintained, they easily fall prey to problems caused by heat, dust, viruses, misuse and fluctuating electrical supplies. Therefore, a computer lab manager needs to be well trained in ways to maintain computers and then repair them when unavoidable problems do occur. Thus the emphasis of this module is on computer maintenance and basic repairs. Although the theory of how a computer works is not emphasized, the module does begin with the background knowledge that is most helpful for people involved in hands on work in a computer lab. Some time is also spent discussing the initial setup and customization of computers. 1.5. Assignments/Activities 1.5.1. Self Assessment: Touch Typing. Go to the website www.typingtest.com and take a few typing speed tests (using different texts each time). Report your scores to your instructor. 1.5.2. Self Study: Touch Typing. Based on your typing test results and your ability to access the Internet, your instructor will recommend to you a self study strategy for touch typing. If you do not have an instructor, here are a couple of suggestions: 1. Find a free touch typing training program that you can use on your computer (without an Internet connection). One option is the Rapid Typing Tutor, available at www.rapidtyping.com/typing-tutor.html. 2. Find a free online touch typing training program that you can participate in. Some options are the typing courses and tutorials offered at http://alison.com, www.sense-lang.org, www.typeonline.co.uk and www.goodtyping.com. 1.5.3. Assessment: Computer User Skills. Discuss your computer user skills with your instructor, and demonstrate your skills by performing a practical activity that your instructor develops. For example, he or she might ask you to type and format a small document using a word processing program, or enter some information into a spreadsheet and do some simple calculations using that data. If you do not have an instructor, find an IT literate individual in your community who can assess your skills. You can also perform a self assessment by attempting suggested activities in an IT user skills curriculum that is available in your area. You can also download sample test papers for the ICDL/ECDL certification (International/European Computer Driving License) from www.icdl.org. 1.5.4. Self Study: Computer User Skills. Discuss with your instructor to determine the best course of study for you to continue to improve your computer user skills. If you do not have an instructor, find an appropriate IT curriculum that you can work through on your own. Many community computer projects will have access to the Microsoft Unlimited Potential or Microsoft Digital Literacy learning materials. You can also study the Microsoft Digital Literacy course and other IT courses online for free through http://alison.com. 6 1.5.5. Assessment: English Reading and Writing. Discuss your English reading and writing skills with your instructor, and demonstrate your skills by performing practical activities that your instructor develops. For example, he or she might ask you to read and explain a short document or write a professional letter. Alternatively, you can take an online business English test at http://alison.com/courses/Business-English-Test-LT-E. A simpler English test can be taken at www.busuu.com/quiz. The English-Online website (http://www.englishonline.org.uk/course.htm) provides a variety of tests to help users asses their level of English understanding. 1.5.6. Self Study: English Reading and Writing. Discuss with your instructor to determine the best course of study for you to continue to improve your English reading and writing skills. If you do not have an instructor, there are some free online options to help you improve your English including basic online courses and tutorials through www.busuu.com and www.gcflearnfree.org. Some intermediate level courses are available online through http://alison.com. Some more advanced quizzes and activities (but not full courses) are available through www.bbc.co.uk/worldservice/learningenglish/, http://a4esl.org, www.usingenglish.com, www.englishlearner.com and www.englishcafe.com. The last site also provides opportunities to practice and learn through conversation. For all English learners, the most important thing to do is practice your skills. Read, write and speak English as frequently as is possible. Table of Contents 2. Basic Computer Technical Knowledge 2.1. How a Computer Works A computer is a fabulous instrument that turns human inputs into electronic information that it then can store or share/distribute through various output devices. A computer performs (if instructed to do so) the steps shown in the diagram below, using information that a user provides (such as a typed sentence): Input Processing Storage Via keyboard, mouse or microphone The information is digitized, becoming a simple code that the computer can store The information is stored as a part of the computer’s memory Output Further Processing Information is shared via monitor, printer, speakers or projector If instructed to do so, the information is edited or enhanced with input from the user 7 All of the equipment (hardware) and the instructions (software) needed to complete the above steps are described in the next section. Amazingly, the information that the user inputs into a computer is processed so that it becomes a simple code made up of only two digits: zero and one! For all its complexity, a computer is only able to handle these two choices. This is because it is based on electrical signals that have only two options (such as either on or off). But computers compensate for this very simple code by using it in huge quantities. A single unit of this zero/one code is called a bit. Grouping 8 bits together makes a unit of information called a byte. Typing a single page of typed text on a computer requires a minimum of about 20 kilobytes (20 KB or 20,000 bytes) of information to be stored. Good quality digital photographs are usually 1 megabyte (1 MB or 1,000,000 bytes) or larger. So a computer is a very “busy” machine indeed! 2.2. Hardware 2.2.1. Basic Hardware Components Hardware is the physical equipment needed for a computer to function properly. The basic hardware parts are briefly described here. Many computer lab managers will already have been exposed to computer hardware through other courses, but those desiring additional information can find it in a variety of texts and online sources. A desktop computer is used in the photos, but all of this equipment is also found (in a more compact arrangement) in a laptop computer. Case. The computer case (also called a tower or housing) is the box that encloses many of the parts shown below. It has attachment points, slots and screws that allow these parts to be fitted onto the case. The case is also sometimes called the CPU, since it houses the CPU (central processing unit or processor), but this designation can lead to confusion. Please see the description of the processor, below. Power Supply. The power supply is used to connect all of the parts of the computer described below to electrical power. It is usually is found at the back of the computer case. Fan. A fan is needed to disperse the significant amount of heat that is generated by the electrically powered parts in a computer. It is important for preventing overheating of the various electronic components. Some computers will also have a heat sink (a piece of fluted metal) located near the processor to absorb heat from the processor. Motherboard. The motherboard is a large electronic board that is used to connect the power supply to various other electronic parts, and to hold these parts in place on the computer. The computer’s memory (RAM, described below) and processor are attached to the motherboard. Also found on the motherboard is the BIOS (Basic Input and Output System) chip that is responsible for some fundamental operations of the computer, such as linking hardware and software. The motherboard also contains a small battery (that looks 8 like a watch battery) and the chips that work with it to store the system time and some other computer settings. Drives. A computer’s drives are the devices used for long term storage of information. The main storage area for a computer is its internal hard drive (also called a hard disk). The computer should also have disk drives for some sort of removable storage media. A floppy disk drive was very common until recent years, and is still found on many older desk top computers. It was replaced by CD-ROM and DVD drives, which have higher storage capacities. The current standard is a DVD-RW drive, which can both read and write information using both CD and DVD disks. The USB ports (described later) on a computer can also be used to connect other storage devices such as flash drives and external hard drives. Power Supply Drives Fan Housing. The processor is underneath on the motherboard. RAM Cards Figure 1 - Inside a Desktop Computer Case 9 Cards. This term is used to describe important tools that allow your computer to connect and communicate with various input and output devices. The term “card” is used because these items are relatively flat in order to fit into the slots provided in the computer case. A computer will probably have a sound card, a video card, a network card and a modem. RAM. RAM is the abbreviation for random access memory. This is the short term memory that is used to store documents while they are being processed. The amount of RAM in a computer is one of the factors that affect the speed of a computer. RAM attaches to the motherboard via some specific slots. It is important to have the right type of RAM for a specific computer, as RAM has changed over the years. Processor. The processor is the main “brain” of a computer system. It performs all of the instructions and calculations that are needed and manages the flow of information through a computer. It is also called the CPU (central processing unit), although this term can also be used to describe a computer case along with all of the hardware found inside it. Another name for the processor is a computer “chip” although this term can refer to other lesser processors (such as the BIOS). Processors are continually evolving and becoming faster and more powerful. The speed of a processor is measured in megahertz (MHz) or gigahertz (GHz). An older computer might have a processor with a speed of 1000 MHz (equivalent to 1 GHz) or lower, but processors with speeds of over 2 GHz are now common. One processor company, Intel, made a popular series of processors called Pentium. Many reconditioned computers contain Pentium II, Pentium III and Pentium 4 processors, with Pentium 4 being the fastest of these. Peripheral hardware. Peripheral hardware is the name for the computer components that are not found within the computer case. This includes input devices such as a mouse, microphone and keyboard, which carry information from the computer user to the processor, and output devices such as a monitor, printer and speakers, which display or transmit information from the computer back to the user. 2.2.2. Computer Ports The peripheral hardware mentioned above must attach to the computer so that it can transmit information from the user to the computer (or vice versa). There are a variety of ports present on a computer for these attachments. These ports have gradually changed over time as computers have changed to become faster and easier to work with. Ports also vary with the type of equipment that connects to the ports. A computer lab manager should become familiar with the most common ports (and their uses), as described below. Serial Port. This port for use with 9 pin connectors is no longer commonly used, but is found on many older computers. It was used for printers, mice, modems and a variety of other digital devices. 10 Parallel Port. This long and slender port is also no longer commonly used, but was the most common way of attaching a printer to a computer until the introduction of USB ports (see below). The most common parallel port has holes for 25 pins, but other models were also manufactured. Serial Port (left) Parallel Port (right) PS/2 Ports VGA. The Video Graphics Array port is found on most computers today and is used to connect video display devices such as monitors and projectors. It has three rows of holes, for a 15 pin connector. PS/2. Until recently, this type of port was commonly used to connect keyboards and mice to computers. Most desktop computers have two of these round ports for six pin connectors, one for the mouse and one for the keyboard. USB Ports VGA Port TRS (mini-jack) Ports Phone/Modem Jacks (top) Ethernet Port (bottom) USB Ports USB. The Universal Serial Bus is now the most common type of port on a computer. Figure 2 - Back of Desktop Computer Showing Ports It was developed in the late 1990s as a way to replace the variety of ports described above. It can be used to connect mice, keyboards, printers, and external storage devices such as DVD-RW drives and flash drives. It has gone through three different models (USB 1.0, USB 2.0 and USB 3.0), with USB 3.0 being the fastest at sending and receiving information. Older USB devices can be used in newer model USB ports. TRS. TRS (tip, ring and sleeve) ports are also known as ports for mini-jacks or audio jacks. They are commonly used to connect audio devices such as headphones and microphones to computers. Ethernet. This port, which looks like a slightly wider version of a port for a phone jack, is used to network computers via category 5 (CAT5) network cable. Although many computers now connect wirelessly, this port is still the standard for wired networked computers. Some computers also have the narrower port for an actual phone jack. These are used for modem connections over telephone lines. 