Topic 2 – Lesson 4 Packet Filtering
advertisement

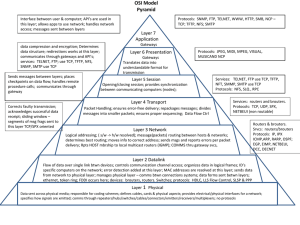
Topic 2 – Lesson 4 Packet Filtering Part I 1 Basic Questions What is packet filtering? What elements are inside an IP header? What is the size for each such element? What elements are inside a TCP header? What is the size for each such element? Assume client A with (5.6.7.8:1078) wants to establish a TCP connection with server B (1.2.3.4: 80), explain the TCP 3-Way Shake process step-by-step. Compare TCP with UDP Discuss Example 1: Explain Figure 2-5 Explain the 4 policy rules one-by-one Explain the 6 firewall rules one-by-one 2 What is packet filtering? Blocks/filters traffic from and to the internal network Hardware can be called: Screening Router Firewall accepts or blocks data based on packet header Network Layer! Does NOT scan content Firewall Policy describes rules for allowing/rejecting packets 3 What elements are inside an IP header? What is the size for each such element? The 4 info: Source IP: source hotel building street address Source port: room number Dest Ip: dest hotel Dest port: room number Source / Dest IP (both 32 bits) Protocol (8bits) (TCP? UDP?) Protocol can also be ICMP 4 What elements are inside a TCP header? What is the size for each such element? Source / Dest Ports (16bits) Contain ACK/SYN flags (1bit each) 5 How to establish a TCP connection between two ports? A TCP connection Step 1: establish the connection Step 2: send the messages back and forth Step 3: terminate the connection A phone call session Step 1: Dial the phone number Step 2: do talking Step 3: hang up Step 1 includes three sub-steps! The three sub-steps are called the TCP 3-way handshake. 6 TCP 3-way handshake A . IP # Port # ACK=0 SYN=1 ACK=1 SYN=1 . B IP # Port # . Note: A and B are two programs ACK=1 SYN=0 . 7 Assume client A with (5.6.7.8:1078) wants to establish a TCP connection with server B (1.2.3.4: 80), explain the TCP 3-Way Shake process step-by-step. 1st Step: Connection request by client A : Contains source IP(5.6.7.8), source port(1078), and destination IP (1.2.3.4), destination Port(80) . Also has SYN flag is set to 1, ACK is 0 2nd Step: the ip 1.2.3.4 will acknowledge by sending ACK flag (set to 1). Source 1.2.3.4 destination is 5.6.7.8 3rd Step: the original IP of 5.6.7.8 sends back to 1.2.3.4 ACK 1 SYN 0. Additional comments: SYN flag is used to setup TCP connection, ACK flag is used to acknowledge receipt of a packet. 8 Compare TCP with UDP header information exactly same UDP connectionless, no flags Unlike TCP, UDP has no way of checking if packet successfully transmitted Block all packets in order to block UDP session UDP= User Datagram Protocol 9 Explain Figure 2-5 Telnet service can go out except for one user No UDP packets allowed Incoming Telnet packets allowed from external servers to internal clients Who is inside and who is outside? Inside network=above firewall 10 Figure 2-5 132.28.6.4 Server (telnet listens on 23) Incoming packets Firewall Outgoing packets Internet 11 Explain the 4 policy rules one-by-one (Example 1) 1. No incoming telnet service (request) should be processed 2. Outgoing telnet requests are OK 3. Computer 132.28.6.4 cannon do Telnet 4. UDP packets are not allowed 12 The 6 Packet Filtering Rules 13 Explain the 6 firewall rules one-by-one (Example 1) Rule A: Denies any incoming TCP packets that attempt to open a Telnet connection Rule B: Denies any outgoing Telnet packets from internal client 132.28.6.4 to external telnet server. Rule C: Denies incoming packets from external telnet serves (internal host server) Rule D and E: Someone from inside firewalls can telnet out, but no one from the outside can telnet in. Connection is established starting from the inside What’s the difference between telnet in and telnet out? Telnet in= Internet client to Telnet server on network internally Telnet out= Client on the network; the server is on the Internet Rule F: Denies any incoming UDP packets Firewall rules are processed sequentially 14 How to enforce policy rule 1 Policy rule 1: no incoming telnet service We can enforce this policy rule by a single packet filtering rule which has the following field: RULE #: RULE A FIELD 1: source address Field 2: destination Inside IP (the IP of the internal telnet server) F3: direction External IP (outside IP) inbound F4: source port -- any port (no restriction) F5: dest port -- 23 (telnet server) F6: protocol -- TCP F7: ACK -- 0 F8: Action -- deny 15 Policy rule 2: outgoing telnet requests OK To enforce this policy rule, we need TWO packet filtering rules We need two rules because even if an internal employee telnets out, he needs to receives packets from the outside telnet server Rule D: permit outgoing packets to the outside telnet server So the source IP must be an internal IP; the dest IP must be an outside IP; the source port can be any; but the dest port must 23; Dir4ection: outbound Protocol: TCP ACK: 0 or 1 -- we need to allow both otherwise the telnet connection can NOT be established. Rule E: permit incoming packets from the outside telnet server 16 Policy rule 2 – cont’d Rule E: permit incoming packets from the outside telnet server Source IP: outside Dest IP; inside Direction: incoming - inbound TCP Source port: 23 (***) Dest port (internal telnet client): any Permit ACK: 1 (********) ACK canNOT be 0 because we do NOT allow an outside telnet server to initiate a connection; actually a Telnet server should NEVER initiate a connection 17 Rule A vs. Rule E Rule A : no incoming telnet service request Rule E: allow incoming telnet packets from an outside telnet server 18 Policy Rule 3: Why is Rule C Redundant? Rule B already specifies host is not able to establish telnet session, so no incoming traffic from a telnet server. If hacker spoofs a packet, and rule C is removed then the packet goes through Will this packet be a problem for the network? No packet like a car, without rule c, packet will get in, packet will die there, packet will not be processed because no telnet session is established. No damage 19 Policy rule 4: Do you think Rule F is enough to block all UDP Packets? Not enough, resources inside can cause damage to outside, if an internal resource gets hacked, it can cause problems for another network. Have to block all UDP going out to be safe. UDP same header information as TCP, there is no way to tell if it is a response or if it is from a session already in progress. UDP no 3 way handshake Worm Slammer- Worm show malicious UDP packets can be sent from inside out to outside computers 20 Rule A and Rule E conflict, how so? Rule A doesn’t give a port number, but Rule E uses port 23. Process rules in order, fail Rule A first before it gets to E. Rule A blocks incoming requests to create a new TCP session, where Rule E allows already established sessions to continue Look at ACK flag 21 Rule B and Rule D conflict, how so? B denies all outgoing telnet packets from an internal server, D does the opposite If D allows outgoing telnet sessions and B denies the outgoing session through the host, is there a point to having written rule B? B trumps D. Rule B will kill packet, if not from the host it will go through rule B. Why is the ACK permitting anything, and in Rule B ACK is set to 1 or 0? Writing 0 or 1 can be replaced by the * 22 Rule C and Rule E conflict, how so? E allows incoming packets, but C denies incoming packets Order doesn’t matter, need both for it to be true, but only 1 to be false to deny packet is there a reason to have D and E since they allow everything? Yes, you want to specify what you allow. Packets that go through rule set are denied by default. Depends on how the firewalls are setup. 23