Slides
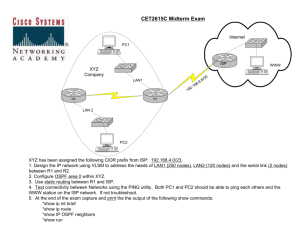
advertisement

Chapter 1 Computer Networks and the Internet These slides are adapted from the slides that accompany the textbook Textbook: Computer Networking: A Top Down Approach , 5th edition. Jim Kurose, Keith Ross Addison-Wesley, April 2009. http://www.aw-bc.com/kurose-ross Introduction 1-1 Chapter 1: Introduction Our goal: Overview: overview, “feel” of networking more depth, detail later in course approach: descriptive use Internet as example what’s a protocol? get context, what’s the Internet network edge & access network core performance: loss, delay, throughput, capacity protocol layers, service models security Introduction 1-2 Chapter 1: roadmap 1.1 What is the Internet? 1.2 Network edge 1.3 Network core 1.4 Delay & loss in packet-switched networks 1.5 Protocol layers, service models 1.6 Security 1.7 History Introduction 1-3 What’s the Internet: “nuts and bolts” view millions of connected computing devices: hosts, end-systems PCs workstations, servers PDAs phones, toasters router server mobile local ISP running network apps communication links workstation regional ISP fiber, copper, radio, satellite transmission rate = bandwidth routers: forward packets (chunks of data) company network Introduction 1-4 What’s the Internet: “nuts and bolts” view protocols control sending, receiving of msgs e.g., TCP, IP, HTTP, FTP, PPP Internet standards RFC: Request for comments IETF: Internet Engineering Task Force router server workstation mobile local ISP regional ISP Internet: “network of networks” loosely hierarchical public Internet versus private intranet company network Introduction 1-5 Internet structure: network of networks roughly hierarchical at center: “tier-1” ISPs (e.g., Verizon, Sprint, AT&T, Cable and Wireless), national/international coverage treat each other as equals (peering points) Tier-1 providers interconnect (peer) privately Tier 1 ISP Tier 1 ISP Tier 1 ISP Introduction 1-6 Internet structure: network of networks “Tier-2” ISPs: smaller (often regional) ISPs Connect to one or more tier-1 ISPs, possibly other tier-2 ISPs Tier-2 ISP pays tier-1 ISP for connectivity to rest of Internet tier-2 ISP is customer of tier-1 provider Tier-2 ISP Tier-2 ISP Tier 1 ISP Tier 1 ISP Tier-2 ISP Tier 1 ISP Tier-2 ISPs also peer privately with each other. Tier-2 ISP Tier-2 ISP Introduction 1-7 Internet structure: network of networks “Tier-3” ISPs and local ISPs last hop (“access”) network (closest to end systems) local ISP Local and tier3 ISPs are customers of higher tier ISPs connecting them to rest of Internet Tier 3 ISP Tier-2 ISP local ISP local ISP local ISP Tier-2 ISP Tier 1 ISP Tier 1 ISP Tier-2 ISP local local ISP ISP Tier 1 ISP Tier-2 ISP local ISP Tier-2 ISP local ISP Introduction 1-8 Tier-1 ISP: e.g., Sprint POP: point-of-presence to/from backbone peering … … . … … … to/from customers Introduction 1-9 POPs reside in buildings like this London IXP 10 Internet Core Routers Look Like These Router on “paper” 11 A closer look at network structure: network edge: applications and hosts network core: routers network of networks access networks, physical media: communication links Introduction 1-12 What’s the Internet: a service view communication infrastructure enables distributed applications: Web, email, games, ecommerce, database., voting, file (MP3) sharing communication services provided to apps: connectionless connection-oriented services provided by protocols running on hosts and routers. Introduction 1-13 What’s a protocol? human protocols: “what’s the time?” “I have a question” introductions … specific msgs sent … specific actions taken when msgs received, or other events network protocols: machines rather than humans all communication activity in Internet governed by protocols protocols define format, order of msgs sent and received among network entities, and actions taken on msg transmission, receipt Introduction 1-14 What’s a protocol? a human protocol and a computer network protocol: Hi TCP connection req Hi TCP connection response Got the time? Get http://www.awl.com/kurose-ross 2:00 <file> time Q: Other human protocols? Introduction 1-15 Internet protocol stack application: supporting network applications FTP, SMTP, HTTP transport: process-process data transfer TCP, UDP network: routing of datagrams from source to destination IP, routing protocols link: data transfer between application transport network link physical neighboring network elements PPP, Ethernet physical: bits “on the wire” Introduction 1-16 Why stack or layering? Dealing with complex systems (e.g., big c/c++ program) Need structured, modular design for easy maintenance (layers = *.c files) Layer n uses the services provided by layer n-1 (e.g., error/flow control, connection set up) Interface between two layers, e.g., Application Programmer’s Interface (API) or sockets Logical connection between two layer n entities (peers) layering harmful (can’t do global/customized optimization) ? 