Secure Remote Access & Lync
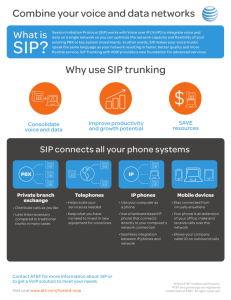
advertisement

Secure Remote Access & Lync Ilse Van Criekinge http://blogs.technet.com/ilvancri @ivcrieki Session Objectives and Takeaways • Session Objectives • Overview of typical Lync Server Edge configurations • DNS Load Balancing and Hardware Load Balancing • NAT support for Edge Deployment • Reverse Proxy • ICE • Takeaways • Understand typical Edge planning and deployment process • Understand certificate requirements for Edge and Reverse Proxy 2 Introduction 3 Conferencing Capabilities of Lync Web Conferencing Video Conferencing Audio Conferencing PSTN Conferencing Instant Messaging Conferencing Integration with thirdparty A/V SIP endpoints and MCUs ACP Integration Dial-In Conferencing Conferencing Attendant Application Conferencing Announcing Application Dial-in Conferencing Web Page Mediation Servers and Gateways or PBX Simple URLs • Lync Server 2010 • Meet • Dial-in • Admin • Scope = Global & Site • Created using PowerShell or Topology Builder Edge Server Role Lync Server Edge scenarios • External User Access • Lync clients can transparently connect to the Lync Server deployment over the public Internet • PIC • Connecting with public IM providers • Federation • Federation with other Enterprises • IM&P only, or • All modalities A/V and Application Sharing Edge Server Role Requirements • General Requirements • 64-bit Windows 2008, Windows 2008 R2 • Microsoft .NET Framework 3.5 SP1 • Windows PowerShell v2 • Cannot be collocated with any other Microsoft Lync Server role • Virtualization is supported (Windows 2008 R2 OS!) Server role Edge Server Physical Virtual CPU Memory Number of users supported CPU Memory Number of users supported 8 cores 16 GB 15,000 4 cores 5 GB 7,500 Edge Server Roles • Access Edge = handles all SIP traffic crossing the corporate firewall • Web Conferencing Edge = proxies PSOM (Persistant Shared Object Model) traffic between the Web Conferencing Server and external clients • Audio/Video Edge = provides a single trusted connection point through which audio and video traffic enters and exits your network Edge Server Role 1 IP, 2 IP, 3 IP, 4 IP, ... ? A Few Networking Lync Facts • Lync Server 2010 supports only IPv4 • It does niet support IPv6 • Can function in a network with dual IP stack enabled • Two network adapters for each Edge Server are required: • one for the internal-facing interface • one for the external-facing interface • Important: The internal and external subnets must not be routable to each other. Single IP address Edge edge.contoso.com 131.107.155.10 External SIP: 5061 Web Conf: 444 A/V Conf: 443, 3478 edge-int.contoso.com 172.25.33.10 Internal SIP: 5061 Web Conf: 8057 A/V Conf: 443, 3478 Multiple IP address Edge access.contoso.com 131.107.155.10 443, 5061 External SIP edge-int.contoso.com 172.25.33.10 webcon.contoso.com 131.107.155.20 443 External Web Conf av.contoso.com 131.107.155.30 443, 3478 External AV Edge Server Internal SIP: 5061 Web Conf: 8057 A/V Conf: 443, 3478 Edge using NAT IP addresses Public IP space IP1’ Lync Server does not need to know translated SIP and Web Conf IP IP2’ Client Clients connect to IP for A/V traffic Translated AV IP must be configured in Lync Server IP3’ IP1 External SIP IP2 External Web Conf IP3 External AV Int DNS Load Balanced Edge Public IP space DNS A records access.contoso.com IP1 and IP4 webcon.contoso.com IP2 and IP5 av.contoso.com IP3 and IP6 Client Client can retrieve and handle multiple IP addresses and can fail over DNS server returns randomized IP address DNS Load Balanced Edge using NAT Public IP space DNS A records access.contoso.com webcon.contoso.com av.contoso.com IP1’ and IP4’ IP2’ and IP5’ IP3’ and IP6’ Translated AV IP addresses must be configured in Lync Server individually