Wireless Topology
advertisement

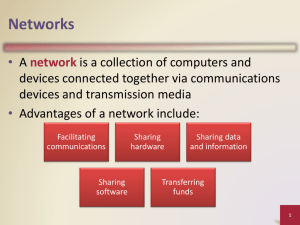
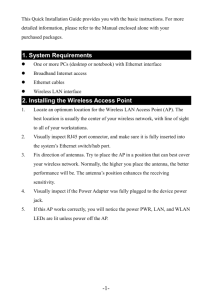
WIRELESS LAN & PDA CIS 454 (LAN) Prof. Ganesan Group members & outline • Belinda – Wireless LAN • Anthony Vu – Topology & wireless technology of LAN • Ka Yan (Susana) Chung – Implementation of wireless LAN • Norman-Ngan Vu Lam – Personal Digital Assistant (PDA) WIRELESS LAN WIRLESS LOCAL AREA NETWORK INTRODUCTION • It is a flexible data communications system implemented as an extension to, or as an alternative for, a wired LAN. • Using radio frequency (RF) technology, wireless LANs transmit and receive data over the air, minimizing the need for wired connections. • With wireless LANs, users can access shared information without looking for a place to plug in, and network managers can set up or augment network without installing or moving wires. WHY WIRELESS? Wireless LANs offer the following Productivity, convenience, and cost advantages over traditional wired networks: • MOBILITY • INSTALLATION SPEED AND SIMPLICITY. • INSTALLATION FLEXIBILITY. • REDUCED COST-OF-OWNERSHIP. • SCALABILITY. MOBILITY Wireless LAN systems can provide LAN users with access to real-time information anywhere at work and in the home. INSTALLATION SPEED AND SIMPLICITY Installing a wireless LAN system can be fast and easy and can eliminate the need to pull cable through walls and ceilings. INSTALLATION FLEXIBLITY Wireless technology allows the network to go where wire cannot go. REDUCED COST-OFOWNERSHIP While the initial investment required for wireless LAN hardware can be higher than the cost of wired LAN hardware, overall installation expenses and life-cycle costs can be significantly lower. Long-term cost and benefits are greatest in dynamic environments requiring frequent moves and changes. SCALABILITY Wireless LAN systems can be configured in a variety of topologies to meet the needs of specific applications and installations. Configurations are easily changed and range from peer-to-peer networks suitable for a small number of users to full infrastructure networks for thousands of users that enable roaming over a broad area. OVERVIEW BY INDUSTRY • Currently wireless LAN is not a replacement for the wired infrastructure, but it is a significant complement to what currently exists. Some examples in the industry are: – – – – – EDUCATION. MANFACTURING COMPANIES. HEALTHCARE. RETAIL. FINANCIAL/OFFICE-AUTOMATION. MAJOR FINDINGS IN THE INDUSTRIES • 89% Of the companies experienced a successful implementation. • 92% of respondents interviewed believe there is a definite economic and business benefit after installation. • 92% of respondents reported that they will continue to deploy wireless technology in their network through 2000 because of the benefits experienced by end users and/or IT staff. • Payback was less than one year, across all industries surveyed. Cost Chart RETAIL MANUFACTURING HEALTHCARE OFFICE AUTOMATION EDUCATION Benefits per Company (millions $) 5.6 2.2 .94 2.5 .5 Costs per Company (millions $) 4.2 1.3 .90 1.3 .3 9.7 7.2 11.4 6.3 7.1 Payback (#of months) Wireless Topology • Topologies are architectural drawings representing the cable layout for the wireless LAN. • Topologies of a network are the physical configuration of the nodes in the network. • They can be hardware dependent. Topologies Star Topology (Centralized) • Star topology is probably the oldest topology used for data communication. Star Topology (cont) • Computers are connected through a series of point-to-point dedicated circuits. • Each computer is linked by a separate full-duplex point-to-point through the central computer. • It is easy to set up. Bus Topology • Star topology is sometimes known as the linearbus topology. • All terminals share a single cable to transmit and receive messages. • There are endpoints to cable segment commonly known as terminating points. Physical Bus Topology Ring Topology • In the ring topology, all computers are connected in a close loop. • Each computer links to the next one. • There is no endpoints to this cable topology. • Messages can travel around the ring in one direction. Physical Ring Topology Speed and Distance • Transmission speed worsens problems – Error rates increase because bit periods are smaller and are more likely to be damaged by brief noise spikes and interference. – High speeds create high-frequency components in the signal that attenuate more rapidly than lower-frequency components. – In general, as speed increases, maximum distance decreases, although improving technology can lessen the decrease. Applications According to Electromagnetic Spectrum How cellular phone works ? (cont.) This process takes the same amount of time that it takes to make a call from a landline phone. Solid Objects Between Office Buildings How Does Satellite Work? • Communication • Frequency • Uplink & downlink Between Ground Unit and Satellite Attenuation • As signal travels, gets weaker – If too weak, cannot tell 1s and 0s Distance Distortion • As signal travels, it become distorted – Changes shape – Successive bits may merge, making reception difficult Distance Noise • Unwanted energy on line. Always present • Noise floor is average level • Noise spikes will cause problems Signal Strength Signal Noise Spike Noise Floor Time Approaching the Noise Floor • Attenuation will bring signal ever closer to the noise floor, creating more errors Signal Strength