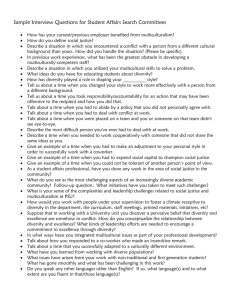
I ntegrit y
advertisement

Headquarters U.S. Air Force Integrity - Service - Excellence Designing Water System Security Measures Mr. Michael X Clawson HQ AFCESA/CESC 17 August 2004 As of: 1 Overview Air Force & Dod Guidance & Policy False assumptions about water system security Water System Security Measures Source Water (Before Treatment) Treatment Plants Distribution System SCADA & Controls Contaminant detection As of: Integrity - Service - Excellence 2 Air Force & DoD Policy Security Engineering Manual Air Force AFMAN 32-1071 Vol 1-4 Army TM 5-853-1/2/3/4 For Official Use Only Comprehensive publication covering everything from front gate, fence, & facility criteria to water systems. Each Chapter being converted into a separate UFC Current publication is to massive to efficiently update and keep current and has not been updated in many years Breaking chapters into separate documents update process and coordination simpler & quicker As of: Funding for converting chapter on water system security has been requested. Integrity - Service - Excellence 3 Air Force & DoD Policy As of: Air Force ETL 04-5 Design Recommendations for Potable Water System Security Issued August 2004 For Official Use Only Contains additional recommendations for water system security Measures in ETL are optional Designed to fill gap between AFMAN 32-1067 and new information & technology on water system security Interim document to be used until new UFC on water system security is published Integrity - Service - Excellence 4 False Assumptions About Water System Security Water systems are not mission critical assets Water system pressure provides security against contamination Water systems have sufficient redundancy Dilution in water systems means large quantities of toxins are necessary Physical security alone can protect systems As of: Integrity - Service - Excellence 5 Source Water Vulnerabilities Water course contamination sources Chemical & fuel manufacturing bulk storage facilities Road & Railroad crossings Industrial impounds, mills, and mines Nuclear Facilities As of: Intake structures Wellhead contamination Piping Integrity - Service - Excellence 6 Source Water Protection Measures As of: General Measures Backup/Alternate source Intrusion detection systems Surface Water Restrict access near intakes Bank Filtration/infiltration galleries Wellhead security measures Wellhead protection plan Restrict access & activities in wellhead area Enclosed well houses Fenced well area Integrity - Service - Excellence 7 Treatment Plant Vulnerabilities Treatment plants have numerous vulnerabilities Areas open to atmosphere Chemical injection points Hazardous material storage As of: Integrity - Service - Excellence 8 Treatment Plant Protection Measures Where feasible, totally enclose treatment plant Provide multiple layers of security & fencing Intrusion Detection Electronic monitoring of valves, pumps, equipment settings, chemical levels, etc. As of: Integrity - Service - Excellence 9 Distribution System Vulnerabilities Smaller amount of contaminate needed Pump can be used to overcome system pressure and introduce contaminates Hydrants Facilities As of: Destruction of key nodes can affect entire system Storage tanks at atmospheric pressure Pump houses Meters & Backflow preventors Integrity - Service - Excellence 10 Distribution System Protection Measures Prevent unauthorized access Fence, alarm, and secure critical components Develop hydraulic model Can be used to determine critical nodes Can predicted contaminate travel when injection point is known By developing unidirectional flushing plan, it can help restore system after contamination As of: Integrity - Service - Excellence 11 Distribution System Protection Measures As of: Valves Secure and lock all valve Eliminate quick closing valves Tamper resistant fire hydrants are NOT recommended Integrity - Service - Excellence 12 Distribution System Protection Measures As of: Storage tanks Remove vegetation or other items that may hide an attacker Install lighting Install locks, tampering/ intrusion alarms, and/or security cameras on tank ladders, scuttles, access panels, access ways, air vents, etc. Secure ladders/tank access Harden tank vents/overflows Integrity - Service - Excellence 13 SCADA & Electronic Controls Attacker does not have to physically be present Can be miles away or half way around the world SCADA attack can be used to damage controls/electronics or actual system components Example – Wastewater system attack in Australia Disgruntled employee of a consultant used SCADA vulnerabilities and laptop computer to attack system Controlled pumps & valves and caused raw sewage to be dumped in waterways, parks, and neighborhoods Only caught when police found computer equipment and stolen cell phone during a traffic stop As of: Integrity - Service - Excellence 14 SCADA & Electronic Controls Protection Measures Develop a attack detection strategy Develop an attack response plan Conduct a thorough analysis to assess the risk and necessity of each connection to the SCADA network. Identify and evaluate the following types of connections: Internal local area networks (LAN) and wide area networks (WAN) Internet Wireless network devices Modem or dial-up connections Connections to contractors, consultants, vendors, or regulatory agencies As of: Integrity - Service - Excellence 15 SCADA & Electronic Controls Protection Measures As of: Isolate the SCADA network from other network connections Some SCADA systems use unique proprietary protocols for communications and the security some SCADA systems is based solely on the secrecy of these protocols. Many older SCADA/EMCS systems have few or no security features. Eliminate backdoors or vendor interfaces to the SCADA/EMCS system Install SCADA/EMCS overrides for local control points are critical to operate the system in the event of attack Integrity - Service - Excellence 16 Contaminate Detection Systems There are two types of contaminate detection systems Single sample testing Continuous on line monitoring The EPA has approved several “Rapid Toxicity Testing Systems” to test single samples Mainly for chemical agent detection Information on these systems is available from the EPA website As of: Integrity - Service - Excellence 17 Contaminate Detection Systems As of: An ideal continuous on-line warning system would: monitor parameters that provide sufficient warning time Detect a wide range of contaminants Chemical & biological Be affordable Be reliable Be easy to operate And give a minimal number of false alarms Unfortunately, the currently available on-line systems fail to meet one or more of these criteria Integrity - Service - Excellence 18 Contaminate Detection Systems Several systems under development show great promise in detecting virtually all potential terrorist agents These systems include detectors using: Immunoassays Bioactive compounds Deoxyribonucleic acid/ribonucleic acid (DNA/RNA) And other methods Technology promises very low detection limits little as a single cell of a biological agent or a few molecules of a chemical agent Most are one to several years away from commercial release As of: Integrity - Service - Excellence 19 Contaminate Detection Systems As of: For these reasons, continuous monitoring systems are not currently recommended for widespread implementation Regardless of the detection method, it is necessary to have an appropriate response plan to follow when something is detected Integrity - Service - Excellence 20 Conclusion Water systems are vulnerably Hardening water system alone does not provide security Water system security must be a comprehensive program that includes Delaying an adversary Detecting the adversary And the appropriate response As of: Integrity - Service - Excellence 21 Questions Michael X. Clawson, PE, REM HQ AFCESA/CESC 139 Barnes Drive, Suite 1 Tyndall AFB, FL 32403-5319 (850)283-6362 DSN 523-6362 FAX: (850)283-6219 DSN FAX 523-6219 E-mail: Michael.Clawson@tyndall.af.mil As of: Integrity - Service - Excellence 22