Computer Security Risks
advertisement
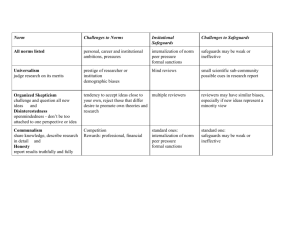
Computer Security Risks Definición: • Un riesgo de seguridad en computadoras es cualquier evento o acción que pueda causar pérdida o daño al hardware, software, datos, información, o capacidad de procesamiento. Computer crime • Cualquier acto ilegal que envuelva el uso de un sistema computadorizado • Cybercrime se refiere a actos ilegales llevados a cabo en linea o a través del internet Cybercrime • Hacker • Cracker • Corporate spy • Unethical employees • Cyberextortionist • Cyberterrorist Internet & Network attacks • Online security service – web site donde se evalua el computador para verificar la vulnerabilidad de este para Internet o e-mails Malware (malicious software) • Computer virus • Worms • Trojan horse • Back doors • spyware Safeguards • Firewalls • Intrusion Detection Software • honeypots Unauthorized Access and Use (Safeguards) • Identifying and Authenticating Users * user names & passwords * possessed objects * biometric devices Hardware Theft (safeguards) • Cables that lock the equipment to a desk Software Theft • Steals software media • Intentionally erases programs • Illegally copies Software Theft (safeguards) • License agreement • Character identification number Information Theft (safeguards) • Encryption Name Method Plaintext Ciphertext Transposition Switch the order of characters SOFTWARE OSTFAWER Expansion Insert characters between existing characters USER UYSYEYRY Substitution Replace characters with other characters INFORMATION WLDIMXQUWIL Compaction Remove characters and store elsewhere ACTIVATION ACIVTIN Information Theft (safeguards) • Digital certificates • Digital signature • Secure Sockets Layer (SSL) • Secure HTTP (S-HTTP) System Failure • Uninterruptible Power Supply (UPS) • Backup Wireless Security • • • • Firewalls Wired Equivalent Privacy (WEP) Wi-Fi Protected Access (WPA) 802.11i network Computer Ethics • Guias morales que dirigen el uso de computadoras y de sistemas de información. • Areas de discusión: – – – – – – Uso no autorizado de computadoras y networks Piratería de software Derechos de propiedad intelectual Códigos de conducta Privacidad de la información Presición de la información Issue 1) A company requires employees to wear badges that track their whereabouts while at work. 2) A supervisor reads an employee’s e-mail. 3) An employee uses his computer at work to send e-mail messages to a friend. 4) An employee sends an e-mail message to several coworkers and blind copies his supervisor. 5) An employee forwards an e-mail message to a third party without permission from the sender. 6) An employee uses her computer at work to complete a homework assigment for school. 7) The vice president of your Student Government Association (SGA) downloads a photograph from the web and uses it in a flier recruiting SGA members. 8) A student copies text from the web and uses it in a research paper for his English Composition class. 9) An employee sends political campaign material to individuals on her employer’s mailing list. 10) As an employee in the registration office, you have access to student grades. You look up grades for your friends, so they do not have to wait for delivery of grades reports from the postal service. 11) An employee makes a copy of software and install it on her home computer. No one uses her home computer while she is at work, and she uses her home computer only to finish projects from work. 12) An employee who has been laid off install a computer virus on his employer’s computer. 13) A person designing a web page finds one on the web similar to his requirements, copies it, modifies it, and published it as his own web page. 14) A student researches using only the web to write a report. 15) In a society in which all transactions occur online (a cashless society), the government tracks every transaction you make and automatically deducts taxes from your bank account. 16) Someone copies a well-known novel to the web and encourages others to read it. Ethical Unethical Information Technology Code of Conduct 1) Computers may not be used to harm other people. 2) Employees may not interfere with others’ computer work. 3) Employees may not meddle in others’ computer files. 4) Computers may not be used to steal. 5) Computers may not be used to bear false witness. 6) Employees may not copy or use software illegally. 7) Employees may not use others’ computer resources without authorization. 8) Employees may not use others’ intellectual property as their own. 9) Employees shall consider the social impact of programs and systems they design. 10) Employees always should use computers in a way that demonstrates consideration and respect for fellows humans. Intellectual Property Rights • Are the rights to which creators are entitled for their work. • Copyright gives authors and artist exclusive rights to duplicate, publish, and sell their materials. Information Privacy • The right of individuals and companies to deny or restrict the collection and use of information about them. Techniques that companies and employers use to collect personal data • Electronic Profiles • Cookies • Spyware and Adware • Spam • Phishing Social Engineering • Is defined as gaining unauthorized access or obtaining confidential information by taking advantage of the trusting human nature of some victims. Health Concerns of Computer Use • • • • • Repetitive strain injury (RSI) Computer vision syndrome (CVS) Ergonomics and Workplace Design Computer Addition Green computing Green Computing Suggestions • Use computers and devices that comply with the ENERGY STAR program. • Do not leave the computer running overnight • Turn off the monitor, printer, and other devices when not in use. • Use paperless methods to communicate. • Recycle paper. • Buy recycled paper. • Recycle toner cartridges. • Recycle old computers and printers. • Telecommute (save gas).