John The Ripper
advertisement
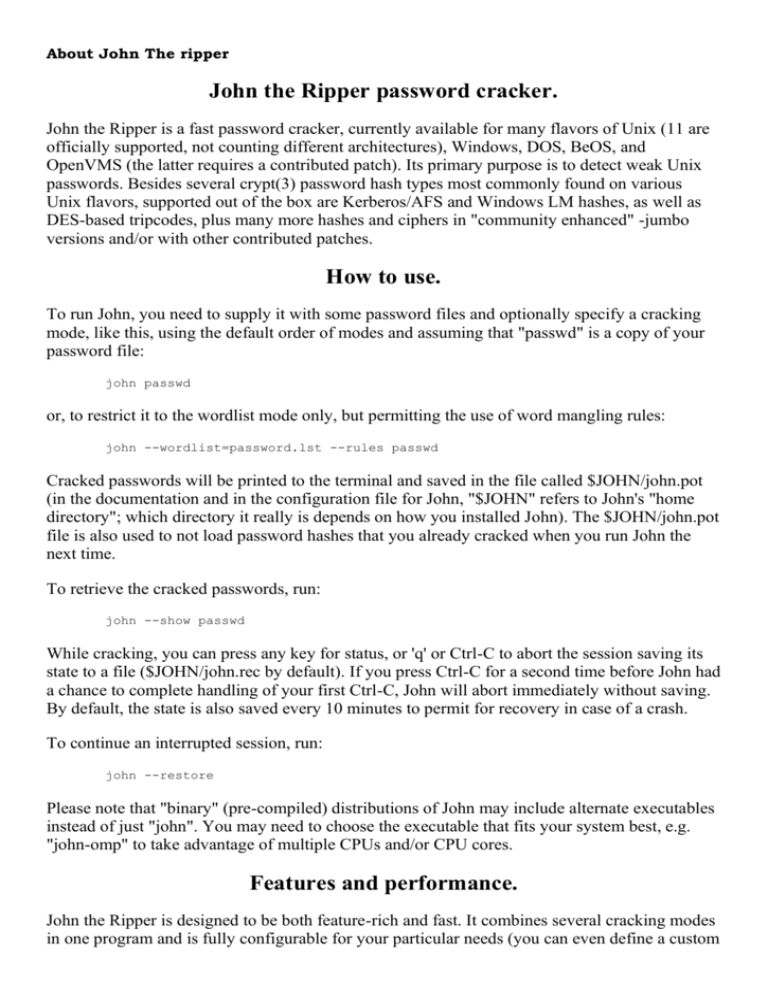
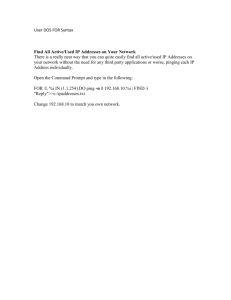
About John The ripper John the Ripper password cracker. John the Ripper is a fast password cracker, currently available for many flavors of Unix (11 are officially supported, not counting different architectures), Windows, DOS, BeOS, and OpenVMS (the latter requires a contributed patch). Its primary purpose is to detect weak Unix passwords. Besides several crypt(3) password hash types most commonly found on various Unix flavors, supported out of the box are Kerberos/AFS and Windows LM hashes, as well as DES-based tripcodes, plus many more hashes and ciphers in "community enhanced" -jumbo versions and/or with other contributed patches. How to use. To run John, you need to supply it with some password files and optionally specify a cracking mode, like this, using the default order of modes and assuming that "passwd" is a copy of your password file: john passwd or, to restrict it to the wordlist mode only, but permitting the use of word mangling rules: john --wordlist=password.lst --rules passwd Cracked passwords will be printed to the terminal and saved in the file called $JOHN/john.pot (in the documentation and in the configuration file for John, "$JOHN" refers to John's "home directory"; which directory it really is depends on how you installed John). The $JOHN/john.pot file is also used to not load password hashes that you already cracked when you run John the next time. To retrieve the cracked passwords, run: john --show passwd While cracking, you can press any key for status, or 'q' or Ctrl-C to abort the session saving its state to a file ($JOHN/john.rec by default). If you press Ctrl-C for a second time before John had a chance to complete handling of your first Ctrl-C, John will abort immediately without saving. By default, the state is also saved every 10 minutes to permit for recovery in case of a crash. To continue an interrupted session, run: john --restore Please note that "binary" (pre-compiled) distributions of John may include alternate executables instead of just "john". You may need to choose the executable that fits your system best, e.g. "john-omp" to take advantage of multiple CPUs and/or CPU cores. Features and performance. John the Ripper is designed to be both feature-rich and fast. It combines several cracking modes in one program and is fully configurable for your particular needs (you can even define a custom cracking mode using the built-in compiler supporting a subset of C). Also, John is available for several different platforms which enables you to use the same cracker everywhere (you can even continue a cracking session which you started on another platform). Out of the box, John supports (and autodetects) the following Unix crypt(3) hash types: traditional DES-based, "bigcrypt", BSDI extended DES-based, FreeBSD MD5-based (also used on Linux and in Cisco IOS), and OpenBSD Blowfish-based (now also used on some Linux distributions and supported by recent versions of Solaris). Also supported out of the box are Kerberos/AFS and Windows LM (DES-based) hashes, as well as DES-based tripcodes. When running on Linux distributions with glibc 2.7+, John 1.7.6+ additionally supports (and autodetects) SHA-crypt hashes (which are actually used by recent versions of Fedora and Ubuntu), with optional OpenMP parallelization (requires GCC 4.2+, needs to be explicitly enabled at compile-time by uncommenting the proper OMPFLAGS line near the beginning of the Makefile). Similarly, when running on recent versions of Solaris, John 1.7.6+ supports and autodetects SHA-crypt and SunMD5 hashes, also with optional OpenMP parallelization (requires GCC 4.2+ or recent Sun Studio, needs to be explicitly enabled at compile-time by uncommenting the proper OMPFLAGS line near the beginning of the Makefile and at runtime by setting the OMP_NUM_THREADS environment variable to the desired number of threads). John the Ripper Pro adds support for Windows NTLM (MD4-based) and Mac OS X 10.4+ salted SHA-1 hashes. "Community enhanced" -jumbo versions add support for many more