A Two-Country Model of Speculative Attacks
advertisement
A Two-Country Model of Speculative Attacks
Carlos Lopez
U.C. Berkeley
Raul Razo-Garcia∗
Department of Economics
Carleton University
October 2013
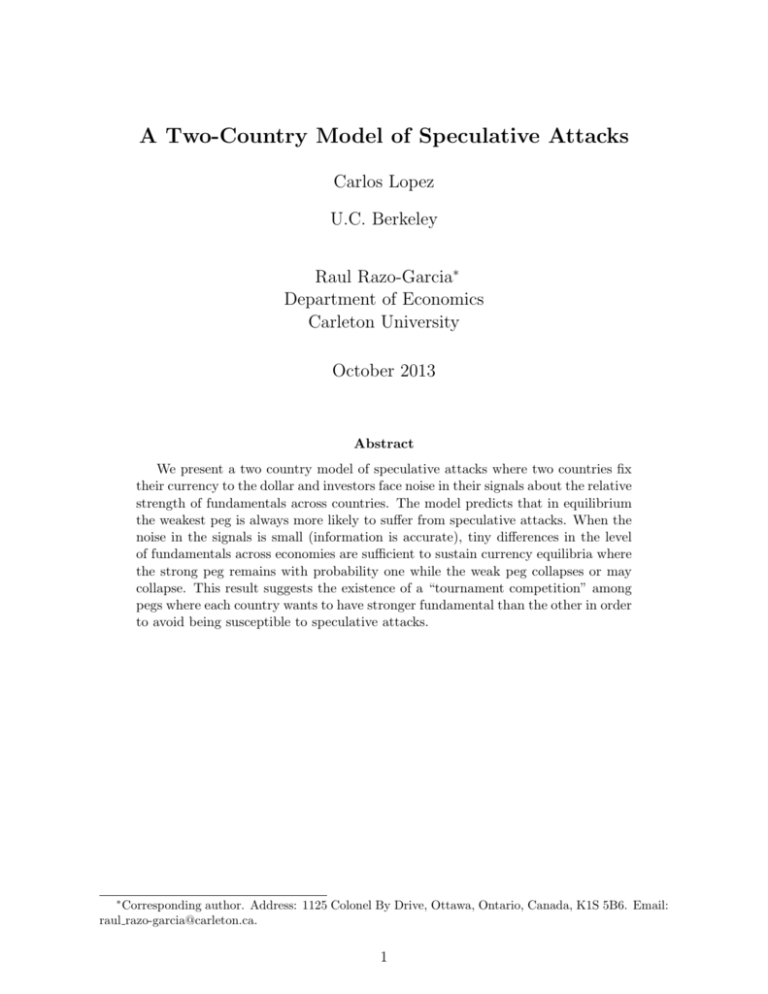
Abstract
We present a two country model of speculative attacks where two countries fix
their currency to the dollar and investors face noise in their signals about the relative
strength of fundamentals across countries. The model predicts that in equilibrium
the weakest peg is always more likely to suffer from speculative attacks. When the
noise in the signals is small (information is accurate), tiny differences in the level
of fundamentals across economies are sufficient to sustain currency equilibria where
the strong peg remains with probability one while the weak peg collapses or may
collapse. This result suggests the existence of a “tournament competition” among
pegs where each country wants to have stronger fundamental than the other in order
to avoid being susceptible to speculative attacks.
∗
Corresponding author. Address: 1125 Colonel By Drive, Ottawa, Ontario, Canada, K1S 5B6. Email:
raul razo-garcia@carleton.ca.
1
1
Introduction
Between the breakdown of the Bretton Woods and the early 21th century the world economy witnessed the collapse of many fixed exchange rates. Emerging markets, developing
countries and, to a lesser extent, advanced countries went through several episodes of
financial instability characterized by speculative currency attacks and currency crises. In
1992, for example, the Exchange Rate Mechanism, one of the main components of the
European Monetary System, was severely challenged by speculators. European countries
pegging their exchange rates faced a series of speculative currency attacks. The pressures
on both Italian lira and the British pound became so large, that both were suspended
from the Exchange Rate Mechanism and depreciated rapidly afterwards. Realignments
of some of the other members’ currencies were also observed between 1992 and 1993.1
Fixed exchange rates in emerging markets were also challenged by speculators. On
December 1994, with international reserves reduced to less than six billion U.S. dollars,
the Mexican government abandoned its crawling band and allowed the Mexican peso to
float. After the collapse of the exchange rate band, there was a financial crisis. Interest
rates soared and the peso plunged. Almost three years later, on May 1997, the Thai baht
was hit by massive speculative currency attacks. The Thai government failed to defend
its peg and was eventually forced to let the baht to float.
Currency crises have strong spillover effects on other countries and the mentioned
crises were not the exception. For example, the Mexican crisis affected, among others,
Argentina and Brazil, as well as Malaysia, the Philippines, and Thailand. Similarly, the
collapse of the Thai baht caused devaluations in Indonesia, Malaysia, the Philippines, and
the Republic of Korea, while it provoked a much wider direct or indirect turbulence in
both developed and emerging markets around the world (e.g. Russian in 1998).
A large literature has developed to explain speculative currency attacks, currency
crises and contagion. One strand, focuses on trying to understand why speculative attacks and currency crises may occur. It is argued that a balance of payment crisis may
arise as a consequence of a steady deterioration in macroeconomic fundamentals (Krugman 1979), self-fulfilling speculation (Obstfeld 1996), or strategic uncertainty (Morris and
Shin 1998). Another strand explains why a currency crisis in one country may spread
1
The Spanish peseta, the Portuguese escudo and the Irish pound were realigned.
2
internationally. Different channels of contagion have been proposed. Common arguments
are that currency crises spread to other countries through common fundamentals (Gerlach
and Smets 1995), herding behavior (Calvo and Mendoza 2000), asymmetric information
(Calvo 1999), hedging macroeconomic risk (Kodres and Pritsker 2002), or frictions in the
financial markets (Pavlova and Rigobon 2005).
Yet despite these efforts to understand currency crises and contagion, there is still
one question completely disregarded in the literature: where the initial attack will occur?
In other words, what peg should be attacked first (e.g. why the East Asian currency
crisis started in Thailand rather than in Indonesia, Malaysia or Philippines)? Current
models of financial crises and contagion provide an incomplete answer to this question.
For example, balance of payment models with complete information predict that the selffulfilling nature on the investors’ expectations may generate a currency crisis in almost
any of the existent pegs.2 The reason is that if investors believe some peg, either weak
or strong, is going to collapse they would attack it, inducing the government to abandon
the peg and vindicating the initial belief. This raises one question: why do investors
coordinate their actions against a strong peg when a weaker peg would be more likely to
collapse?
The aim of the paper is to analyze where initial speculative attack and currency crisis
should be located. Unfortunately, previous global games models of currency attacks and
crises cannot be used for doing so because they consider only a single peg (e.g. Morris
and Shin 1998 and Guimaraes and Morris 2007). Building on the work of Morris and Shin
(1998) and Guimaraes and Morris (2007) we propose a two country model of speculative
attacks where a continuum of risk neutral investors face strategic uncertainty and the
two countries peg their currency to the dollar. In the model, market participants face
uncertainty about the difference of the fundamentals across the two pegs but are certain
about “regional” level of fundamentals, defined as the average level of fundamentals of
the two countries. In doing so, this paper makes one key contribution: to analyze what
currency should be attacked or defended first out of two pegs.
To simplify the analysis we assume payoffs are constant, so that it will always be
profitable for an investor to short positions in a collapsing peg in the event of a collapse,
2
Unless the level of fundamentals is so high that it would not be profitable for investors to attack it
in the first place.
3
even when the economic fundamentals of such peg are very strong. We focus on threshold
equilibria, where for each possible realization of the “regional” level of fundamentals there
will be a collapse of a peg if and only if its level of fundamentals is below its threshold level.
The main insight to emerge is that, in equilibrium, a weak peg is always in disadvantage
relative to the strong peg. In addition, we show that the precision of private information
plays a key role in the model. More precise information means that investors react more
strongly to differences in the level of fundamentals. Hence, when private information
is precise, tiny differences in the level of fundamentals will be sufficient to sustain an
equilibrium where the strong peg remains while the weak one collapses. This result has
important implications for emerging markets and developing countries because it provides
a plausible explanation for why these countries may want to be overcautious regarding
the strength of their fundamentals.
The rest of the paper is organized as follows. Section 2 presents the model. In Section
3 we solve the model assuming complete information. Section 4 solves the model under
strategic uncertainty and presents the states of the world that are possible on equilibria.
Some final remarks are included in Section 5.
2
The Model
2.1
Economic Environment
There are two countries fixing their currencies to the U.S. dollar and continuum of risk
neutral investors of measure one, indexed by j, uniformly distributed over ∈ [0, 1]. Each
investor j, endowed with a stock of wealth W denominated in dollars, chooses her net
demands for the two local currencies, yi (j) with i ∈ {1, 2}, to maximize her end of period
utility. Whenever yi (j) > 0 the investor is “attacking country (peg) i” because she would
be borrowing (going short) yi (j) dollars in the local currency of peg i in order to invest
that money in dollars. On the other hand, if yi (j) < 0 the investor is “defending peg i”
because she would be borrowing yi (j) dollars in dollars in order to invest that money (go
long) in the local currency of peg i.
Interest rates are assumed to be exogenous while the decision to abandon the peg
remains endogenous. While dollar investments earn an interest rate normalized to zero,
4
the interest rate on the two local currencies is fixed to r. Following Guimaraes and Morris
(2007), we assume that the peg in country i is abandoned if the total demand of currency
i valued in dollars, yi , exceeds the level of fundamentals of peg i (θi ),
Z
yi ≡
1
yi (j)dj > θi
(1)
0
Hence, the stronger the fundamentals, the less likely a peg would collapse from a
speculative attack. This assumption can be seen as a reduced form description of an
optimizing decision by the government whether to defend the peg or not.