IP3 to IP3’ IP6 to IP6’ IP2’ IP3’ IP4’ IP5’ IP6’ Hardware Load Balanced Edge Public IP space DNS A records access.contoso.com webcon.contoso.com av.contoso.com VIP1 VIP2 VIP3 Initial AV connection requires will land on VIP and gets forwarded. However clients will connect to Edge directly (UDP) TCP traffic continues to use VIP NAT and HLB is not possible VIP1 VIP2 VIP3 Edge Server Role INSTALLATION Edge Server Role CERTIFICATE REQUIREMENTS Certificate Requirements Edge Server Role • A single public certificate is supported in Lync for • Access Edge external interface • Web conferencing Edge external interface • A/V Authentication Edge internal interface • Edge internal interface • Can be issued by an internal CA • Subject name is typically the Edge internal interface FQDN or HWLB VIP • No subject alternative names required Requirements External Certificate • Issued by an approved public CA (http://go.microsoft.com/fwlink/?LinkId=202834) • If Edge pool, same cert on every Edge, must be exportable • Subject Name = Access Edge FQDN or HWLB VIP(Not required, but recommended (previous versions) ) • Subject Alternative Names • Access Edge external interface or HWLB VIP • Web Conferencing Edge external interface or HWLB VIP • Any SIP doman FQDN (for auto-discovery, federation) Edge Server Role DNS REQUIREMENTS DNS Requirements • DNS Entries • External DNS lookups by remote users and federated partners • Entries for DNS lookups for use by the Edge Servers within the perimeter network • Internal DNS entries for lookups by the internal clients and servers running Lync Server 2010 • Edge Server requires DNS Suffix Need client auto configuration? YES Default SIP domain FQDN = AD domain FQDN NO NO YES You are using split-brain DNS Internal DNS _sipinternaltls._tcp.<sip domain> External DNS _sip._tls. <sip domain> Use GPOs or configure clients manually You are not using split-brain DNS Internal DNS _sipinternaltls._tcp.<sip domain> sip. <sip domain> External DNS _sip._tls. <sip domain> Is Federation required? NO Internal DNS A Record internal interface External DNS A Record external interfaces YES External DNS _sipfederationtls._tcp.<sip domain> DNS Records for External Devices Type Value Note SRV Edge Server: _sipexternal._tls.<SIP domain>, and _sipexternaltls.<SIP domain> Allows external devices to connect by using SIP over TLS to the Registrar internally. Reverse proxy FQDN: <server name>.<SIP domain> Allows external devices to connect by using TLS over HTTP to the Device Update Web service. A Edge Server Role REVERSE PROXY & DIRECTOR Reverse Proxy and Director Internet Perimeter Network Internal Network Reverse Proxy Front End Remote Clients Federated Clients Anonymous Clients Edge Server Director Reverse Proxy and external access (1) • Forwards External HTTPS and HTTP traffic to Front End and Director Pool • External user access to: • • • • • • • Meeting content for meetings (HTTPS) Expand and display of distribution groups (HTTPS) Downloadable files from the Address Book Service (HTTPS) The Lync Web App client (HTTPS) The Dial-In Conferencing Settings web page (HTTPS) Location Information Service (HTTPS) Device Update Service and obtain updates (HTTP) Reverse Proxy and external access (2) • Simple URL forward to Director (recommended) • • Forwarding rule for Simple URL to a single Director (or Pool); port 443 Reverse Proxy certificate’s SAN to contain base FQDN of each Simple URL • Web External Pool traffic forwarded to pools by Reverse Proxy • • • Reverse Proxy requires a forwarding rule each Web External FQDN (Front End Pool and Director); port 443 If external Phone Devices are implemented, Reverse Proxy rule for port 80 is required Reverse Proxy certificate’s SAN to contain base FQDN of all configured Web external Pools (Front End Pool