2.3. Software 2.3.1. Software Types and Categories As mentioned in section 2.1, computer software is the term used for the instructions that have been programmed to allow a computer to process information. Software comes in three main categories, described below: 11 Operating Systems. These are the basic software programs that are needed to for a computer to work. They give a computer the basic information needed for it to process and store information. Currently all common operating systems are also graphical user interfaces (GUIs) which means they use graphics to help the user to easily input instructions, and open other programs. The most common operating systems (OS) are the Windows family of operating systems, from Microsoft. A computer lab manager is likely to encounter Windows 2000, Windows XP, Windows Vista and Windows 7 (the most recent Microsoft OS) in a computer lab. Other operating systems are described in the next section. Utility Software. This is a broad category of programs that allow a computer to perform tasks that aren’t a part of the operating system, but are still practical and useful. For example, a utility might instruct a computer on how to copy (burn) information to a CDROM disk, or it might be an anti-virus program (see section 3.3). Productivity Software. This is one term used to describe the type of software used to perform standard office computer tasks. Word processing, presentation, spreadsheet and database software are all common examples of productivity programs. The most common set of productivity programs is Microsoft Office, offered by the Microsoft Corporation. 2.3.2. Proprietary Software vs. Open Source Software The Microsoft operating system and productivity software packages mentioned above are very common and used around the world in business and education. The Apple Corporation also has very popular and successful operating systems used for their Macintosh computers. Despite the success of these software products, they aren’t the best choices for everyone. They are proprietary, which means that their use and modification are restricted. They can be quite costly to buy licenses for, and they are not adaptable to meet local needs. Some users, particularly in developing countries, illegally use unlicensed (also known as pirate) copies of this software. This is legally unwise, and can also keep the user from accessing important software updates. Users who cannot afford proprietary software or prefer software that can be locally modified, can choose to use open source (often called free and open source or FOSS) software. For most of the standard computer uses, an open source software option is available. This includes the Linux family of operating systems (which includes Ubuntu, a common operating system in African countries) and the OpenOffice.org productivity programs. The Source Forge website (www.sourceforge.net) is a good resource for finding and downloading open source programs. While open source software often does not come with professional support available, there are user groups found on the Internet who can offer assistance to puzzled users. This training module does describe how to perform some tasks using the Ubuntu operating system, but does not provide thorough coverage. Further assistance with Ubuntu is available through the website: http://help.ubuntu.com. 12 When first setting up a computer lab, the steering committee for a computer project should discuss the benefits of both proprietary and open source software and make an informed and intentional choice on which way to go. The computer lab manager should then make sure that he or she is aware of all policies related to software choices. It is possible that a computer project will choose to use proprietary software for some purposes and open source software for others. For example, a project might be able to obtain used computers that have a Windows operating system legally installed (such as through a Microsoft Authorized Refurbisher) but these computers do not include other Microsoft programs. In this case the organization might choose to continue to run Windows on its computers, but choose open source options for all utility and productivity software. 2.4. Assignments/Activities Please Note: Throughout this module there are assignments that require a learner to have access to computers and the Internet. Students who are not already working as computer lab managers may find performing these assignments to be difficult. These learners are encouraged to consult with the staff of a local computer project or Internet café to gain access to equipment and the Internet. It is even possible that short term internships could be arranged that would be beneficial to both the learner and the computer project. 2.4.1. Study the exterior of a particular computer. See if you can identify the power supply, the drives, and all of the ports described in this chapter. 2.4.2. Find a broken or disused desktop computer. Figure out how to open up the case. Identify all of the hardware components that have been described in this chapter. 2.4.3. What type of software is used on the computer you use most frequently? Identify the operating system, the productivity software, the Internet browser and the anti-virus software. For each of these also state whether they are proprietary or open source. If you are having trouble finding out information about some of your programs, here are some tips: To find out about your computer’s operating system, right click on the Computer or My Computer icon from your desktop or Start menu. Choose Properties. To find out about a productivity program, open that program and then find a menu that includes the word “About”. To find the About screen in Microsoft Office 2007, click on the Microsoft Office Button, then click on Options Resources About. 2.4.4. How much RAM does the computer you use most frequently have? Also how fast is the processor on this computer? To find this information, right click on the Computer or My Computer icon from your desktop or Start menu. Choose Properties. 2.4.5. Have a discussion with a manager of a local computer lab about computer operating systems. What operating systems are being used in that computer lab and why? What factors went into the decision to choose an operating system? 2.4.6. Workshop Activity: In a group, observe the exterior of computer. How many ports and hardware devices can your group identify? Ask the instructor for assistance with any items that cannot be identified. 13 2.4.7. Workshop Activity: In a group, open up the case of a computer. Identify all of the hardware components that have been described in this chapter. 2.4.8. Workshop Activity: Participate in a group discussion or a debate on the advantages and disadvantages of using open source software. 2.4.9. Workshop Activity: Experiment with an operating system that you are not familiar with. See if you can figure out how to change the background, open and close windows, open and close programs, and perform any other computer tasks that you frequently perform with other operating systems. Table of Contents 3. Computer Maintenance 3.1. Why Maintain? Think of a computer as being like a human body. We are advised to perform certain tasks to keep our body in good shape. These maintenance tasks such as eating well, avoiding some harmful activities and getting exercise keep our body in good condition. If we don’t maintain our bodies, we might end up in the hospital with problems that result from the abuse such as high blood pressure from eating too much salt, obesity from not exercising or lung problems from smoking. Similarly, if we allow our computers to intake harmful materials (such as dust) and programs (such as viruses) and we don’t keep our software in good condition (updated) then the computer may also end up with significant problems that are then harder to deal with. Proper maintenance of a computer, on the other hand, can keep it running smoothly for years and years. Some of the different categories of computer maintenance are described below. 3.2. Updating Software Software programmers gradually develop updates for their software packages as they discover problems with the software and design tools to address or fix these problems. This can be true for any of the types of software described in section 2.3, but is typically most common and important for operating systems. It is important for a computer user to find and install software updates in order to have well performing computers. Updating software can be done in a variety of ways, described below. Automatic Updates. If a computer is on a reasonably fast Internet connection, the easiest way to keep it up to date is to allow the programs to automatically check for updates and download and install them as needed. When setting up a new computer with Microsoft Windows, this is the choice that the software recommends. It does not require any action on the part of the user, and results in a computer system that is current. To turn on automatic updates for a Windows operating system, find the Systems and Maintenance options in the Control Panel. Automatic Alerts for Updates. If a computer is connected to the Internet, but the connection is slow at some times of the day, another option is to have the computer 14 automatically check for updates but not download or install them until the user elects to do so. For Microsoft Windows computers, if this option is selected, an alert appears in the computer’s system tray stating that there are updates waiting, and then the user can wait until the Internet is faster to install these updates. Manual Updating. A computer user can also turn off all automatic update checking and choose to manually check for updates. For a computer that is rarely connected to the Internet, this would be a good option as long as the user remembered to check when connecting to the Internet. Also some programs do not have automatic update options, and can only be updated in this manner. A program usually has a menu item titled “check for updates” that a user can click on when connected to the Internet. Offline Updating. If a computer is in a location that never has access to the Internet, a computer lab manager will need to download updates from a computer that is connected to the Internet and then transfer them (via a disk or flash drive) to the computer in question to be installed. This option is also useful if a computer lab has several computers that all need the same update. Instead of having each computer download the update separately, one computer could download the update and then it could be shared amongst all of the computers. Offline updates for operating systems can easily be found through Internet searches. Updates to download for Windows computers can also be found through www.microsoft.com/downloads. 3.3. Virus and Malware Prevention and Removal Viruses, spyware and other malicious programs can all be referred to together as malware. Malware prevention is a significant maintenance task for a computer lab manager. Without vigilance, a computer lab will quickly become prey to malware. It will spread from machine to machine causing the computers to slow down, work improperly or possibly even stop working altogether. The computer lab manager needs to make sure that all of the computers have anti-virus software installed, and that this software is set up so that it regularly updates its virus databases and scans the computers. The tip box here gives more details on how to do this. The computer lab manager also needs to have strict policies in place to prevent virus infection. Since viruses are easily spread by the use of flash drives, the policy could prohibit the use of flash drives, or require them to be scanned by a staff member before use. Another policy to consider is the prohibition of downloading, since unsuspecting users can accidentally download malware. A firewall that blocks dangerous downloads can also be useful. 15 Tips for Using Anti-Virus Software 1. You can get very good antivirus protection using the free edition of AVG, available online at http://free.avg.com. No anti-virus software is perfect, however, so you might choose to have a back-up antivirus program as well. Avast antivirus, available at www.avast.com will work well and will not conflict with AVG if it is not set up to scan automatically. Another good back-up program is Malwarebytes’ Anti-Malware program, available at www.malwarebytes.org. 2. After installing antivirus software, make sure that you have selected the settings needed for the software to automatically download and install updates from the Internet. This allows the software to protect against newer viruses. To change the settings for AVG choose Update Manager from the Overview screen. 3. When setting up antivirus software, make sure that you choose the proper settings so that the computer is automatically scanned for viruses on a regular basis (such as every day at 12:00). Also make sure that you have selected for the scheduled scans to “run on computer startup if task has been missed”. In other words, if you have chosen to have scans run at 8:00, but the computer isn’t turned on until 10:00, it will still run a scan. In AVG these options are chosen by choosing Manage Scheduled Scans from the Computer Scanner screen. 4. Make sure that your computer has the proper date and time set. If it is not set properly, the update manager and schedule scans may not run at the time you desire. If your computer does not keep proper time, this is a sign that the small (watch style) battery on the motherboard needs to be replaced. 