CBS Interfaces - ICAI | Online Web TV
advertisement

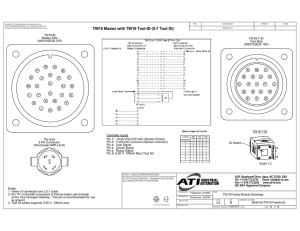
CBS Interfaces N D Kundu Agenda Alternate Delivery Channels Automated Teller Machines Internet Banking Real Time Gross Settlement Cash Management Systems External Interfaces • • • • • • • • ATM Interface ATM interface with switch Tele banking Internet banking Mobile Banking Cash Management Real Time Gross Settlement Bunch Note Acceptor Central Bank Clearing House National Payment System Bank A Bank B Retail Payment System (ATM, EFTPOS, Credit Cards Customer Customer Customer I T and Retail Payment Systems Customer List of Interfaces and mode of connectivity Global Treasury CTS DMS CMS Interfaces used 19 6 4 6 STP – TCP/IP 1 1 - 2 DBlink 4 1 - 1 FTP - - 1 - STP – SFTP 2 - 1 - - 1 1 Network Share 9 2 Manual 2 DB Port 1 1 1 - RDP - 1 1 - SMTP - - - 1 Connect-24 • One view to the external world through all delivery channels • Middleware for real time interface of delivery channels to Finacle • Supports traditional and emerging delivery channels viz. ATM, Telephone or Internet using ISO 8583 and OFX standards Connect-24 Finacle DATABASE DATA CENTER CONNECT-24 e-Channels/ e-Corporate Public Network ATM ATM SWITCH POS Telebanking ATM Deskt ops Automated Teller Machine (ATM) ATM Card & Debit Card Procedure for issuing ATM Cards ATM Switches Host Security Module Natural PIN Generation Storage of PIN?? Track 2 on Magnetic-strip Chip based Card Cash Dispenser Functions of ATM Cash Withdrawal Balance Inquiry Cheque book request PIN Change Mini Statement Utility Bill Payment Mobile Top-up Updation of Mobile number *** ATM Structure Functioning of the ATM Customer swipe the card Enter PIN, encrypted using HSM/SSM Validation of data by SWITCH Customer authenticated Service request like withdrawal of cash sent to Database Balance verification for adequacy Account debited and on confirmation ATM dispensed cash In the changed process, even the cash is not picked up, it will not gone back to the ATM BIN. All details recorded in journal Interchange agency –VISA, MASTER, RUPAY Verification of PIN Customer insert card & enter PIN Encrypted PIN sent to ATM Switch ATM verifies card details from database & confirm correctness Natural PIN generated Switch is having the value which is difference between actual PIN & natural PIN This offset value verified using HSM/SSM If tallied customer/card is authenticated Change of PIN Card inserted, verified from Switch databases PIN change option – enter old PIN, verifies through SSM/HSM Enter new PIN Using card no., Natural PIN new offset value generated & stored in SSM/HSM Old offset value erased No where in the system PIN is stored There is a process of computing PIN using card no. & the offset value stored in HSM/SSM. Operational Issue Insufficient Cash Journal paper exhausted Network connection lost Faulty card CCTV should be there Guard/ watchman should be insisted upon Three wrong attempts card should be blocked Limit of cash withdrawal, no. of txn per day Hotlisting of cards Fraud Risk Management Solution Evaluation of Controls in ATM Card & PIN generation process Dealing with surrendered card Security of PIN Control over cash Maintenance of transaction records Dealing with lost/ stolen cards ATM Switch operations Card & PIN Generation Separate department to handle card & PIN Confidentiality in PIN mailer generation Reconciliation of no. of PIN mailer & card produced Physical & Logical access control Flow of data to card printing agency, if outsourced Stock of blank cards Control on card card embossing & PIN mailer PIN & card should be despatched separately by different courier Record maintenance Handling of returned cards Surrendered & Captured Cards Complete documentation Process for replacement of card & PIN Process for making captured card ineffective PIN mailer need not be returned by customer Register for surrendered card Removal of captured card on regular basis Report from Data Centre & reconciliation Capture procedure for entering wrong PIN thrice Security of PIN Report by customer- block immediately Not to disclose PIN to anyone Process of timely generation of new PIN PIN/PIN offset should always be in encrypted form HSM/SSM should be in self destructive mode All storage for PIN encryption should be zeroised after each calculation No hard copy of record of PIN produced ATM cash Management Documented procedures for cash balancing Journal should automatically record all withdrawals Cash inserted in each BIN/ cassette should also be recorded Cash reconciliation for cash dispensed, remaining cash, misfit notes All discrepancies noted & reported Maintenance of cash & reconciliation by 2 different persons Wrong denomination – should be doubly check Daily balance procedure Record