Security
advertisement
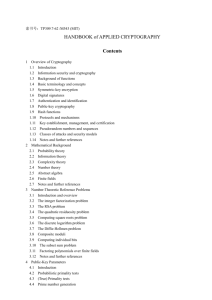
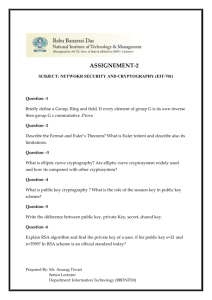
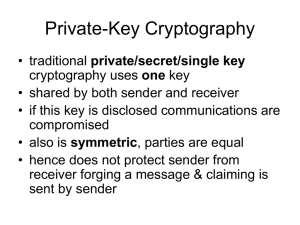
(1901758): Computer Protection and Security Computer Science Dept., Jordan University, 2007/2008 Instructor: Dr. Imad Salah Course Description: Computer security and basic cryptography topics, introduction to the mathematical principles of data security, information security, various developments in security are discussed, with emphasis on public-key encryption, digital signature, the data encryption standard (DES), key-safeguarding schemes vulnerabilities, policy formation, control and protection methods, and Internet security. (This description is the same as appeared in the computer science dept. curriculum). Intended Learning Outcomes: The intended learning outcomes of this course are: A- Knowledge and Understanding: Students should … A1) Learn the basic concepts in computer security.. A2) Understand the advance d features in public-key cryptosystems. B- Intellectual skills: with the ability to … B1) Compare and analyze algorithms as fundamental tools of security. B2) Apply mathematical tools to algorithm verification and analysis. B3) Analytically recognize the needed security schema in relevance to some application. C- Subject specific skills – with ability to … C1) Work on case studies to show how all the tools are used together to build a complete project and research. C2) Translate abstract ideas into practice. C3) Implement and handle security projects. D- Transferable skills – with ability to D1) Possess good security policy. D2) Develop advanced public key cryptanalysis. D3) Choose the appropriate methods for public key generation of RSA algorithm. Course Contents: Course Introduction: Digital Threats, Security needs, Security systems, Security Policy, Symmetric Cryptography, Seizer Cipher, One Time Pad. Finite Fields Groups: Fields, and Rings Modular Arithmetic, Euclid’s Algorithm, Finite Field of the form GF(p), Polynomial Arithmetic, Finite Fields of the form GF(2). Symmetric key Encryption: DES Encryption modes. Triple DES , and AES. Number Theory: Prime numbers, Fermat’s theorem, Euler’s Totient Function, Euler’s Theorem. Testing for Primality, The Chinese remainder theorem, Discrete logarithms. Public-Key Cryptography: Public-Key cryptosystems, Applications for public Key cryptosystems, Requirements for Public-Key cryptosystems. The RSA algorithm: Description of the Algorithm, Computational Aspects, RSA Cryptanalysis and the security of RSA. Other Public-Key approaches: The DiffieHellman key exchange, Elliptic curve arithmetic, Abelian groups, Eleptic curves over real numbers, Elliptic curves over Zp, Elliptic curves over GF(2^m), Elliptic curves cryptography, analog of Diffie-Hellman key exchange, Security of Elliptic curve cryptography. Message Authentication and Hash functions: Authentication functions. Digital signatures Authentication servers: Kerberos Hash algorithms: MD5 and MD4, Secure Hash algorithms. Web security: PGP Intrusion Detection Teaching methods. Lectures, Demos, Researches and Projects, Seminars and Presentations, Invited Speakers. Evaluations: 1- Mid Term Exam: 35 2- Project, Technical Report Writing, and Seminars: 25 3- Final Exam: 40. Textbooks; Cryptography and Network Security, Third Edition. By William Stallings. from Prentice Hall. A good overview of computer security in plain English from one of the leading cryptographic experts: Secrets & Lies: Digital Security in a Networked World, by Bruce Schneier. ISBN: 0471253111. References: Journal of Computer Security, IEEE Security and Privacy