3.4. Computer Hardware Maintenance There are some common hardware problems that can be avoided, or at least made less frequent by taking particular preventive measures with computers. These preventive measures are listed below. Dust Control. Dust is very harmful for computer parts. Excess dust can cause mechanical failures, particularly on computer components with moving parts. Minimizing dust in a computer lab is an important part of computer maintenance. Computer lab cleaning advice is discussed further in Module 2. The computers themselves should be regularly dusted (wiped with a dry cloth or duster) and if the computers are housed in a particularly dusty area, the use of dust covers (when the computers are turned off) is advised. In addition, when a computer case is opened for other repairs, the dust that has built up inside the case should be blown out. This works best with forced air. Different mechanical and electrical tools are available to compress air. These tools are described in section 5.7.1. Heat Control. Computer parts, in particular the CPU, produce a large amount of heat while operating. It is important for this heat to dissipate, so that the computer is not damaged by overheating. Computers do have fans and heat sinks, but these will only work well if the air 16 flow to the computer is not blocked. This means, for example, that a laptop computer should not be left running for any length of time on a soft surface (like a sofa) that conforms around it, and a desktop computer case should not be used while in an enclosed cabinet. In addition, it is ideal that the computer lab temperature be kept low. Using air conditioners is a good option, since the windows can also be kept closed to minimize dust, but many computer projects cannot afford air conditioners or the associated electricity costs. Therefore curtains (to reduce the heat of the sunlight), open windows and fans are often the best alternatives, although their use requires increased vigilance against dust. Surge Protection. In many countries, the electrical supply does not have a uniform (well controlled) voltage. Voltage is also variable due to surges that occur, particularly during thunderstorms and when power is returning after an outage. Voltage surges can be very damaging to computers and other electrical components, and it is important to protect against these events. The simplest form of surge protection is to purchase surge protecting power (adaptor) strips. These devices contain 4 or 5 outlets that are protected by a fuse that is blown in case of a power surge. The quality of these power strips varies, though, and they cannot be guaranteed to be the safest form of surge protection. A second form of surge protection is a surge suppressor that is installed where the main power enters a computer lab. These devices, though more expensive, are of higher quality and will protect all of the electrical components plugged in to electrical sockets within the room. A third option to consider is to purchase uninterrupted power supplies (UPSs) to share between every two computers in a computer lab (since a UPS includes six to ten electrical sockets). A UPS regulates the voltage sent to the sockets located on the UPS itself, and also contains a battery that allows for continued operation of a computer after a power outage. Depending on the UPS model and the amount of equipment attached to the UPS, the battery might last for an hour or for just a few minutes, but even just a few minutes allows enough time for the user to save their work and shut the computer down properly. Laptop Maintenance Issues. For computer labs using laptop computers, there are a couple of additional issues to be aware of that can affect the lifespan of the computer. Because laptop computers are moved around from place to place and handled more roughly than desktop computers, they are more likely to have hardware problems develop. One problem area, for example, is in the AC adaptor port. If it is found in the back of a laptop computer, it is easy for the computer user to tilt the laptop backwards and unintentionally place pressure on the AC adaptor as it is forced against the table top. The AC port (and any other port located on the back of a laptop) can be easily damaged from this stress. Therefore computer users should be instructed on the proper technique to use when picking up a laptop computer. A second problem area for laptop computers is that the screws on the laptop body gradually become loosened as the computer is moved about. A computer lab manager should periodically (perhaps twice a year) tighten the screws on all laptop computers. 3.5. Peripheral Hardware Use and Maintenance 17 Peripheral hardware will also last longer if it is well maintained. For peripheral hardware such as printers, projectors and external drives, all of the advice above about heat, dust and power surge control is still relevant and important. In addition, there are some tips below for using printers and projectors that will help these pieces of equipment work efficiently and last a long time. Proper Use of an LCD Projector. An LCD projector is a valuable tool for making presentations and assisting in training courses. However, these projectors are very expensive to purchase. If a computer project has had the good fortune of being able to purchase a projector, it is important that every effort be taken to make sure that the projector is kept in good repair. Some suggestions are shown here: Store and carry the projector in a padded case. This will keep dust out of the projector and cushion it in case of rough handling. Keep a designated surge protecting power strip (adaptor strip) with the projector, and make sure that all projector users know the importance of using the projector with surge protector. Make sure that the appropriate procedure for shutting down the projector is used, and inform all projector users about the procedure. For most projectors, the proper shut down procedure includes not unplugging the projector until the cooling process is complete. This is indicated by a status light changing color, or a fan turning itself off. It is important to allow the projector bulb to cool completely in order to extend the life of the bulb. It is particularly important to note that the projector bulb, which is the most expensive part in a projector, will wear out and need to be replaced eventually. Projector bulbs can cost half the price of buying a new projector! A computer project will need to make a plan for bulb replacement, ideally even keeping a spare bulb on hand. Efficient Use of a Printer. Most computer labs will have at least one printer for the use of the computer lab manager and selected computer lab users. Printers are a great resource, but if not controlled well they can be overused. This puts unnecessary wear on the printer, and also uses up expensive ink and paper. It would be wise for a computer lab manager to have in place some policies about what sort of material can be printed, and when color ink use is allowed. Users should also be instructed to preview their work before printing, to avoid printing unnecessary pages. In addition, many printers have different printing settings that control the quality of the printouts and thus the amount of ink used. Inkjet printers, for example, usually have an option for “draft” or “fast” printing that uses significantly less ink, but still looks reasonably good. To find this option when printing a document, select Print from the File menu (or the Office Button in MS Word 2007). When the print menu opens, there will be a Properties button next to the selected printer. Clicking here will bring up choices such as the print quality and whether the printout should be in color or black and white. 3.6. Assignments/Activities 18 3.6.1. Find and open the anti-virus software on a computer. Check to see if the virus database is up to date. If it isn’t, update the software and also see if there is an option to setup the program to automatically look for updates. Also see if there is an option that allows you to schedule regular (daily) scans. 3.6.2. Go to a local computer lab and ask the computer lab manager about maintenance tasks. What tasks does he or she do to keep the computers in good condition, and how often are these tasks performed (daily, weekly, monthly or yearly)? If the computer lab manger does not have any maintenance systems in place, instead report your recommendations for computer maintenance. 3.6.3. Open the case of a computer and observe the dust inside. What tools do you have at hand that could be used to safely remove that dust without damaging the equipment? Experiment with the equipment that is available to you and report your findings. 3.6.4. Figure out how to set up a printer so that the default print settings are black and white (not color) and “draft” or “fast” printing. 3.6.5. Workshop Activity: Observe a demonstration on how to properly set up and shut down an LCD projector. Make sure that you have an opportunity to practice these techniques yourself sometime during the workshop. 3.6.6. Workshop Activity: Using provided tools, find and tighten all of the screws on a laptop computer. 3.6.7. Workshop Activity: Participate in a role play (and follow up discussion) in which a lab manager tries to convince a person with a home computer to bring it in to the lab for updates. Table of Contents 4. Setting Up or Customizing a Computer 4.1. When a Computer Arrives What should be done before using a new computer? This depends very much on where the computer came from and what software was already installed. If a computer project receives new computers complete with an operating system and all productivity software, little needs to be done before using the computers. The computer lab manager should check, however, to make sure the computer is fully set up to meet the needs of the project. Some items to investigate are listed here: Does the computer already have all of the programs that are desired for the project? This could include, for example, an Internet browser, productivity (office) software, antivirus software or perhaps some educational software. Does the computer already have all of the files that are desired for the project? For example, an educational project might want to have an encyclopedia or some educational presentations loaded on all of the computers. Does the computer have separate user accounts with passwords? This is a good way to control what access some users have to particular programs, files or settings. See 19 section 4.5 for more information. Another option to consider is installing and using Microsoft SteadyState as a way to control what part of a computer certain users can access (see Module 2, section 6.2.4 for more information). 4.2. Partitioning a Hard Drive A partitioned hard drive is one that has two (or more) different sections for storage of different types of information. In some cases, one partition is used to store the operating system and related files, while the other partition is used to store user documents and settings. This partitioning is valuable in cases when the hard disk has not failed, but the partition with the operating system needs to be reformatted due to some sort of localized problem. Then the computer user’s documents and settings are not lost in the process. This sort of partitioning is usually done when installing a computer operating system. Computer lab managers can see the tip box in the next section for more information on this process. A computer lab manager can, however, create a new partition at any time. If a new computer arrives with an operating system installed but without a separate partition, the computer lab manager may want to add one or two partitions. A separate partition can also be used by a computer lab manager that would like to have two different operating systems on the same hard drive, with one operating system loaded onto each partition. The tip box here describes the process for creating a partition after an operating system has already been installed. Tips for Partitioning a Hard Drive Please Note: The instructions below are for a computer running Windows XP or Vista that a computer lab manager would like to add a partition to without reinstalling the current operating system. 1. Go to Start Control Panel Administrative Tools (for Windows Vista, Administrative Tools is found inside System and Maintenance). 2. Double click on Computer Management, and then from the left side of the window select Disk Management. 3. The window that appears will show the different disks in the computer. Right click in the space to the right of the label for the hard disk, and click New Simple Volume. The New Simple Volume wizard will open. Follow the prompts to format the new volume with an NTFS file system. Please Note: if a disk is already partitioned, right clicking on a partition volume and will give you options to change its size or delete the partition. 4.3. Installing Operating Systems If a computer project receives a new computer with no software or with an unlicensed operating system, the computer lab manager will need to install a new operating system. The computer lab manager will need to choose between installing an open source operating system (such as Ubuntu) or go with a proprietary operating system (such as Microsoft Windows). While legal copies of the most current Microsoft operating system (Windows 7 in 2010) are expensive, a computer project may be able to find less expensive or free copies of older versions of Windows, through 20 a Community Microsoft Authorized Refurbisher (MAR). Some computer refurbishing centers in developing countries are MARs. Please see the website: www.microsoft.com/communitymar. An operating system should be installed from a CD-ROM or DVD disk. Before installation, the computer lab manager needs to set up the computer so that it boots from the CD or DVD drive first. This is the default arrangement for newer computers, but older computers may boot first from the floppy drive. After installing the new operating system, the lab manger needs to be sure to change this back again to the standard boot order. Details on how to change the boot order and how to install an operating system are shown in the tip box here. Tips for Installing an Operating System 1. Make sure that the computer is set to boot first from the CD/DVD drive. To do this, enter the BIOS Setup program when starting up the computer. This will require pressing a key during startup. The key (often one of the function keys or the delete key) is specified at the bottom of the first screen during boot up. When the BIOS Setup program opens, scroll down (using the down arrow) to the “First Boot Device” line, and then use the onscreen instructions to select CDROM and save the change. 2. Shut down the computer, put the operating system CD or DVD into the drive, and then start the computer again. 3. The installation will automatically start, and you will be guided through the process by on screen tips and questions. Make sure you read each screen! 4. You will be asked for your preferences in regards to installation language, time and currency formats and keyboard layouts. Please note that the more common keyboard layout in your country might be United States English, even for those using the British English language. 5. When prompted, enter the product key (for Microsoft Windows operating systems). This is an important step for affirming the legality of your copy, and will allow your computer full access to online updates. Make sure, however, that you know how many computers your product license is good for, and then do not load the operating system onto too many computers. 