Security Advisory-The Firewall Module of SPU Board
advertisement

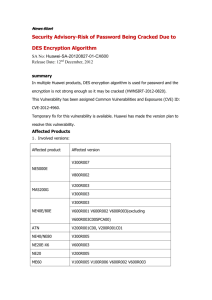
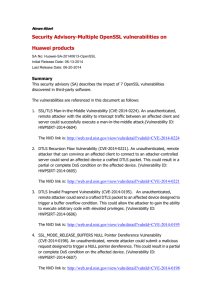
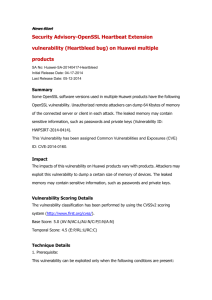
News Start Security Advisory-The Firewall Module of SPU Board Information Leakage Vulnerability of Huawei Campus Switch SA No: Huawei-SA-20130516-01-SPU Initial Release Date: 05-16-2013 Last Release Date: 05-16-2013 Summary The Service Process Unit (SPU) is the value-added service card of the Switch. SPU provides services such as load balancing, firewall, Network Address Translation (NAT), IP Security (IPSec), and NetStream. It mainly be deployed in network of carrier and enterprise customers, and provides network security solution and interconnection solution between campuses and private networks. SPU contains a vulnerability that the users of low priority security zone may visit the contents located in high priority security zone, and it could cause information leakage. The vulnerability is due to improper handling process while the switch works in a specific working model (Vulnerability ID: HWNSIRT-2013-0317). Currently, this vulnerability has been fixed in Quidway official release. Affected Products Products Name Products Version Quidway S7700 V200R001C00SPC300 SPU V200R001C10SPC300 Quidway S9300 V200R001C00SPC300 SPU V200R001C10SPC300 Quidway S9700 V200R001C00SPC300 SPU V200R001C10SPC300 Impact By exploiting the vulnerability successfully, it may lead to the user in low priority security zone of switch could access to the data existed in high priority security zone, and it causes information leakage. Vulnerability Scoring Details The vulnerability classification has been performed by using the CVSSv2 scoring system (http://www.first.org/cvss/). The score of the vulnerability is following: Base Score: 4.9(AV:N/AC:M/Au:S/C:P/I:N/A:P) Temporal Score: 4.1 (E:F/RL:O/RC:C) Overall Score: 4.1 Technical Details Vulnerability exploitation prerequisites: The attacker is a legal user of the security zone in switch, The switch works in the specific model and runs with default configuration between different security zones. Vulnerability details: The user in the low priority security zone visits the data located in the high priority security zone. Temporary Fixes To prevent the information leakage occurring, modify the default packet filter policy between the security zones. Please refer to the Configuration Guide for detailed info. Below is a configuration example: 1, Configure ACL rules: [SPU]acl number 2000 [SPU-acl-basic-2000]rule 10 deny [SPU-acl-basic-2000]quit 2, Apply ACL rules. We assume that the security zones named “trust” and “untrust” are pre-configured in the switch according to users accessing privilege: [SPU]firewall interzone trust untrust [SPU-interzone-trust-untrust]firewall enable [SPU-interzone-trust-untrust]packet-filter 2000 outbound [SPU-interzone-trust-untrust]packet-filter 2000 inbound [SPU-interzone-trust-untrust]quit Software Versions and Fixes Solution Modify the default packet filter policy handling process between the security zones to prevent the information leakage vulnerability. This vulnerability has been fixed in the following version: Products Name Products Version V200R001C00SPC30 Quidway 0 S7700 SPU V200R001C10SPC30 0 V200R001C00SPC30 Quidway 0 S9300 SPU V200R001C10SPC30 0 V200R001C00SPC30 Quidway 0 S9700 SPU V200R001C10SPC30 0 SPU Patches Version Release Data VASP-V200R001SPH00 3 2012-12-31 and later patches VASP-V200R001SPH00 3 2012-12-31 and later patches VASP-V200R001SPH00 3 2012-12-31 and later patches Obtaining Fixed Software Carrier customers please contact Huawei TAC (Huawei Technical Assistance Center) to request the upgrades, and enterprise customers please obtain them through Huawei Enterprise worldwide website at http://support.huawei.com/enterprise/. For TAC contact information, please refer to Huawei worldwide website at http://www.huawei.com/en/security/psirt/report-vulnerabilities/index.htm. Exploitation and Vulnerability Source This vulnerability is reported by Huawei internal tester and hasn’t received any impact report. Huawei PSIRT is not aware of any malicious use launched to attack through the vulnerability described in this advisory. Contact Channel for Technical Issue For security problems about Huawei products and solutions, please contact PSIRT@huawei.com For general problems about Huawei products and solutions, please directly contact Huawei TAC (Huawei Technical Assistance Center) to request the configuration or technical assistance. Revision History 2013-05-16 V1.0 INITIAL Declaration This document is provided on an "AS IS" basis and does not imply any kind of guarantee or warranty, either express or implied, including the warranties of merchantability or fitness for a particular purpose. In no event shall Huawei Investment & Holding Co., Ltd. or any of its directly or indirectly controlled subsidiaries or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages. Your use of the document, by whatsoever means, will be totally at your own risk. Huawei is entitled to amend or update this document from time to time. Huawei Security Procedures Complete information on providing feedback on security vulnerability of Huawei products, getting support for Huawei security incident response services, and obtaining Huawei security vulnerability information, is available on Huawei's worldwide website at http://www.huawei.com/en/security/psirt/ News End