Ch 16 5 A Day_Javier Rodriguez
advertisement

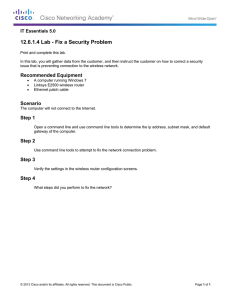
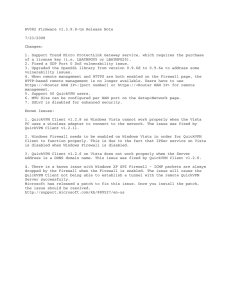
Cisco Chapter 16: Advanced Security 5 A Day (part 1) Name: ________________________________________________ 1. Which issue should be addressed in the detailed information that is provided by a local security policy? The cost and the access to the security 2. What are two interrelated aspects that would be involved in the physical security of an organization? Infrastructure and conduit. 3. Which two factors should management consider when developing a security policy? Security of data, and the cost of the software. 4. Why would security application software be implemented on a network? A firewall. 1. Which two hashing algorithms are used to ensure that messages are unaltered during transmission? SHA, MD5 5. Which data security technology takes the form of an object which must be close to a computer before the user can successfully submit a username and password? FOB 6. Which physical security technology uses an embedded integrated circuit chip to store data safely and is commonly used in secure ID badges? Smart card 7. Which two advantages are attributed to a hardware firewall when compared to a software firewall ? It doesn’t slow down the computer, It can be put on more than one computer Cisco Chapter 16: Advanced Security 5 A Day (part 2) 9. Why should the default username and password be changed as soon as an access point is powered on and accessed? It will provide minimal security. 10. A customer has a web server for a small business. The business uses both wired and wireless networking. A Linksys WRT300N wireless router provides wireless and wired connectivity. What firewall option may be enabled in order for customers to gain access to the web server from their remote locations? Enable port forwarding. 11. What can a homeowner who has a wireless router do to hide the wireless router signal from the surrounding neighbors? Disable ssid broadcast. 12. What is a feature of the firewall capability when Windows Vista is the operating system? It can be enabled and disabled. 13. Windows XP should be updated on a regular basis. In which situation should automatic updates be disabled? When you have a dial up connection. 14. Which Windows XP command initiates a backup from the command line? NTBackup 15. What are two features of Windows Vista Backup? It will be in a Zip file, and it can be saved on another computer. Cisco Chapter 16: Advanced Security 5 A Day (part 3) 16. After a technician collects information from the computer, which two sources can provide the technician with possible solutions for various types of network-related problems? Access to data and infrastructure. 17. A user reports that the antivirus software on a computer is always turned off when the computer is restarted, despite being reactivated each time the computer starts up. Further investigation by the technician shows that the Internet browser also displays an incorrect homepage. What is the probable cause of these problems? Spyware is on the computer 18. A network administrator is trying to change the account name of a user but cannot make the changes. What could be a possible cause? The administrator does not have enough permission. 19. After logging into a computer, a user is unable to access the CIW folder. Access to this folder is necessary to complete an assignment. Which two actions can the administrator take to provide the user access to the folder? GIVE PERMISSION TO THE PERSON, OR ASSIGN THEM TO A GROUP. 20. Which important feature is offered by the USB standard? It PROVIDES POWER.