Public-Key Cryptosystems Based on 3rd-Order
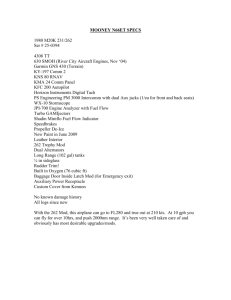
advertisement

Public-Key Cryptosystems Based on Cubic
Finite Field Extensions
Guang Gong* and Lein Harn
The Communication Sciences Institute
University of Southern California
Electrical Engineering Systems, EEB#500
Los Angeles, California 90089-2565, USA
Tel. (1- 213) 740 7332, Fax. (1-213) 740-8729
Email. guanggon@milly.usc.edu.
Department of Computer Networking
University of Missouri-Kansas City
Kansas City, Missouri 64110-2499, USA
Fax. (1-816) 235-5159 , Tel. (1-816) 235- 2367
Email: harn@cstp.umkc.edu
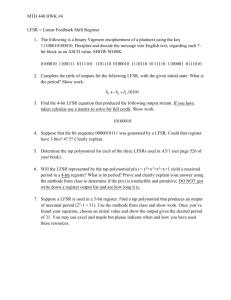
Abstract: The cryptographic properties of 3rd-order linear feedback shift register
(LFSR) sequences over GF(p) are investigated. A fast computational algorithm for
evaluating the kth term of a characteristic sequence of order 3 is presented. Based on these
properties, a new public-key distribution scheme and a RSA-type encryption algorithm
are proposed. Their security, implementation, information rate, and computational cost
for the new schemes are discussed.
Index words: Cubic finite field extension, linear feedback shift register sequence,
characteristic sequence, public-key exchange scheme, RSA-type encryption.
*
Work was done when the author visited the Department of Computer Networking, University of
Missouri-Kansas City.
1
Public-Key Cryptosystems Based on Cubic
Finite Field Extensions
Guang Gong and Lein Harn
Abstract: The cryptographic properties of 3rd-order linear feedback shift register
(LFSR) sequences over GF(p) are investigated. A fast computational algorithm for
evaluating the kth term of a characteristic sequence of order 3 is presented. Based on these
properties, a new public-key distribution scheme and a RSA-type encryption algorithm
are proposed. Their security, implementation, information rate, and computational cost
for the new schemes are discussed.
Index words: Cubic finite field extension, linear feedback shift register sequence,
characteristic sequence, public-key exchange scheme, RSA-type encryption.
I. Introduction
With the rapid development of Internet applications, information security in
today’s world is more important than that in any previous era. Designing cryptosystems
that meet requirements of communication bandwidth, information rate, computational
speed, and various security strategies, has become a very challenging task for researchers.
In the most widely used modern cryptosystems, such as the RSA [18], the DiffieHellman public-key distribution scheme [3], the ElGamal cryptosystem [5] and DSS [16],
increasing the size of the modulus is necessary in order to strengthen their security.
From the point of the linear feedback shift register (LFSR) sequences, the
exponential function which used in the RSA encryption, the Diffie-Hellman (DH) publickey exchange scheme [3], and the ElGamal digital signature scheme is a 1st-order LFSR
sequence over GF(p) or Zn, where n is a product of two prime numbers. In the literature,
there is another family of public-key cryptosystems similar to RSA, DH, and ElGamal
2
public-key cryptosystems, which are called the Dickson polynomial scheme [13, 14, 15]
or LUC [20, 21], respectively. The mathematical function used in this family of the
public-key cryptosystems is the 2nd-order LFSR sequence over GF(p) or Zn with a special
initial state. This kind of LFSR sequences are coset constant [8]. We will give their
definition in Section II. (Note: throughout of this paper, we will use the term LFSR
sequences over GF(p) or Zn instead of linear recurring sequences over GF(p) or Zn, since
the term of initial state is related to a LFSR.)
In this paper, we will explore to construct public-key cryptosystems by using 3rdorder LFSR sequences over GF(p) or Zn. First, we will investigate the cryptographic
properties of 3rd-order LFSR sequences and propose a fast computational algorithm to
evaluate the kth term of a 3rd-order characteristic sequence. Based on these properties, we
will construct two public-key cryptographic algorithms. One is a public-key distribution
scheme that can reduce the size of the modulus while speeding up the computation. The
security is based on the difficulty of solving the discrete logarithm in GF(p3). Another
one is a RSA-type encryption algorithm whose security is based on the difficulty of
factoring a large composite integer. We will also discuss their security, implementation,
information rate, and computational cost.