Since the two local currencies are fixed to the U.S. dollar there is a possibility that
the exchange rates will be devalued next period. In the event of a collapse, the net rate
of depreciation of exchange rate i is assumed equal to gi (H)(> 0). Let va be the end of
period payoff in dollars of a position yi (j) = 1 when there is a collapse of peg i. Hence,
(1+r)
va ≡ 1 − (1+g
and the investor’s payoffs in this environment are
H)
Table 1: Payoffs
Collapses
Attacks
va
Defends
−va
No Devaluation
−r
r
The net return to attacking a weak collapsing peg, va , is assumed to be larger than
the returns the return in dollars of a position yi (j) = −1 when peg i does not collapse:
va > r
(2)
Inequality (2) is commonly knows as the one way bet assumption.3
3
Assuming that the net rate of depreciation of the peg, in the event of a collapse, is equal to gH implies
that it is always profitable to attack a collapsing peg. Similar qualitative results are obtained relaxing
this assumption.
5
2.2
The Investors’ Problem
Investors maximize their end of period utility subject to a creditor constraint,
∗
y = arg max E0 W + y1
y1 ,y2
1+r
1−
1 + g(θ1 )
+ y2 1 −
1+r
1 + g(θ2 )
s.t. |y1 | + |y2 | ≤
(3)
W
c
(4)
where c ≥ va .
The creditor constraint ensures that wealth is positive in every state of the world
(i.e. investors can build large short or long positions across markets but the size of those
positions cannot exceed
W
c
dollars). In addition, the constraint imposes the simplifying
assumption that the size of an optimal attack equals the size of an optimal defense.4
Unlike the single country model proposed by Guimaraes and Morris (2007), in which
investors can either short or not one dollar, in this model investors can either short or
long
W
c
dollars and may be able to split their positions across the two markets.
Let pi denote the probability of a profitable collapse for peg i. With these probabilities
we can rewrite the maximization program as
y ∗ = arg max [W + y1 (p1 va − (1 − p1 )r) + y2 (p2 va − (1 − p2 )r)]
(5)
(y1 ,y2 )
so the investor j just compares the four levels of expected wealth she can get from setting
(y1 , y2 ) equal to ( Wc , 0), (− Wc , 0), (0, Wc ) or (0, − Wc ) and choose the option with the highest
expected payoff. Thus, the (bang-bang) solution to the investor problem is
( Wc , 0)
(α W , (1 − α) W )
c
c
∗
∗ ∗
y (pi , pj , va /r, W ) = (y1 , y2 ) =
W
(− c , 0)
(−α W , −(1 − α) W )
c
c
if f pi + pj >
2r
va +r
and pi > pj
if f pi + pj >
2r
va +r
and pi = pj
if f pi + pj ≤
2r
va +r
and pi < pj
if f pi + pj ≤
2r
va +r
and pi = pj
(6)
where α is a random variable with support in the interval [0,1], independent across individuals and with finite first and second moments given by µα and σα2 .5
We assume that µα is a random variable in the population with first moment equal to
4
If inequality (4) is replaced by the Inada conditions all the results would remain. Inequality (4) is
analogous to the constraint used by Morris and Shin (1998).
5
The solution of the investor problem is presented in the Appendix.
6
1
2
so that there is no particular bias against any of the two pegs. The implication of this
“no bias assumption” is that whenever a fraction z of the population sets their positions
equal to (y1 , y2 ) = (αW/c, (1 − α)W/c) there is an aggregate position that converges in
probability to (zW/2c, zW/2c) by the law of large numbers. So that aggregate positions
equal the ones obtained if all these investors were perfectly hedging across markets (i.e.
(y1 , y2 ) = (W/2c, W/2c)) rather than randomizing their position across markets. An
identical argument applies when a fraction of the investors are randomizing with long
positions across markets by setting (y1 , y2 ) = (−αW/c, −(1 − α)W/c). Thus, hereafter we
may refer occasionally to the optimal solutions (αW/c, (1 − α)W/c) and (−αW/c, −(1 −
α)W/c) as the ones where investors are either attacking or defending both pegs equally,
in the sense that on average the statement will always be true.
Figure 1 shows the solution of the investor problem. The solution depends only on
the sum of probabilities and the identity (450 ) line. For example, attacking peg 1 at the
dollar amount
W
c
if the p1 + p2 >
is the solution of the investor problem (i.e. (y1∗ , y2∗ ) = ( Wc , 0)) if and only
2r
va +2
and p1 > p2 . Similarly, defending peg 1 at the dollar amount
the solution of the investor problem (i.e. (y1∗ , y2∗ ) = (− Wc , 0)) if and only if p1 + p2 ≤
and p1 < p2 .
Figure 1: Solution of the Investor Problem
1
P1=P2
P2
2r
va+r
Attack 2
r
va+r
Attack 1
Defend 1
Defend 2
P1+P2=2r/(va+r)
0
0
r
va+r
2r
va+r
P1
7
1
W
c
is
2r
va +2
3
Complete information.
We now solve the model under the assumption that investors know the realization of
the fundamentals, θ, and there is common knowledge about this information. Common
knowledge about θ opens the door for multiple equilibria. The reason is that any initial
belief investors may have about the collapse of a peg would be self-fulfilling in equilibrium,
provided some general conditions on the realization of the fundamentals hold.
Now we provide an exact mapping from the realization of the fundamentals into the
set of possible equilibria. We do this by deriving the set of probabilities that could be
sustained in equilibrium (the set of possible self-fulfilling beliefs) and then computing the
set of fundamentals that are consistent with each possible self-fulfilling belief.
Deriving the set of probabilities that can be sustained in equilibrium is not difficult.
There are only four sets of expected probabilities that could be self-fulfilling,
1. Investors know that y i > θi for i = 1 , 2 ; implying p1 = p2 = 1. In this case the
optimal investment strategy for all investors is to randomize short position across
markets (y ∗ (pi , pj , va /r, W ) = (αW/c, (1 − α)W/c)) generating a net aggregate demand equal to W/2c for both pegs. Then, there is an equilibrium where both pegs
collapse as long as the fundamentals in both economies are smaller than W/2c.
2. Investors know that y i > θi only for country i, implying pi = 1 and p−i = 0. In
this scenario, the optimal investor strategy is to attack peg i at W/c without taking
positions in the other country. These expectations would be self-fulfilling as long as
the fundamentals in country i are smaller than W/c and the fundamentals in the
other country are larger than zero.6
3. Investors know that y i > θi does not hold for i = 1 , 2 ; implying p1 = p2 = 0.
Here, it is optimal for investors to set y ∗ (pi , pj , va /r, W ) = (−αW/c, −(1 − α)W/c)
generating a net aggregate demand equal to −W/2c for both pegs. Then, there is
an equilibrium where both pegs remain if the fundamentals of both pegs are larger
than −W/2c.
The mapping from the realization of the fundamentals into the set of possible currency
equilibria is presented in Figure 2. There are four thresholds denominated CC, RR, RC
6
If the fundamentals of the other peg were below zero there would also be a collapse of that peg.
8
and CR. CC is the threshold for the equilibrium in which peg 1 and peg 2 collapse, RR
is the threshold for the remain peg 1 and remain peg 2 equilibrium, RC is the boundary
of the case where peg 1 remains but peg 2 collapses, and CR represents the threshold for
the collapse peg 1 and remain peg 2 equilibrium. The set of fundamentals (θ1 , θ2 ), located
to the left and below the threshold CC correspond to the equilibrium where both pegs
collapse. The region located above and to the right of RR correspond to the equilibrium
where both pegs remain. The set located above and to the left of CR correspond to
the equilibrium where only peg 1 collapses, while the set below and to the right of RC
correspond to the set where only peg 2 collapses.
Figure 2: Currency Equilibria with Complete Information
RR
CR
θ2
1 State Possible:
Both Pegs Remain
1 State Possible:
W/c
Only Peg 1 collapses
RC
2 States Possible:
3 States Possible:
“Both remain” or
“Only Peg 1
Collapses”
All but “Both collapse”
W/2c
CC
2 States Possible :
3 States Possible:
“Both Collapse” or
All but “Only Peg 2
Collapses”
All 4 States
Possible
“Only Peg 1 Collapses”
θ1
CR
-W/2c
W/2c
(0,0)
W/c
2 States Possible:
3 States Possible:
2 States Possible:
“Both collapse” or
“Both remain”
All but “Only 1
collapses”
“Both remain” or “Only Peg 2 Collapses”
RR
-W/2c
2 States Possible:
1 State Possible:
“Both collapse” or
1 State Possible:
“Only Peg 2 Collapses”
Only Peg 2 Collapses
Both Pegs Collapse
CC
RC
We now have a full characterization of the currency equilibria in the (θ1 , θ2 ) space of
9
fundamentals. There are four regions with a unique equilibrium (state): 1) when fundamentals are strong in both countries, θ1 >
W
C
and θ2 >
W
that both pegs remain; 2) when θ1 < − 2C
and θ2 >
one where only peg 1 collapses; 3) when θ1 >
W
2C
W
2C
W
,
C
the only possible equilibrium is
then the unique equilibrium is the
W
and θ2 < − 2C
then the only equilibrium
is the one where only peg 2 collapses; and 4) when both fundamentals are weak (negative)
W
and, at least one of them is smaller than − 2C
, then the only possible equilibrium is a
collapse of both pegs.
There are other regions where 2, 3 or even 4 currency equilibria are possible. For
W
≤ θi ≤
example, in all sets close to the origin (i.e. − 2C
W
2C
for i = 1, 2) it is possible
to observe a successful double attack or defense of the pegs. Within this region of fundamentals the extreme case is located where 0 ≤ θi ≤
W
2C
for i = 1, 2, because all four
currency equilibria are possible. In fact, under complete information there is a range of
fundamentals where the strong regime may collapse while the weak peg remains in place
so that in principle any peg could be successfully attacked 0 ≤ θi ≤
W
C
for i = 1, 2.7
In the next section we show that an equilibrium where the strong peg collapses while
the weak one remains in place can no longer be true in the presence of strategic uncertainty.
When investors are uncertain about the actions of other investors they would either attack
the weak peg or defend the strong one so that in equilibrium it must be the case that the
strong peg is always in a better position than the weak peg.
4
The Incomplete Information Model.
We introduce incomplete information by assuming that investors observe a noisy private
signal about the differences of fundamentals across countries, θd = θ1 − θ2 , and using the
following decomposition
θd
2
θd
θ2 = θl −
2
θ1 = θl +
(7)
(8)
where θl is the level of “regional” fundamentals, defined as the average of the fundamentals
in the two countries (θl ≡
7
θ1 +θ2
),
2
and θd ≡ θ1 − θ2 . With this decomposition is possible to
This set is given by the square formed by the intersection of thresholds CR and RC.