2: Application Layer 17 encapsulation at each layer source message segment M Ht M datagram Hn Ht M frame Hl Hn Ht M application transport network link physical link physical switch destination M Ht M Hn Ht Hl Hn Ht M M application transport network link physical Hn Ht Hl Hn Ht M M network link physical Hn Ht M router Introduction 1-18 An analogy (Fig.1-10 of Tanenbaum) 2: Application Layer 19 The Edge end systems (hosts): run application programs e.g. Web, email at “edge of network” client/server model peer-peer client host requests, receives service from always-on server e.g. Web browser/server; client/server email client/server peer-peer model: minimal (or no) use of dedicated servers e.g. Skype, BitTorrent 20 Network edge: connection-oriented service Goal: data transfer between end systems handshaking: setup (prepare for) data transfer ahead of time Hello, hello back human protocol set up “state” in two communicating hosts TCP - Transmission Control Protocol Internet’s connectionoriented service TCP service [RFC 793] reliable, in-order byte- stream data transfer loss: acknowledgements and retransmissions flow control: sender won’t overwhelm receiver congestion control: senders “slow down sending rate” when network congested Introduction 1-21 Network edge: connectionless service Goal: data transfer between end systems same as before! UDP - User Datagram Protocol [RFC 768]: Internet’s connectionless service unreliable data transfer no flow control no congestion control App’s using TCP: HTTP (Web), FTP (file transfer), Telnet (remote login), SMTP (email) App’s using UDP: streaming media, teleconferencing, DNS, Internet telephony Introduction 1-22 Access networks and physical media Q: How to connect end systems to edge router? residential access nets institutional access networks (school, company) mobile access networks 2: Application Layer 23 Wireless access networks wireless LANs: router o 802.11b (2.4GHz): 11 Mbps; o 802.11a (5GHz), 802.11g (2.4GHz): 54Mps access point o 802.11n (2.4 or 5GHz): up to 600Mps (40Mhz channel and MIMO) Personal Area Networks (PANs) o Bluetooth: upto 1 Mbps within ~ 10m Wide-area Cellular Access o 2G (GSM, TDMA, CDMA, iDEN) 10-20kpbs (circuit-switched) o 2.5G system (GPRS, 1xRTT, EDGE ) 30-50kbps ( up to 114kbps) o 3G (UMTS, W-CDMA) 300 – 500kbps, (up to a few Mbps) o 1xEvolutional Data Only (EV-DO) 2.4M/700K) o 1XEV – DV (Data and Voice) (3.1M/1.5M) and HSPDA o 4G: LTE (and LTE-Advanced) by 3GPP, TD-LTE in China, and WiMax (by IEEE 802.16): about 100Mbps down and 50Mbps up. 2: Application Layer 24 Home networks Typical home network components: cable (or DSL) modem router/firewall/NAT Ethernet wireless access point DD-WRT, Tomato… to/from cable headend cable modem wireless laptops router/ firewall Ethernet (switched) wireless access point 2: Application Layer 25 The Network Core mesh of interconnected routers (wide area networks or WANs) the fundamental question: how is data transferred through net? circuit switching (CS) dedicated circuit per call: e.g. telephone net packet-switching (PS) data sent thru net in discrete “chunks” called “packets” Introduction 1-26 Network Core: Circuit Switching End-end resources reserved for “call” call setup required link bandwidth, switch capacity dedicated resources to each call: no sharing multiple calls can be multiplexed onto a link guaranteed performance Introduction 1-27 Network Core: Circuit Switching network resources (e.g., bandwidth) divided into “pieces” pieces allocated to calls resource piece idle if not used by owning call (dedicated, no sharing) not bandwidth efficient if data is sporadic (or bursty with a variable bit rate) dividing link bandwidth into “pieces” (for call grooming, aggregating or multiplexing) frequency division (wavelength division) • f x l = C (speed of light) time division code division (e.g., wireless/cellular) space division (with a multi-fiber link) Introduction 