password hash types, including Windows NTLM (MD4-based), Mac OS X 10.4-10.6 salted SHA-1 hashes, Mac OS X 10.7 salted SHA-512 hashes, raw MD5 and SHA-1, arbitrary MD5-based "web application" password hash types, hashes used by SQL database servers (MySQL, MS SQL, Oracle) and by some LDAP servers, several hash types used on OpenVMS, password hashes of the Eggdrop IRC bot, and lots of other hash types, as well as many non-hashes such as OpenSSH private keys, S/Key skeykeys files, Kerberos TGTs, PDF files, ZIP (classic PKZIP and WinZip/AES) and RAR archives. Unlike older crackers, John normally does not use a crypt(3)-style routine. Instead, it has its own highly optimized modules for different hash types and processor architectures. Some of the algorithms used, such as bitslice DES, couldn't have been implemented within the crypt(3) API; they require a more powerful interface such as the one used in John. Additionally, there are assembly language routines for several processor architectures, most importantly for x86-64 and x86 with SSE2. The Process JTR. Winzip. In unix type tar -xzf john-1.6.tar.gz 'command' (no quotes) and press enter. You with me? Good. Go to whatever directory to have JTR in. Type 'john' and press enter. A whole list of options will come up: John the Ripper Version 1.6 Copyright (c) 1996-98 by Solar Designer Usage: /WINDOWS/DESKTOP/JTR/JOHN-16/RUN/john [OPTIONS] [PASSWORDFILES] -single "single crack" mode -wordfile:FILE -stdin wordlist mode, read words from FILE or stdin -rules enable rules for wordlist mode -incremental[:MODE] incremental mode [using section MODE] -external:MODE external mode or word filter -stdout[:LENGTH] no cracking, just write words to stdout -restore[:FILE] restore an interrupted session [from FILE] -session:FILE set session file name to FILE -status[:FILE] print status of a session [from FILE] -makechars:FILE make a charset, FILE will be overwritten -show show cracked passwords -test perform a benchmark -users:[-]LOGIN|UID[,..] load this (these) user(s) only -groups:[-]GID[,..] load users of this (these) group(s) only -shells:[-]SHELL[,..] load users with this (these) shell(s) only -salts:[-]COUNT load salts with at least COUNT passwords only -format:NAME force ciphertext format NAME (DES/BSDI/MD5/BF/AFS/LM) -savemem:LEVEL enable memory saving, at LEVEL 1..3 You wont need most of these options. In fact, you don't really need any of these options. You can simply type 'john[filename]'. The filename must include the .txt extension. This is the regular crack. It will use bruteforce to decrypt all of the passwords in the file. If you're an impatient ass you can use a word list. This is not as effective but it's quicker (more on that later). How to make a crackable file: Let's say that for some reason you have a DES encrypted password but no file. If you want to crack it (why else would you be here?) you need to make your own file. Just create a text file and paste in the password. Now put a username (just any old name will do) in front of it with a colon separating the two. It should look something like this: User:gyuJo098KkLy9 Save the file as crackme.txt (just an example) and go to the prompt and type 'john crackme.txt' (no quotes obviously). Now you just have to wait. Options Here are a list of the options and what they do. includes only a few rules and a small wordlist. Usage: john -single crackme.txt word in the list until it finds a match or you reach the end of the list. This is quicker than the default (bruteforce) attack, but I don't recommend this because it doesn't always find a match. More notes on wordlists below. Usage: john -wordfile:password.lst crackme.txt want to use this option I wont help you. Ok, ok, I'm just lazy. Shoot me. under certain modes. Usage: john -incremental:alpha crackme.txt (only letters) john -incremental:digits crackme.txt (only numbers) john -incremental:lanman crackme.txt (letters, numbers, and some special characters) john -incremental:all crackme.txt (all characters) ess with it. Basically this calls the options that are defined in the configuration settings. You can change these yourself, but