maintenance Journal Roll – recording of all events Hard copies of journal to be preserved Soft copy of EJ – no modification allowed Secure storage of EJ Journal roll should be checked regularly Unauthorised opening of ATM should also be recorded Lost & Stolen Cards Documented Procedure Uptodate record of all stolen cards Restricted access Facility to identify when stolen card is used Reject the transaction or capture the card on trigger Procedure to note verbal instruction to stop usage Replacement card after written request only Legal provision to be followed Report to be generated & preserved ATM Switch Operations ATM switch is also a server with dtabase Card No. & its offset value stored Details of hotlisted cards Details of surrendered card Account balance of customer ATM- Audit Check List Security guard & CCTV Control on Server OS & DB Sys Admin controls Security of Admin password Setting of parameters like max. no. of withdrawal, withdrawal per day, no. of failed attempts etc. Review the procedure for configuration Authorised modification only allowed Security of key encryption & decryption Review procedure for hot-listing Review types of logs generated Agreement with other Banks & agency. Skimming Sample Picture Source: http://www.snopes.com/fraud/atm/atmcamera.asp Skimming Sample Picture Source: http://www.snopes.com/fraud/atm/atmcamera.asp Skimming Sample Picture Source: http://www.snopes.com/fraud/atm/atmcamera.asp Internet Banking Banking transactions through Internet Permitted to registered customer only Any time, any where banking 24X7 Adequate security to be built Customer awareness to be increased Beware of phishing attacks Internet Banking Components Demilitarised Zone Web server Internet Banking Application Server Internet Banking Database Server Middleware – Connect 24 Central Database Server Firewal Customer accesses Bank’s website using a browser Web server sends the Bank’s Webpage to the customer Customer types Internet Banking user name and password Web server sends user name and password to IBAS IBAS requests user name and password of the customer from IBDS IBDS sends user Name and Password of Customer to IBAS Customer chooses an IB service say “Account statement view” Web server presents the facing page of the Customer’s account (assuming customer is authenticated) IBAS authenticates the customer and intimates the web server Web server forwards the service request to IBAS for processing A A IBAS requests customer account information from IBDS IBDS requests customer account information from Core DB that is accessed via Middleware Middleware forwards request from IBDS to Core DB Middleware converts customer account information to suit the requirements of IBDS IBAS accesses the customer information in IBDS and presents it to the Web Server Web server presents the customer a dynamic web page with the account information Customer is presented with the requested account statement IBDS temporarily stores customer account information Core DB retrieves customer account information and forwards it to the middleware Internet Banking Process Customer application – issue ID & Password Login password & Transaction password Change password immediately after first login Browser based access through web pages Website/ URL hosted in web server Webserver is in DMZ of DC Separate Firewall for Web server Access through user-ID & login password Customer detail will flow from web-server to IBAS IBAS access IBDS which contains all details of IB customers IBDS will verify the details, otherwise access will be denied On successful authentication, customer will get access. IB-available functions Fund transfer – self & third party Balance inquiry Statement of accounts Opening of Fixed Deposit & Recurring Deposit account Request for Cheque Book Stop Payment ATM/Debit card queries Other value added services Process Flow Customer choose his function say statement of account Web server send information to IBAS IBAS access IBDS for getting data IBDS will interact with Central DB server through middleware Middleware convert the data to suit the requirement of central DB IBDS forward customer data to IBAS which process the request Statement of accounts from central DB made available to IBDS IBDS will send to IBAS then to web browser Web server generate dynamic web pages Customer will get their required services. Security Concern Hacking, Phracking Phishing, Vishing etc Incorrect account linkage Fraudulent balance transfer Unauthorised access Cyber-related frauds Lack of segregation of duties Incorrect Firewall configuration Insufficient built in application controls Unstructured change management procedures Audit Program of Internet Banking Security policy User inentity & authentication Access control to operating staff – proper segregation Sysadmin roles & responsibilities Firewall configuration Live & test environment separation Network security Router configuration Web server security Built in operation control Key Management procedure HSM/SSM security Change Management process Data/information/system security Internet banking systems have security features such as separate transaction passwords, two factor authentication, multi-channel process for registering payees, upper limit on transaction value and SMS alerts to customers. Appropriate verification procedures should also be incorporated at all channels such as phone banking, ATMs, branches and internet to ensure that only genuine transactions are put through. 