Signal Noise Floor Distance Interference • Unwanted signal from outside sources – Often intermittent, difficult to diagnose Signal Strength Signal Interference Implementation of Wireless LAN by Susana Wired Vs. Wireless LAN. • Wired LAN transmit data in cables such as twisted pair, coaxial, and fiber optic cable. • Wireless LAN transmit data in air, it use infrared (IR) or radio frequency (RF) to transmit data on air. Radio Frequency (RF) • Microwave transmission high frequency, narrow band radio waves that require special license. • Spread spectrum - spread signal over a range of frequency, therefore, harder to intercept • RF electromagnetic wave can easily pass through ordinary wall, it needs to implement with heavy concrete or metal screening. Infrared (IR) • Indoor infrared is the most secure wireless LAN, it’s the easiest types of wireless signal to contain with a certain location. Also, no license needed. • Use to connect nodes over small distance. • Point-to-point infrared must be within sight of each other with no obstacles in the path of signal. • Signal would be weaken by moist environment, dusty environment, person in signal path, and sheet of plastic. Wireless LAN Hardware Implementation • A wireless NIC - connect nodes to transmission medium. Allow communication between node and network. Consist of on board transceiver, & fix/external antenna. • For PC, wireless NIC are either PCI/ISA, for laptop, it uses PCMCIA type II card. • Installs driver to configure NIC. • Another option of wireless LAN implementation is “wireless LAN adapter” - external desktop transceiver and antenna connect to PC through parallel port and it function like a NIC. Wire Replacement System • It use wireless transmission instead of cabling to communicate with backbone. • Make use of existing Ethernet . • Use device called “user modules and control modules.” • User module is a desktop transceiver and antenna can be shared with up to 8 nodes with Ethernet cards that are individually wired to the user module. • Control modules are similar to AP, it allow communication with wired backbone through control modules. Data-link Layer • Data-link layer of the OSI model governs a node’s access to a shared medium. • Logical link control (LLC) layer deal with communication between nodes over a single link of network. • Media access control (MAC) layer which define how user obtain access to the shared medium when they need it. “OSI 7 layers” Different Types of MAC •Random Access MAC •Ordered MAC •Deterministic MAC Random Access MAC • • • • Simple to implement Offer fast response time under light network traffic Offer effective throughput under heavy traffic Wired network use CSMA/CD protocol to ensure data transmit efficiently (it checks if line is free, then transmits and listen if there’s collision, if collision, it stops and waits for re-send) • Wireless NICs can’t transmit and receive on the same frequency at the same time, therefore, it can’t detect collisions. Random Access MAC (continue) • Wireless NIC might not aware of all other node on network known as “hidden node” (a node outside of coverage area) Wireless network use CSMA/CA - Carrier sense multiply access with collision avoidance. Also known as LBT - Listen before you talk. (Check if line I free, if yes, send and wait for acknowledgment for receiving node, if no acknowledgement receive within set period of time, it assume a collision occur and wait to re-send) • CSMA/CA can’t be use when there’s hidden node • CSMA/CA cam be adapted to use with hidden node with the use of RTS/CTS/ACK - request to send/clear to send/acknowledge. Ordered MAC • Ordered MAC is unsuitable for wireless LAN because it is possible for a node to leave the bus or ring and break the orders Deterministic MAC (3 types) 1) Time division multiple access (TDMA) - each node given the same set amount of time to transmit data. -Another type of TDMA is reservation/polling MAC - node sends request to control point to request channel, channels are issue on a “first come first serve” base. 2) Frequency division multiple access (FDMA) - available bandwidth is divide into channels of different frequency and nodes allocate a particular frequency. 3) Code division multiple access (CDMA) - nodes share same channel bandwidth but use different spreading code to prevent interference. Deterministic MAC (continue) • Deterministic MAC provide effective throughout and response time when network traffic is heavy. • Each node must request access from control point before transmitting, therefore, deterministic MAC have slower response time than Random Access MACs in light traffic conditions. CSMA/TDMA • Combination of random-access MAC and deterministic MAC technique is called CSMA/TDMA. It offers fast response time in light traffic; effective throughout under heavy, but more complexes to administer on the network • CSMA/CA, RTS/CTS/ACK and CSMA/TDMS are suitable for wireless networks. Access Point (AP) Access Point are consists of 1) A wired NIC to communicate with wired backbone 2) A transceiver and antenna to communicate with wireless node within range 3) MAC-layer bridging software. • AP can be use to extend the range of a wireless network or connect an existing wired LAN to a wireless LAN. • Wireless subnets are connected to a wired backbone through AP. • AP bridging ensure only packet destined for wireless nodes within its service are forwarded to the wireless subnet. Bridging • Bridging - device that filters traffic between different section of the same network, of different LAN • It acts like a repeater, & sends data to both wired and wireless network. 