OU Information Security & Risk Management
advertisement
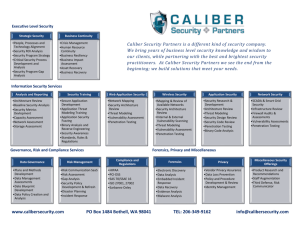
OU INFORMATION SECURITY & RISK MANAGEMENT ISA – February 4, 2015 Security realities and trends • Higher Ed = Target Rich Environment • “BYOD / IOE” • Evolving threat landscape – i.e. ransomware • Encryption becomes the standard • Attack surfaces/exploits for mobile devices are on the rise • Cyber-Espionage continues trending up • Weak (and reused) Passwords • Networks and users lack the basics Our Goals • Ensure a safe and secure online environment for OU • Be operationally relevant and enable the business • Provide excellent customer service • Lead a collaborative and innovative OU information security community • Partner to educate and raise security awareness across the University Background • Our Team – 12 full time + 1 student • Multiple vacancies posted on jobs.ou.edu – Two Teams • • IT Risk, Compliance & Awareness • Information Security Operations About Me – 10+ years in information security • 7+ at the National Security Agency / 3+ at the US Naval Academy’s non-profits • Everything from high level strategy development to program management for crypto certification/security engineering to running an operational network and hands on with all security capabilities – US Naval Academy / Johns Hopkins University grad – Navy NFO stationed at Tinker AFB from 2000-2004 – Started at OU in Nov 2014 IT Risk, Compliance, & Awareness • • IT Risk & Architecture – Performs risk assessments in coordination with the IS Operations Team – Recommends security technologies for use within the OU IT enterprise – Supports the remediation of risk/vulnerability findings within OU IT networks Compliance (PCI, HIPAA, FERPA, etc) – • • Leads PCI (and other standards) risk assessments for Norman and OU IT architectures as required Security Training and Awareness – Develops and execute an ongoing campus-wide training and awareness program for various groups of stakeholders (online & offline) – Internal / External facing online presence for security IT Security Policy – Maintains policy repository (online) – Develops draft policy as required – Represents Norman in security policy development, discussion, adjudication at the working level Information Security Operations • • • • OU Computer Security Incident Response Team (CSIRT) – Maintains a common operational security picture via an establish network security monitoring infrastructure for the Norman campus and Norman data/assets within S2 -> evolves into OU CSIRT – Responds to security incidents as appropriate – Makes recommendations to forensics for additional investigation when appropriate Forensics – Conducts forensic investigations as requested – Maintains the Computer Forensics Lab (CFL) Vulnerability Analysis – Conducts network vulnerability analysis (blue team/red team) as required/requested for OU IT – Develops a standard tool suite for vulnerability analysis and penetration testing – Assists with compliance assessments (technical, PCI scans, etc) Security Engineering – Identifies, assesses, and implements tools and security capabilities for integration into the OU IT network architecture – Assists with the technical remediation of findings from risk/vulnerability assessments Stop. Think. Connect. • Stop: Before you use the Internet, take time to understand the risks and learn how to spot potential problems • Think: Take a moment to be certain the path ahead is clear. Watch for the warning signs and consider how your actions online could impact your safety, or your family’s. • Connect: Enjoy the Internet with greater confidence, knowing you’ve taken the right steps to safeguard yourself and your computer Tips & Advice • Keep a Clean Machine • Protect Your Personal Information • Connect with Care • Be Wise Web • Be a Good Online Citizen Keep a Clean Machine • Keep security software current • Automate software updates • Protect all devices that connect to the Internet • Plug & scan Protect Your Personal Information • Secure your accounts (2-factor) • Make passwords long and strong • Unique account, unique password • Write it down and keep it safe • Own your online presence • Mobile – Use a strong passcode to lock your phone • Mobile – Think before you app • Mobile – Online give your mobile number out to people you know and trust • Mobile – Learn how to disable the geo-tagging feature on your phone – http://icanstalku.com/how.php#disable Connect with Care • When in doubt, throw it out • Get savvy about Wi-Fi hotspots • Protect your $$ • Mobile – When it doubt, don’t respond Be Web Wise • Stay current. Keep pace with new ways to stay safe online • Think before you act • Back it up • Mobile - Know how to cell block others Be a Good Online Citizen • Safer for me more secure for all • Post only about others as you have them post about you • Help authorities fight cyber crime – www.ic3.gov (Internet Crime Complaint Center) Questions? • Ken Kurz, Director, Information Security & Risk Management – kkurz@ou.edu – 405-325-6441 • Incidents / Security Questions – security@ou.edu / csirt@ou.edu – CSIRT Hotline – 405-325-7258 • Online Resources – www.stopthinkconnect.org – https://www.us-cert.gov/ – http://www.sans.org/tip_of_the_day.php