1-28 Circuit Switching: TDMA and TDMA Example: FDMA 4 users frequency time TDMA frequency time Introduction 1-29 Electromagnetic Spectrum Introduction 1-30 Network Core: Packet Switching each end-end data stream each packet has a divided into packets “header” (containing e.g., destination user A & B’s packets share address) in addition to network resources “payload” (data) each packet uses full link Store and Forward bandwidth (requires buffer and resources used as needed introduces delay) Statistical multiplexing (support an aggregate Bandwidth division into “pieces” demand that exceeds Dedicated allocation link bandwidth) Resource reservation Introduction 1-31 Packet-switching: store-and-forward L R entire packet must R arrive at router before it can be transmitted on next link: store and forward must have a large enough buffer incurs transmission delay per hop alternative: cut-through switching as in CS R Example: transmit (push out) a packet of L bits on to link of R bps L = 7.5 Mbits R = 1.5 Mbps Transmission delay per hop = L/R = 5 sec Total transmission delay (3 hops) = 15 sec Introduction 1-32 Four sources of delay (I) 1. Transmission delay: R=link bandwidth (bps) L=packet length (bits) time to send bits into link = L/R transmission A 2. Propagation delay: d = length of physical link c = propagation speed in medium (~2x108 m/sec) propagation delay = d/c Note: c and R are very different quantities! propagation B nodal processing queueing Introduction 1-33 Four sources of delay (II) 3. nodal processing: check bit errors determine output link (based on e.g., the destination address) 4. queueing time waiting at output link for transmission (and at input buffer too) depends on congestion level of router transmission A propagation B nodal processing queueing Introduction 1-34 Nodal delay d nodal = d proc d queue d trans d prop dproc = processing delay typically a few microsecs or less dqueue = queuing delay depends on congestion dtrans = transmission delay = L/R, significant for low-speed links dprop = propagation delay a few microsecs to hundreds of msecs Introduction 1-35 Queueing delay (revisited) R=link bandwidth (bps) L=packet length (bits) a=average packet arrival rate traffic intensity = La/R La/R ~ 0: average queueing delay small La/R -> 1: delays become large La/R > 1: more “work” arriving than can be serviced, average delay infinite! Introduction 1-36 “Real” Internet delays and routes What do “real” Internet delay & loss look like? Traceroute program: provides delay measurement from source to router along end-end Internet path towards destination. For all i: sends three packets that will reach router i on path towards destination router i will return packets to sender sender times interval between transmission and reply. 3 probes 3 probes 3 probes Introduction 1-37 “Real” Internet delays and routes traceroute: gaia.cs.umass.edu to www.eurecom.fr Three delay measurements from gaia.cs.umass.edu to cs-gw.cs.umass.edu 1 cs-gw (128.119.240.254) 1 ms 1 ms 2 ms 2 border1-rt-fa5-1-0.gw.umass.edu (128.119.3.145) 1 ms 1 ms 2 ms 3 cht-vbns.gw.umass.edu (128.119.3.130) 6 ms 5 ms 5 ms 4 jn1-at1-0-0-19.wor.vbns.net (204.147.132.129) 16 ms 11 ms 13 ms 5 jn1-so7-0-0-0.wae.vbns.net (204.147.136.136) 21 ms 18 ms 18 ms 6 abilene-vbns.abilene.ucaid.edu (198.32.11.9) 22 ms 18 ms 22 ms 7 nycm-wash.abilene.ucaid.edu (198.32.8.46) 22 ms 22 ms 22 ms trans-oceanic 8 62.40.103.253 (62.40.103.253) 104 ms 109 ms 106 ms link 9 de2-1.de1.de.geant.net (62.40.96.129) 109 ms 102 ms 104 ms 10 de.fr1.fr.geant.net (62.40.96.50) 113 ms 121 ms 114 ms 11 renater-gw.fr1.fr.geant.net (62.40.103.54) 112 ms 114 ms 112 ms 12 nio-n2.cssi.renater.fr (193.51.206.13) 111 ms 114 ms 116 ms 13 nice.cssi.renater.fr (195.220.98.102) 123 ms 125 ms 124 ms 14 r3t2-nice.cssi.renater.fr (195.220.98.110) 126 ms 126 ms 124 ms 15 eurecom-valbonne.r3t2.ft.net (193.48.50.54) 135 ms 128 ms 133 ms 16 194.214.211.25 (194.214.211.25) 126 ms 128 ms 126 ms 17 * * * * means no response (probe lost, router not replying) 18 * * * 19 fantasia.eurecom.fr (193.55.113.142) 132 ms 128 ms 136 ms Introduction 1-38 Throughput throughput: rate (bits/time unit) at which bits transferred between sender/receiver instantaneous: rate at given point in time average: rate over longer period of time link capacity that can carry server, with server sends bits pipe Rs bits/sec fluid at rate file of F bits (fluid) into pipe Rs bits/sec) to send to client link