10
work in a tractable way with the issue of strategic uncertainty regarding “what peg should
be attacked (defended) first” while abstracting from the issue of strategic uncertainty
related to “whether to attack or not” that is studied in detail in Morris and Shin (1998)
and Guimaraes and Morris (2007).
In the model, investors observe θl but there is uncertainty in the size of the differences
of the fundamentals across countries θd . In particular, agents observe noisy private signals
xd (j) = θd + ε(j), where ε(j) is assumed to be uniform in the interval [− √S2 , √S2 ] and the
prior of θd is assumed to be the improper uniform over the entire real line. One way
to think about this is as a world where investors have a precise idea about the level of
fundamentals of the region but are a little uncertain on how weak or strong a peg is
relative to the other. Since positions are bounded we know that: for peg 1 (peg 2), there
is a θd sufficiently large (small) so that the peg remains for sure and a θd sufficiently low
(large) so that the peg collapses for sure.
We focus on threshold equilibria, so that there is a collapse of peg i if the level of
fundamentals in that economy is lower than the threshold θiT
θi < θiT
(9)
We show that a threshold equilibrium exists and that in any possible equilibrium the weak
peg is always in disadvantage relative to the strong peg. We also show that when private
information is very precise tiny differences in the level of fundamentals are sufficient to
sustain the equilibrium result where the strong peg remains while the weak peg collapses.
We prove these results in two steps. First, we show how to derive the mapping from
signals xd into beliefs (p1 , p2 ) and optimal strategies assuming a threshold solution (θ1T , θ2T )
exists. Second, using the previous step and the fact that in equilibrium the thresholds are
identical across countries (i.e. θ1T = θ2T ) we show how to derive the threshold solutions.
4.1
Distribution of Beliefs in the Population.
Here we show how to map signals about the difference of fundamentals into the probabilities p1 and p2 under the assumption that a threshold solution exists. Here, investor j
knows θl and receives a signal xd (j) about the difference on the level of fundamentals that
11
use to infer the probability that the fundamental level of each peg is below its threshold
level.
Since this is a one-dimensional problem (θl is known) we can transform it into a
standard one-dimensional setting where each variable is measured as the distance from
each point to what we call “origin” (where the “origin” here will be the middle point in
the θl line, given by θ1 = θ2 = θl ). In order to do this we use the fact that there is a one
to one relation between θd and a signed measure of the distance between the “origin” and
any point (θ1 , θ2 ) along the line θl
θan (θl , θ1 , θ2 ) ≡
p
(θ1 − θl )2 + (θ2 − θl )2 (1 − 2 ∗ 1θd <0 )
(10)
where 1A is an indicator function assuming the value of 1 if event A occurs. Hence,
this “adjusted norm” is positive when θ1 > θ2 and negative otherwise. The equivalence
between θd and θan (θl ) can be derived using equations (7), (8) and (10)
θan (θl , θ1 , θ2 ) =
p
The equivalent relation θan =
θd
(θ1 − θl )2 + (θ2 − θl )2 (1 − 2 ∗ 1θd <0 ) = √
2
θd
√
2
(11)
allow us to fully restate the problem in terms of θan .
Hence, equations (7) and (8) can be rewritten as follows:
θan
θ1 = θl + √
2
θan
θ2 = θl − √
2
(12)
(13)
The problem where investor j knows θl and receives a signal xd (j) about θd is equivalent
to the one where she knows θl and receives a signal xan (j) about θan
1
xd (j)
xan (j) = √ = √ (θd + ε(j)) = θan + λ(j)
2
2
(14)
where λ(j) is independent across agents and has a uniform distribution with support in
the interval [− S2 , S2 ], while the prior of θan is the improper uniform distribution over the
entire real line.
12
In this framework, the threshold level of pegs 1 and 2 are
T
θd,1
= θl +
= θl +
2
T
θd,2
θ2T (θl ) = θl −
= θl −
2
θ1T (θl )
T
θan,1
√
2
T
θan,2
√
2
(15)
(16)
and the probability of collapse of each peg is just a function of the location of the thresholds
and the signal along the line
θ1 +θ2
2
= θl . The probability of collapse of peg 1 is
T
T
ps1 (xan , θan,1
, S) = P [θ1 < θ1T |xan ] = P [θan < θan,1
|xan ] =
T
= P [xan − λ < θan,1
|xan ] = T[0,1]
T
(θan,1
+ S2 ) − xan
S
!
(17)
where the function T[0,1] (x) truncates the value of x so that it is always located between
0 and 1. That is,
0
T[0,1] (x) ≡
x
1
if x < 0
(18)
if x ∈ [zl , zu ]
otherwise
Similarly, the probability of collapse of peg 2 is given by
T
ps2 (xan , θan,2
, S)
= T[0,1]
T
− S2 )
xan − (θan,2
S
!
(19)
The probability of collapse of peg i depends on three factors: 1) the signal xan ; 2)
T
θan,i
; and 3) the precision of the signals (S). As expected, the higher is xan the lower is
the probability of collapse of peg 1. The reason being that a higher signal reflects an
improvement in fundamentals in country 1 relative to the fundamentals in country 2.8
In contrast, the probability of collapse of peg 2 rises with xan due to the fact that a
higher signal reflects a deterioration in the fundamentals in country 2 relative to country
T
T
1. While p1 rises with θan,1
, p2 declines with θan,2
. For peg i, the intuition is that a higher
T
θan,i
implies that stronger fundamentals in country i are needed to maintain the peg.
Figures 3 and 4 show the mapping of signals xan to beliefs for an arbitrary (symmetric)
T
T
pair of thresholds (θan,1
, θan,2
) for two different levels of S (information precision). The
8
Recall that θd = θ1 − θ2 .
13
T
T
only difference between both figures is that in Figure 3 we assume that θan,1
> θan,2
and
T
T
. In both figures the probability of collapse of peg
< θan,2
in Figure 4 we assume that θan,1
T
T
− S2 , θan,i
1 and peg 2 goes gradually from 0 to 1 in the interval xan (j) ∈ [θan,i
+ S2 ]. This
behavior provide us with an easy to use rule for the derivation of an optimal investment
strategy (the mapping from signals to optimal actions).
Panels A and B in Figures 3 and 4 also show how the precision of the signals affect
the probabilities of collapse. Three interesting facts are observed. First, when the signals
are very accurate investors react more. A lower S increases the slope of the probabilities
T
T
+ S2 ]. In an extreme situation, when S → 0, a
within the interval xan (j) ∈ [θan,i
− S2 , θan,i
T
can be sufficient to change pi from zero to one or
small change in the signal around θan,i
viceversa. Second, the length of the interval on which p1 (p2 ) is decreasing (increasing)
is inversely related to the precision of the signals. Third, the length of the interval of
xan (j) where p1 = p2 decreases with S. When investors have fairly precise information
concerning the difference in the fundamentals (small S), both probabilities are equal to
T
T
+ S2 , θan,1
one (p1 = p2 = 1) in the interval xan (j) ∈ [θan,2
− S2 ] if
T
θan,1
S
≥
1
2
T
T
> θan,2
and θan,1
(Panel A in Figure 3). On the contrary, both probabilities are equal to zero, p1 = p2 = 0,
T
T
in the interval xan (j) ∈ [θan,1
+ S2 , θan,2
− S2 ] if
T
θan,2
S
≥
1
2
T
T
(Panel A
< θan,2
and θan,1
in Figure 4).9 When information is noisy (large S) p1 = p2 only at xa (j) = 0, then
T
θan,1
S
1
2
≤ p1 = p2 < 1 if
(Panel B in Figure 3) or 0 ≤ p1 = p2 <
1
2
if
+
1
2
T
−θan,2
S
+ 12 . In fact,
p1 = p 2 =
=
T
θan,1
S
T
θan,1
S
<
1
2
T
T
> θan,2
and θan,1
T
T
(Panel B in
< θan,2
> − 12 and θan,1
Figure 4).
9
T
T
The symmetry between the thresholds, θan,1
= −θan,2
, implies that if
14
T
θan,i
S
≥
1
2
then
T
θan,−i
S
≤ − 12 .
T
T
Figure 3: Distribution of Beliefs for an Arbitrary Pair of (Symmetric) Thresholds with θan,1
> θan,2
p1, p2
p1
p1, p2
p2
1
p1
15
1/2
θTan,2- S/2
θTan,2
S
θTan,2+ S/2 0 θTan,1-S/2
p2
1
1/2
θTan,1
θTan,1+S/2
S
Panel A: Small S (Precise Information).
xan
θTan,2- S/2
θTan,2
S
θTan,1-S/2 0 θTan,2+ S/2
θTan,1
S
Panel B: Large S (Noisy Information).
θTan,1+S/2
xan
T
T
Figure 4: Distribution of Beliefs for an Arbitrary Pair of (Symmetric) Thresholds with θan,1
< θan,2
p1, p2
p1, p2
p1
p1
p2
1
1/2
16
1/2
θTan,1-S/2
θTan,1
S
θTan,1+S/2 0 θTan,2- S/2
p2
1
xan
θTan,2
θTan,2+ S/2
S
Panel A: Small S (Precise Information).
θTan,1-S/2
θTan,1
S
θTan,2- S/2 0 θTan,1+S/2
θTan,2
S
Panel B: Large S (Noisy Information).
θTan,2+ S/2
xan
An additional result is that the distribution of beliefs on the collapse of peg i is uniform
∗
∗
T
, S) =
exists so that p1 (xan , θan,1
. Hence, if a θan,1
in the population when θan = θan,i
(θ∗ + S )−x an
an,1 2
T
, then the distribution of beliefs on p1 is uniform in the population when
S
∗
T
θan = θan,1
.10 The argument is the following. Consider the case of peg 1, when θan = θan,1
the proportion of the population with p1 < p is given by the proportion of the population
receiving a signal above xIan,1 (p), where xIan,1 (·) is just the inverse function of equation
(17). But such proportion is given by
T
(θan,1
+ S2 )−xIan (p)
S
which equals p by equation (17). It
follows that a p percentage of the population believes that the probability of collapse of
regime 1 is p or lower. That is, the distribution of beliefs is uniform in the population at
the threshold level.11 The proof of this statement is presented in the Appendix.
