MSDN Briefing - IIS 7.0
advertisement

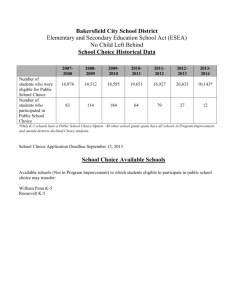
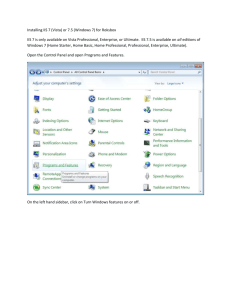
MSDN Briefing IIS7 für Entwickler Christoph Wille, MVP ASP.NET http://chrison.net/ i n t e r n e t i n f o r m at i o n s e r v i c e s seven integrated extensible componentized delegated secure compatible supportable IIS – A Colorful Past 1996 - V1 ships with WindowsNT 4.0 V2 & V3 releases came in follow-up SP releases 1997 – V4 part of NT 4 Option Pack 2000 – V5 installed by default in Windows 2000 2001 March 2001, #1 in Internet Site Share Fall 2001, Code Red and Nimda 2003 – V6 released in Windows Server 2003 IIS 6 Today Secure by Default IIS no longer installed by default with OS IIS installs with “locked down” configuration Runs with minimal permissions, secure configuration Secure by Design Extensive design & code reviews Penetration testing Defense in depth Process architecture design for application failure Health detection Automatic recycling of applications Result: Zero critical security patches since release. #1 in reliability for major internet sites. Agenda Architecture Overview Modularization Extensibility Administration & Troubleshooting For Developers Where do I get IIS 7.0? Windows Vista Editions with IIS 7.0 Vista Edition Available Home Basic N Home Premium N Business Y Ultimate Y Where do I start? What type of developer are you? Native Developers vs. Managed-code Devs Understanding the Core Server Architecture Installation Differences IIS 7.0 Rebuilt setup architecture Uses Vista’s Windows Features On and Off Can also use Vista’s Package Manager (Pkgmgr.exe) start /w pkgmgr /iu:IIS-WebServerRole;WASWindowsActivationService;WAS-ProcessModel; WAS-NetFxEnvironment;WAS-ConfigurationAPI Full Install of all IIS Components start /w pkgmgr /iu:IIS-WebServerRole;IIS-WebServer;IIS-CommonHttpFeatures;IIS-StaticContent; IIS-DefaultDocument;IIS-DirectoryBrowsing;IIS-HttpErrors;IIS-HttpRedirect; IIS-ApplicationDevelopment;IIS-ASPNET;IIS-NetFxExtensibility;IIS-ASP;IIS-CGI;IISISAPIExtensions; IIS-ISAPIFilter;IIS-ServerSideIncludes;IIS-HealthAndDiagnostics;IIS-HttpLogging;IISLoggingLibraries; IIS-RequestMonitor;IIS-HttpTracing;IIS-CustomLogging;IIS-ODBCLogging;IIS-Security;IISBasicAuthentication; IIS-WindowsAuthentication;IIS-DigestAuthentication;IIS-ClientCertificateMappingAuthentication; IIS-IISCertificateMappingAuthentication;IIS-URLAuthorization;IIS-RequestFiltering;IIS-IPSecurity; IIS-Performance;IIS-HttpCompressionStatic;IIS-HttpCompressionDynamic;IISWebServerManagementTools; IIS-ManagementConsole;IIS-ManagementScriptingTools;IIS-ManagementService;IISIIS6ManagementCompatibility; IIS-Metabase;IIS-WMICompatibility;IIS-LegacyScripts;IIS-LegacySnapIn;IIS-FTPPublishingService; IIS-FTPServer;IIS-FTPManagement;WAS-WindowsActivationService;WAS-ProcessModel;WASNetFxEnvironment; WAS-ConfigurationAPI IIS Minimal Install Architecture Introduction IIS 7.0’s architecture, albeit similar to IIS 6.0, offers unique changes Default architecture has same “players” with some fresh new ones W3SVC W W3WP A S HTTP.sys WPAS Inetinfo (optional) A Review…IIS 6.0 Architecture Authentication NTLM Basic Anon … Monolithic implementation Install all or nothing… CGI Determine Handler Static File ASP.NET ISAPI … Send Response Log Compress PHP Extend server functionality only through ISAPI… IIS7 Request Processing Server functionality is split into ~ 40 modules... Authentication NTLM Basic Anon Authorization … ResolveCache CGI … Determine Static File Handler ExecuteHandler ISAPI … … UpdateCache Send Response SendResponse Log Compress Modules plug into a generic request pipeline… Modules extend server functionality through a public module API. Architecture in IIS7 What does the “Core” do? Exposes interfaces Agrees to “hook” up interfaces via subscription or events Extensibility Primary workhorse for Web server Code authors: Microsoft: In the form of “modules” that will ship with the IIS7 platform You: The rest of the world IIS6 ASP.NET Integration Runtime limitations Only sees ASP.NET requests Feature duplication Authentication NTLM Basic Anon … CGI Determine Handler Static File ISAPI … Send Response Log Compress aspnet_isapi.dll Authentication Forms Windows … Map Handler ASPX Trace … … IIS7 ASP.NET Integration Basic Two Modes Anon Classic (runs as ISAPI) Integrated Authentication Authorization ResolveCache … ExecuteHandler … Integrated aspnet_isapi.dll Static File ISAPI UpdateCache SendResponse .NET modules Authentication / Forms handlers Windows plug directly … into pipeline ASPXall requests Process Map Trace fidelity HandlerFull runtime … Compress Log Mode … Reviewing IIS 7.0 Architecture IIS 6.0 W3WP’s IIS 7.0 W3WP’s Demo The Most Secure Web Server Ever Metabase vs. “AppHost.config” IIS 6.0’s Metabase Design Supported legacy, out-dated interface (ABO) Maintained own ACL’ing within file, rather than via file system ACL’ing Delegation wasn’t supported, relied solely on Administrative privileges Remote capabilities were limited, not userfriendly experience Schema wasn’t architected in easy-to-use format Extending schema was nearly impossible Metabase vs. “AppHost.config” (2) Introducing ApplicationHost.config Location: %windir%\system32\inetsrv\config Default configuration: All features disabled *except* Directory Browsing (directoryBrowse) Default Document (defaultDocument) HTTP Redirect (httpRedirect) HTTP Protocol (httpProtocol) Features unlocked using IIS Manager or ApplicationHost.config Metabase vs. “AppHost.config” (3) ApplicationHost.config Facts: Uses strongly-typed Schema (%windir%\system32\inetsrv\config\schema\IIS_schema.xml) Easily edited using favorite XML editor Broken down into two pieces: system.applicationHost system.webServer Delegation of IIS settings are unlockable and distributable to web.config’s deployed with content Metabase vs. “AppHost.config” (4) ApplicationHost.config Facts (cont.): Uses well-known XML Organized into tightly-coupled groups for like features (i.e. collections) Uses simple key\value pairs for many options like true\false, 0 or 1, etc. <directoryBrowse enabled="false" /> Extending schema is drag\drop experience (add XML file to /config directory and restart IIS) Configuration Highlights Delegated Configuration Administration Administrators may allow app owner to modify settings Developers can set and deploy settings with their applications Xcopy-deployment of self-contained applications without running admin tool or scripts to configure -- even to centralized UNC share Unified Configuration Model for Entire Web Platform Administrators may use same file for IIS, ASP.NET, Indigo settings Developers can use same API and concepts across entire platform AuthN, AuthZ, custom errors, handlers, etc are set one single way Extensibility and Customization is easy Administrators can control what sections are registered with the system Developers can reuse base classes to quickly develop custom sections Clean schema allows smooth editing by hand (text/XML editor), API or admin tool Compatibility Built-In at the API level ABO / ADSI scripts and applications continue to work Configuration Layout Inheritance… IIS IIS + ASP.NET + .NET Framework ASP.NET applicationHost.config .NET Framework web.config root web.config machine.config root configuration files web.config files Configuration Delegation Delegation is: Configuration locking, “overrideMode” ACL’s on configuration files By default… All IIS sections locked except: Default Document Directory Browsing HTTP Header HTTP Redirects All .NET Framework / ASP.NET sections are unlocked Demo Customized Workload Site Creation – A Tour of the UI Currently Executing Requests Configuring a Site for AuthN Modules vs. ISAPI IIS 6.0 Development First-class access to requests were only allowed using Internet Server API (ISAPI) ISAPI only supported C\C++ languages and was rather complex technology Client vs. Server Versions Windows XP Professional shipped with IIS 5.1 yet lots of development was for IIS 6.0 IIS 6.0 shipped on Windows Server 2003 and architected differently than IIS 5.x Modules vs. ISAPI (2) Client vs. Server Versions (cont.) Managed-code development architecture differed heavily between IIS 5.x & 6.0 ASP.NET was written as an ISAPI and had duplicate functionality as IIS 6.0 IIS 7.0 IIS 7.0 on client is the same as on Server (via service packs) Support for multiple development interfaces to interact with IIS 7 Core Server IIS 7.0 Native Modules Vista ships with the potential of 40+ modules Most are native modules built using the new Native C\C++ APIs Native modules are defined in the <globalModules> section of applicationhost.config IIS 7.0 full install has 33 native modules Utility Modules Used to help the server engine with it’s internal operations Do not provide configuration for these in applicationhost.config Module Name cacheuri.dll cachfile.dll cachtokn.dll Purpose If removed? Cache configuration, etc. after first request for a URI Cache of file handles currently opened by core server Caches token for passwordbased authentication