and Director) Edge Server Role RECAP DNS VS HW LOAD BALANCING DNS vs. Hardware Load Balancing DNS LB HLB Public IP addresses required Each Server x 3 (Each Server+1 VIP) x 3 Failover Support No, Delayed Failover* for: • Exchange UM (remote user) • PIC • Federation of older version of OCS Yes, instant Failover for: • Exchange UM (remote user) • PIC • Federation of older version of OCS NATing of IP addresses (Edge Server) Supported Not supported * Delayed Failover: DNS TTL period Edge Server Role XMPP Extensible Messaging and Presence Protocol (XMPP) Gateway • Features provided • Add and delete each other as contacts • Publish Presence and subscribe for each other’s Presence • Engage in one-to-one conversations • Three scenarios • Public federation with hosted network • Federation between two organizations • On-premises deployment with Jabber SIP/MTLS:5061 XMPP Gateway Edge Server Role MANAGE & CONTROL REMOTE ACCESS Manage & Control Remote Access • To support external user access, you must do both of the following: • Enable support for external user access to your organization • Configure and assign one or more policies to support external user access • Policies • External user access policies • Conferencing policies Edge Server Role CLIENT COMMUNICATIONS IM And Presence Workload Step 1. Client resolves DNS SRV record _sip._tls.<sip-domain> to Edge Server Step 2. Client connects to Edge Server SIP/MTLS:5061 Step 3. . Edge Server proxies connection to Director HTTPS: 443 SIP/MTLS:5061 Step 4. Director authenticates user and proxies connection to user’s home pool SIP/MTLS:5061 Federated IM & Presence Workloads HTTPS: 443 SIP/MTLS:5061 SIP/MTLS:5061 ICE ESTABLISHING MEDIA PATH SDP, STUN, TURN, ICE • Lync uses SDP to provide initialization parameters for media stream • Add a Media Relay (aka A/V Edge Server) • STUN reflects NAT addresses • TURN relays media packets • ICE exchanges candidates (cand) and determines optimal media path to assist media in traversing NATs without requiring the endpoints to be aware of their network topologies • All three protocols based IETF standards ICE Details • There are five phases for establishing a media path • During login • TURN Provisioning and Credentials (MRAS – Media Relay Authentication Service) • When establishing a call • Address Discovery (Allocation) (Obtain Candidate List) • Address Exchange (SIP Invite/200 OK) • Connectivity Checks • Candidate Promotion In summary, to send media into the enterprise, the external user must be authenticated and have an authenticated internal user explicitly agree to exchange media streams. Lync Server 2010 uses TCP 50,000-59,999 outbound. Lync Server 2010 federating with Office Communications Server 2007 partners continues to use the port range of 50,000 – 59,999 UDP/TCP. Federation involving Lync Server 2010 partners or Office Communications Server 2007 R2 partners will use 3478/UDP and 443/TCP, and TCP 50,00059,999 outbound Step 1. Inband Provisioning Process duing Lync Sign-In Step 2. Obtain Candidate List Step 3. Connectivity Checks Step 4. Candidate Promotion Stay up to date with TechNet Belux Register for our newsletters and stay up to date: http://www.technet-newsletters.be • Technical updates • Event announcements and registration • Top downloads Join us on Facebook Download MSDN/TechNet Desktop Gadget http://www.facebook.com/technetbe http://bit.ly/msdntngadget http://www.facebook.com/technetbelux LinkedIn: http://linkd.in/technetbelux/ Twitter: @technetbelux TechDays 2011 On-Demand • Watch this session on-demand via TechNet Edge http://technet.microsoft.com/fr-be/edge/ http://technet.microsoft.com/nl-be/edge/ • Download to your favorite MP3 or video player • Get access to slides and recommended resources by the speakers THANK YOU ilvancri@microsoft.com