I wouldn't recommend it unless you know what you're doing. No, I wont tell you how, go away. Usage: john -external:[MODE] crackme.txt (replace MODE with whatever the name of your mode is). A file will be created in the JTR directory named 'restore' (no quotes doofus, and yes, no file extention). You can start the crack back up from that restore point. If you used thesession option you probably have a different filename. Usage: john -restore:restore It allows you to create a new file that holds the data of your session. You can then restore your session later. Usage: john -session:[save to filename] crackme.txt -session option). Usage: john -status:[filename] any passwords have been cracked in a file and how many are left. Usage: john -show crackme.txt Usage: john -test Usage: john -users:User crackme.txt Usage: john -group:lamers crackme.txt Usage: john -shells:shelly crackme.txt Usage: john -salts:2 crackme.txt the most widely used one). Use this to force JTR to try a certain format. Usage: john -format:DES crackme.txt (force DES) john -format:BSDI crackme.txt (force BSDI) john -format:MD5 crackme.txt (force MD5) john -format:BF crackme.txt (force BF) john -format:AFS crackme.txt (force AFS) john -format:LM crackme.txt (force LM) level you specify from one to three. Usage: john -savemem:1 crackme.txt (save at level 1) john -savemem:2 crackme.txt (save at level 2) john -savemem:3 crackme.txt (save at level 3) How to use a wordlist with JTR: I'll assume you already have a wordlist in the JTR directory (it comes with password.lst, if you want to make your own I'll tell you how later). Go to the prompt and type 'john -wordfile:password.lst crackme.txt' (no quotes, damnit). If the password is in the wordlist, it will work. Otherwise, you deserve it for using a wordlist when you have bruteforce capabilities, shame on you. How to create a wordlist to use with JTR: First I will include a few lines of the wordlist supplied with JTR: #!comment: Common passwords, compiled by Solar Designer. 12345 abc123 password passwd 123456 How to use John The Ripper (Practical) JTR is a very useful and fast password cracking program. It is the favourite among hackers for cracking .htpasswd (DES) encrypted passwords and now can handle other encryptions such as LM and MD5. This is a very useful tool to have and is completely free too. This quick tutorial just shows you how to install and run it in standard mode. Starting JTR: This assumes that you are using Windows XP, however it is available for mac and linux operating systems. You can use terminal and the commands are usually the same: First of all download it and extract it to your C drive (C:\john1701) If you are using a newer version since the article has been written, just change the commands below to fit the new version name. Click start → run → and type cmd you should now have a black window on your screen. Keep typing: cd .. To go back directories until you are at your C drive. Then type: cd john1701\run And you should be in the folder containing JTR. Test this by typing: John-mmx You will now be greeted with the JTR welcome screen which will look similar to this: Ok, time to test it out. Get your encrypted file (if you don't have one, use this example: thisislegal:cGPV5pzv1OdLQ) and create a new file in the run folder called pass.txt and copy and paste your password string into the text file. Now, to run JTR in default mode all you have to do is type: john-mmx pass.txt And it should begin cracking the hash. You can hold space or any other key down to check its progress. Passwords 1-5 characters in length can be cracked in seconds. 6-7 can take around an hour depending on the password and longer than 7 can take a few days to crack. This tutorial is only going to cover cracking password in the default mode. Another good option though is the -wordlist option which allows you to try cracking the password using a wordlist. Just type john-mmx in cmd again and look at all the available options. When cracked, the password will be displayed on screen and john will exit. This screenshot below shows when JTR cracks the example password above: