NAC
advertisement

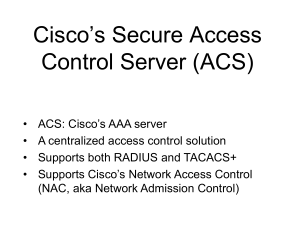
Network Access Control • • • http://en.wikipedia.org/wiki/Network_Access_Control “an approach to computer network security that attempts to unify endpoint security technology (such as antivirus, host intrusion prevention, and vulnerability assessment), user or system authentication and network security enforcement” Aim: to control endpoint security by unifying it with network device security and the whole network Result: End devices that do not comply to the set security policies are identified and quarantined. Why and What? • Why NAC? http://www.ashimmy.com/2007/03/a_brief_history.html – “The biggest driver for NAC was the realization that after spending billions on the perimeter, we still were not any more secure.” Why? Internal threats … • What is NAC? http://www.ashimmy.com/2007/03/nac_bust_or_boo.html – “The original concept of NAC was performing pre-admission health or profile checks on devices as they sought to enter the network. If the device failed they were denied access or quarantined. Then we added post-admission vulnerability scans, then IDS detection, behavior based detection, identity based access controls, etc. Before you know it, anything that has anything to do with getting on the network and staying there is part of NAC.” T. A. Yang Network Security 2 NAC: Goals • http://en.wikipedia.org/wiki/Network_Access_Control 1. Mitigation of non-zero-day attacks (?) - To prevent end-stations that lack antivirus, patches, or host intrusion prevention software from accessing the network and placing other computers at risk of cross-contamination 2. Policy enforcement - To allow network operators to define policies, such as the types of computers or roles of users allowed to access areas of the network, and enforce them in switches, routers, and network middleboxes (like firewalls). 3. Identity and access management - Instead of using IP addresses, NAC enforces network access based on authenticated user identities, at least for user end-stations such as laptops and desktop computers. Support for NAC • Cisco: Network Admission Control (NAC), since 2003/2004 - A brief history of NAC (3/8/2007) http://www.ashimmy.com/2007/03/a_brief_history.html • Other companies joined and pushed out their “NAC” products (next page) - A 2006 survey by Network Computing (local copy) • Microsoft’s response: Network Access Protection, NAP (first introduced in Windows Server 2008) http://en.wikipedia.org/wiki/Network_Access_Protection • Joel Conover, NAC Vendors Square Off, Network Computing, 7/6/2006 (local copy) T. A. Yang Network Security 5 • Source: http://www.forescout.com/wpcontent/media/ForresterVendorSummary_ForeScout_publishable_2011.pdf T. A. Yang Network Security 6 • Gartner’s Magic Quadrant for NAC: published 12/2011 http://www.gartner.com/tech nology/reprints.do?id=118VNF2C&ct=120119&st=sb (local copy) T. A. Yang Network Security 7 • NAC vendors compared (using comparison tools at Mosaicsecurity.com) T. A. Yang Network Security 8 NAC Basic Concepts Source: http://en.wikipedia.org/wiki/Network_Access_Control • Pre-admission vs Post-admission enforcement • Agent vs Agentless data collection – An agent s/w runs on the endpoint to report the status – Agentless devices • Some devices do not support NAC agent s/w • e.g., printers, scanners, phones, photocopiers, and other special devices • NAC uses scanning and network inventory techniques (whitelisting, blacklisting, ACLs) to discern those characteristics remotely T. A. Yang Network Security 9 NAC Basic Concepts Source: http://en.wikipedia.org/wiki/Network_Access_Control • Out-of-band vs Inline solutions – Inline: A single box acts as an internal firewall for access-layer networks and enforces the policy – Out-of-band: Agents on end-stations report information to a central console, which in turn control switches to enforce policy. T. A. Yang Network Security 10 NAC Basic Concepts Source: http://en.wikipedia.org/wiki/Network_Access_Control Quarantine