4.2
Solving the Model With Strategic Uncertainty
4.2.1
The Two Possible Scenarios for a Threshold Solution
For any average level of fundamentals, if a threshold equilibrium exist, this must be symT
T
and θ1T = θ2T .12
= −θan,2
metrically centered around the point θ1 = θ2 = θl , so that θan,1
Therefore, the probabilities, optimal strategies and total net demands can be expressed in
T
T
terms of the size of an intermediate state where both pegs collapse BCC = θan,1
− θan,2
if
10
The same property applies on p2 if
∗
p2 (xan , θan,2
, S)
=T
T
xan −(θan,2
−S
2)
S
∗
and θan = θan,2
.
11
This property is not a special feature of our model or the uniform distribution. It can be shown that
if λ were not uniform, but instead a symmetric random variable centered around zero with support in
T
the interval [s , s], then we could still characterize the mapping of signals to beliefs using ps1 (xan , θan,1
)=
−
T
T
T
Fλ (T[ s ,s] −λ = (θan,1
− xan ) ) and ps2 (xan , θan,2
) = Fλ (T[ s ,s] λ = (xan − θan,2
) ). Furthermore, the dis−
−
tribution of beliefs would also be uniform in the population at the threshold. Then, the convenience of
the uniform distribution in this model is not based on the these properties but instead on the fact that
the mapping of signals to beliefs given by equations (17)and (19) interacts very easily with the optimal
investor rule given by equation (6), facilitating the construction of an optimal investment strategy and
the characterization of the currency equilibria. Guimaraes and Morris (2007) have shown that the distribution of beliefs is uniform in the population at the threshold in a single country model with strategic
uncertainty. See also Morris and Shin (2000) for a case in which investors observe a signal with an
independent normal noise term.
12
A proof of this statement is included in the Appendix. The argument is the following. Let
T
T
, S) denote the net demand of currency i when the realization of fundamentals is
y i (θan , θan,1
, θan,2
T
θan . When θan = θan,i
we can show that the distribution of beliefs in the population regarding the
probability of collapse of regime i and −i is identical for i = 1, 2. This implies that the net aggregate demand a regime faces when θan equals its threshold level is equal for both pegs, that is
T
T
T
T
T
T
y 1 (θan,1
, θan,1
, θan,2
, S) = y 2 (θan,2
, θan,1
, θan,2
, S). Since a necessary condition for an equilibrium is that
T
T
at the threshold net demand equal the level of fundamentals then it must also be true that θan,1
= −θan,2
,
T
T
T
which implies θ1 = θ2 = θ .
17
T
T
T
θan,1
> 0 and an intermediate state where both pegs remain BRR = θan,2
− θan,1
if instead
T
T
T
then
= −θan,2
< 0. Since θan,1
θan,1
BCC
2
T
T
and
= −θan,2
= θan,1
BRR
2
T
T
.
= θan,2
= −θan,1
T
> 0) there is a region where both pegs collapse,
Hence, whenever θT > θl (i.e. θan,1
T
BCC , while if instead θT < θl (i.e. θan,1
< 0) there is a region where both pegs remain, BRR .
Figure 5 shows these two cases. In Panel A of the figure the case where θT > θl is presented
T
T
> 0. In this situation, only peg 1 collapses when the realization
= −θan,2
so that θan,1
T
T
T
) and
, θan,1
, both pegs collapse when θan ∈ (θan,2
of θan is smaller than or equal to θan,2
T
only peg 2 collapses when the realization of θan is larger than or equal to θan,1
.13 Panel B
presents the case where θT < θl so that only peg 1 collapses when the realization of θan is
T
T
T
) and only peg 2
, θan,2
, both pegs remain when θan ∈ (θan,1
smaller than or equal to θan,1
T
collapses when the realization of θan is larger than or equal to θan,2
.
To derive the currency equilibria for any world level of fundamentals θl we follow two
steps. First, derive the set of θl for which a solution where the CC (RR) region exists.
We do this by constructing the net demand at the threshold as a function of BCC (BRR ),
the level of fundamentals at the threshold as a function of BCC (BRR ). Second, derive the
set of θl for which a BCC > 0 (BRR > 0) exists so that the level of fundamentals equal to
the net demand at the threshold for both pegs. We find that for low level of “regional”
fundamentals there is only one threshold equilibrium where CC is an intermediate region,
for intermediate level of “regional” fundamentals there is multiple equilibria, while for
high level of world fundamentals there is only one threshold equilibrium where RR is the
intermediate region.
13
T
Recall that the probability of collapse of peg 1 is given by ps1 (xan , θan,1
, S) = P [θ1 < θ1T |xan ] =
T
T
P [θan < θan,1
|xan ] and the probability of collapse of peg 2 is given by ps2 (xan , θan,1
, S) = P [θ2 <
T
T
T
θ2 |xan ] = P [−θan < −θan,1 |xan ] = P [θan > θan,1 |xan ].
18
Figure 5: The Two Possible Scenarios for a Threshold Solution
Peg 1 Collapses
Peg 1 Collapses
Peg 1 Remains
Peg 1 Remains
θan
θTan,2
θTan,1
0
19
Peg 2 Remains
θan
θTan,1
Peg 2 Collapses
0
θTan,2
Peg 2 Collapses
Peg 2 Remains
θan
θTan,2
θan
θTan,1
θTan,1
θTan,2
CR
CC
RC
CR
RR
RC
Peg 1 Collapses and
Peg 2 Remains
Peg 1 and Peg 2
Collapse
Peg 1 Remains and
Peg 2 Collapses
Peg 1 Collapses and
Peg 2 Remains
Peg 1 and Peg 2
Remain
Peg 1 Remains and
Peg 2 Collapses
T
Panel A: A Region CC Where Both Pegs Collapse (θan,1
> 0).
T
Panel B: A Region RR Where Both Pegs Collapse (θan,1
< 0).
4.2.2
Region Where Both Pegs Collapse (CC)
The first step in the construction of the net demand at the threshold as a function of
BCC is the derivation of the optimal strategies as a function of BCC , the interval where
both pegs collapse. We show that as long as
BCC
S
< 1 investors find optimal to attack one
of the two regimes for any possible signal xan . This result can be graphically verified in
θT
1
Panel B in Figure 3. When signals are noisy relative to BCC , BSCC < 1 i.e. an,1
,
<
S
2
p1 > p2 when xa (j) < 0 and instead p1 ≤ p2 when xa (j) ≥ 0. Hence, investors receiving
a negative signal attack peg 1 while investors receiving a positive signal attack peg 2.14
That is, if
B
S
< 1 then the optimal strategy is given by,
( W , 0)
if xan < 0
c
y(xan , BCC , S, va /r, W ) =
(α Wc , (1 − α) Wc ) if xan = 0
(0, W )
if xan > 0
c
BCC
S
When signals are accurate relative to BCC ,
≥ 1 (i.e
T
θan,1
S
(20)
≥ 21 ), investors with
signals close to zero randomize short positions across markets while the others prefer to
attack only one of the pegs as before.15 This can be verified in Panel A in Figure 3. In the
T
T
+ S2 , θan,1
interval xan (j) ∈ [θan,2
− S2 ] (i.e. when xan (j) ∈ [− BCC
+ S2 , BCC
− S2 ]) p1 = p2 ,
2
2
so in this region of signals investors randomize short positions across markets. Thus, if
T
θan,1
S
≥
1
2
T
T
and θan,1
= −θan,2
> 0, then the optimal strategy is given by
( W , 0)
c
y(xan , BCC , S, va /r, W ) =
(α Wc , (1 − α) Wc )
(0, W )
if xan < − BCC
+
2
S
2
if xan = [− BCC
+ S2 , BCC
− S2 ]
2
2
if xan >
c
BCC
2
−
S
2
(21)
Two interesting results are derived from the optimal strategies in (21). First, the range
of xan where it is optimal to attack both pegs increases with the size of the BCC region
14
From the solution of the investor problem, equation (6), peg 1 is attacked if p1 > p2 and p1 +p2 >
From equations (17) and (19) we know that p1 + p2 =
BCC
S
2r
va+r .
T
T
θan,1
−θan,2
S
2r
va +r .
+ 1. Using the definition of BCC we
θT
−θ T
can prove that p1 + p2 =
+1>
By definition BCC > 0, so p1 + p2 = an,1 S an,2 + 1 > 1 also,
2r
by the one-way bet assumption we have that va+r
< 1. Hence, p1 + p2 > va2r+r .
15
From equation (6), pegs 1 and 2 are both attacked if p1 = p2 and p1 + p2 > va2r+r . From equations
(17) and (19) we know that p1 + p2 =
2r
that va+r
< 1. Hence, p1 + p2 > va2r+r .
T
T
θan,1
−θan,2
S
+ 1 > 1. Also, by the one-way bet assumption we have
20
T
(i.e. θan,1
). Second, the optimal responses of attacking only one of the two pegs remain
always nicely located around the threshold levels (i.e. in the interval xan > θ1T −
peg 1 and in the interval xan < θ2T +
S
2
for peg 2). It is around θ1T −
S
2
S
2
for
(θ2T + S2 ) that the
probability of collapse of peg 1 (peg 2) starts decreasing, so that it is optimal to attack
peg 2 (peg 1), which has a probability of collapse equal to one.
It follows from the optimal strategies in (20) and (21) that the net aggregate demand
that peg i faces at the threshold is decreasing in the size of BCC
T
θan,i
+ S2
y i (θan =
T
θan,i
, BCC /S, W )
Z
=
y ∗ (xan , BCC , S, va /r, W )dxan
T
θan,i
− S2
(1 −
=
0
BCC W
) 2c
S
if BCC < S
(22)
if BCC ≥ S
and the level of fundamentals is increasing in BCC ,
θiT
S BCC BCC
= θl + √ = θl + √
2 2
2 2 S
(23)
The net aggregate demand can be obtained directly from the integral on equation
(22) or by using the property that the distribution of beliefs about the collapse of peg i
is uniform at its threshold.16
We now show that for any θl ≤
W
2c
there is an equilibrium where one or both pegs
collapse. Figure 6 shows the net aggregate demand from equation (22) and the fundamentals level line from equation (23) for several possible values of θl . Since the intercept of
the fundamentals level line is given by θl it is possible to verify that a threshold solution
exists as long as θl <
W
.