Performance Performance Performance Compression Modules Provides Static & Dynamic compression mechanisms for IIS requests Module Name Purpose Compdyn.dll Implements in-memory compression of dynamic content Implements in-memory as well as file-based compression for static content Compstat.dll Configurable locations: system.webServer/httpCompression system.webServer/urlCompression If removed? None, not installed by default Network Bandwidth saturation with large requests Authentication Modules IIS 7.0 core authentication modules Module Name authanon.dll authbas.dll authsspi.dll authmd5.dll authcert.dll authmap.dll Purpose Implements anonymous authentication Implements HTTP basic authentication Implements Windows Authentication (NTLM\Kerberos) Implements Digest Authentication Implements IIS Client Certificate Mapping (Requires SSL) Maps SSL Client Certs to an Active Directory Account If removed? Anonymous Authentication is not allowed Basic authentication is not available Negotiate (Kerberos), NTLM are unavailable Digest Authentication is not available Client Certificates are not accepted for authenticatio Active Directory mapping is unavailable Security Modules Implements URL authorization, and IP\Domain restrictions Module Name Purpose Urlauthz.dll Implements authorization based on configuration rules Iprestr.dll Implements an authorization of requests based on the client’s IPv4 Address modrqflt Implements a powerful set of security rules based on known & unknown attack vector points (previously known as URLScan) If removed? No ability to do URLbased denying via configuration and users No Ip-based restricting of requests No request filtering based on extension, query string size, etc. Logging & Error Modules Implements logging functionality Implements custom & detailed errors Module Name Logcust.dll Loghttp.dll Custerr.dll Purpose Implements the ILogPlugin interface on top of IIS7. It is not recommended to use this as it is a old implementation. Recommendation is to write your own module and subscribe to RQ_Log_Request event. Implements standard IIS logging Allows for the use of custom errors and the new IIS7 detailed error features If removed? Applications dependent on legacy interface will not work No request data will be logged No error messages (custom or detailed) will be sent to clients Diagnostics Modules Implements IIS 7.0’s Request Monitoring, tracing, and Failed Request Tracing Module Name Purpose If removed? iisetw.dll Implements Enterprise Tracing for Windows functionality to capture detailed trace logs No tracing of specific requests are available iisfreb.dll Implements tracing of failed requests No automatic tracing based on the configured rules iisreqs.dll Implements the runtime state & control APIs for IIS 7.0 allowing viewing of executing requests, start\stop of sites, etc. Unable to see runtime data or start\stop\pause websites Development Modules Development technologies offered as to execute code from that platform Implements Managed Interfaces, etc. Module Name Isapi.dll Filter.dll Cgi.dll Purpose Implements ISAPI Extension Server Functionality Implements ISAPI filter functionality Implements Common Gateway Interface (CGI) on top of IIS 7.0 Webengine.dll Connects the IIS core pipeline with the ASP.NET runtime and bridge between native and managed code in IIS 7.0 If removed? No ISAPI extension will be executed No ISAPI filter will be loaded into any process No CGI dll or exe will is executed No managed code will be supported in IIS 7.0 Misc. Modules Performs independent functionality outside of any group Module Name Purpose If removed? defdoc.dll Implements default document feature using defaultdoc section files Specific URL is required and any / will fail dirlist.dll Implements IIS 7.0’s directory browsing functionality Implements: • custom/redirect response headers • custom HTTP verbs (trace\options) Directory browsing will not be allowed Specific features outlined in purpose will not be available protsup.dll • allows use of HTTP keep-alive redirect.dll Implements redirect functionality of incoming requests If redirects are removed, content protected by redirect will be available Misc. Modules (cont.) Module Name Purpose If removed? Iis_ssi.dll Implements server-side includes Special case where this module is actually mapped as handler for .stm, .shtm, and .shtml static.dll Responsible for sending out reponses for extensions listed in mimeMap section Without it, no static file (htm, images, etc.) will be sent to client validcfg.dll