36 ujvala consultants Naavi Defeating 2-factor •Vishing attacks –Phisher poses as Bank’s call center personnel on telephone and requests customer for SMS OTP for verification •Smartphone malware to capture OTP –Malware on symbian and Palm OS for stealing sms from banks • Physical SIM replacement – Multiple cases seen in India over last year Enterprise Security- trends & concepts Phishing, NetBanking & Call Center Fraud Example Card Application My Accounts Internet Banking Account Balance Uses Harvested Web Credentials Get Personal Data from Autoforms Authenticate using Personal Details and gets new PIN Request Transfer Account Id 12345678 Passcodes godisGreat 2 Factor Auth Address Belapur DOB 15 Aug 1947 Products Card, Current Mother’s Name Sheela Call Center Customer Sales Officer Discussion Room Reception Universal Teller Customer Care Team Customer Waiting Area Internal Transaction Fraud • 30 crore transferred in 12 minutes using RTGS • Fraud transactions were carried out early morning before the branch is fully • • • • • operational Bank employee logs in with an user-id with “Maker” privileges Creates a RTGS transaction for 17 Crore debiting a corporate account in another branch. Beneficiary is a corporate account in external bank Logs out and Logs in from same machine with user-id with “Checker” privileges and approves transaction Repeats the same cycle to put a second RTGS transaction of 13 Crore from same account All fraud transactions were carried out from a new IP in the branch subnet range Presentation Name Risk Based Authentication – Internet Banking Token, Knowledge Based, SMS, Soft tokens, Device Based, Interactive Customer Challenge Policies Block Fail High Risk Login /Transaction activity Pass Real Time Risk Assessment Continue Low Risk Risk Based Authentication Flow Cash Management System Exclusive utility for all India based customers Collection & Payment at different location – large scale High volume of disbursement for salary, dividend payment Need not open account in multiple centres Multiple centres authorised to receive cheques etc. Credit to base account on same day subject to limit MIS generated, partywise, location wise report available Information through e-mail Parameter setting Clearing cycle Credit limit Slab maintenance Interest calculation Processing charges Waiver of charges Validation of data Encryption Controls Calculation process to be verified Any modification allowed in middle? Integrity of data – implement encryption Security on data moving through internet Authentication & verification EOD processing Pooling account – reconciliation- zeroise daily Interface with CBS Built in controls for exception reporting Audit trail to be maintained. Real Time Gross Settlement Inter Bank Money transfer system No waiting period- immediate within 2 hours All transaction are gross, reflected in central bank account Payment is final & irrevokable Minimum amount 1 lac, no upper limit Debit first to customer account & credit through RBI Customer make the application, rest is automatic Correct account number and IFSC code of the Bank branch Money will return within 2 hours, if not credited. RTGS information Amount to be remitted Customer account number Name of beneficiary Bank Name of beneficiary Account number of Beneficiary IFSC Code Type of account RTGS Technology Routed through INFINET SFMS formats are used for messages RBI CBS used mainframe to handle the system Inter Bank Fund Transfer Processor (IFTP) & Integrated Accounting System of RBI used. Message in standard MQ series software of IBM RTGS Client software is participant interface-PI PI processes the inward and outward messages IFTP transmit it to RTGS of RBI From RBI it will travel to destination Bank in the same way. RTGS RTGS Message Flow Participant Interface Inter Bank Fund Transfer Processor at RBI RTGS System at RBI Communication Systems Encryption Process of Transactions PI Interface - Gateway Module - Outward Message Manager at OMM server - Inward Message Manager at IMM server User Control Tool Settlement RTGS