2c
In fact, such solution is
BCC
=
S
W
−θl
2c
W
S
√
+
2c
2 2
−θl
2
S
√
√ , W]
if θl ∈ [ 2−S
2 2c
if θl <
2
−S
√
2 2
(24)
When private information is highly precise (i.e. S → 0), θiT → θl for θl > 0 and θiT = 0
CC
Individuals attacking peg i would be those with a pi > pM = 21 + B2S
. Then, the proportion of
individuals attacking the peg would be (1 − pM ) with an aggregate net demand equal to (1 − pM )( W
c ).
16
21
for θl < 0. Therefore, small variations in the realization of fundamentals can switch large
aggregate positions against one country or another so that small differences in fundamentals can determine which one of the two pegs would collapse, providing the foundations
for a rank-order result.
Formally, for any θl <
W
2c
there is a threshold equilibria including a region where both
pegs collapse (CC) with θiT given by
θiT
=
W
2c
W
S
+ √
2c
2 2
0
θl +
S
√
2 2
S
if θl ∈ [− 2√
, W]
2 2c
(25)
S
if θl < − 2√
2
or equivalently,
θiT
=
W
2c
W
+ √S
2c
2
0
θ−i +
S
√
2
if θ−i ∈ [− √S2 , W
]
2c
(26)
if θ−i < − √S2
for i = 1, 2.
T
> 0 with a Region Where Both Pegs Collapse
Figure 6: Deriving the Equilibrium for θan,1
W/2c
Aggregate Net Demand BCC<S
Fundamental Level Lines
yi=
θl > 0
θl =0
(0,0)
B/S
1
θl = -S/23/2
Aggregate Net Demand BCC>S
yi= 0
θl <
-S/23/2
The proof of this result is included in the Appendix. Figure 7 shows how that equilibrium looks like in the space of fundamentals (θ1 , θ2 ). To derive the currency equilibria
22
graphically we first construct two “support lines”. Both of them parallel and equidistant to the 450 line with a total distance between them equals to S. Then to build the
S
, W ] we graph two lines. The first (second) one goes from
equilibrium for θl ∈ [− 2√
2 2c
the intersection of the above (below) “support line” and the θ1 (θ2 ) axis to the point
θ1 = θ2 = θl =
W
.
2c
S
The equilibrium for θl < − 2√
is just given by θiT = 0 for i = 1, 2.
2
Using this construction method we can verify how both thresholds approach to the 450
line when S → 0 for θl ∈ [0, W
], while the thresholds approach to zero for any θl < 0.
2c
In Figure 7 it is possible verify that the threshold θiT increases with θ−i if θ−i ∈
W
}. The intuition is as follows: when fundamentals are neither weak nor strong,
{− √S2 , 2C
an improvement in the fundamentals of country −i makes more difficult to maintain peg
i and this in turn makes more likely an attack to that peg. When fundamentals are
weak, θi < − √S2 the threshold is constant and equal to zero. Therefore, when θiT = 0 any
demand of dollars in country i brings down the fixed exchange rate.
It is possible to verify in Figure 7 that there are three regions in the space of fundamentals (θ1 , θ2 ) if θi <
W
.
2C
A region where both pegs collapse (θ1 < θ1T , θ2 < θiT ), a region
where peg 1 collapses and peg 1 survives (θ1 < θ1T , θ2 ≥ θiT ), and a region where peg 2
collapses and peg 1 survives (θ1 ≥ θ1T , θ2 < θiT ).
T
Figure 7: Currency Equilibria for θan,1
> 0 with a Region Where Both Pegs Collapse
S
Peg 1 Collapses
W/2c
θT1
θT2
Peg 1 Collapses
Peg 2
Collapses
0
W/2c
Peg 2 Collapses
Peg 1 and Peg 2
Collapse
2
23
W/c
1
4.2.3
Region Where Both Pegs Remain (RR)
Following a similar approach we now derive the set of θl for which an equilibrium where
both pegs remain. First, we derive the net demand and the level of fundamentals at the
threshold as a function of BRR . Second, derive the set of θl for which a BRR > 0 exists so
that the level of fundamentals equal to the net demand at the threshold for both pegs.
The obtain the net demand at the threshold it is necessary to derive the optimal
strategies as a function of BRR . We do so by analyzing three sets of
ii)
(va −r)
S
(va +r)
≤
When
BRR
S
BRR
S
<
≤ 1; and iii)
(va −r)
(va +r)
BRR
S
BRR
:
S
i)
BRR
S
<
(va −r)
S;
(va +r)
> 1.
investors find optimal to attack only one of the two pegs for any
signal xan (j) 6= 0. Panel A in Figure 8 shows this optimal strategy. When information is
very noisy relatively to BRR (i.e.
BRR
S
<
(va −r)
),
(va +r)
the probabilities of collapse of both pegs
are the same only at xan (j) = 0; p1 = p2 = 12 (1 −
BRR
).
S
positions across markets only when xan (j) = 0 and
BRR
S
Thus, agents randomize short
<
(va −r) 17
.
(va +r)
Investors receiving a
negative signal prefer to attack peg 1 while investors receiving a positive signal prefer to
attack peg 2.18 Hence, when BRR <
(va −r)
S
(va +r)
the optimal strategy is given by
( W , 0)
c
y(xan , BRR , S, va /r, W ) =
(α Wc , (1 − α) Wc )
(0, W )
if xan < 0
(27)
if xan = 0
if xan > 0
c
The intuition is simple. When signals are very noisy relatively to BRR (i.e.
(va −r)
)
(va +r)
BRR
S
<
the probabilities of collapse among investors are sufficiently high to induce them
to keep attacking one of the two pegs.
If BRR gets less noisier relatively to BRR ,
BRR
S
∈
(va −r)
,
1
, individuals with signals
(va +r)
close to zero prefer to defend rather than attack a peg. When
BRR
S
=
(va −r)
(va +r)
there is a
discontinuity in the optimal investment strategy. At this point a marginal investor assigns
a probability p1 (xan (j) = 0) = p2 (xan (j) = 0) =
r
va +r
<
2r
va +r
and no longer find optimal to
1
2r
a −r)
In fact, since BSRR < (v
(va +r) < 1 then p1 = p2 < 2 and p1 + p2 > va +r .
18
From equation (6), peg 1 is attacked if p1 > p2 and p1 + p2 > va2r+r . From equations (17) and (19)
we can show that p1 > p2 if xa (j) < 0 and p1 ≤ p2 if xa (j) > 0 (see Panel B in Figure 4). Also, we can
17
θT
−θ T
show that p1 + p2 = an,1 S an,2 + 1 = 1 − BSRR . Since
attacked when investors receive a negative signal.
24
BRR
S
<
(va −r)
(va +r)
then p1 + p2 >
2r
va+r .
Then, peg 1 is
attack both regimes but instead to defend them (see Panel B in Figure 8).19 Furthermore,
The switch in the optimal investment strategy is not restricted to the marginal investor.
Agents with a moderately positive signal, that is xan (j) ∈ (0, BRR
−
2
S
2
2r
S)
va +r
+
prefer to
defend peg 1 instead of attacking peg 2, while those with a moderately negative signal,
+
that is xan ∈ [− BRR
2
S
2
−
2r
S, 0],
va +r
prefer to defend peg 2 instead of attacking peg
1.20 Investors with a signal sufficiently far from zero do not have a switch in the optimal
strategy and they still prefer to attack one of the two regimes as before.21
As long as
BRR
S
∈ [ vvaa −r
, 1] the optimal strategy, illustrated in Panel B in Figure 8 and
+r
Panel A in Figure 9, is given by investors either defending or attacking one of the two
pegs
( Wc , 0)
(0, − Wc )
y(xan , BRR , S, va /r, W ) =
(−α Wc , −(1 − α) Wc )
(− Wc , 0)
(0, W )
c
if xan < − BRR
+
2
S
2
−
2r
S
va +r
if xan ∈ [− BRR
+
2
S
2
−
2r
S, 0]
va +r
S
2
+
2r
S]
va +r
if xan = 0
if xan ∈ [0, BRR
−
2
if xan >
BRR
2
−
S
2
+
2r
S
va +r
(28)
When
BRR
S
> 1, the marginal investor and those receiving a signal close to zero assign
a probability of zero to the event of having a collapse on either one of the two pegs and
they find optimal to defend both pegs (see Panel B in Figure 9). As before, investors
receiving moderately positive or negative signals prefer to defend only one of the two
regimes, while those receiving large positive or negative signals prefer to attack one of the
19
From equation (6) we know that both pegs are defended if p1 = p2 and p1 + p2 ≤
BRR
S
2r
va +r .
At xan (j) = 0
(va −r)
(va +r) .
both conditions hold as long as
≥
So, investors randomize long positions across markets. The
magnitude of the discontinuity changes with the structure of the payoffs vra . If vra → ∞ the discontinuity
vanishes while if vra → 1 the discontinuity reaches the maximum possible range of xan ∈ [− S2 , S2 ] given
the one-way bet assumption va > r.
20
The optimal strategy can be derived noting that for moderately positive signals we have p1 < p2 with
BRR
S
2r
a −r)
p1 + p2 = 1 − BSRR < va2r+r if BSRR ≥ (v
(va +r) and xan (j) ∈ (0, − 2 + 2 ) or with p1 + p2 = p2 < va +r
instead if
BRR
S
≥
(va −r)
(va +r)
and xan (j) ≥ − BRR
2 +
S
2.
Then it is optimal to defend peg 1. For moderately
S
negative signals, we have p1 > p2 and p1 + p2 = 1 − BSRR < va2r+r if xan ∈ ( BRR
2 − 2 , 0)
(v
−r)
BRR
S
a
or with p1 + p2 = p1 ≤ va2r+r if instead xan < BRR
2 − 2 and S ≥ (va +r) . Then it is
and
BRR
S
≥
(va −r)
(va +r)
optimal to defend
peg 2.
21
For large positive signals (xan > BRR
− S2 + va2r+r S), p1 < p2 if p1 + p2 = p2 > va2r+r so it is
2
S
2r
optimal to attack peg 2. For large negative signals (xan < − BRR
2 + 2 − va +r S) we have p1 > p2 with
p1 + p2 = p1 > va2r+r and it is optimal to attack peg 1.