vs captive portals for remediation • Quarantine: A non-compliant end-station is only allowed to access a restricted network with patch and update servers. • Captive portals: The captive portal technique forces an HTTP client on a network to see a special web page before gaining full access. – In NAC, a captive portal intercepts HTTP access to web pages, redirecting users to a web application that provides instructions and tools for updating their computers. T. A. Yang Network Security 11 Cisco’s NAC • Source: http://www.cisco.com/en/US/prod/collateral/vpndevc/ps5707/ps5923 /product_data_sheet0900aecd80119868.html • NAC is a set of technologies and solutions built on an industry initiative led by Cisco Systems®. • NAC uses the network infrastructure to enforce security policy compliance on all devices seeking to access network computing resources, thereby limiting damage from emerging security threats such as viruses, worms, and spyware. T. A. Yang Network Security 12 Why NAC? • Endpoints that do not comply with established security policies pose a threat and can introduce a security risk into the network. • Goal of NAC: to prevent vulnerable and noncompliant hosts from obtaining network access Q: Why isn’t user authentication (like 802.1x) sufficient? Ans? T. A. Yang Network Security 13 Cisco’s approach to NAC • The NAC solution uses the network access devices (NAD) to protect the network infrastructure from any endpoint seeking network access. – Only compliant endpoints are granted access. – Noncompliant devices are denied access and quarantined for remediation. T. A. Yang Network Security 14 • Source: http://www.cisco.com/en/US/solutions/ns340/ns394/ns171/ns466/ns 617/net_design_guidance0900aecd80417226.pdf T. A. Yang Network Security 15 Cisco’s NAC Solutions: Two options 1. The NAC Appliance approach - Aka Cisco Clean Access (CCA) appliance A Cisco packaged solution CCA agent provides posture information; Cisco Security Agent (CSA) provides protection. 2. The NAC Framework approach T. A. Yang Network Security 16 Cisco’s NAC Solutions: Two options 2. The NAC Framework approach – Built on NAC-enabled network access devices (NAD), Cisco or non-Cisco – Compliant endpoints are granted access to the network – Noncompliant endpoints are placed in quarantine for remediation c.f., Figure 13-2 T. A. Yang Network Security 17 Cisco NAC Solution: two options • Figure 13-2 T. A. Yang Network Security 18 Cisco Security Agent (CSA) • Cisco’s host intrusion prevention tool – Details in Ch 21 – On June 11, 2010, Cisco announced the end-of-life and end-ofsale of CSA. (source: http://en.wikipedia.org/wiki/Cisco_Security_Agent) • CSA components – CSA endpoints: enforcing security policies received from the management server, sending events, interacting with the user – CSA management server: a repository of configuration database – CSA management console: an admin web-based user interface and policy configuration tool T. A. Yang Network Security 19 Cisco’s NAC Framework source: http://www.cisco.com/en/US/solutions/collateral/ns340/ns394/ns171/ns466/ns6 17/net_implementation_white_paper0900aecd80217e26.pdf (2005) T. A. Yang Network Security 20 1. 2. 3. 4. 5. 6. 7. 8. 9. Client sends a packet through a NAC-enabled router. NAD begins posture validation using EOU. Client sends posture credentials using EOU to the NAD. NAD sends posture to Cisco ACS using RADIUS. Cisco Secure ACS requests posture validation using the Host Credential Authorization Protocol (HCAP) inside an HTTPS tunnel. Posture validation/remediation server sends validation response of pass, fail, quarantine, and so on. To permit or deny network access, Cisco Secure ACS sends an accept with ACLs/URL redirect. NAD forwards posture response to client. Client is granted or denied access, redirected, or contained. T. A. Yang Network Security 21 • Cisco Trust Agent (CTA) http://www.cisco.com/en/US/prod/collateral/vpndevc/ps5707/ps5923/product_data_s heet0900aecd80119868.html • A posture agent (PA) serves as