PPT
advertisement

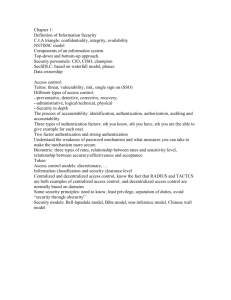
Network security and Hot topics in networking EECS 489 Computer Networks http://www.eecs.umich.edu/courses/eecs489/w07 Z. Morley Mao Wednesday, April 11, 2007 Announcements Agenda today: Icecream to celebrate almost finishing EECS489 Finish up network security Where to go from here? Hot topics in networks. Course evaluation (need volunteer) Practice final is posted (announcement page) Solution available next Monday Mandatory PA3 Demo: Starting Thursday (4/12), last day is Friday (4/20), signup available. Next Monday 4/16 Course summary and review for final Final exam: 4/19 Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography 8.3 Authentication 8.4 Integrity 8.5 Key Distribution and certification 8.6 Access control: firewalls 8.7 Attacks and counter measures 8.8 Security in many layers 8.8.1. Secure email 8.8.2. Secure sockets 8.8.3. IPsec 8.8.4. Security in 802.11 Secure e-mail Alice wants to send confidential e-mail, m, to Bob. KS m K (.) S + KS + . K B( ) + KS(m ) KS(m ) + KB(KS ) - Internet + KB(KS ) KB Alice: . KS( ) generates random symmetric private key, KS. encrypts message with KS (for efficiency) also encrypts KS with Bob’s public key. sends both KS(m) and KB(KS) to Bob. KS - . K B( ) - KB m Secure e-mail Alice wants to send confidential e-mail, m, to Bob. KS m K (.) S + KS + . K B( ) + KS(m ) KS(m ) + KB(KS ) - Internet + KB(KS ) KB Bob: . KS( ) uses his private key to decrypt and recover KS uses KS to decrypt KS(m) to recover m KS - . K B( ) - KB m Secure e-mail (continued) • Alice wants to provide sender authentication message integrity. + - KA m H(.) - . KA( ) - - KA(H(m)) KA(H(m)) + Internet m • Alice digitally signs message. KA + . KA( ) m H(m ) compare . H( ) H(m ) • sends both message (in the clear) and digital signature. Secure e-mail (continued) • Alice wants to provide secrecy, sender authentication, message integrity. - KA m . H( ) - . KA( ) - KA(H(m)) + KS . KS( ) + m KS + . K B( ) + Internet + KB(KS ) KB Alice uses three keys: her private key, Bob’s public key, newly created symmetric key Pretty good privacy (PGP) Internet e-mail encryption scheme, defacto standard. uses symmetric key cryptography, public key cryptography, hash function, and digital signature as described. provides secrecy, sender authentication, integrity. inventor, Phil Zimmerman, was target of 3-year federal investigation due to US export regulations. A PGP signed message: ---BEGIN PGP SIGNED MESSAGE-Hash: SHA1 Alice: I developed a new worm that can exploit the zeroday flaw on Windows Vista. Bob ---BEGIN PGP SIGNATURE--Version: PGP 5.0 Charset: noconv yhHJRHhGJGhgg/12EpJ+lo8gE4vB3 mqJhFEvZP9t6n7G6m5Gw2 ---END PGP SIGNATURE--- Secure sockets layer (SSL) transport layer security to any TCPbased app using SSL services. used between Web browsers, servers for e-commerce (https). security services: server authentication data encryption client authentication (optional) server authentication: SSL-enabled browser includes public keys for trusted CAs. Browser requests server certificate, issued by trusted CA. Browser uses CA’s public key to extract server’s public key from certificate. check your browser’s security menu to see its trusted CAs. SSL (continued) Encrypted SSL session: Browser generates symmetric session key, encrypts it with server’s public key, sends encrypted key to server. Using private key, server decrypts session key. Browser, server know session key All data sent into TCP socket (by client or server) encrypted with session key. SSL: basis of IETF Transport Layer Security (TLS). SSL can be used for non-Web applications, e.g., IMAP. Client authentication can be done with client certificates. IPsec: Network Layer Security Network-layer secrecy: sending host encrypts the data in IP datagram TCP and UDP segments; ICMP and SNMP messages. Network-layer authentication destination host can authenticate source IP address Two principle protocols: authentication header (AH) protocol encapsulation security payload (ESP) protocol For both AH and ESP, source, destination handshake: create network-layer logical channel called a security association (SA) Each SA unidirectional. Uniquely determined by: security protocol (AH or ESP) source IP address 32-bit connection ID Authentication Header (AH) Protocol AH header includes: authentication, data connection identifier integrity, no authentication data: confidentiality source-signed message AH header inserted digest calculated over between IP header, data original IP datagram. field. next header field: protocol field: 51 specifies type of data (e.g., TCP, UDP, ICMP) intermediate routers process datagrams as usual provides source IP header AH header data (e.g., TCP, UDP segment) ESP Protocol provides secrecy, host ESP authentication authentication, data field is similar to AH integrity. authentication field. data, ESP trailer encrypted. Protocol = 50. next header field is in ESP trailer. authenticated encrypted IP header ESP ESP ESP TCP/UDP segment header trailer authent. IEEE 802.11 security War-driving: drive around Bay Area, see what 802.11 networks available? More than 9000 accessible from public roadways 85% use no encryption/authentication packet-sniffing and various attacks easy! Securing 802.11 encryption, authentication first attempt at 802.11 security: Wired Equivalent Privacy (WEP): a failure current attempt: 802.11i Wired Equivalent Privacy (WEP): authentication as in protocol ap4.0 host requests