For the theory of LFSR sequences, the reader is refereed to [8, 12], and for the
fundamental theory of finite fields, see [12].
II. 3rd-order Characteristic Sequences
Let F = GF(p), where p is a prime and
f x x 3 ax 2 bx 1 , a , b F
(1)
be a polynomial over F. A sequence s sk is said to be a 3rd-order LFSR sequence
with a characteristic polynomial f(x) if the elements of s satisfy
sk ask 1 bsk 2 sk 3 , k 3.
(2)
If s has the initial state: s0 3 , s1 a and s2 a 2 2b , then s sk is called the
characteristic sequence generated by f(x). We denote sk as sk (a , b) or sk(f), and s as
s(a, b) or s(f).
3
Assume that 1 , 2 , 3 are all three roots of f(x) in the splitting field of f(x) over
F. According to Newton's formula, the elements of s can be represented by the symmetric
kth power sum of the roots as follows
sk 1k 2k 3k , k = 0, 1, ….
(3)
Let us denote the period of f(x) as per(f). Notice that if f(x) is irreducible over F,
then the period of s(f) is equal to per(f).
Lemma 1. Let f x x 3 ax 2 bx 1 be a polynomial over F, 1 , 2 , 3 be
three roots of f(x) in the splitting field of f(x) over F, and s be the characteristic sequence
generated by f(x). Let f k x x 1k x 2k x 3k .
(i)
(ii)
f k x x 3 sk (a , b) x 2 s k (a , b) x 1 , where s k (a , b) sk (b, a ) .
If f(x) is irreducible over F, then f(x) and fk(x) have the same period if and
only if (per(f), k) = 1.
(iii)
If (per(f), k) = 1, then f(x) is irreducible over F if and only if fk(x) is
irreducible over F.
Proof. (i). It follows from Newton's formula of equation (3). (ii). If f(x) is
irreducible over F , then the minimal polynomial of ik over F is fk(x) and per(fk(x)) =
per(f)/(per(f), k). So, per(fk(x)) = per(f) if and only if (per(f), k) = 1. (iii). It follows from
(ii).
Remark. Let
f
1
( x) x 3 bx 2 ax 1 . Then
f
1
( x)
is the reciprocal
polynomial of f(x) and {s-k(a,b)} is the characteristic sequence over F generated by
f
1
( x) . We also call {s-k(a,b)} the reciprocal sequence of {sk(a,b)}.
Lemma 2. Let f x x 3 ax 2 bx 1 be a polynomial over F, and let s be the
characteristic sequence generated by f(x). Then for all positive integers k and e,
sk se (a , b), se (a , b) ske (a , b) .
(5)
Proof. From Lemma 1,
f e x x 1e x 2e x 3e = x 3 se a , b x 2 s e a , b x 1 .
Thus
4
(6)
sk se (a , b), se (a , b) = 1e 2e 3e = 1ek 2ek 3ek = ske (a , b) .
k
k
k
Q.E.D.
Note. If we consider a and b as variables in F and k as a fixed integer, then sk(a,b)
and s-k(a,b) are Waring polynomials. From Theorem 7.46 in [12] , we have the following
fact.
Fact 1. Let k be a fixed positive integer. If k satisfies (k, pi – 1) = 1, i = 1, 2, 3,
then for any u, v F, the system of equations:
s k (a, b) u and s k (a, b) v
has a unique solution (a, b) FF. In other words, sk(a,b) and s-k(a,b) are orthogonal in
F in variables a and b.
We denote that Q = p 2 p 1 . A positive integer r is called a coset leader
modulo Q if r is the smallest integer in the set {tpi mod Q | i = 0, 1, 2}, where t is a
positive integer.
Theorem 1. Let f x x 3 ax 2 bx 1 be an irreducible polynomial over F of
the period Q = p 2 p 1 and s sk be the characteristic sequence generated by f(x).
Let k and k’ be different coset leaders modulo Q, and both k and k’ are relatively prime to
Q. Then
s , s s
, then
k
Proof. If sk , s k sk ' , s k '
k
k'
, s k ' .
f k ( x) x 3 sk x 2 s k x 1 = x 3 sk ' x 2 s k ' x 1 f k ' x .