1) Bridging software processes data and analyzes address info on packet. 2) It construct a table indicate location of each node. 3) Each time it receives packet, it checks if destination address is in table 4) If address to wired LAN, it checks if on table, if yes, only forward to wired LAN, if not, it forward to both wired and wireless. Bridging (continue) • There are 2 ways to create table 1) Source route algorithm - entire path of the package is included in each frame and bridge record information, most of the routing work is performed by nodes. 2) Spanning tree algorithm - used by most network, bridge notes the direction from which it receives each packet and concludes source node can be reach by sending packet in that direction and record it in table. It regularly exchange configuration message with other bridge, if one fails, network can adjust routing accordingly. • Bridge-to-bridge protocol ensures each network section can only access through a designated bridge. • Table is not permanent. For wired LAN, entries “age out” in hours; in wireless LAN, entries “age out” in minutes. Mobile IP • Wired node’s IP address associate with a particular physical location; wireless node is addressed by a protocol called Mobile IP. • Mobile IP allows nodes to take an IP address with them when they move. • Wireless node using mobile IP is known as a mobile host. • Mobile host can have 2 IP address at a time, one is home address which is permanent; the other is “care of” address which is temporary. • Foreign agents provide mobile host with “care of” address and home agents redirect package from home network to “care of” address. Security • Encryption is an effective security technique, there are 2 types of encryption technique. 1) DES chip - is a symmetric encryption method, use same key for encrypting and decrypting. 2) RSA - is an asymmetric encryption method, use different key encode and decode. Data is encoded using public encryption key, and decoded using private key. • Symmetric encryption is faster than asymmetric, but possible security risk. • Only encrypting sensitive message at higher application level before transmitting can reduce processing time. PERSONAL DIGITAL ASSISTANT (PDA) By Norman-Ngan Vu Lam What is PDA? • Personal Digital Assistant • A handheld PC that is capable of handling all the normal task of the organizer and more. Features of PDA • All Palm organizers include the following features: – Applications: Date Book, Address Book, To Do List, Memo Pad, Expense, Calculator, desktop e-mail connectivity, Security, Games, and HotSync software for local and remote synchronization – Modem-enabled and Internet-ready with TCP/IP software – An infrared port – Windows and Macintosh compatibility** Palm VII • Check stock quotes from the airport. Send e-mail from a taxi. Book a flight, get directions and read the news virtually anywhere, anytime. • Wireless Features of Palm VII • • • • • AAA bateries Data transfer rate at 8kbps 2 MB of RAM Web clipping Palm Query Application (PQA) Web Clipping Apps • Financial – – – • News – – – • ABCNEWS.com ESPN.com USATODAY.com Reference and Directory – – – • Bank of America Fidelity Investments E*Trade Merriam-Webster US WEST Dex Yahoo! People Search Travel and Entertainment – – – MapQuest.com Moviefone.com The Weather Channel iMessenger • Receiving messages – Through your user@Palm.net account – Only first 500 characters are being sent • Sending messages – There are 3 ways to compose text to send. 3 ways to enter data • Graffiti – Only display lower case • Onscreen keyboard – Both lower and upper case • Desktop keyboard – Hotsync technology Graffiti Characters On screen keyboard Area coverage for PDA What’s new? • Unlimited plan • Download web clipping apps at http://www.palm.net/apps/ PDA service plan Basic Plan Expanded Plan Volume Plan Unlimited Plan Monthly service fee $9.99 $24.99 $39.99 $44.99 Kilobytes included in your monthly service fee 50KB1 150KB2 300KB Unlimited Service Plan Options Sample monthly usage4 Each additional kilobyte One-time set-up fee 30 messages 20 stock quotes 10 sports scores 10 traffic reports 10 weather updates $.20 $9.99 90 messages 60 stock quotes 30 sports scores 30 traffic reports 30 weather updates $.20 $9.99 180 messages 120 stock quotes 60 sports scores 60 traffic reports 60 weather updates Unlimited $.20 $0 $9.99 $9.99 Strengths and weaknesses • Pros – Webclipping PQA – iMessaging • Cons – Coverage for wireless services too limited – Only 2MB of storage space – Expensive & monthly service charges too high References • • • • • • Shelly, Cashman, and Serwatka. “ Business Data Communications” International Thomson Publishing, 1998. Naugle, G Mathew. “ Local Area Networking” McGraw-Hill, Inc. New York, 1991. FitzGerald, Jerry & Dennis, Allen. “Business Data Communications and Networking”. John Wiley & Sons, Inc. New York, 1999. Robinson, Teri. “ Mobile Computing” Micro Times. No 203, pg137-39. Feb 8, 2000. www.blackbox.com www.calstatela.edu/cbtweb/curicula/courses/lant01e/lant01e.htm References • www.palm.net • www.palm.com • Hudson, I.J. “Intranet Access In the Palm of your hand” TechWeb www.techweb.com August 23, 1999 • The PC technology guide www.pctechguide.com/25mob2.htm