25
regimes. The optimal strategy is given by22
( Wc , 0)
(0, − Wc )
y(xan , BRR , S, va /r, W ) =
(−α Wc , −(1 − α) Wc )
(− Wc , 0)
(0, W )
c
if xan < − BRR
+
2
S
2
−
2r
S
va +r
if xan ∈ [− BRR
+
2
S
2
−
2r
S, − BRR
va +r
2
if xan = [− BRR
+ S2 , BRR
− S2 ]
2
2
if xan ∈ [ BRR
− S2 , BRR
−
2
2
if xan >
BRR
2
−
S
2
+
S
2
+
2r
S]
va +r
2r
S
va +r
(29)
The optimal strategy can be derived noting that p1 = p2 = 0 and p1 + p2 = 0 for xan ∈ [− BRR
2 +
S BRR
S
2r
− S2 ], p1 = 0 with p2 ∈ [0, va2r+r ] (p1 + p2 ≤ va2r+r ) for xan ∈ [ BRR
−
,
−
+
S]
and
2
2
2
2
va +r
BRR
2r
2r
S
2r
p1 = 0 with p2 > va +r (p1 + p2 > va +r ) for xan > 2 − 2 + va +r S.
22
S BRR
2, 2
26
+ S2 ]
T
T
and
< θn,2
Figure 8: Optimal Strategies When θan,1
Attack Peg 1
p1
−r
∈ [0, vvaa +r
].
Attack Peg 2
Attack Peg 1
p1< p2 and p1+p2>2r/(va+r)
p1>p2 and p1+p2>2r/(va+r)
p1, p2
p1>p2 and p1+p2>2r/(va+r)
BRR
S
p2
1
Attack Peg 2
p1, p2
Defend
Peg 2
p1
Defend
Peg 1
p1< p2 and p1+p2>2r/(va+r)
p2
1
27
1/2
1/2
2r/(va+r)
½ (1-BRR/S)
θTan,1-S/2
θTan,1 θTan,2- S/2
0
θTan,1+S/2 θTan,2
½ (1-BRR/S) = r/(va+r)
θTan,2+ S/2
xan
θTan,1-S/2
θTan,1 θTan,2- S/2
=S[-r/(va+r)]
Panel A:
BRR
S
<
va −r
.
va +r
0
θTan,1+S/2 θTan,2
θTan,2+ S/2
=S[r/(va+r)]
Panel B: A Discontinuity When
BRR
S
=
va −r
.
va +r
xan
T
T
and
< θn,2
Figure 9: Optimal Strategies When θan,1
Attack Peg 1
Attack Peg 2
Attack Peg 1
p1< p2 and p1+p2>2r/(va+r)
p1>p2 and p1+p2>2r/(va+r)
p1, p2
Defend
Peg 2
p1>p2 and p1+p2>2r/(va+r)
p1
Defend
Peg 1
BRR
S
p2
1
p1
∈ ( vvaa −r
, 1).
+r
Defend
Peg 2
p1, p2
Attack Peg 2
Defend
Peg 1
p1< p2 and p1+p2>2r/(va+r)
p2
1
28
1/2
1/2
2r/(va+r)
2r/(va+r)
½ (1-BRR/S) < r/(va+r)
θTan,1-S/2
θTan,1
θTan,2- S/2
0 θTan,1+S/2
θTan,1+S/2 – S[2r/(va+r)]
Panel A:
BRR
S
θTan,2
θTan,2-S/2 +S[2r/(va+r)]
−r
∈ ( vvaa +r
, 1).
θTan,2+ S/2
xan
θTan,1-S/2
θTan,1
θTan,2- S/2= 0 = θTan,1+S/2
θTan,1+S/2 – S[2r/(va+r)] = – S[2r/(va+r)]
Panel B:
BRR
S
θTan,2
θTan,2-S/2 +S[2r/(va+r)] = S[2r/(va+r)]
= 1.
θTan,2+ S/2
xan
T
T
and
< θn,2
Figure 10: Optimal Strategies When θan,1
Attack Peg 1
p1>p2 and p1+p2>2r/(va+r)
Defend
Peg 2
p1, p2
p1
Defend
Peg 1
BRR
S
> 1.
Attack Peg 2
p1< p2 and p1+p2>2r/(va+r)
p2
1
Defend Defend
Both Pegs Both Pegs
1/2
2r/(va+r)
θTan,1-S/2
θTan,1
θTan,1+S/2
θTan,1+S/2 – S[2r/(va+r)]
θTan,2
θTan,2- S/2
xan
θTan,2+ S/2
θTan,2-S/2 +S[2r/(va+r)]
It follows from the optimal strategies that except for the discontinuity at BRR =
va −r
S, the net aggregate demand the regime i faces at the threshold is increasing in
va +r
BRR
y i (θan =
T
θan,i
, BRR /S, W )
Z
T
θan,i
+ S2
=
y s (xan , BRR , S, va /r, W )dxan
T
θan,i
− S2
RR W
( 12 + B2S
)c
va −r W
=
−
va +r
c
va −r W
va +r
c
29
1
2
−
BRR
2S
W
c
if
BRR
S
<
if
BRR
S
∈
h
if BSRR > 1
va −r
va +r
va −r
va +r
i
,1
(30)
while the level of fundamentals is decreasing in BRR ,
θiT
S BRR BRR
√
√
= θl −
= θl −
2 2
2 2 S
(31)
The aggregate demand can be obtained by computing directly the integral on equation
(30) using the optimal strategies presented in equations (27), (28) and (29) or using
instead the property that the distribution of beliefs on the collapse of peg i is uniform at
the threshold.23
The aggregate demand is increasing in
BRR
S
h i
−r
in the range 0, vvaa +r
because the pro-
portion of the population attacking peg i is increasing in BSRR .24 Net aggregate demand
−
BRR
W
va −r
a
reaches the maximum of vav+r
when
→
. At the point of the discontic
S
va +r
−r
, the net demand drops by - va2r+r Wc since a var+r percentage of
nuity BSRR = vvaa +r
r
the population switches from attacking i towards defending j and an additional va +r
percentage of the population switches from attacking j towards defending i (see Panel
i
BRR
va −r
B in Figure 8). For S ∈ va +r , 1 further increases in BSRR increases net aggregate
demand since the percentage of the population defending i decreases while the percentage
defending j increases (see Panels A and B in Figure 9). Once
BRR
S
> 1 net aggregate
demand is constant. At this point, investors are sure the regime j is going to remain
while the probability of collapse of i is uniform in the population, so that a fraction
of the population prefer to defend peg 2 while the rest (a fraction
va −r
)
va +r
2r
va +r
prefer to attack
i (see Figure 10).
Next, we show that for any θl ≥
W
2c
there is an equilibrium where one or the two pegs
are defended or one of the two regimes is attacked. Figure 11 presents the net aggregate
demand from equation (30) and the fundamental line from equation (31) for different
23
When
BRR
S
<
va −r
va +r
, we know that at xan = 0 pi = p2 = pe =
1
2
RR
− B2S
>
r
va +r
and that all investors
with pi > pe would be attacking peg i. It follows that at the threshold there is a proportion of (1 − pei )
W
attacking
i and a proportion pei attacking j, so that the net aggregate demand equals (1 − pei ) c . When
BRR
S
∈[
va −r
va +r
, 1] we know that pe =
1
2
−
BRR
2S
≤
r
va +r .
Therefore, investors with a pi larger than
2r
va +r
attack i, those with pi ∈ (e
p, va2r+r ] defend j and those with pi < pe defend i. It follows that there is a
proportion (1 − va2r+r ) = vvaa −r
e defending it. Then the aggregate demand
+r attacking i and a proportion p
BRR
va −r W
W
on peg i is va +r c − pe c . When S > 1, individuals with pi larger than va2r+r attack i while those
W
with pi ∈ (0, va2r+r ] defend regime j. The aggregate demand on peg i is just vvaa −r
+r
c .
24
See Panel A in Figure 8. Note that both probabilities intersect at xan = 0 where both are equal to
− BRR
1
. When BSRR → vvaa −r
, 12 1 − BSRR falls and 1 − 12 1 − BSRR = 12 1 + BSRR rises.
2 1− S
+r
30
values of θl . Using the fact that the intercept of the fundamentals level line is given by
θl , it is straightforward to note that an equilibrium exists for any θl >
W
.
2c
Furthermore,
the discontinuity in the aggregate demand ensures that multiple equilibria exists in the
va −r S va W va −r S 25
W
+ va +r 2√2 , va +r c + va +r 2√2 ].
range θl ∈ [ vvaa−2r
+r
c
T
Figure 11: Deriving the Equilibrium for θan,1
< 0 with a Region Where Both Pegs Remain
Fundamental Level Lines
θl= ((va-r)/(va+r))W/c +S/23/2
θl= (va/(va+r))W/c +
S/23/2 ((va-r)/(va+r))
(va/(va+r))W/c
Aggregate Net Demand B/S > 1
θl= ((va-2r)/(va+r))W/c +
S/23/2 ((va-r)/(va+r))
((va-r)/(va+r))W/c
yi =
W/2c
((va-2r)/(va+r))W/c
Aggregate Net Demand
B/S <
Aggregate Net Demand B/S Є
yi=
[
,1
]
yi =
B/S
(0,0)
1
Formally, there is a set of θl , which includes at least all θl >
W
,
2c
for which a threshold
equilibria exist where both pegs may remain.26 The thresholds θiT in equilibrium are equal
v −r S W
If vvaa−2r
+ vaa +r 2√2 > W
+r
c
2c there are two different equilibria in this range where both pegs
may remain. If instead the previous inequality does not hold then there is an equilibrium where both pegs
v −r S
W
might remain (RR) and one where both pegs may collapse (CC) for θl ∈ [ vvaa−2r
+ vaa +r 2√2 , W
+r
c
2c ]
va
va −r
W
S
√
and two different equilibria in the range θl ∈ [ W
2c , va +r
c + va +r 2 2 ] where both pegs may remain
25
(RR).