that capacity pipe can carry Rfluid c bits/sec at rate Rc bits/sec) Introduction 1-39 Throughput (more) Rs < Rc What is average end-end throughput? Rs bits/sec Rc bits/sec Rs > Rc What is average end-end throughput? Rs bits/sec Rc bits/sec bottleneck link link on end-end path that constrains end-end throughput Introduction 1-40 Throughput: Internet scenario per-connection end-end throughput: min(Rc,Rs,R/10) in practice: Rc or Rs is often bottleneck Rs Rs Rs R Rc Rc Rc 10 connections (fairly) share backbone bottleneck link R bits/sec Introduction 1-41 Packet Switching: Statistical Multiplexing 10 Mbs Ethernet A B statistical multiplexing C 1.5 Mbs queue of packets waiting for output link D E Sequence of A & B packets does not have fixed pattern statistical (time division) multiplexing. Unlike in TDM, where each host gets same slot in revolving TDM frame. Introduction 1-42 Packet switching versus circuit switching Packet switching allows more users to use network! 1 Mbit link each user: 100 kbps when “active” active 10% of time circuit-switching: 10 users N users 1 Mbps link packet switching: with 35 users, probability > 10 active less than .0004 Introduction 1-43 Packet switching versus circuit switching Is packet switching a “slam dunk winner?” Great for bursty data resource sharing (statistical multiplexing) simpler, no call setup Excessive congestion: packet delay and loss protocols needed for reliable data transfer, congestion control Q: How to provide circuit-like behavior? bandwidth guarantees needed for audio/video apps still an unsolved problem (chapter 6) Introduction 1-44 Message Switching (A mesg = 7.5Mbits) at 1.5Mbps transmission rate Introduction 1-45 Packet Switching: Message Segmenting Now break up the message into 5000 packets Each packet 1,500 bits 1 msec to transmit packet on one link pipelining: each link works in parallel Delay reduced from 15 sec to 5.002 sec Q: the smaller the packets, the better? Introduction 1-46 Packet-switched networks: forwarding Goal: move packets through routers from source to destination we’ll study several path selection (i.e. routing) algorithms (ch. 4) datagram network: destination address in packet determines next hop (according to the network’s routing algorithm) routes may change during session (out of order delivery) due to congested/failed links/routers analogy: driving, asking directions at each/every intersection virtual circuit network: each packet carries tag (virtual circuit ID), tag determines next hop fixed path determined at call setup time, remains fixed thru call (can be manually chosen for traffic engineering purposes) routers maintain per-call state Introduction 1-47 VC vs Datagram With VC, two packets with the same destination can be assigned two different VC# and forced to take different paths. Introduction 1-48 Network Taxonomy Telecommunication networks Circuit-switched networks FDM TDM Packet-switched networks Networks with VCs Datagram Networks • One may have a circuit-switched network (e.g. optical WDM) below, over which a packet-switched network runs • Internet provides both connection-oriented (TCP) and connectionless services (UDP) to apps. Introduction 1-49 Network Security The field of network security is about: how bad guys can attack computer networks how we can defend networks against attacks how to design architectures that are immune to attacks Internet not originally designed with (much) security in mind original vision: “a group of mutually trusting users attached to a transparent network” Internet protocol designers playing “catch-up” Security considerations in all layers! Introduction 1-50 The bad guys can sniff packets Packet sniffing: broadcast media (shared Ethernet, wireless) promiscuous network interface reads/records all packets (e.g., including passwords!) passing by C A src:B dest:A payload B Wireshark software used for end-of-chapter labs is a (free) packet-sniffer Introduction 1-51 The bad guys can use false source addresses IP spoofing: send packet with false source address C A src:B dest:A payload B Introduction 1-52 The bad guys can record and playback record-and-playback: sniff sensitive info (e.g., password), and use later password holder is that user from system point of view A C src:B dest:A user: B; password: foo B Introduction 1-53 Network Security more throughout this course A chapter focuses on security crypographic techniques: obvious uses and not so obvious uses Introduction 1-54