Thus fk(x) also has ik ' , 1 i 3 , as its roots. From Lemma 1, fk(x) is irreducible over F.
Therefore, ik and ik ' are conjugate of each other. In other word, there exists an integer
t, 0 t 2, such that
k ' kp t (mod Q).
This contradicts with the fact that k and k are different coset leaders modulo Q.
Q.E.D.
Remark. Lemma 2 and Theorem 1 will play as key roles in constructing a publickey distribution scheme, since the former guarantees the commutative property and the
5
later provides one-to-one correspondence between the private key space and the public
key space. Fact 1, together with Lemma 2, will be used to construct a RSA-type
encryption scheme.
III. Fast Computational Method
In reference [7], there is an algorithm to calculate the kth term of any linear
recurring sequences. Here we will provide a much more efficient algorithm to calculate
the kth term of a 3rd-order characteristic sequence.
Lemma 3. Let
s
be the 3rd-order reciprocal characteristic sequence over F
k
with the characteristic polynomial f(x), defined by (1), and s k , its reciprocal sequence.
Then for any positive integers n and m,
(i) s2 n sn2 2sn , and
(ii) sn sm sn m s m sn m sn 2 m , n m .
Proof. From (2), we have
s2 n 12 n 22 n 32 n , and
sn2 1n 2n 3n .
2
Notice that 1 2 3 1 . Then
s
2
n
2n
1
2n
2
2n
3
2
1i j 3
n
i
3
= s2 n 2 i n = s2 n 2 sn
n
j
i 1
which gives (i). The same argument can be applied to (ii).
Q.E.D.
r
Let
k k i 2 r i
be the binary representation of k,
i 0
T0 k 0 0
and
Tj k j 2Tj 1 , 1 j r . So, Tr k . From Lemma 3, the recurrence can be described
by the following formulae:
For k j = 0,
sTj 1 sTj 1 sTj 1 1 bs Tj 1 s ( Tj 1 1) ,
(7)
sTj sT2j 1 2 sTj 1 , and
(8)
6
sTj 1 sTj 1 sTj 1 1 as Tj 1 s ( Tj 1 1) .
(9)
For k j = 1,
sTj 1 sT2j 1 2 sTj 1 ,
(10)
sTj sTj 1 sTj 1 1 as Tj 1 s ( Tj 1 1) , and
(11)
sTj 1 sT2j 1 1 2 s( Tj 1 1) .
(12)
Since sk and s k are symmetric in (7) - (12) and the probability that kj equals
0 or 1 is 1 / 2, therefore we obtain the following result.
Theorem 2. With the same f(x), sk and s k as in Lemma 3. Using (7) - (12)
to calculate a pair of the kth terms sk and s-k needs 9logk modulo p multiplications on
average.
Note. This method is much more efficient than the algorithm using modulo
polynomial [7]. The algorithm provided in [7] requires O((n)logk) arithmetic operations
to calculate the kth term of a LFSR sequence of order n over F where (n) is the total
number of arithmetic operations required to multiply two polynomials of degree n 1. In
case of n = 3, (3) is the total number of multiplications modulo p required to multiply
two polynomials of degree 2 over F (=GF(p)) and reduce it by modulo f(x). Notice that
multiplying two polynomials of degree 2 over F without reduction by modulo f(x) already
requires 9 multiplications modulo p. So, by using the algorithm in [7] to calculate the kth
term sk requires at least 9logk multiplications modulo p. Consequently, the total
computational cost for calculating a pair of the kth term sk and s-k needs at least 18logk
multiplications modulo p.
IV. A Public-Key Distribution Scheme
In this section, we will present a public-key distribution (GH-PKD) scheme that is
constructed by a pair of 3rd-order characteristic sequences and discuss its security.
7
A. GH-PKD Scheme
Key Generation Phase
System public parameters: p is a prime number, and f x x 3 ax 2 bx 1 is an
irreducible polynomial over GF(p) with the period Q = p 2 p 1 .
User Alice selects e that satisfies 0 e Q and gcd(e, Q)=1 as her private key.
She then computes ( se , s e ) as her public key from the system public key p and
f x x 3 ax 2 bx 1 .
User Bob selects r that satisfies that 0 r Q and gcd(r, Q) = 1 as his private
key. He then computes ( sr , s r ) as his public key from the system public key p and
f x x 3 ax 2 bx 1 .