6. When prompted, choose the location (which partition) for installing the operating system. You may also be given the option of creating new partitions at this step. If so, the partition created for the operating system should be at least 20 GB, preferably 30 GB. Make sure that you format the partition using the NTFS file system. 7. Follow any more on screen prompts and then wait patiently for the installation to finish. 8. Don’t forget to change your boot order back to the original setting! 4.4. Installing and Uninstalling Other Software Knowing the proper method for installing and uninstalling programs is important for any computer lab manager. Consider the situation, for example, when a computer lab manager has 21 been using fee-based antivirus software, but the free trial subscription has expired. He or she has decided to install free anti-virus software, rather than pay a subscription fee for the original software, but needs to know how to uninstall the initial anti-virus software first. It is possible that if the original anti-virus software remains, it will cause conflicts with the new anti-virus software, either preventing it from functioning properly or slowing down the computer. Another reason it is useful to know how to uninstall software, is to know how to respond when a computer lab user has downloaded software that is unnecessary, inappropriate or slowing down the computer. The steps for properly uninstalling software are shown in the tip box here. Tips for Uninstalling Software 1. Make sure that the software you wish to remove is not vital for the functioning of the computer. If you aren’t sure, ask co-workers or search the Internet to learn more about that software. 2. Once you are sure that you want to remove that software, go to the Start menu and select Control Panel. In Windows XP you should click on the choice for Add/Remove programs. In Windows Vista, click on the choice for Programs then select Uninstall a Program. 3. A list of installed software will appear. Choose the program that you wish to remove, and then select Uninstall or Remove. You will then be guided through the removal steps. 4. If not prompted to do so, restart your computer after completing the removal process. When the computer restarts, check the list of programs again to make sure the desired program was fully removed. Installing software is typically easier than uninstalling. The Add/Remove programs screen can be used to install software, but most software will automatically install once you open its installer program. It is important, however, that a computer lab manager make sure that he or she is installing software that is beneficial for the computers, compatible with the current operating system and will not slow down the functioning of the computers. A good way to find these programs is through the C-Net website, www.download.com. More details are included in the tip box here, which uses touch typing practice software as an example. 22 Tips for Finding and Installing Software 1. Consider carefully what software will be beneficial for your computer users. Then go to the website www.download.com to find software that has been previously tested and reviewed by users, and is known to be free of spyware. 2. At the above website, search for programs that are compatible with your operating system, and meet your needs. In this example, enter “free touch typing” in the search box. 3. Click on one of the software choices: “Rapid Typing Tutor”. Then read some reviews and make sure that the software is compatible with your operating system. If it meets your needs, select “download now”. 4. Your computer will prompt you to confirm that you wish to download and/or install the software. If given a choice, choose to save the software to install it later. The file you save can then be used to perform the installation on other computers without needing to download the software again. Make sure that you save the file in a place that you will be able to find it again. 5. Once the download is complete, open the file to begin the installation. You will be asked to confirm the installation and a wizard will guide you through the installation process. In this example, installation of Rapid Typing will be followed by giving you some options about how to setup the program, including language choices, keyboard layout and whether typing speeds should be recorded in words per minute (wpm) or characters per minute (cpm). 4.5. Setting Up User Accounts A user account is a set of information that is used by a computer’s operating system to designate the settings that a particular user prefers (such as desktop background or icon size), control what files and folders a user can access, and control what changes a user is permitted to make to a computer. After a new operating system has been installed on a computer, the user is required to set up an initial user account. This account is by default an administrator account, which means that the user of this account has the ability to access and change all computer settings, and install and uninstall programs as desired. In most cases, a computer lab manager will not want all of the other lab users to also have these privileges and will therefore want to set up more restricted user accounts for other computer users. Depending on the type of computer project, the lab manager might want to set up general accounts for all users of a certain type (such as an account called “students” or “clients”) or they might want to set up specific password protected accounts for individual users. User accounts can be easily set up by a lab manager who is logged into a computer using an administrator account. For a Windows computer the lab manager would select Start Control Panel User Accounts. On a computer running the Ubuntu operating system the lab manager would go to the main menu and choose System Administration Users and Groups. Once there, the lab manager will able to set up the account and choose the privileges 23 for those users. For Windows computers, the “standard” account type should be chosen for all users that the lab manger does not want to have administrative privileges. The lab manager can also log in to his or her administrative account on a computer to remove users or change the passwords on user accounts as needed to control access. 4.6. Assignments/Activities 4.6.1. Is the computer you usually use partitioned? Follow the instructions in the “Tips for Partitioning a Hard Drive” tip box to the point where you can see what partitions are already there and what their sizes are. If your computer is already partitioned, what sorts of files or programs are stored on each partition? See if you can find this out by opening My Computer. 4.6.2. Following the steps in “Tips for Uninstalling Software” tip box, find and uninstall a bit of unnecessary software that you find on your computer. If the computer is not yours, or if you aren’t sure which software is unnecessary, ask for assistance and permission first. 4.6.3. Explore the www.download.com website. Can you tell the difference between sponsored (paid advertising) links and the programs that are recommended by CNET? Summarize your findings. Also browse through the different categories of programs. See if you can find some that would be useful for a computer project in your area. 4.6.4. Set up a new user account on a computer and then log into the computer using this account. How is the appearance different and how are the privileges different? 4.6.5. Workshop Activity: As a group, find a list of installed software on a computer (for Windows computers this can be done through the Add/Remove Software tool in the Control Panel). Review the list and discuss what each software program does. Determine whether or not any of these programs should be removed from the computer. 4.6.6. Workshop Activity: As a group, install a new operating system on a test computer. 4.6.7. Workshop Activity: As a group, discuss what types of software are needed for a new computer. Develop a list of software that would work well in a computer project in your area. If time allows and the software is available, install all of these programs on the computer used in the previous activity. Table of Contents 5. Computer Troubleshooting and Repair Basics This section of Module 1 is designed to empower the computer lab manager to take care of minor computer problems. Without the knowledge here, many lab managers will end up letting computers sit idle that could be easily put back into service, or paying for expensive repairs that could have been handled locally. There will still be times when computers fail and need to be sent out for repair by an expert, but those times should be few and far between. 5.1. Improving Slow Performance Many of us have had an experience with a computer in which we open a program, and then find that we are waiting for over a minute for the program to actually open. Some of us 24 have also had the experience of turning on a computer and then having to wait several minutes for the computer to fully start up and load all of the features that we are accustomed to seeing on the desktop. There can be several reasons for this sort of slow speed, and many of these reasons are due to problems that can be easily addressed. Several possible problems and the strategies for addressing them are described in the sections below. Please note that software solutions are discussed before hardware solutions since the software solutions are usually the right place to start for computers that have gradually decreased in performance over time. In some cases, however, such as much older computers with small amounts of RAM and slow processors, the hardware solutions will be more effective. 5.1.1. Hard Disk Fragmentation Over time, all computer hard disks become fragmented. Fragmentation is when files are stored in different “pieces” in different places on a hard drive, depending on what storage space was available when the file was last modified. As the amount of free space on a hard drive decreases, typically the fragmentation increases. Accessing files becomes slower because the computer has to look around in different places on the hard drive to find the different pieces of a file. To address this problem, a hard drive should be defragmented. Defragmenting can also become a regular maintenance task for heavily used computers to keep them performing well. Most computers come with a defragmentation program installed. On a Windows computer it should be found in Start All Programs Accessories System Tools. If no defragmenting program is found there, some free defragmenting programs are available from www.download.com. 5.1.2. Excess/Unused Files As a hard disk becomes full, a computer’s performance is reduced. It takes more time to find and access needed files, and defragmentation is not as successful due to a lack of free space to temporarily move files to while they are being rearranged. For best performance, there should be at least 1 GB of free space on the computer’s hard disk. Therefore, it is wise for a computer user not to keep files that are no longer needed. Files that have been stored in a user’s documents folder that are no longer needed (such as extra photos or older versions of documents) are best deleted individually by the user. A computer lab manager should also have a policy and procedure for regularly deleting old files created by computer lab users on shared computers. In an educational lab, for example, the lab manager could announce that student files are deleted at the end of every term, unless the student makes special arrangements to preserve his or her work. Sometimes there are other files, such as temporary Internet files, that are stored on a computer without the user knowing it. To delete these sorts of files, perform both of the following techniques: Disk Cleanup. In a Windows computer the Disk Cleanup utility is found in Start All Programs Accessories System Tools. It scans a hard disk for unnecessary files, and then (with the user’s permission) removes these files. 25 Deleting Browsing History. When using the Internet, the browser stores the recent history of the web pages that the user has viewed, in order to make it easier to find and load these web pages again. The browser also stores other small bits of information such as data entered into forms and usernames or passwords if a user has asked a web page to “remember me” (although this is not a good idea for shared computers). This stored information can be easily deleted. In Mozilla Firefox, choose Clear Recent History from the Tools menu. In Internet Explorer, choose Delete Browsing History from the Tools menu. 5.1.3. Excess/Unused Software Excess software, particularly if it is software that loads when the computer is booting up, can certainly slow performance. If a user is certain that a particular program is not used and is not needed for the computer to function properly, then this software can and should be deleted, as described in section 4.4. It is also possible to stop some software from automatically starting up when the computer boots. For computers running Windows operating systems, the System Configuration Utility can be used to perform this task. From the Start menu choose Run then type in “MSCONFIG” (for Windows Vista users, find the Run command line from Start All Programs Accessories Run). From the window that appears, choose the Startup tab, and then unselect any programs that do not need to be enabled during computer start up. 5.1.4. Hard Disk Faults Most computers come installed with a program that allows a user to scan the hard disk for faults and even repair them if possible. On many Windows computers there is a program called Scandisk, found in Start All Programs Accessories System Tools Scandisk. Another option is to run a program called Chkdsk, available on all Windows computers. To run Chkdsk, go to Start My Computer and then right click on the image for the C: drive. Select Properties and then click on the Tools tab. Under Error Checking, click Check Now. The computer may require the check to happen while restarting the computer and if so will schedule this task to occur. 