the single point of contact on the host for aggregating credentials from all posture plugins and communicating with the network. • This module also provides a trusted relationship with the network for the purposes of exchanging these posture credentials. T. A. Yang Network Security 22 • Cisco Trust Agent (CTA) http://www.cisco.com/en/US/prod/collateral/vpndevc/ps5707/ps5923/product_data_s heet0900aecd80119868.html (2009) • Acts as a middleware component that takes host policy information and securely communicates the information to the AAA policy server • Interacts directly with "NAC-enabled" applications running on the host without user intervention • Can communicate at Layer 3 (EAP over UDP) or Layer 2 (802.1x supplicant) with the NADs – The supplicant is able to use the EAP-FAST protocol to carry both identity and posture information within the 802.1x transport. • Free to download T. A. Yang Network Security 23 • Cisco Trust Agent (CTA) http://www.cisco.com/en/US/prod/collateral/vpndevc/ps5707/ps5923/product_data_s heet0900aecd80119868.html T. A. Yang Network Security 24 • Source: http://www.cisco.com/en/US/solutions/ns340/ns394/ns171/ns466/ns 617/net_design_guidance0900aecd80417226.pdf (2006) T. A. Yang Network Security 25 T. A. Yang Network Security 26 source: http://www.cisco.com/en/US/solutions/collateral/ns340/ns394/ns171/ns466/ns6 17/net_implementation_white_paper0900aecd80217e26.pdf (2005) T. A. Yang Network Security 27 NAC vs 802.1X for endpoint security • Source: http://www.cloudcentrics.com/?p=579 • 802.1x technologies do a great job in protecting network assets before they are utilized on the network. Nonauthorized machines generally never get on the network. In addition 802.1x technologies have greater flexibility in provisioning users in different types of VLANs for isolation such as guest or remediation VLANs. • NAC technologies do a great job in assuring when a user is on a network they meet minimum criteria of software patches to stay on the network. If they do not meet these requirements upstream devices, such as firewalls from accessing the network, block them. Q: Agree ? T. A. Yang Network Security 28 NAC Comparison Guide • Source: http://www.itsecurity.com/whitepaper/pdf/nac-comp-guide_8-07.pdf (2007), local copy • Vendors included in the comparison: Bradford Networks, Check Point Software Technologies, Cisco Systems, ConSentry Networks, Elemental Security, Enterasys Networks, ForeScout, HP, Infoblox, InfoExpress, Insightix, Juniper Networks, Lockdown Networks, McAfee, Mirage Networks, Nevis Networks, Nortel Networks, Senforce Technologies, Sophos, StillSecure, Symantec, Trend Micro, and Vernier Networks • Comparison criteria: – – – – – – – Product type (s/w, appliance) Endpoint assessment & compliance? User authentication? Remediation? Preadmission? Post-Admission? Price T. A. Yang Network Security 29 More recent lists and comparisons • By Mosaic Security Research – Source: https://mosaicsecurity.com/categories/81-network-accesscontrol?direction=asc&sort=vendors.name – 39 vendors (as of 7/2012) – Product info, resources, awards, etc. • By JafSec.com – Source: http://jafsec.com/Network-Access-Control/Network-Access-Control-AB.html – About 29 vendors (as of 7/2012) – Include two open source NACs: FreeNAC, PacketFence T. A. Yang Network Security 30 More References • Joel Snyder, Network access control vendors pass endpoint security testing - Alcatel-Lucent, Bradford, Enterasys, ForeScout, McAfee go above and beyond, Network World , June 21, 2010 http://www.networkworld.com/reviews/2010/062110-network-accesscontrol-test-end-point.html • Tutorial: Network Access Control (NAC), July 17, 2007 http://www.networkcomputing.com/data-protection/229607166?pgno=3 • Good explanation of basic NAC concepts: http://en.wikipedia.org/wiki/Network_Access_Control • FAQ for Network Admission Control (NAC), 2006: http://www.cisco.com/en/US/solutions/ns340/ns394/ns171/ns466/ns617/net _design_guidance0900aecd8040bc84.pdf T. A. Yang Network Security 31