Key Distribution Phase
Alice
Bob
( se , s e )
computing:
computing:
( sr , s r )
se sr , s r and se sr , sr
sr se , s e and sr se , se
According to Lemma 2,
se sr , s r = ser = sr se , s e , and se sr , sr = s er = sr se , se .
Namely, their common key is ( ser , s er ).
Example. Let p = 11, and f x x 3 4 x 1 is an irreducible polynomial over
GF(11) of period 133 = 719.
Alice: Selects e = 9 as her private key. Her public key is ( s9 , s 9 ) = (10, 6).
Bob: Selects r = 13 as private key. His public key is ( s13 , s13 ) = (7, 1).
Key Distribution Phase:
Alice : se sr , s r = s9(7, 1) = 8, and se sr , sr = s-9(7, 1) = s124(7, 1) = 5.
So she obtains the key (8, 5).
8
Bob: sr se , s e = s13(10, 6) = 8, and s-13(10, 6) = s120(10, 6) = 5. He obtains
the same key (8, 5) as Alice.
Remark.
(i). In the Key Distribution Phase, this scheme doesn’t involve the system public
key f x x 3 ax 2 bx 1 .
(ii) The spaces of the private keys and public keys are the sets consisting of all
coset leaders modulo p 2 p 1 relatively prime to p 2 p 1 and all
irreducible polynomials over GF(p) of degree 3 with the period p 2 p 1 ,
respectively. According to Theorem 1, the map: k: sk , s k from the space
of the private keys to the space of the public keys is bijective. Thus, there will
be different public keys corresponding to different private keys in GH-PKD.
Moreover, the size of the space of private (or public) keys is ( p 2 p 1) / 3
where (.) is the Euler function.
(iii) In each key exchange session, the computational cost for each user is 9logp
modulo p multiplications on average.
B. Security of GH-PKD
The security for GH key distribution scheme is based on the difficulty of solving
the discrete logarithm in GF(p3). If an attacker tries to compute Alice’s private key e
from her public key ( se , se ) , a polynomial f e x x 3 se x 2 se x 1 can be formed.
Since f x x 3 ax 2 bx 1 is irreducible over F, according to Lemma 1, f e x is
also irreducible over F. Assume that and are the roots of f(x) and f e x in the
extension GF(p3) of F, respectively. They then can be derived by solving roots of
f x x 3 ax 2 bx 1 and f e x x 3 se x 2 se x 1 in GF(p3). Then = e. As a
result, once and are known, solving the exponent e is equivalent to solving the
discrete logarithm in GF(p3). According to [1, 2, 6, 9, 11], solving the discrete logarithm
in GF(p3) is much harder than solving discrete logarithm in the GF(p) for the same p.
9
V. A RSA-Type Encryption Scheme
In this section, we will propose a RSA-type public-key cryptosystem by using a
pair of 3rd-order characteristic sequences over Zn, which is an integer ring modulo n.
A. A RSA-type Encryption Algrithm
1. Public keys: e and n, where n = pq, p and q are primes, and gcd(e, pi – 1) = 1,
i = 2, 3.
2. Private keys di, 1 i 9, where di’s are given by Table 3.
3. Enciphering: For a message m = (m1, m2) where 0 < m1, m2 < n, the sender
computes c1 = se(m1, m2) and c2 = s-e(m1, m2). The ciphertext c = (c1, c2).
4. Deciphering: First, the receiver computes three functions (15)-(17) of the
ciphers c1, c2 in order to choose a proper decryption key d, in the set { di,1 i
9 } in Table. Then he computes m1 = sd(c1, c2) and m2 = s-d(c1, c2) using the
selected key d.
Note that all computations here are performed in Zn.
Remark. According to Fact 1 and the Chinese Remainder Theorem, the map
m1 , m2 se (m1 , m2 ), se (m1 , m2 )
is a bijective map from the message space to the ciphertext space.
Next we will show how to construct decryption keys. For a 3rd-order characteristic
sequence s over F = GF(p) generated by f x x 3 ax 2 bx 1 , its period, per(s), may
be one of three cases as listed below:
Case 1. f(x) is reducible over F per(s) | p – 1.
Case 2. f(x) = (x - )f1(x) where f1(x) is irreducible over F and F
per(s) | p2 – 1 and per(s) is not a factor of p – 1.
Case 3. f(x) is irreduclible over F per(s) | p2 + p + 1.