5.1.5. Malware Viruses, worms, spyware and adware are collectively known as malware. These undesirable programs, which are usually added without a user’s knowledge, can significantly slow down the performance of a computer. Keeping antivirus software up to date and running scans on a regular basis are the best ways to prevent virus infections. This is discussed further in section 3.3. Occasionally, however, a computer will still become infected with a virus or other bit of malware that the anti-virus program did not catch. Some signs of these infections, other than slow speed, could be strange files popping up in folders, new small programs that appear (with an .exe file extension) or odd performance issues. When this occurs, the computer lab manager can do an Internet search using the names of the strange files or programs, or a description of other symptoms. These searches will often result in information about the particular malware infection and how to remove it. Another option for computer lab 26 manager is to try scanning the computer with a second anti-virus program, which might identify the infection that the other anti-virus software missed. However, the lab manager needs to be aware of the possibility that the two anti-virus programs will conflict with each other and themselves cause the computer to run poorly. If a second anti-virus program is installed, the computer lab manager should make sure that it is not also set up to do any sort of automatic scanning. 5.1.6. Overheating Excessive heat can cause a significant decrease in computer performance. In order to cool down an overheated computer processor, the first step to take is to try to cool the environment around the computer. Avoid operating the computer if the case is in an enclosed space (such as a drawer or cupboard). Also try to cool the room with fans or air-conditioning. The next step is to verify that all of the fans in the computer case are functioning properly. Check around the computer vents to see if the spinning of the fans can be observed or if airflow can be detected. If neither of these steps address the problem, the computer lab manager could consider installing additional fans or replacing the existing fans with higher quality ones. 5.1.7. Insufficient RAM If none of the measures discussed above have resulted in improved performance, it’s possible that a computer does not have sufficient RAM to perform the desired functions. This problem is most likely if the computer is rather old and has had a newer (and more memory demanding) operating system installed. For example, a computer with only 256 MB of RAM would operate slowly with Windows XP, and would not be able to operate Windows Vista. One option to address this problem is to install a less demanding operating system. The lightweight open source operating system Xubuntu, for example, only requires 192 MB of RAM. Another option is to add more RAM to the computer. Before taking this step, the computer lab manager would need to find out the answers to the following questions: How much RAM does the computer already have? (This information is available from right clicking on My Computer from the Start menu.) What kind of RAM does the computer take? And how much RAM can be added to the computer? The answers to these questions are going to depend on the number of memory slots available, and the capacity of the type of RAM that is compatible with the computer. The best way to find the answers to these questions is via an Internet search using the brand and model of the computer, “memory” and “upgrade” as search terms, or by visiting the website for an online RAM sales company (see section 5.7.3). This should result in the necessary information to make sure that the right kind of memory is purchased (such as size and type – for example is it SDRAM or DDR2 SDRAM?). It will also be important to note whether or not the memory needs to be installed in pairs or if a single strip of RAM will suffice. Does the computer have enough slots to add in the desired memory? It is possible that a computer will already have all of the memory slots filled (for example, there are only two slots and each is already filled with 128 MB RAM strips). In this case, it would not 27 be possible to upgrade to 512 MB of RAM by adding a single strip of 256 MB RAM. The lab manager instead would need to purchase two 256 MB strips of RAM, and take out both of the 128 MB strips. The actual replacement of RAM will be discussed in section 5.7.3 of this module. 5.2. Stepwise Guides for Common Problems There are some computer problems that are common enough that is helpful for a computer lab manager to have some standard steps that he or she can follow in case this sort of problem occurs. Below are the stepwise guides for addressing some standard problems. 5.2.1. The Computer Freezes It is relatively common for a computer Tips for Troubleshooting the “Frozen” Computer to freeze. When a computer “freezes” it 1. Take a deep breath and wait a minute. You should do this to might look like help prevent you from panicking, but it also is a good way to see if the program can fix itself. Perhaps it was engaged in a task everything on the that was using significant memory and just needed extra time. screen has gone still, or 2. See if some windows or programs are still functioning and active. the computer may no If so, save any changes in the functioning programs you are longer responding to working on and then close those programs. This might free up the inputs (such as memory so that the computer can finish whatever task it was mouse clicks) of the working on. user. It is also possible 3. If a program is still frozen, but the computer is functioning in that a single program other ways, simultaneously press the Ctrl, Alt and Del (Delete) will freeze while the rest keys. In a Windows computer this brings up a small program of the computer called the Task Manager, or gives you options including starting remains functional. the Task Manager. Start the Task Manager and click on the Applications tab. Click on the names of any programs that you These problems are not know are not functioning or say they are “Not Responding”. something to panic Then click on End Task. If you are asked to confirm ending the over, since often they task, do so. Then wait a bit, because it can take some time for are not a sign of a major the computer to end the task. hardware problem but 4. If step 3 doesn’t work, or the entire computer is frozen, the only instead a sign of a small step left is to turn off the computer “the wrong way”, by holding glitch that can be easily down the power button until the computer turns off. This fixed by restarting a method can be harmful to running programs or open files, so it program or the is best to be avoided if at all possible. After shutting down in computer. The tip box this manner, the next time the computer is started it will alert here shows some simple the user to the fact that the computer was not shut down properly, and will scan for any files that need to be repaired or steps that the computer recovered due to the improper shut down. lab manager can follow. 28 5.2.2. The Computer Won’t Turn On It can be very frustrating to have a computer that is totally “dead”. It’s not working at all and the user doesn’t know the cause. This tip box includes some steps to take to identify and address some common causes. Tips for Troubleshooting a “Dead” Computer 1. Evaluate the situation more fully. Are the computer and the monitor plugged in to a functioning surge protector or UPS? Is the surge protector or UPS plugged into a functioning outlet on a circuit that has not blown or tripped? If you aren’t sure, try to plug something else that you know works into the same outlet. If that item works, try swapping the power cable with one from a functioning computer. 2. For desktop computers, has the computer supply been set to the wrong voltage? Check and make sure that the switch on the power supply is set to the proper voltage for your country (230V in Zambia). If it wasn’t set properly, switch it and try again, although the power supply may now be damaged. Also make sure that the on/off switch on the power supply is in the on position. If there are still no lights visible on the computer, try replacing the power supply (see section 5.7.3). 3. If there are lights on, but the computer is still not starting, you can try booting from a different drive (see section 5.6.5). 4. If the computer produces a series of beeps when you attempt to boot it, there is a problem with the memory. Try reseating or replacing the memory (see section 5.7.3 for information). 5. If a desktop computer is producing all of the usual startup sounds and lights, but the monitor is not displaying any information, perhaps there is a problem with the monitor. Make sure that it is connected to a power source, and also that the VGA cable is connected to the computer. If there is still no image, try pressing the Fn key and the function key for monitor choices a few times. The proper function key depends on the computer model, but should show a picture of a computer monitor on the key. Also try adjusting the brightness dial on the monitor. If there is still no image, try connecting a different monitor. 5.3. Understanding Error Messages Often when there is a problem with a computer’s hardware or software, the computer will show an error message that explains what the problem is. The computer lab manager should make sure that he or she reads these error messages and takes the information within them into account. Below are some common error message categories and steps that can be taken to address the problems. 5.3.1. Out of Memory Errors Out of memory error messages can be caused by a variety of problems, including memory glitches (that will be solved by rebooting), insufficient memory, poor memory management, not enough hard disk space, faulty memory and software problems. The user may be running too many programs at once, and could try closing some of the open programs. If this doesn’t work, the next step to try is to reboot the computer and see if that fixes the problem. If it does not, the following approaches could be considered: 29 1. Create more space on the hard drive by deleting unnecessary files and then defragmenting. 2. Investigate any recently added software. Does the computer system have enough RAM to run this software? Are there any updates or patches for this software available on the Internet? 3. Is some memory management software running? If so, disable it and see if performance improves. 4. There may be a physical problem with the memory or its connection to the motherboard. Try reseating (removing and replacing) the RAM and if that does not work swapping the RAM (see section 5.7.3) with the RAM from a working computer. 5.3.2. Memory Parity Errors The term parity has to do with two items matching in terms of size, type or operation. A problem with memory parity could be caused by conflicts between two memory (RAM) strips that are of different brands or types. The error could just be a random occurrence, however, so it is best to try to reboot the computer first. If this does not help, the following approaches could be attempted: 1. Remove any recently installed RAM (see section 5.7.3) to see if it is causing the issue. 2. Try a different power outlet or power strip, because a poor power supply could also cause this error. 3. There may be a physical problem with the memory or its connection to the motherboard. Try reseating the RAM and if that does not work swapping the RAM with the RAM from a working computer. 4. There may be a problem with the motherboard. Consider replacing the motherboard. 5.3.3. “The Blue Screen of Death” “The Blue Screen of Death” is the colloquial name given to the error code that occurs with Windows operating systems when a critical error has occurred that causes the system to shut down to prevent further errors. Its nickname comes from the fact that the screen turns blue in color, and the computer “dies” or “crashes”, meaning it is shut down. These errors are often caused by poorly functioning device drivers, hardware problems (such as with memory, power supplies or system overheating), or problems with the system software. Some suggestions for managing the Blue Screen of Death are shown in the tip box here. 30 Tips for Managing the “Blue Screen of Death” 1. Take a deep breath. It may not be a serious problem, and panicking won’t help. Also if you have been saving your work frequently as you go (which is always a good idea), you will not have lost much information. 2. Make a note of any error code numbers shown in the text on the blue screen. If the problem persists later it might be helpful to look these error codes up on the Internet (from another computer). 3. Restart the computer. First do not open the program that you were using when the crash occurred, but instead see if other programs operate normally. Then open that program to see if the crash occurs again. It’s possible that the event was random and won’t occur again, or it’s possible that there is a problem with the software program you were using. 4. If it appears to be a problem with a specific piece of software, search online for updates or patches for that program, or try reinstalling the program. Also make sure that the computer meets the specifications (operating system, processor speed and RAM) for running that software. 5. Make sure that the computer’s operating system is fully updated. 6. If the problem appears to occur when using a specific computer device, the driver could be faulty. When the computer is running, check the Device Manager for problems and possible solutions (see section 5.5 and 5.7.2). 7. Check for problems with the computer’s fans, power supply or memory, as discussed in section 5.1. 5.4. How to Search for Information It is very important that a computer lab manager not “give up” easily when presented with a computer problem. Instead the computer lab manager should turn the problem into an opportunity to gain knowledge about computers. This includes asking for help and searching for information about the particular problem, its causes and solutions. The first step in this process is to see what advice is available on the computer itself (or another one running the same operating system). With Windows computers, there are “Help and Support” documents located on the computer, and more available on the Internet. From the Start menu, click on Help and Support and then see which categories of help best match the problem. If a computer lab manager doesn’t find the needed answers using Help and Support on the computer, the next step is to find answers on the Internet. In most cases, the computer problems that a lab manager encounters will not be new or unique. Someone else would have had the same problem and would have written a description of how they solved the problem. It is important that the computer lab manager give very specific search terms and try different terms if not successful at first. For example, if a lab manager is having problems getting the sound to work on a specific computer, “sound problems” would not be a specific enough search. The lab manager would be better trying “sound problem Dell D600” or “sound failure 31 Dell D600”. If the lab manager knows that the problem is due to the device driver, an even better search would be “sound device driver problem Dell D600”. 