Enterprise Directory Strategy & Recommendations

Enterprise Directory
Strategy & Recommendations
March 27, 2000
Georgia State University
GSU/IST/Advanced Campus
Services
1
Enterprise Directory
eUniversity Environment
Opportunities - account mgmt, mail,
Requirements - functional & technical
ID, Directory, Authentication, Authorization
Policy, Procedure, & Practice
Strategic Process & Methodology
Goals
March 27, 2000
GSU/IST/Advanced Campus
Services
2
eUniversity Environment
The electronic, wired environment of the information age is pervasive - eUniversity
Work & learning interactions are not bounded by time, place, distance
Interactions and access in the electronic world are strategic advantages, necessities
Enterprise Directory is a basic infrastructure
March 27, 2000
GSU/IST/Advanced Campus
Services
3
Gartner Group Recommendation
Business Strategy Will Drive Directory Services
“Pressures from intranet, extranet and E-commerce applications are increasing the need for an enterprise strategy for directories. This will not be easy to achieve, but tactical solutions will cause greater problems.
“GartnerGroup has been advising clients for some time that directory services will be key to success in electronic workplace implementations — to analyze usage and requirements for such services, and to focus on opportunities for directory synchronization pending consolidation of the multiple directory services found in most enterprises. While this advice remains valid, we are now recommending that enterprises proactively plan for directory implementation as part of their overall
Internet and electronic workplace strategies. Why this change of emphasis?
Directories are moving from an incidental support role in workgroup systems toward the core of the required infrastructure.”
Research Note, S. Hayward, J. Graff, N. MacDonald, 11 March 1999, (Tactical
Guidelines, TG-07-4615)
March 27, 2000
GSU/IST/Advanced Campus
Services
4
The Burton Group Recommendation
Major Recommendations
“The University System must begin implementation of the common directory infrastructure discussed in the October [1999] Directory Services
Workshop. The long-term success and scalability of the GLOBE, Banner,
PeopleSoft, GALILEO, and GIL applications are dependent upon this happening immediately.”
“... Member institutions should not deploy PKI without a clear understanding of their directory plans. And to create scalable and manageable inter-institutional capabilities, the University System must build a directory infrastructure that binds the member institutions to a community, allowing them to view each other as authoritative sources for information on their own students, faculty, and services.”
Public Key Infrastructure (PKI) Strategy Workshop, Summary Observations and Recommendations
Prepared for the University System of Georgia, March 22, 2000
March 27, 2000
GSU/IST/Advanced Campus
Services
5
Internet2 “Middleware” Initiative
“Directories are the operational linchpin of almost all middleware services. They can contain critical customization information for people, processes, resources and groups. By placing such information in a common storage area, diverse applications from diverse locations can access a consistent and comprehensive source for current values of key data. In future information technology environments, directories will be among the most critical services offered.” http://www.internet2.edu/middleware/core/directories.shtml
6
March 27, 2000
GSU/IST/Advanced Campus
Services
Internet2 “Middleware” … what?
“The items included under the heading of middleware differ depending on who is making the list…. These categorizations are all centered around sets of tools and data that help applications use networked resources and services….
“Middleware has emerged as a critical second level of the enterprise IT infrastructure. The need for middleware stems from growth in the number of applications, in the customizations within those applications and in the number of locations in our environments. These and other factors now require that a set of core data and services be moved from their multiple instances into a centralized institutional offering….
“Interoperable middleware between organizations is a particular need of higher education….”
March 27, 2000 http://www.internet2.edu/middleware/overview/
GSU/IST/Advanced Campus
Services
7
Internet2 “Middleware” …core.
Identifiers: A set of computer-readable codes that uniquely specify a subject.
Authentication: The process of a subject electronically establishing that it is, in fact, the subject associated with a particular identity.
Directories: Central repositories that hold information and data associated with identities….
Authorization: Those permissions and workflow engines that drive transaction handling, administrative applications and automation of business processes.
Certificates and: Certificates and PKI are related to the previous four core public-key middleware services in several important ways.
Infrastructures
March 27, 2000 http://www.internet2.edu/middleware/core/
GSU/IST/Advanced Campus
Services
8
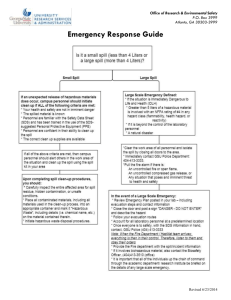
Account Administration -
Opportunities for management
Netware Groupwise Panther Oasis,
Orator
Peoplesoft SCT Lynx,
Lion…
WebCT
MVS CV1,
CV2…
Oracle
ATM, routers
IDMS
Citrix
Unix Root admin
Panther
Card
Cheetah
Green
Card
Crystal Remedy
March 27, 2000
GSU/IST/Advanced Campus
Services
9
Lookup & Phonebooks -
Opportunities for searching
Groupwise
“panther”
Outlook
Express
HR PPS
Eudora,
Compuserv
CSO phonebook
AOL,
BellSouth
Yahoo,
Hotmail
Student, faculty, staff phonebook
March 27, 2000
GSU/IST/Advanced Campus
Services
10
Directory Technology -
Opportunities for interfaces
Novell
Netware
Directory
Services
GroupWise
LDAP interface
Oracle8i
LDAP read/write
SCT (Campus
Pipeline) future LDAP
GSU
?