According to the method for solving a cubic equation in a finite field in [17],
substituting x y 31 a into f(x), then
f ( x) g ( y) y 3 C (a, b) y D(a, b) ,
where
10
(13)
C (a, b) 31 a 2 b and D(a, b) 2 33 a 3 31 ab 1.
(14)
The discriminate of the cubic (13) is defined as
(a, b) 4C 3 (a, b) 27 D 2 (a, b) .
(15)
Let x {p, q},
27 D(a, b) 27(a, b)
( a, b)
27 D(a, b) 27(a, b)
2N
(16)
where N ( x 1) 6 , ( x 1) 6, and
i
, the Legendre symbol of an integer i with respect to the prime x.
x
(17)
Now we are in a position to give a definition for a logic function ( j , x) , which is related
to the ciphertext ( c1, c2), where j {1, 2, 3} and x {p, q}.
(c1 , c 2 )
(1, x) is true ( c1, c2) (mod x) = 0 or ( c1, c2) (mod x) 0,
= 1 and
x
(c1 , c2 ) (mod x) = 1.
Case 1
(c1 , c 2 )
(2, x) is true ( c1, c2) (mod x) 0 and
= - 1.
x
Case 2
(c1 , c 2 )
(3, x) is true ( c1, c2) (mod x) 0,
= 1 and (c1 , c2 ) (mod x) 1.
x
Case 3
We denote R1, x x 1 , R2, x x 2 1 and R2, x x 2 x 1 . From Lemma 1, two
polynomials x 3 m1 x 2 m2 x 1 and x 3 c1 x 2 c2 x 1 have the same period. So the
receiver can select a proper deciphering key based on the polynomial constructed by the
ciphertext (c1, c2). The following Table gives the construction of these deciphering keys.
11
Table. A Construction for the Deciphering Keys
Condition
Multiplier of the
Deciphering Key
Period
(1, p) (1, q)
1 = R1,p R1,q
d1e 1 (mod 1)
(1, p) (2, q)
2 = R1,p R2,q
d2e 1 (mod 2)
(1, p) (3, q)
3 = R1,p R3,q
d3e 1 (mod 3)
(2, p) (1, q)
4 = R2,p R1,q
d4e 1 (mod 4)
(2, p) (2, q)
5 = R2,p R2,q
d5e 1 (mod 5)
(2, p) (3, q)
6 = R2,p R3,q
d6e 1 (mod 6)
(3, p) (1, q)
7 = R3,p R1,q
d7e 1 (mod 7)
(3, p) (2, q)
8 = R3,p R2,q
d8e 1 (mod 8)
(3, p) (3, q)
9 = R3,p R3,q
d9e 1 (mod 9)
B. Security
It is clear that the security of the scheme is based on the difficulty of factoring a
large composite integer.
C. Computational Cost
As the RSA public-key system, we can choose a small e such that the
computational cost for computing the eth terms of the 3rd-order characteristic sequence
with f(x) = x 3 m1 x 2 m2 x 1 and its reciprocal polynomial is low. For example, by
taking e = 5, we compute
s0 = 3, s1 = m1, and s2 = m1 – 2m2,
s3 = m1 s2 - m2 s1 + s0,
s4 = s 22 -2 s-2, and
s5 = m1 s4 - m2 s3 + s2.
So, c1 = s5 . Similarly,
s0 = 3, s-1 = m2, and s-2 = m2 – 2m1,
s-3 = m2 s-2 - m1 s-1 + s0,
12
s-4 = s 22 -2 s2, and
s-5 = m2 s-4 - m1 s-3 + s-2.
We get c2 = s-5 . Totally, we only need 10 modulo n multiplications for enciphering a
2logn-bit message. For deciphering process, first we need to decide a proper deciphering
key d, i.e., we need to compute three functions. ( c1, c2) (mod x) requires 8 modulo n
(c1 , c 2 )
multiplications. For
and (c1 , c2 ) (mod x), each of the last two functions
x
requires 1.5logp modulo p multiplications and 1.5logq modulo q multiplications,
respectively. Second, we need to compute the dth terms the 3rd-order characteristic
sequence with x 3 c1 x 2 c2 x 1 and its reciprocal polynomial, which needs 9logn
modulo n multiplications on average. Therefore, the total computational cost in the
deciphering process is 12logn modulo n multiplications on average.