5.5. How to Distinguish a Software Tips for Distinguishing Between Hardware Problems and Issue from a Hardware Software Problems Issue 1. Make sure you reduce possible “external” problems before It isn’t always easy proceeding. This means unplug any external devices (such as to know the source of a hard drives, scanners or printers), and remove any floppy, CD or computer problem, but DVD disks from their drives. determining whether the 2. Were there any loud noises or smoke when the problem first problem is with hardware appeared? Then it is probably a hardware problem, with the or software will help give most likely culprit being the power supply unit. a computer lab manager 3. Is the computer entirely dead? Or the screen blank? Or the some direction for action screen showing a poor/incomplete picture? These faults are in troubleshooting and probably also due to hardware problems. 4. Does the computer produce a series of beeps? This is a code repair. Some general that can be used to distinguish some hardware problems. guidelines for 5. Does the system give any error codes or descriptions while distinguishing between booting? These can be due to hardware or software problems. hardware problems and Take careful note of all information given in the error code. software problems are in 6. Does the computer produce error information after it has the tip box here, but one booted or only when you open specific programs? These error general bit of advice is codes are probably due to software problems. important for all 7. Have any recent changes been made to hardware or software computer (including BIOS settings)? If so, these are likely culprits. troubleshooters: think 8. Has the computer been exposed to viruses or other malware? about what was This could be a cause of software problems. 9. Use the Device Manager, which can found on many Windows happening just before the computers (for Windows XP go to Start Control Panel problem occurred. If new System Device Manager). The Device Manager will list all of software was just the hardware devices installed on a PC. Any device with a installed, it is quite likely problem will have a warning symbol next to it, and double that the problem is clicking on that device would give details and suggested caused by that new remedies for the problem. software. If a power surge occurred, it is possible that hardware problems were caused by that power surge. 5.6. Fixing Software Problems 5.6.1. Using Safe Mode Safe Mode is a convenient tool for both troubleshooting and repairing software problems. It is a simplified version of a Windows operating system, which can often be used when a computer is having problems that prevent its standard Windows operating system from loading. To boot a computer in Safe Mode the user should turn on the computer and 32 immediately start tapping the F8 key. After a few moments, the Windows Advanced Options menu will appear. Using the arrow keys, the user can select Safe Mode and then click Enter to proceed. Once a computer has been started in Safe Mode, it is possible to access the diagnostic tools such as Chkdsk (described in section 5.1.4). Other options at this point include running virus scans, uninstalling suspicious software, or using System Restore (see section 5.6.4). 5.6.2. Finding and Installing Updates and Patches If a computer user has identified that there is a problem with a particular piece of software, before uninstalling that software it is wise to see if the software producers have identified and fixed any problems with that software. In many cases this can be done easily by selecting the “Check for Updates” command in the software, often found in the Help menu. Updates are groups of software patches (small fixes to the software’s program) that address problems that were found after the software was released, or provide improvements to the software. If there are any updates available, these should be downloaded and installed. In many cases the computer (or at least the particular software program being updated) will need to be restarted after installation. If a particular piece of software does not have a “Check for Updates” option, the user will need to go to the website for that software and search there for updates. This can also be used to search for individual software patches to address the particular problem that the user has found. It is also possible to do general web searches on a particular software problem and find patches that have been produced by individuals or organizations other than those that produced the software. This can result in good fixes, but can also introduce other problems into a computer system (such as other unforeseen software conflicts or malware). A computer lab manager should proceed very cautiously down this path, if at all. 5.6.3. Reinstalling Software If updates and patches haven’t fixed the problem with a particular piece of software, reinstalling that software is a good step to try next. This will solve problems caused by the corruption of software (damage to the programs) that can be caused by malware. It’s important to properly uninstall all software before reinstalling it. More information on uninstalling and reinstalling software is found in section 4.4 of this module. Reinstalling an operating system is also an option (see section 4.3), but the computer lab manager should make sure that all computer data has been backed up before taking this action. 5.6.4. Using System Restore System Restore is a utility program that is found with most versions of the Microsoft Windows operating system. It periodically (when major software changes are made or at scheduled times) takes images of the computer’s operating system and other software. These images, called restore points, are saved so that the user can “reset” the computer system to 33 that restore point and thus avoid problems that were caused by later changes. If a computer is reset to an earlier restore point, however, any software (whether it was problematic or not) that was installed after the restore point will be uninstalled. To access the System Restore utility on a Windows computer, go to Start All Programs Accessories System Tools System Restore. 5.6.5. Booting from a Different Device During typical use a computer boots (starts) from information and instructions that are in its internal hard drive. A computer can also be booted, however, from other devices such as floppy disks, CD/DVD disks, flash drives or external hard drives. Booting from these devices is the only option if the software on the hard drive has been corrupted to the point that it will not start the computer. The standard boot order for a computer (the order in which the computer looks for startup files) starts with the floppy drive (for older computers), then is followed by the CD or DVD drives and then the internal hard drive. This means that any time the computer starts up it will first read any disk in the floppy drive to see if startup files are contained there, and then moves on to the CD/DVD drive if startup files are not found. This order can be changed by following the steps in the tip box in section 4.3 of this module. In order to boot from a disk, the computer user must have a boot disk or recovery disk for that computer. Boot disks contain only critical startup files, and they are best prepared and used by experienced computer technicians. They can also be used as a part of the reimaging process, described below. Recovery disks used to come standard with all new computers. In recent years, however, the computer manufacturers have instead set up systems for users to create their own recovery disks when first using a new computer. If a computer lab manager has recently received new computers, he or she would be wise to create recovery disks before putting the computers into general use. 5.6.6. Reimaging Computers One very handy “tool” for a computer lab manager to have for managing software problems is disk reimaging (also known as cloning). The idea here is that a lab manager can create a complete copy of a computer’s system when it is running perfectly. These copies, which are known as images or clones, include all software and files. The purpose of having these images is that when a computer in the computer lab fails due to a software problem, the computer lab manager can choose to reimage or clone the computer using the perfect image, rather than uninstalling and reinstalling each software program separately until the problem is identified and fixed. One type of proprietary reimaging software is called Symantec Ghost (see www.ghost.com). A common open source reimaging program is called Clonezilla (see www.clonezilla.org). 34 Before creating an image, the computer lab manager should make sure that the computer is set up “perfectly” and free of any malware. Images are best made when a computer is newly setup, before it has seen much use. However the lab manager should make sure that the computer that is being used to create the image has already been loaded with all the utilities, productivity software and educational materials that are commonly used in that computer lab. The tip box here suggests some items. The computer lab manager should also make sure that all of the programs have been updated fully, as discussed in section 5.6.2 of this module. Tips for Creating a Computer Image A computer that is going to serve as an image or clone, to be used on other computers, should meet the following criteria: 1. Its make, model and hardware are identical (or nearly so) to the computers that it is going to be used to clone. It is important that it only be used to reimage computers that have hard drives of the same size or larger. 2. It is new or has recently had its operating system and other software reinstalled. This reduces the chance that it would have any malware or have had undesirable changes made to software settings. Also all of the software should have been recently updated. 3. It does not contain any personal files or other unnecessary files, folders or software. 4. It does include software that is going to be commonly used on the computers that it is going to be used to image. For example it should include: a. Common utilities such as antivirus software and Before creating an image, printer drivers a computer lab manager needs b. Productivity software such as Microsoft Office to consider two questions: 1. or Open Office What drive should be used to c. Educational materials that will be useful locally. boot the computer from while This could include touch typing programs, creating the image and reimaging encyclopedias, or any locally appropriate a computer? And 2. What media educational content. will be used to store the computer image? The answers to these questions will depend on the imaging program being used and the limitations of the computer system. When using Clonezilla Live, for example, the program can be downloaded from the Internet to fit onto a bootable CD ROM disk. Therefore one option is to boot the computers from the Clonezilla Live CD. The image that is created then can be easily stored on a flash drive or external hard drive, using the USB port. For complete instructions on using Clonezilla Live, please see the www.clonezilla.org website. Once an image has been created, it can be stored until needed to reimage the computer it was created from or any other computer with identical hardware. This is very useful for a computer lab that received a donation of ten identical computers, for example. If using the image to reimage another computer in a computer lab, however, there are some important points that the computer lab manager needs to keep in mind. The first is computer identity. Any cloned computers will have the same name and Security Identification (SID). The computer 35 lab manager should change the name of the computer after reimaging by right clicking on the Computer (or My Computer) icon or menu item and then selecting Properties. The computer SID can remain unchanged. The second important point is that the software license keys will be the same for all cloned computers. If the computers are running proprietary software, the computer lab manager needs to be aware of how many computers are permitted to run on a single license. If a license is only for an individual computer, the computer lab manager will need to buy additional license keys for the software in question and enter the proper license keys into the computer. 5.7. Fixing Hardware Problems 5.7.1. Tools and Safe Repair Practices What tools will a computer lab manager need to perform basic hardware repair? This will depend on the type of computers being worked on, and also on what tools are locally available. However, good quality screwdrivers in different sizes will be on every lab’s equipment list. The majority of the screws encountered in computers are of the Phillips type (the screw head has an X shape on the top), but flat head and hex head screws may also occur. A computer lab manager can look and see what types of screws are in use in the lab before making a purchase. Magnetic tip screwdrivers can be very useful since the screws will stay magnetically attached to the screwdriver while the lab manager locates the screw hole. However it is very important to avoid touching the tips of magnetic screwdrivers to RAM or hard drives, since the magnetic storage on those devices could be damaged. A pair of needle nose pliers may also be useful to assist when working in narrow spaces. For cleaning computer parts, a computer lab manager will need some method for blowing dust out of computer hardware. If an electric blower is available, this is a very good option. Otherwise a hand operated blower (with a bellows or bladder attached to a narrow outlet) will do. If affordable, a computer lab manager can also purchase compressed air in aerosol cans. For dusting and cleaning computer and monitor cases, a lint free cloth is best. Screens (LCD and CRT) can be cleaned with slightly damp cloths or with small amounts of mild cleaning solutions that have been reported to be safe for computer monitors. If RAM needs to be cleaned, isopropyl alcohol and lint free swaps can be used. There are several safety concerns (both for the lab manager and for the computer equipment) that need to be attended to. They are listed below. Working Environment. The computer work room should be clean, well organized and properly lit. Avoid hazards to the computer (such as dust or moisture) and hazards to the workers (such as electrical cords that can be tripped over). The lab manager should also consider good organization as a way to make repair work more efficient. It should be easy for a worker to return to a project without any difficulty finding the parts involved. 