26
The fact that the optimal strategy for peg 1 (peg 2) of equation (28) is not weakly decreasing
(increasing) in the whole range xan implies that additional requirements are needed to ensure the existence
of an equilibria when a threshold solution exists for negative values of θl . Such technical restrictions are
not needed for positive values of θl since in the region where xan is not weakly decreasing (increasing)
the net aggregate demand is bounded below by zero, so that a positive θl ensures that the peg 1 (peg 2)
T
T
).
remains whenever θan > θan,1
(θan < θan,2
31
to
θiT =
W
2c
S
W
+ √
2c
2 2
(θl +
M in
S
√
)
2 2
W
2c
W
S
+ √
2c
2 2
(θl +
if θl ∈
va −3r
va +r
S
√
2 2
),
va −r
va +r
W
c
h
W
, va
2c va +r
W
c
+
va −r
va +r
S
√
2 2
i
if θl ∈ Γl
(32)
for i = 1, 2. Where
h
i
va −2r W
va −r
S
√
+
,
∞
otherwise
va +r vca −7r Wva +r 4r2 2 S Γl =
( )−( va +r ) 2√2
va −2r W
S
L
√
√
θl,RR
= va +r 2c
<
−
,
∞
if
2 2 W
va +r
c
2
+2
S ( 2c )
(33)
or equivalently,
W
2c
h
S
W
√
(θ
+
)
if
θ
∈
, va
−i
−i
W
2c va +r
2
+ √S
2c
2
θiT =
W
v
−3r
S
v
−r
a
a
2c
M in W √S (θ−i + v +r √ ), v +r Wc
if θ−i ∈ Γ−i
2
+
a
a
2c
W
c
+
va −r
va +r
S
√
2
i
2
(34)
for i = 1, 2. Where
h
i
va −2r W
va −r √
S
+
,
∞
otherwise
c
va +r
2
Lva +r
v
−3r
W
W
S
S
Γ−i
+ √ + √ ( va +r ) 2c
θ
2
2 2
a
S
va −2r W
√
l,RR 2c W
,
∞
if
<
−
va +r
c
2
+ √S
2c
(35)
2
A proof of this result is included in the Appendix. Figure 12 shows how these equilibria looks like in the space of fundamentals (θ1 , θ2 ). To derive the currency equilibria
graphically we first construct two “large support lines” parallel and equidistant to the 450
line with a total distance among them equal to S. Next, we construct two “small support lines”that are also parallel and equidistant to the 450 line but the distance between
−r
them is only vvaa +r
S. Then, to build the equilibrium based on the first equation of the
aggregate demand on equation (30), we graph a line from the point ( W
, W ) to the point
2c 2c
W
a
of intersection of θ1 = vav+r
and the upper small support line. In order to graph the
c
equilibrium, based on the second equation of the aggregate demand, we graph a line from
W
the point of intersection of the upper small support line and θ1 = vvaa−2r
to the point
+r
c
W
of intersection of the upper large support line and θ1 = vvaa −r
. The equilibrium based
+r
c
on the third equation can be built plotting a vertical line above this last point of inter-
32
section. Finally, we graph the mirror image along the 450 line of the three lines described
above. The shaded area is the region where multiple equilibria can be obtained.
Thresholds in Figure 12 are composed of three segments. The first segment of θiT is
an upward sloping line from the point θ−i =
W
2c
to the point θ−i =
va W
va +r c
−r √
S
+ vvaa +r
which
2
is based on the first equation of the net aggregate demand (equation 30). The second
segment, based on the second equation of the net aggregate demand, is also an upward
sloping but now from the point θ−i =
va −2r W
va +r c
S
√
to the point θ−i =
+ vvaa −r
+r 2
va −r W
va +r c
+ √S2 . As
expected, these two segments indicate that if fundamentals of economy −i improve then
the threshold for peg i, θiT , rises and this in turn makes more difficult to maintain peg
i. The third segment is just a vertical (horizontal) line for θ1T (θ2T ). This third segment
does not increase with θ−i due to the fact that once θ−i ≥
va −r W
va +r c
+
S
√
2
investors are sure
the regime −i is going to remain while the probability of collapse of i is uniform in the
population, so that a fraction
rest (a fraction
va −r
)
va +r
2r
va +r
of the population prefer to defend peg −i while the
prefer to attack i (see Figure 10).
T
< 0 with a Region Where Both Pegs Remain
Figure 12: Currency Equilibria for θan,1
θ2
θT1
θT1
θT2
θT2
θ1
(
(0,0)
)
S
33
4.3
States of the World That are Possible on Equilibria
In this section we analyze how information precision (S) affects the states of the world
that can be observed in equilibrium. The set of equilibria can be summarized by equations
(25), (32) and (33).27 The set of states of the world that are possible depends on how
precise the private information is. On the one hand, if the support of the noise S is finite,
there are up to 6 states of the world (see Figure 13): (i) Both collapse; (ii) Both may
collapse; (iii) The weakest collapses while the strongest may remain; (iv) Only the weakest
collapses; (v) The weakest may collapse while the strongest remains; and (vi) Both pegs
remain. Figure 13 presents the location of all states by putting together Figures 7 and
12. On the other hand, if information is precise, S → 0, then there are only four states
that can be sustainable in equilibria. The reason is that when S → 0 the equilibrium can
be characterized with the following three equations
θT = 0
i
θiT → θl
θT → va −r W
i
va +r
c
if θl < 0
va
va +r
W
if θl ∈ (0,
]
c
W
if θl > [ vvaa −r
, ∞]
+r
c
(36)
for i = 1, 2.
Hence only 4 states –(i), (iv), (v) and (vi)– are possible in equilibria when information is accurate.28 Figure 14 shows the location of the four possible states of the world
when the private information is accurate. In the figure it is easy to notice how lack of
common knowledge and accurate private information generate a strong rank-order result
in the sense that an infinitesimal difference in the level of fundamentals can be sufficient to support an equilibrium where either “the weak peg collapses while the strong
one remains (iv)” or “the weak peg may collapse while the strong one remains for sure
(iv)”. This rank-order result is present in a large region of the world fundamentals. If
W
θl ∈ (0, vvaa −r
) then the weakest regime collapses while the strong one remains, while
+r
c
W
va
W
if instead θl ∈ ( vvaa −r
,
) then the weakest regime may collapse while the
+r
c
va +r
c
strong one remains for sure.
27
Or equivalently by equations (26), (34) and (35).
State (ii) vanishes directly as a result of S → 0 while state (iii) is ruled out by the fact that a threshold
solution in which both pegs may remain is not an equilibria when θl < 0 and S → 0 as expressed in
equations 32 and 33.
28
34
The exact characterization of the equilibria, provided in equation (36), depends on the
structure of the payoffs and the level of wealth. Furthermore, the region of fundamentals
where only the weakest regime collapses is strictly increasing in wealth, (W), no matter
how high the fundamentals of the weakest country are. This property is a direct result of
our initial assumption that it was always profitable to attack a peg (θp → ∞).
35
Figure 13: Characterization of the Equilibria when S is Finite
θT1
θ2
(iv)
θ2 = θ1 + ((va-r)/(va+r))S/21/2
W/c
(vi)
θ2 = θ1 - ((va-r)/(va+r))S/21/2
θT1
(v)
θT2
(v)
36
θT2
(ii)
(iii)
(iii)
(0,0)
θ1
W/c
(i)
(iv)
S
Figure 14: Characterization of the Equilibria when is Very Accurate (S → 0)
θ2
θT1
(vi)
W/c
(iv)
θ 1=
θ2
[va/(va+r)]W/c
θl = [va/(va+r)]W/c
W/2c
(v)
θT2
[(va-r)/(va+r)]W/c
[(va-2r)/(va+r)]W/c
θl = W/2c (i.e. θ2 = W/c - θ1)
(0,0)
θ1
W/c
W/2c
[va/(va+r)]W/c
(i)
[(va-r)/(va+r)]W/c
[(va-2r)/(va+r)]W/c
5
(iv)
Conclusions
Coming soon
References
Calvo, G. (1999): “Contagion in emerging markets: When Wall Street is a carrier,”
Mimeo.
Calvo, G. A., and E. G. Mendoza (2000): “Rational contagion and the globalization
of securities markets,” Journal of International Economics, 51(1), 79–113.
Gerlach, S., and F. Smets (1995): “Contagious speculative attacks,” European Journal of Political Economy, 11(1), 45–63.
Guimaraes, B., and S. Morris (2007): “Risk and wealth in a model of self-fulfilling
currency attacks,” Journal of Monetary Economics, 54(8), 2205–2230.
37
Kodres, L. E., and M. Pritsker (2002): “A Rational Expectations Model of Financial
Contagion,” Journal of Finance, 57(2), 769–799.
Krugman, P. (1979): “A Model of Balance-of-Payments Crises,” Journal of Money,
Credit and Banking, 11(3), 311–25.
Morris, S., and H. S. Shin (1998): “Unique Equilibrium in a Model of Self-Fulfilling
Currency Attacks,” American Economic Review, 88(3), 587–97.
(2000): “Global Games: Theory and Applications,” Cowles Foundation Discussion Papers 1275R, Cowles Foundation for Research in Economics, Yale University.
Obstfeld, M. (1996): “Models of currency crises with self-fulfilling features,” European
Economic Review, 40(3-5), 1037–1047.
Pavlova, A., and R. Rigobon (2005): “Wealth Transfers, Contagion, and Portfolio
Constraints,” NBER Working Papers 11440, National Bureau of Economic Research,
Inc.
38
6
Appendix A: Proof.
Proof of Equation (6).
The solution to the risk neutral problem can be characterized with the following statements:
(i) An investor prefers to attack peg i rather than defend it if and only if pi >
r
.
va +r
In
what follows we will call attack “the preferred action in the single country problem”
if and only if this inequality holds.
(ii) If attack i and attack j are the preferred actions in the single country problem then
attack i will be the solution to the investor problem if and only if pi > pj .
(iii) If defend i and defend j are the preferred actions in the single country problem then
defend i is the optimal action if and only if pi < pj .
(iv) If attack i and defend j are the optimal actions in the single country problem then
attack i is the solution to the investor problem if and only if pi > va2r+r − pj .
(v) If attack is the preferred action in both pegs and p1 = p2 then the investor is indifferent between attacking one peg or the other. In this case either pure or mixed
strategies may result from optimal behavior and the investor’s positions would be
given by (yi∗ , yj∗ ) = (α Wc , (1 − α) Wc ). Note that α is a random variable with support
in the interval [0, 1].