Validates at run-time if configuration is valid for IIS 7.0’s integrated mode No validation or help is available when configuration is deployed improperly IIS 7.0 Managed Modules Managed Modules are loaded in two ways Called by webengine.dll (integrated mode) Called by core ISAPI module – isapimodule.dll (Classic) Integrated Mode offers ASP.NET module features access to all types of content Classic mode runs exactly like IIS 6.0 & ASP.NET 2.0 Managed modules are only defined at application level (<modules>) along with native modules IIS 7.0 Managed Modules Implements managed code module parity with ASP.NET 2.0 Requires webengine. dll native module to execute Name Purpose WindowsAuthentication Sets the identity for the application to the WindowsAuthenticated user FormsAuthentication Allows authentication against all content using forms-based authenticaiton to a database\file DefaultAuthentication Ensures that an auth object is present in the app context OutputCache URLMappingModule Session UrlAuthorization Profile RoleManager FileAuthorization AnonymousIndentification Controls the output caching policies for your applcation Defines a mapping that hides the real URL and maps to a friendly one Configures session state settings for current application Allows URL-based authorization via managedcode Configures parameters for mapping user profiles values Configures an application for role management Allows file-based authorization via managed-code Configures anonymous auth for application authorization s y s t e m . w e b Demo URL Rewriting Directory Listing Basic “Deluxe” IIS 6.0 Tracing vs. Failed Request Tracing Tracing: What it is? IIS 6.0 Usage: No User Interface Support Updated as part of Service Pack 1 Very difficult to restrict tracing to extensions, or paths Not extensible with custom events written by developers IIS 6.0 Tracing vs. Failed Request Tracing (2) IIS 7.0’s Failed Request Tracing Setting up Tracing: • IIS Manager • Enabled Globally (Administrator) • Actual Trace attributes settable per-site or perapplication IIS 6.0 Tracing vs. Failed Request Tracing (3) Viewing Trace Data in IIS 6.0 difficult, yet when understood is very useful Viewing Trace Data in IIS 7.0, easy-touse XLST breaks out various data to simplify reviewing Demo FREB in Action IIS 6.0 Security vs. 7.0 Security IIS 6.0 Security – All Bits Installed (%windir%\system32\inetsrv) “Features” turned on\off Uses local account and group for anonymous client requests and process account IIS_WPG: Group for allowing process creation and security URLScan added for additional security features not offered by Core server IIS 6.0 Security vs. 7.0 Security (2) IIS 7.0 Security: Change Purpose Benefit Only Install Bits Selected Reduce the footprint, lesson management tasks such as patching, etc. Build truly customizable Web workloads to maximize security and improve performance Convert URLScan to installable features, rather than add-on Bring a popular security tool into the product to simplify deployment, configuring, and supporting With one click, RequestFilteringModule can be installed, and with one easy file deployed with your content it is working Change local accounts to built-in accounts Avoid management of passwords, ACL’ing problems and better handle Web farm deployments Every installation of IIS 7.0 installs the same accounts, with same GUIDs, and with same ACLs and everything “just works.” Unified authentication, authorization across web server platform Fully supports non-Windows principals! All authentication schemes configured one single way for all types of content Forms authentication is now fully supported IIS extends its ACL authorization model with URL Authorization: Membership system support (includes support for custom providers) Windows principals (stored in the local SAM or Active Directory) Custom configuration credential sections (non Window principals) Unified Authentication and Authorization Reconciled impersonation model IIS 7.0 always uses the following rules (in order of precedence) 1. If a username/password is configured at a virtual directory it is used first 2. If virtual directory username/password is not configured, the authenticated users credentials are used (anonymous, basic, windows) 3. If no authenticated user (e.g. if forms authentication was used or no authentication module is configured) the process identity is used Unified Authentication and Authorization Reconciled impersonation model IIS 7.0 always uses the following rules (in order of precedence) 1. If a