36 Static Electricity. Static electricity discharges (sparks) can be significantly damaging to computer equipment such as RAM, CPUs and motherboards. Therefore it is important for the computer lab manager to ground him Tips for Avoiding Electrostatic Shocks or herself before working with computer 1. Avoid walking around as much as possible while equipment. The tip box working on a computer. Shuffling your feet here gives some (particularly on carpeted surfaces) can build up suggestions. If electrostatic charges. electrostatic mats or 2. Make sure to ground yourself before beginning a grounding wrist straps computer repair. The simplest way to do this is to are available locally, touch a large metal object (such as a filing cabinet these items can also be or metal computer case). used to prevent 3. Before picking up each new computer component, electrostatic shocks. ground yourself again. Electrical Shock. Before opening up the case of a computer or any other electronic device or cleaning it with any fluid, make sure that it is unplugged. Otherwise, electricity can be transmitted through the electronic device and into the worker’s body. This can cause severe injury or even death. Laptop batteries should also be removed before performing any laptop computer repairs. It is best to avoid attempting repairs on computer monitors, particularly CRT monitors due to a risk of a dangerous electrical discharge. 5.7.2. Hardware Repair Planning and Strategy Before beginning a computer hardware repair, it is important to make sure that the repair is necessary and that a repair plan is in place. To determine if a repair is necessary, the lab manager should have worked through the troubleshooting steps described earlier in this module. If a computer is still operational, the lab manager should be using software tools to diagnose (and in some cases repair) problems before physically opening the computer. For example, the Device Manager (described in section 5.5) can be used to check for hardware faults, and a hard drive diagnostic tool (such as Chkdsk, described in section 5.1.4) can be used to determine if a hard drive needs to be replaced. Also remember that error messages can give important information about what is wrong with a computer. When developing a repair plan, the computer lab manager needs to know which parts are going to be replaced and how to find and remove those parts from the computer. It is also important to have replacement parts on hand that are known to be in good condition. Part re-seating and part swapping are both good strategies to keep in mind when repairing computers. Re-seating means removing or disconnecting a part, cleaning it if appropriate, and correctly replacing the part. Sometimes a computer part can function poorly just because a connection is loose or dirty, and re-seating will improve its performance. If this does not solve a problem, a good next step is to try to swap the same part with one from a 37 functioning computer. This can be a useful part of troubleshooting, since it helps the lab manager identify whether or not that part truly is the source of a computer problem, before a purchase is made. People who are just learning about computer repair can easily practice this with peripheral devices. If a desktop computer keyboard appears not to be working, for example, try replacing it with a keyboard that is known to work properly. 5.7.3. Basic Hardware Repairs Below are descriptions of some of the most common hardware repairs, including key steps in the process. In all cases, however, the lab manager who is just beginning to work on computer repair would be encouraged to complete these repairs alongside a more experienced technician as they gain skill and confidence. If the lab manager has an opportunity (through this course or any other) to attend a hardware repair training session, he or she should insist on being involved in as much hands-on training as is possible. Replacing a Power Supply. For desktop computers in developing countries, power supply failure is a common problem. This is due to an uneven or “dirty” voltage and power surges. Before replacing a power supply, a lab manager should make sure that it truly is dead by following the tip box in section 5.2.2. Then follow the steps below: 1. Unplug the power cord from the back of the computer case. 2. Open up the computer case. The method varies with the brand and model of computer, but often involves laying the case on its side and opening up the side panel. Some computer cases use screws and others have buttons to press that release one side panel. 3. Find and unscrew all of the screws attaching the power supply to the back of the case. Usually there will be four screws, located just outside the cut out in the case (or along the mesh grid) where the power supply is found. Do not disconnect the various cables yet. Move the dead power supply as far out of the way as the cables will allow. You may be able to set the power supply on top of the case (see photo). 4. Install the new power supply and screw in all screws. 5. One by one, detach the cables from Figure 3 - Replacing a Power Supply the old power supply to the various computer components, and replace For the complete procedure see http://www.fonerbooks.com/r_power.htm them with the cables from the new power supply. Doing this one by one will help make sure that no components are missed. There will be power supply connectors for the motherboard and all drives. When removing the cables, keep an eye out for latches that need to be depressed to 38 release the connector. All of the connectors should only fit in one direction, and with little force. If a connector does not attach easily, make sure that it is properly aligned before pushing harder. Replacing a Hard Drive. Replacing a faulty hard drive is not a difficult task, but a lab manager should have done some investigative work first to determine if the hard drive is faulty. This could include running the Chkdsk utility, as described in section 5.1.4, listening for unusual noises coming from the hard drive and also checking to make sure the cables to the hard drive are still fully connected. The computer may also present error codes during start up that indicate a problem with the hard drive. Before replacing a hard drive, it is worth trying to reset the BIOS to the default settings to see if this fixes the problem. To do this, enter the BIOS during computer start up (as described in section 4.3) and choose the default settings. Then save the new settings and exit. The onscreen instructions in the BIOS program will guide the computer lab manager through these steps. Once it has been determined that a hard drive problem is likely, the computer lab manager should follow the steps below to replace the hard drive with a known working hard drive. 1. Disconnect the computer case from electricity and then open the computer case (as described above). 2. Locate the hard drive. It will likely be found in a metal case or cage near the front of the computer case, below the other drives. It could be mounted directly on the cage or it could be mounted on rails that will slide out of the case (see photo). 3. Unscrew the hard drive from the cage or slide the rails out and unscrew the hard drive from the rails. 4. Remove the long ribbon cable from hard drive. There may have been a Figure 4 - Removing a Hard Drive small amount of glue used to hold For the complete procedure see the ribbon in place that will also http://www.fonerbooks.com/r_hard.htm need to be removed. Then remove the smaller power cable. If it is difficult to remove, gently wiggle the connector back and forth along its long axis as you pull. Note the orientation of the connector (which end is the red wire on?) to make sure that the new hard drive is connected in the same manner. 5. If there are two hard drives in a computer, one is called the master and the other the slave. On older hard drives, an electrical connection needs to be changed to indicate whether the hard drive is a master or a slave. If the hard drive being installed has not 39 been used before, it will be correctly set as a master (or also on the acceptable “Cable Select” setting, used when the ribbon cable has two connectors – one for a master and one for a slave). If the hard drive has been previously used as a slave, however, it will need to be changed to a master. To do this, look for a diagram on the hard drive that shows the pattern for connecting (jumping) two of the eight pins located between the two cable connectors on the front end of the hard drive. Then using needle nose pliers, pull off the jumper that is connecting two of the pins and replace it to connect the proper pair. 6. Connect the cables to the new hard drive. Then screw the hard drive back on to the rails and slide the rails into position (or screw the hard drive directly to the cage if there are no rails). Make sure that all of the other ribbons and cables are as they were found. Close the case and the repair is complete. Note that if any new noises or problems appear after the installation, it is possible that another device or cable was disrupted during the repair and needs to be reattached or reseated. Replacing a Hard Drive for a Laptop Computer. Hard drives for many laptop computers can be replaced quite easily because the manufacturers have made the hard drives accessible from hatches on the underside of the computer. To replace the hard drive on a laptop with an accessible hard drive follow the steps below: 1. Remove the laptop battery before making this (or any other) laptop repair. This is important in order to avoid electricity from the battery flowing through the computer during repair, which could be damaging to computer components. The technique for removing the battery depends on the make and model of the laptop, but often involves unlocking the battery at one or two points (on the underside of the computer) and then sliding it out. 2. With the laptop resting upside down on a table, find the hard drive compartment and unscrew the screw or screws holding the lid in place. Remove the lid and examine how the hard drive is attached to the computer. Most likely you will see that the hard drive is attached to a Figure 5 - A Laptop Hard Drive in its "Cage" cage or brackets that will slide out For the complete procedure see http://www.fonerbooks.com/laptop_1.htm with the hard drive (see photo). 3. Slide out the assembly containing the hard drive in its cage or brackets. You may have to push the assembly in or lift it up first in order to clear anything else used to hold the assembly in place. 4. Remove any screws attaching the laptop to its cage/brackets, remove the damaged hard drive, replace it with a functioning laptop hard drive and then retighten all screws. 40 5. Slide the assembly back into the laptop and secure it as it was previously. Make sure that you push hard enough to reattach the hard drive to the power and data connectors. Push horizontally (or as close as possible to horizontally) when reconnecting. 6. Close the hard drive compartment and replace all screws. Then replace the laptop battery, turn the computer over and restart it. Replacing RAM. As discussed in section 5.1.7, a lab manager may want to add RAM to speed up a slow computer. RAM also can fail or come loose from its housing and need to be reseated. If a lab manager has decided that a computer needs new or additional RAM, it is important to make sure that the RAM used is compatible with the computer system. There are several online RAM sales companies that will identify the appropriate RAM if a user inputs the computer make and model. Two example companies are Corsair (www.corsairmemory.com) and Crucial (www.crucial.com). Once the RAM has been obtained, the lab manager should follow the steps below to replace the RAM. Please Note: RAM is very easily damaged by electrostatic charges, so it is very important for the user to be grounded before picking up RAM. Also RAM should only be handled by the edges. 1. Open the computer case as previously described. Find the RAM slots (long parallel connectors). Note which slots are occupied and if the slots are numbered (at the ends). If the slots are not numbered, the slots closest to the processor are probably the lower numbered slots and should be filled first. 2. Simultaneously push down and out on both retaining clips (on each end) of a RAM slot to remove the old RAM. Note the orientation of the RAM so that the replacement RAM can be put in facing the same direction. There should be some notches on the bottom edge of the RAM that can be used as a guide. 