IV. Conclusion and Discussion
As we have shown, we can conclude that the proposed public-key distribution
scheme (GH-PKD) and the RSA-type encryption scheme are practical efficient publickey cryptosystems. Especially, GH-PKD is successful in reducing the size of the modulus
while speeding up the computation. Note that from current literatures [19, 22, 23], only a
few of public-key cryptosystems have been put into practical use.
The method presented here can be leading to construct public-key cryptosystems
by using nth-order characteristic sequences over GF(p) of any degree n > 3.
Acknowledgement
The authors wish to thank the referees for their valuable comments and
suggestions.
13
References
[1] L.M. Adleman and J. DeMarrais, “A subexponential algorithm for descrete
logarithms over all finite fields,” Proceedings Crypto'93, Lecture Notes in Computer
Science, No. 773, 1994, pp.147-158.
[2] L.M. Adleman and M.A. Huang, "Function field sieve method for discrete logarithms
over finite fields, " preprint, December 1997.
[3] W. Diffie and M.E. Hellman, “New directions in cryptography,” IEEE Trans. on
Inform. Theory, vol. IT-22, November 1976, pp.644-654.
[4] P. Donnelly and G. Grimmett, “On the asymptotic distribution of large prime
factors,” J. London Math. Soc. (2), 47 (1993), pp. 395-404.
[5] T. ElGamal, “A public key cryptosystem and a signature scheme based on discrete
logarithms,” IEEE Trans. on Inform. Theory, vol. IT- 31, no. 4, July 1985, pp.469472.
[6] T. ElGamal, “A subexponential-time algorithm for computing discrete logarithms
over GF(p2), IEEE Trans. on Inform. Theory, vol. IT-32, 1985.
[7] C.M. Fiduccia, “ An efficient formula for linear recurrences,” SIAM J. Comput. 14,
1985, pp. 106-112.
[8] S.W. Golomb, Shift Register Sequences, Laguna Hills, CA: Aegean Park Press, 1982.
[9] D. Gordon, “Discrete logarithms in GF(p) suing the number field sieve,” SIAM J.
Disc. Math. 6(1993), pp. 124-138.
[10] D.E. Knuth, The Art of Computer Programming, vol. 2, Seminumerical Algorithms,
Addison-Wesley Publishing Co., MA, 1969.
[11] A.K. Lenstra and H.W. Lenstra, Jr. (eds), The Development of the Number Field
Sieve, Lecture Notes in Math. 1554, Springer-Verlag, Berlin, 1993.
[12] R. Lidl and H. Niederreiter, Finite Fields, Encyclopedia of Mathematics and its
Applications, Volume 20, Addison-Wesley, 1983.
[13] R. Lidl, G.L. Mullen and G. Turnwald, Dickson Polynomials, Pitman Monographs
and Surveys in Pure and Applied Mathematics 65, John Wiley & Sons, Inc., 1993.
14
[14] W.B. Mller and W. Nbauer, "Cryptanalysis of the Dickson-scheme, "
Proceedings of Eurocrypt'85, Springer-Verlag, pp. 71-76.
[15] W. Nbauer, "Cryptanalysis of a public-key cryptosystem based on Dickson
polynomials, " Mathematica Slovaca 38 (1989), pp. 309-323.
[16] NIST, “A proposed federal information processing standard for digital signature
standard (DSS),” Federal Register 56 (1991), 42980-42982.
[17] L. Rédei, Algebra, Geest & Portig, Leipzig, 1959; Pergamon Press, London 1967.
[18] R.L. Rivest, A. Shamir, and L. Adleman, “A method for obtaining digital signatures
and public key cryptosystems,” ACM, vol. 21, no. 2, Feb. 1978, pp.120-126.
[19] B. Schneier, Applied Cryptography, John Wiley & Sons, Inc., Second edition, 1996.
[20] P. Smith, "LUC public-key encryption, " Dr. Dobb's Journal, pp. 44-49, January
1993.
[21] P. Smith and C. Skinner, "A public-key cryptosystem and a digital signature system
based on the Lucas function analogue to discrete logarithms," Proceedings of
Asiacrypt'94, pp. 298-306, Nov. 1994.
[22] D.R. Stison, Cryptography, Theory and Practice, CRC Press, Inc., 1995.
[23] W. Stallings, Network and Internetwork Security Principles and Practice, IEEE
Press, Inc., New York, 1995.
15