username/password is configured at a virtual directory it is used first 2. If virtual directory username/password is not configured, the authenticated users credentials are used (anonymous, basic, windows) 3. If no authenticated user (e.g. if forms authentication was used or no authentication module is configured) the process identity is used Web user requests page VDIR has username and password configured Credentials configured for the virtual directory are used Unified Authentication and Authorization Reconciled impersonation model IIS 7.0 always uses the following rules (in order of precedence) 1. If a username/password is configured at a virtual directory it is used first 2. If virtual directory username/password is not configured, the authenticated users credentials are used (anonymous, basic, windows) 3. If no authenticated user (e.g. if forms authentication was used or no authentication module is configured) the process identity is used Web user requests page VDIR has no username, password configured User is prompted and provides valid Windows credentials. Note - the <authentication> section needs to be configured The client credentials or anonymous identity provided during authentication is used Unified Authentication and Authorization Reconciled impersonation model IIS 7.0 always uses the following rules (in order of precedence) 1. If a username/password is configured at a virtual directory it is used first 2. If virtual directory username/password is not configured, the authenticated users credentials are used (anonymous, basic, windows) 3. If no authenticated user (e.g. if forms authentication was used or no authentication module is configured) the process identity is used Web user requests page VDIR has no username, password configured No user authentication is configured The process identity is used Unified Authentication and Authorization Reconciled impersonation model ASP.NET developers can still define their own identity section if required by their applications Useful for applications that reside on different machines Web user requests page IIS uses any of the impersonation methods and impersonates some Windows identity ASP.NET developers can use their web.config to impersonate an alternate identity (example - for database access) Demo Extending AuthN & AuthZ Administration Extensibility Delegated administration Non-administrators can change relevant settings. Admins specify what’s allowed per site and application. Unified management for the entire web platform IIS and ASP.NET settings are presented within the same user interface. Extensible architecture Developers can create custom management features. Remote administration Administer locally, over the intranet, or over the Internet. New modern look and feel A new navigation-based, task-oriented, rich user experience. Architecture Web Management Client Connection Manager Module UI Content and Configuration Login Handler IIS 7.0 (http://server/MyApp) Connection Connection Module Service Service Proxy Module UI Web Management Server (Standalone Web server : http://server:8080/… ) Runtime state Provider Data Application appdomain Provider Extensibility Extensibility Points New Features and Pages Register new pages with the Control Panel Existing plug-in points Authentication Lock Configuration Provider Configuration Validation Custom extensibility using the Extensibility Manager Extensibility Adding a new management module Server Write a new Module Provider Write a Module Service Install the DLL to the GAC Register the module in the root configuration Enable the module Client Write a new Module Write a Module Service Proxy Write some Module Pages Plug in existing features using the Extensibility Manager Demo MRU Server Header End-to-End Sample with Module Microsoft.Web.Administration Demo Microsoft.Web.Administration Listing Sites Creating a Site App Pool Creation Summary Something new for everyone in IIS 7.0 Most radical changes in IIS since IIS 4.0 IIS 6.0 was… Limited for Developers because of ISAPI and less-than desirable support for Managed-code Limiting configuration for key scenarios, such as delegation and schema extensibility Limited troubleshooting capabilities to support zero-repro environments IIS 7.0 is… Easy to extend using any language, native or managed Robust configuration supporting delegation, schema extensibility Task-based oriented, newly re-written IIS Manager supporting delegation, and much more Has awesome diagnostics which is natively built-in to the plumbing of IIS 7.0