3. Gently place the new RAM in the socket and press down firmly on the top of the RAM at both ends (see photo). When the RAM module is correctly seated, the retaining clips will automatically close. Figure 6 - Installing RAM 4. Close the computer case as previously For the complete procedure see described. http://www.fonerbooks.com/r_ram.htm Replacing Laptop RAM. Laptop computers have a compartment on the back side designed for accessing RAM. When the screws for this compartment are removed (but don’t forget to remove the laptop battery first for safety reasons!), the RAM should be visible. For some laptops, however, only the slot for expansion (extra) RAM is visible. In these cases the rest of the RAM is can be accessed by removing the keyboard, a more difficult task (discussed below). Laptop RAM rests horizontally, with the slot on one end. To install RAM, hold the RAM 41 by its edges, and bring it up towards its slot at about a 30 degree angle (see photo). Then gently push the RAM in while flattening out the angle. Other Laptop Repairs. It is possible to replace the keyboard, individual keys or the screen on a laptop with only a moderate amount of difficulty. The challenge, however, is that every different model of laptop requires a different method for accessing and removing these Figure 7 - Replacing Laptop RAM parts. Either a lab manager should watch For the complete procedure see other people do these repairs and learn http://www.fonerbooks.com/laptop_2.htm from them, or find information on the Internet for the specific desired repair. Specific searches should result in detailed diagrams, descriptions or videos. For example, if someone wanted to replace a key on a Dell laptop, the search terms “replacing laptop keys Dell” will yield useful results. Similarly, if someone wanted to replace the entire keyboard on a Toshiba laptop, the search terms “replacing laptop keyboard Toshiba” will suffice. In general when performing laptop repairs, the computer lab manager should remember these guiding principles: 1. Always remove the battery first for safety reasons. 2. Keep note of what screws are removed and in what order. Also keep track of the actual screws! 3. When taking a laptop apart, be slow and mindful of the process. This will make it easier to put the computer back together afterwards. For complicated repairs, consider keeping notes of the steps performed. 5.8. Troubleshooting and Repairing Printers Problems with a printer are generally in the following categories: 1. Software problems with the computer, including problems with the printer driver 2. Poor connections or electrical problems with the printer 3. Insufficient ink 4. Paper jam 5. Printer hardware problems All of these except for number five are easily managed by a trained computer lab manager. The tip box here gives some suggestions for troubleshooting a faulty printer. 42 Tips for Troubleshooting Printer Problems 1. Try restarting the printer (by turning it on and off at the switch) and the computer (using the standard restart technique). 2. Make sure that the computer is sending the document to the right printer by checking the printer name in the dialog box that comes up when printing a document. To change the default printer (on a Windows computer) choose the Printer window in the Control Panel. If the printer you are using is not listed, you will need to add that printer and install the drivers for that printer. Printer drivers are usually available online by going to the website for the printer manufacturer and searching for the drivers for the particular printer model. 3. Try to print a test page for the printer. If you are using MS Windows, open the Printer window in the Control Panel, right click on the icon for the printer you are using, choose Properties and then select “Print Test Page”. If the test page prints successfully, the problem is with the application (productivity software) you are using and not the printer. 4. If the printer does not successfully print as above, note what happens. Does it start to print and then stop? Does it make unusual noises? These are signs of a paper jam or a hardware problem. Open up the top of the printer and look for any jammed paper. 5. Does the printer print faintly or with only some colors? This is a sign that the ink cartridges need to be primed or that the printer is running out of ink. Look at the printer’s instruction book or use the menu and buttons on the printer to figure out how to prime the printer. 5.9. Managing E-Waste In concluding this module, it is important to recognize that not all computer problems can or should be fixed. Sometimes computers become too old or obsolete to make the effort of repairing them worthwhile, and some repairs (such as repairs to CRT computer monitors) are not advisable except by experts. Due to these realities, computer labs often have a collection of old and broken computers and peripheral equipment that develops and increases over the years. This equipment is collectively known as electronic waste or e-waste. In many developing countries e-waste is a problem because the equipment can contain hazardous materials and there often are not recycling or waste facilities that are capable of managing these hazardous materials properly. The first step in managing e-waste is to try to reduce the amount of it that is produced by a computer lab. A lab manager can do this by avoiding accepting donations of equipment that is already very old or obsolete, since this equipment will not remain useful for long. A lab manager can also make sure that existing equipment is maintained well so that it remains useful for a longer period of time. The computer lab manager should also work with any organizations donating computers to discuss the e-waste problem and strategize how the computers will be disposed of properly when they are no longer useful. Options for proper disposal of e-waste will vary from country to country. In some countries there will be private companies that collect e-waste, and in others there will be government projects for e-waste disposal. Larger non-profit organizations that donate used 43 computer equipment often have plans for collecting and managing e-waste. If no e-waste options exist in a particular country, several computer projects could team together to ship a container of e-waste to an e-waste facility in a neighboring country. One e-waste management facility that accepts shipments is Desco Electronic Recyclers in South Africa (www.desco.co.za). 5.10. Assignments/Activities 5.10.1. Compare the start up speed between two computers, by actually starting them both up and noting the time it takes for the desktop to be fully loaded. Then compare the factors that can control the start up time for each computer. Which computer has more programs that load on start up (see section 5.1.3)? Which computer has more RAM? What is the processor speed of each computer? What operating system does each computer use? Summarize your findings. 5.10.2. Update the operating system and productivity (office) software for a computer. Describe the process you used in each case. 5.10.3. Practice running a disk defragmenter and disk cleanup program on a computer. Note any change in performance from before and after defragmentation. 5.10.4. Practice finding help and support on a computer use or troubleshooting topic, both on a computer and online. Choose a computer topic of interest to you. If you do not have a topic in mind, here are some examples: installing a printer, changing the size of desktop icons, using a text reader (text to voice tool), or taking a screen shot (a picture of what is on your desktop screen). Remember to be as specific as possible in your word choice. If at first you are not successful, try other related words. 5.10.5. Practice using diagnostic tools on a computer. For computers running Windows operating systems, try Chkdsk (described in section 5.1.4) and the Device Manager (described in section 5.5). 5.10.6. Investigate a laptop computer. Figure out how to replace and remove the battery. Also identify all ports and the access panels for the hard drive and memory. 5.10.7. Observe a computer repair technician in action. Notice what techniques he or she uses to avoid electrostatic shocks and to clean computer components. Observe at least one software repair and one hardware repair from start to finish. Take notes on these procedures for future use. 5.10.8. Practice properly uninstalling and reinstalling a software program. Choose something that you have a current installer file for. 5.10.9. Practice starting a computer in Safe Mode. Take note of which features of your computer function in Safe Mode and which have been disabled. 5.10.10. Workshop Activity: As a team, set up a computer “perfectly” so that it is ready to produce an image or clone. Then participate in the process of preparing an image and using it to reimage another computer. 5.10.11. Workshop Activity: Practice troubleshooting malfunctioning computers. The instructor may intentionally produce malfunctions in computers in order to provide you with practice 5.10.12. Workshop Activity: Replace the hard drive in a desk top computer. 44 5.10.13. Workshop Activity: Take apart a laptop computer, including accessing all RAM, the keyboard and screen. Then put the laptop back together! Table of Contents 6. Overall Assignments/Activities 6.1. Revisit and reflect on your own skill level after having completed this module: 6.1.1. What skills do you still feel you need in the categories covered by this module? Make a plan for gaining those skills and (if appropriate) discuss the plan with your supervisor. 6.1.2. What skills do you still feel you need in the self-study areas (English reading/writing, touch typing and computer user skills) presented at the beginning of this module? Make a plan for gaining those skills and (if appropriate) discuss it with your supervisor. 6.1.3. Consider the topics covered in Modules 2, 3, and 4 of this course (as described in the introduction to this module). Do you think that taking those courses (or studying the learning materials for those courses independently) will help you meet your career goals? Discuss this with your instructor and your supervisor (if appropriate) and consider your next steps. 6.2. If you work in a project that uses Microsoft or other types of proprietary software, consider making a shift over to an entirely open source environment. What would the benefits and drawbacks of such a shift be? Make a list of all the FOSS software you would need, including the names of specific programs if possible. Also what training would need to occur if you made this switch? 6.3. Workshop Activity: Participate in a team project to overhaul an old computer. Clean the components, add RAM to the computer, install an appropriate operating system and install all other necessary software. 6.4. Workshop Activity: Participate in a workshop evaluation process. Table of Contents 7. List of Internet Resources The table below provides a list of the Internet resources previously mentioned in this document. The resources are listed in the order they appeared in this module. Title TypingTest.Com Rapid Typing Alison (free online courses) Web Address (URL) www.typingtest.com www.rapidtyping.com/typing-tutor.html http://alison.com 45 Sense-Lang.org TypeOnline.co.uk Good Typing European/International Computer Driving License Busuu.com (language training) English Online Goodwill Community Foundation (free courses) BBC World Service Learning English Activities for ESL Students UsingEnglish.com EnglishLearner.com EnglishCafe.com Source Forge Official Ubuntu Documentation Microsoft Downloads AVG Free Antivirus Avast Antivirus Malwarebytes’ Anti-Malware Microsoft Community MAR Program CNET Download.com Symantec Ghost Clonezilla Foner Books – Replacing PC Parts Corsair Memory Crucial (computer memory) Desco Electronic Recyclers www.sense-lang.org www.typeonline.co.uk www.goodtyping.com www.icdl.org www.busuu.com http://www.english-online.org.uk/course.htm www.gcflearnfree.org www.bbc.co.uk/worldservice/learningenglish/ http://a4esl.org www.usingenglish.com www.englishlearner.com www.englishcafe.com www.sourceforge.net http://help.ubuntu.com www.microsoft.com/downloads http://free.avg.com www.avast.com www.malwarebytes.org www.microsoft.com/communitymar www.download.com www.ghost.com www.clonezilla.org www.fonerbooks.com/replace.htm www.corsairmemory.com www.crucial.com www.desco.co.za Table of Contents 8. Bibliography Bit. (2010). In Wikipedia, The Free Encyclopedia. Retrieved January 26, 2010, from: http://en.wikipedia.org/w/index.php?title=Bit&oldid=339499368 46 Blue Screen of Death (2010). In Wikipedia, The Free Encyclopedia. Retrieved January 26, 2010, from: http://en.wikipedia.org/w/index.php?title=Blue_Screen_of_Death&oldid=336735006 Computer. (2010). In Wikipedia, The Free Encyclopedia. Retrieved January 26, 2010, from: http://en.wikipedia.org/w/index.php?title=Computer&oldid=339667990 Computer Ports (Hardware). (2010). In Wikipedia, The Free Encyclopedia. Retrieved January 26, 2010, from: http://en.wikipedia.org/w/index.php?title=Computer_port_(hardware)&oldid=338140393 Computers for Zambian Schools. (2008). Basic Computer Maintenance and Troubleshooting. Lusaka, Zambia. PCTechBytes. (2009). Computer Troubleshooting Zone. Retrieved January 26, 2010, from PCTechBytes: http://www.pctechbytes.com/troubleshooting/ Rosenthal, M. (2009). Replacing Laptop Hard Drives. Retrieved January 26, 2010, from Foner Books: http://www.fonerbooks.com/laptop_1.htm Rosenthal, M. (2008). Replacing PC Parts. Retrieved January 26, 2010, from http://www.fonerbooks.com/replace.htm Rosenthal, M. (2009). Upgrading Laptop Memory. Retrieved January 26, 2010, from Foner Books: http://www.fonerbooks.com/laptop_2.htm Yarnold, S. (2008). Upgrading and Fixing a PC, Second Edition. Warwickshire, United Kingdom: In Easy Steps Limited. Table of Contents About Zambia Pacific Trust There are many challenges for schools and community organizations in Zambia to consider when starting or maintaining computer projects. Sourcing good quality computers is just the beginning. The organizations also need to consider infrastructure issues, staff training, computer education curricula, and internet connectivity. Zambia Pacific Trust (ZPT) helps institutions address these challenges through advice, training, and a cost-sharing grant process. ZPT currently works with five schools in the Lusaka area, but has plans to add other organizations in the future. For more information please contact info@zptrust.org. About Heidi Neff 47 Heidi Neff is a former high school science teacher with 15 years of experience in the classroom. While teaching in Seattle, Washington, she used computers extensively as a part of her curriculum. She also assisted with computer training in Zambian schools as a part of the Seattle Academy Zambia Program. Ms. Neff starting working with ZPT in 2006, assisting their efforts to support school computer projects in Zambia. She is currently a consultant specializing in IT in Education. For more information please contact her at heidi.h.heff@gmail.com. 48