(vi) If defend is the preferred action in both pegs and p1 = p2 then (yi∗ , yj∗ ) = (−α Wc , −(1−
α) Wc )
Statement (i) follows from comparing the payoff of going long versus going short in
a single regime. Here, we imposed the innocuous assumption that when an investor is
indifferent between attacking or defending a peg she would defend it. Statements (ii)
and (iii) result from comparing long and short positions across markets. Statement (iv)
follows from comparing the payoffs of going short in i versus long in j. Statement (v)
results from the fact that the securities are perfect substitutes when the probability of a
profitable collapse is equal among countries.
39
Now we show that attack i is the solution if and only if pi + pj >
2r
va +r
and pi > pj .
In order to see this note that if these two equations holds then either (pi >
r
, pi
va +r
> pj ) or (pi >
r
, pj
va +r
≤
r
, pi
va +r
2r
)
va +2
+ pj >
r
, pj
va +r
>
must be true, so that in both cases
the solution to the investor problem is to attack i. The reverse argument is straightforward
since from statements (ii) and (iv) we know that either (pi >
(pi >
r
, pj
va +r
≤
r
, pi
va +r
+ pj >
2r
)
va +2
r
, pj
va +r
>
r
, pi
va +r
> pj ) or
must be true if attack i is the optimal solution,
being that both of these group of equations imply pi + pj >
2r
va +2
and pi > pj . Following an
identical argument, we can show that defend i will be the solution of the investor problem
if and only if pi + pj ≤
2r
va +2
and pi < pj .
Proof of the Property that the Distribution of Beliefs on the Collapse of Peg
T
.
i is Uniform in the Population When θan = θan,i
∗
Let δ1 (θan = θan,1
, p) denote the proportion of the population with p1 < p. Then,
δ1 (θan =
∗
θan,1
, p)
Z
1
1p1 (j)<p dj
=
0
Z
1
1Fλ (−λj )<p dj
i
h
= Eλ 1−λ<F −1 (p)
λ
h
i
= Eλ 1λ<F −1 (p)
=
0
λ
= Fλ (Fλ−1 (p)) = p
The second equality follows from the derivation of equation (17). The third equality follows from the law of large numbers while the fourth uses the fact that λ has the same
∗
distribution as -λ. The proof that δ1 (θan = θan,2
, p) = p2 is simpler.
Proof of the Symmetry of the Thresholds.
The aggregate demand of currency i when the realization of the fundamentals is θan is
40
given by
T
T
y si (θan , θan,1
, θan,2
, S)
Z
=
1
yi∗ (j)dj
0
T
T
= E[yi∗ (p1 (xan , θan,1
, S), p2 (xan , θan,2
, S), va /r, W )]
Z S
2
T
T
=
yi∗ p1 (θan + λ, θan,1
, S), p2 (θan + λ, θan,2
, S), va /r, W dλ
− S2
The second equality uses the law of large numbers and the third takes the expectations
with respect to the random variable λ. Using the last line we can compute the aggregate
demand of each regime at its threshold and show they are equal,
Z 1
s T
T
T
y 1 (θan,1 , θan,1 , θan,2 , S) =
y1∗ (j)dj
0
!
!
!
Z S
S
T
T
S
2
)
−
θ
+
(θ
λ
+
−
λ
an,2
an,1
2
=
y1∗ T 2
,T
, va /r, W dλ
S
S
S
−2
!
!
!
Z S
S
T
T
S
2
)
−
θ
+
(θ
λ
+
−
λ
an,2
an,1
2
=
y2∗ T
,T 2
, va /r, W dλ
S
S
S
−2
!
!
!
Z S
S
T
T
S
2
)
−
θ
−
λ
+
(θ
λ
+
an,2
an,1
2
y2∗ T 2
,T
, va /r, W dλ
=
S
S
S
−2
T
T
T
= y s2 (θan,2
, θan,1
, θan,2
, S)
The third equality uses the symmetry on the solution of the investor problem and fourth
is just a change of variables in the integral such as z = −λ. It follows that the net currency
demand at the thresholds are equal and if an equilibrium exist it must be true that the
threshold levels are also equal, proving our statement.
Proof of the Existence of Equilibrium Where Both Pegs May Collapse (i.e. if
T
θan,1
> 0).
Equations (23) and (24) deliver equation (25), while the following equation,
T
θan,i
BCC
S BCC
)
θiT = θl + √ (1 − 2 ∗ 1i=2 ) = θ−i + √ = θ−i + √ (
2
2
2 S
(37)
and equation (24) deliver the solution in terms of θ−i as in equation (26).
In order to show that equations (25) and (26) are indeed an equilibrium we need to
41
T
show that net aggregate demand is larger than the fundamentals only when θan < θan,1
T
) for country 1 (country 2). This condition follows from the facts that for
(θan > θan,2
country 1 (country 2) fundamentals are increasing (decreasing) in θan ,
θan
θi = θl + √ (1 − 2 ∗ 1i=2 )
2
(38)
while net aggregate demand is weakly decreasing (increasing) in θan ,
y si (θan , BCC /S, W )
Z
θan + S2
=
y s (xan , BCC , S, va /r, W )dxan
(39)
θan − S2
since the optimal strategy of the individual investor given by equations (20) and (21) is
weakly decreasing (increasing) in xan .
Proof of the Existence of Equilibrium Where Both Pegs May Remain (i.e. if
T
θan,1
< 0).
The threshold solutions of equation (32) follow from solving the first part of the aggregate demand on equation (30) and the fundamentals line of equation (31). These threshold
solutions are indeed an equilibrium since the optimal strategy of equation (27) is weakly
decreasing (increasing) everywhere in xan for peg 1 (peg 2). The threshold solution on
equation (34) nests the solution of the second and third part of the aggregate demand
and the fundamentals line. Since the optimal strategies of equations (28) and (29) are not
weakly decreasing (increasing) everywhere for peg 1 (peg 2) we need to corroborate that
a peg would collapse only when the fundamentals are weaker than the threshold solution.
In those cases where θl is positive the corroboration exercise is straightforward. If
BRR ≤ S the net aggregate demand is weakly decreasing (increasing) in the range
θan ∈ [−∞, S2 ] (θan ∈ [− S2 , ∞]) for peg 1 (peg 2) and the solution will be well defined
in this range. When θan =
S
2
(θan = − S2 ) investors are either defending 1 or attacking
2 (defending 2 or attacking 1) so that aggregate demand is negative. Further increments (decrements) in θan may increase net aggregate position but this will always be
bounded below by zero. It follows that a positive level of fundamentals when θan =
S
2
(θan = − S2 ) is sufficient to guarantee that the threshold solution is indeed an equilibria.
Since θ1 = θl +
θ√
an
2
(θ2 = θl −
θ√
an
)
2
is always positive when θan =
S
2
the result follows. If
instead BRR > S we know at the threshold there are only two types of investors. Those
42
T
attacking the peg and those defending the other peg. For θan < θan,1
the demand is weakly
T
we can show that the peg remains
decreasing and the regime collapses. For θan > θan,1
using an auxiliary strategy. Let us define the auxiliary strategy as the optimal strategy
with the only exception that when p1 = p2 = 0 investors arbitrarily set y1 = y2 = 0. The
net demand at the threshold is equal using either the optimal or the auxiliary strategy
so that the threshold solution holds using either one of them. On the other hand the
net aggregate demand using the optimal strategy is bounded above by the one you would
T
obtain using the auxiliary strategy so that if the peg remains for θan > θan,1
using the
auxiliary strategy it must also remain using the optimal strategy. But showing that the
peg remains with the auxiliary strategy is trivial since demand would be weakly decreasing (increasing) for peg 1 (peg 2) in the range θan ∈ [−∞, S2 ] (θan ∈ [− S2 , ∞]) and the
fundamentals for peg 1 (peg 2) would be positive when θan =
S
2
(θan = − S2 ) so that the
peg must remain by those same arguments we used when BRR ≤ S
In what follows it will be useful to note that a threshold solution with BRR ≥ S only
exists for positive values of θl since the lowest value with such type of solution is given by
W
S
θl = vvaa −r
+ 2√
> 0. Then when θl is negative and a threshold solution with RR as
+r
c
2
an intermediate state exists we know that BRR < S and we can easily compute the net
aggregate demand when θan > S2 ,
h
i
h
i
2r
W
S BRR
2r − θan − BRR
− c if θan ∈ 2 , 2 + va +r S
va +r
2
2S
0
if θan > BRR
+ va2r+r S
2
Since the net aggregate demand is well behaved for peg 1 in the range xan ∈ (−∞, S2 ]
we know that the average level of fundamentals is larger than the net aggregate demand
when θan = 0 if a threshold solution exists. This fact, together with the functional form of
the aggregate demand of peg 1 above, implies that if a threshold solution exists a necessary
condition for not being an equilibrium is that the level of fundamentals becomes lower
than the net aggregate demand at the point θan =
BRR
2
+
2r
S,
va +r
since the slope of the
aggregate would have to be larger that the slope of fundamentals line. It follows that a
necessary and sufficient condition for a threshold solution to be an equilibria is that the
level of fundamentals is larger than zero at the point θ1 = θl + θ√an2 |θ
an =
BRR (θl )
+ v 2r+r S
2
a
. Since
L
the solution of BRR (θl ) is increasing in θl this solution tells us that if a θl,RR
exists where
43
θ1 = θl +
BRR (θl )
√
2 2
+
2r
va +r
S
√
| L
2 θl =θl,RR
= 0 then it must be the case that the threshold
L
solution would be an equilibria if and only if θl > θl,RR
. It also tells us that such condition
would be binding if and only if the lowest level of θl for which a threshold solution exists
is not an equilibria. That is if
S
BRR (θl )
2r
√
√ |θl =( va −2r ) W +( va −r ) √S
θ1 = θl +
+
va +r
c
va +r 2 2
va + r
2 2
2
S
va − 2r W
+√ <0
=
va + r
c
2
as expressed in equation (33). A symmetrical argument applies for peg 2. The proof for
equations (34) and (35) follow identical steps, using the equation,
T
2θan,i
BRR
S BRR
θiT = θ−i + √ (1 − 2 ∗ 1i=2 ) = θ−i − √ = θ−i − √ (
)
2
2
2 S
instead of the fundamental line of equation (31).
44