authentication from access point access point sends 128 bit nonce host encrypts nonce using shared symmetric key access point decrypts nonce, authenticates host no key distribution mechanism authentication: knowing the shared key is enough WEP data encryption Host/AP share 40 bit symmetric key (semi permanent) Host appends 24-bit initialization vector (IV) to create 64-bit key 64 bit key used to generate stream of keys, kiIV kiIV used to encrypt ith byte, di, in frame: ci = di XOR kiIV IV and encrypted bytes, ci sent in frame 802.11 WEP encryption IV (per frame) KS: 40-bit secret symmetric key plaintext frame data plus CRC key sequence generator ( for given KS, IV) k1IV k2IV k3IV … kNIV kN+1IV… kN+1IV d1 d2 d3 … dN CRC1 … CRC4 c1 c2 c3 … cN cN+1 … cN+4 Figure 7.8-new1: 802.11encryption WEP protocol Sender-side WEP 802.11 IV header WEP-encrypted data plus CRC Breaking 802.11 WEP encryption Security hole: 24-bit IV, one IV per frame, -> IV’s eventually reused IV transmitted in plaintext -> IV reuse detected Attack: Trudy causes Alice to encrypt known plaintext d1 d2 d3 d4 … IV Trudy sees: ci = di XOR ki Trudy knows ci di, so can compute kiIV IV IV IV Trudy knows encrypting key sequence k1 k2 k3 … Next time IV is used, Trudy can decrypt! 802.11i: improved security numerous (stronger) forms of encryption possible provides key distribution uses authentication server separate from access point Wi-Fi Protected Access (WPA) implements the majority of this standard 802.11i: four phases of operation STA: client station AP: access point AS: Authentication server wired network 1 Discovery of security capabilities 2 STA and AS mutually authenticate, together generate Master Key (MK). AP servers as “pass through” 3 STA derives Pairwise Master Key (PMK) 4 STA, AP use PMK to derive Temporal Key (TK) used for message encryption, integrity 3 AS derives same PMK, sends to AP EAP: extensible authentication protocol EAP: end-end client (mobile) to authentication server protocol EAP sent over separate “links” mobile-to-AP (EAP over LAN) AP to authentication server (RADIUS over UDP) wired network EAP TLS EAP EAP over LAN (EAPoL) IEEE 802.11 RADIUS UDP/IP SSH (rfc4251) Establishes a secure channel between a local and remote computer Uses public-key crypto to authenticate remote host and user Provides confidentiality, integrity Authentication Password-based Public-key based • Public and private key pair generation using ssh-keygen Host keys ssh liberty.eecs.umich.edu @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ @@@@@@@@@@@@@@@@@@@@@ @ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! @ @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ @@@@@@@@@@@@@@@@@@@@@ IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY! Someone could be eavesdropping on you right now (man-in-the-middle attack)! It is also possible that the RSA host key has just been changed. The fingerprint for the RSA key sent by the remote host is 00:61:14:7c:76:02:5a:94:42:a1:8e:ce:e1:ef:d7:9a. Please contact your system administrator. Add correct host key in /n/edinburgh/x/zmao/.ssh/known_hosts to get rid of this message. Offending key in /n/edinburgh/x/zmao/.ssh/known_hosts:276 Password authentication is disabled to avoid man-in-the-middle attacks. Keyboard-interactive authentication is disabled to avoid man-in-the-middle attacks. Enter passphrase for key '/n/edinburgh/x/zmao/.ssh/id_rsa': One time password RSA SecurID tokens (has a built-in accurate clock) Opposite of static passwords constantly altering passwords Password generation algorithms math algorithm: generates next password based on the previous one, e.g., hash chain. time sychronization btw. client and authentication server math algorithm: next password based on a challenge and counter (e.g., used by smart cards). Network Security (summary) Basic techniques…... cryptography (symmetric and public) authentication message integrity key distribution …. used in many different security scenarios secure email secure transport (SSL) IP sec 802.11 What are hot topics in networking? Information sharing Fighting Coordinated Attackers with CrossOrganizational Information Sharing Social networks SPACE: Secure Protocol for Address Book based Connection Establishment Exploiting Social Networks for Internet Search Detect Sybil Attacks Revisiting Internet design Decongestion control IP multicast Evolutionary PKI, security through publicity What are hot topics in networking? next-generation Internet new addressing, routing schemes Churn in distributed systems Troubleshooting, diagnosis, mitigation Detecting Evasion Attacks at High Speeds without Reassembly New network applications Internet is not the only network “New” networks vehicular networks sensor networks wireless networks cellular networks delay-tolerant networks networks in rural areas integration with Internet Biggest problem with today’s Internet: Lack of security Lack of manageability and QoS assurance Other desirable properties: mobility, faultresilience. Network security is an ongoing arms race Measuring Internet-scale Adversaries Endemic worms, malicious scanning Huge dataset headache Huge privacy/legal/policy/commercial hurdles Attacks on passive monitoring • state, analysis flooding • bugs in analyzers: adversary crafts such a packet, overruns buffer, causes analyzer to execute arbitrary code • evasion, confuse monitoring analysis algorithms Defense Automated response Unwanted traffic spam reconnaissance, probe traffic attack traffic misconfigurations