March 27, 2000
GSU/IST/Advanced Campus
Services
11
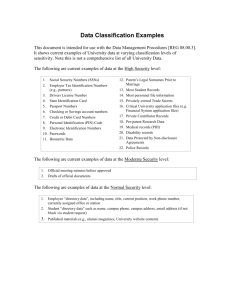
Functional Requirements driving needs
Management of application access
– Coordinating and change management
– IT Audit Finding
Finding email addresses, group lists
– Standard groups automated? (class rosters? departments?)
– Use of lists is appropriately managed
Preparing for future applications
– eCore and GLOBE potential
– SCT Banner strategic direction
– Federal financial aid interfaces
March 27, 2000
GSU/IST/Advanced Campus
Services
12
Technical Requirements - basic infrastructure
Scalable solutions
Standards based technology
Interoperable architecture
Reusable components (object oriented)
Infrastructure to enable future applications
Trusted security model
Manageable administration
March 27, 2000
GSU/IST/Advanced Campus
Services
13
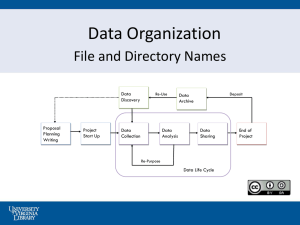
ID, Directory, Registration &
Authentication, Authorization
UUID - Identify entities (persons, resources) with Universal Unique ID
DIRECTORY - Implement/maintain directory storing UUID related information
REGISTER/AUTHENTICATE - Verify & register; establish authentication method
AUTHORIZATION - Permit authenticated users to access resources and services
March 27, 2000
GSU/IST/Advanced Campus
Services
14
Policy, Procedure, & Practice
Policy issues must be addressed
– Official persons or entities - who/what, role(s)/service(s)
– Legal - FERPA, Open records, application specific...
– Security - responsibility & accountability
Procedures to implement policy
– How to establish unique ID (SSN, application specific, random…)
– Who is involved in ID process, how access is requested, how access is permitted, how access is changed/terminated
Practice as the long term success factor
– Management, monitoring, audits, change control
March 27, 2000
GSU/IST/Advanced Campus
Services
15
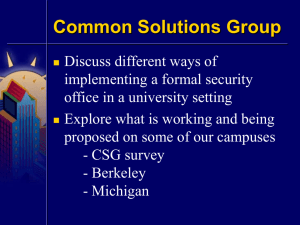
Strategic Process & Methodology
Work with existing resources:
– University System of Georgia (Georgia Tech, UGA, OIIT…)
– The Burton Group - Directory & PKI workshops for USG
– Internet2 “Middleware” Initiative ( www.internet2.edu/middleware )
– Common Solutions Group ( www.stonesoup.org
)
– IETF: Internet Engineering Task Force (protocol standards - LDAP,
PKI, etc.) (www.ietf.org)
– CREN: Corporation for Research & Educational Networking (Tech
Talks) ( www.cren.net/know/techtalk/archives.html
)
– CNI: Coalition for Networked Information ( www.cni.org/)
– Educause Information Resources Library ( www.educause.edu/ir/irlibrary.html
)
Prototypes, feedback, working group process
March 27, 2000
GSU/IST/Advanced Campus
Services
16
Strategic Goals
Build an enterprise directory infrastructure
– Use standards-based protocol & architecture
– Coordinated, strategic response - not ad hoc fixes
Use collaborative methodology
– IETF working group model
– IST Directors / GSU campus groups / University System
– Higher Education alliances
Deliver Account Management 3/2001
– Establish UUID
– Implement directory, load with legacy extracts
– Adopt policy and procedure guidelines
March 27, 2000
GSU/IST/Advanced Campus
Services
17
Recommended Reading
Building Directories: The Fundamentals, with Ken Klingenstein and Keith Hazelton - 2/17/00 http://www.cren.net/know/techtalk/events/directauthen.html
Directories on Campus: Getting Started, with Frank Grewe & Mike LaHaye - 11/4/99 http://www.cren.net/know/techtalk/events/getstarted.html
Campus Directories, with Frank Grewe & Jeff Hodges - 4/22/99 http://www.cren.net/know/techtalk/events/directories.html
Stanford Registry & Directory Infrastructure: A Case History, Jeff Hodges - 5/10/1999 http://www.stanford.edu/~hodges/talks/EMA99-DirectoryEnabledApps/StanfordRegistryAndDirectoryCaseHistory/index.htm
Introduction to Directories and the Lightweight Directory Access Protocol, Jeff Hodges - 1997 http://www.stanford.edu/~hodges/talks/mactivity.ldap.97/index.html
Early Harvest Technical Workshop, September 23-24, 1999, Denver, Colorado http://www.internet2.edu/middleware/earlyharvest/
Current Activities in Middleware, Ken Klingenstein, Project Director, Internet2 Middleware Initiative http://www.internet2.edu/middleware/
Schema Design Workshop presentations, Common Solutions Group, May 1999 meeting http://www.stonesoup.org/Meetings.past/9905/schema.pres/
A White Paper on Authentication and Access Management Issues in Cross-organizational Use of Networked
Information Resources, Clifford Lynch, editor, Revised Discussion Draft of April 14, 1998 http://www.cni.org/projects/authentication/authentication-wp.html
March 27, 2000
GSU/IST/Advanced Campus
Services
18