Introduction to Security

Introduction to Security
Chapter 5
Risk Management: The Foundation of
Private Security
1
Risk defined:
A known threat that has unpredictable effects in either timing or extent
2 types of Risk:
1.
Pure risk
2.
Dynamic Risk
2
1. Pure Risk
The potential for injury, damage or loss with no possible benefits.
Examples:
Crime
Terrorism
Natural Disasters
3
2. Dynamic Risk
This has potential for both benefits and losses.
Examples:
Accepting checks to stimulate business
Hiring our own security personnel
4
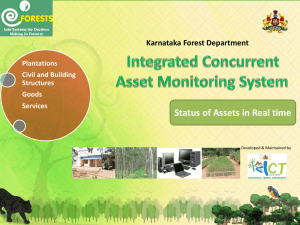
Risk Management: The Big Picture
Anticipating Risk
Recognizing Risk
Analyzing Risk
Taking steps to reduce or prevent such risks
Evaluating the Results
5
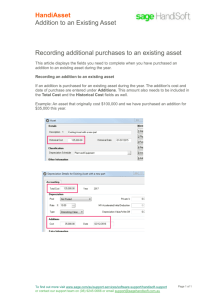
Risk Management: The Big Picture
Asset Worth
An important part of any risk management program is the worth of the asset being protected.
3 Factors:
Overall value of the asset to the organization
Immediate financial impact of losing the asset
Indirect business impact of losing the asset.
6
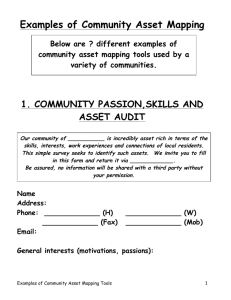
Risk Assessment
Risk Assessment is the process of identifying and prioritizing risks to a business.
“A risk assessment serves as the foundation upon which an organization builds its physical security plan.” (Fredrick, 2006, p. 19)
7
Sources of Information on Risk
Local police crime statistics
UCR reports
Internal organization documents
Prior complaints
Prior civil claims against security
Industry-related information
Law enforcement intelligence
8
3 Factors of Risk Analysis
1.
Vulnerability – where and how could losses occur
2.
Probability – analyzing those factors that favor loss
3.
Criticality – deciding the consequences of a loss if it should occur
9
How to handle identified risks:
1.
Risk elimination
2.
Risk reduction
3.
Risk spreading
4.
Risk transfer
5.
Risk acceptance
10
1. Risk Elimination
The best alternative, if it is realistic.
For example, we can eliminate the risk of losses from credit card fraud if we don’t take credit cards.
However, the loss of business would be more than the loss from credit card fraud.
11
2. Risk Reduction
We can not eliminate all pure risk, but we can reduce it.
We reduce it by establishing control and procedures.
Lighting, installing locks and alarm systems are all examples of methods of risk reduction.
12
2. Risk Reduction – attack trees
These give us a visual representation of our risk.
13
3. Risk Spreading
Related to risk reduction
This approach uses methods that reduce the potential loss by splitting up the risk into several areas.
14
4. Risk Transfer
We can transfer the risk by either raising prices or insurance.
Insurance has a couple of important principles:
Indemnity: states the insurer pays only the actual amount of the loss and no more
Subrogation: substitution of the insurer in place of the insured for the purposes of claiming indemnity from a third party for a loss covered by insurance
15
5. Risk Acceptance
It is never cost effective, practical, or indeed possible, to provide 100% security, thus some risks we simply have to accept.
Some risks are simply the costs of doing business.
16
Qualitative and Quantitative Risk
Assessment
Quantitative – calculate the objective values for each component during risk assessment and cost benefit analysis.
Qualitative – identifies the most important risks quickly by assigning relative values to assets, risks, control and effects.
This balances cost and effectiveness.
17
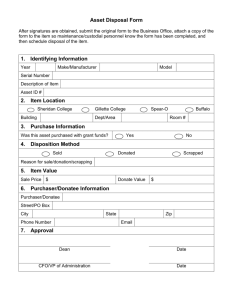
Conducting the Security Survey
A survey instrument needs to be developed
A thorough, physical walk-through should be done
Walk-through should include talking to and observing personnel and observing the environment as a whole
18
Reporting the Results
1.
Introduction
2.
A discussion of the risk analysis
3.
Strengths of the system
4.
Weaknesses of the system
5.
Recommendations for alternatives for managing the risks, including the estimated cost and savings, and who should be responsible for making the changes
19
Implementing the Recommendations
It is important to note that most companies will not have the money to implement all the changes at once.
It is important to establish a schedule for implementation of the recommendations, in order to accommodate budget issues and ensure items do not get overlooked.
20
Keys to Success
Executive sponsorship
Well defined list of stakeholders
Clear definition of roles and responsibilities
Atmosphere of open communication
Spirit of teamwork
Holistic view of organization
Authority throughout process
21