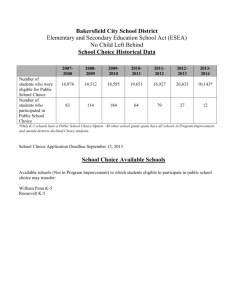
IIS7 Security
Proven Scalability
Proven Security
Proven Trust
A solid foundation to build on.
Two security patches for IIS 6 since RTM (>3 yrs)
2002
2003
4/15
Server2003
RTM
2004
2005
2006
(WebDAV DoS)
(ASP)
06/11
06-034
10/12
04-021
IIS 6
6/11
4/10
02-018 02-028
IIS 5
8
10/30
02-062
5/28
03-018
4
4
7/13
04-021
8
IIS 4
4
< Critical
= Critical
X
= Rollup with
X updates
4
Notes
•MS02-011 & 012 not included: updates SMTP service only
•ASP.NET adds:
1 – v 2.0 2 - v 1.1
3 - v 1.0
• Modular Design:
– Reduced exposure at installation and runtime
• .Net Integration:
– Forms Auth for any content
– Use of .NET Role and Membership Providers
• Built in anonymous account
– Easier to administer, restore, and configure
• Application Pool Isolation
– Improved Sandboxing between applications
• URLAuthorization and Request Filtering
– New choices for improving security
• Kernel mode SSL and authentication
– Faster negotiation of security exchanges, fewer
problems
Features implemented as discrete
modules
Modularity improves security
Reduced module set by default at install
Remove modules that you do not need
Extensibility allows security customization
Add authentication, logging, or blocking
mechanisms
Integrated pipeline enables Forms
authentication with any content
Leverage existing user database with
.NET Role/Membership providers
Examples: Store user names in:
Active directory or local SAM
SQL 2005 Express for static site users
ADAM for users and groups in a PHP application
DB2 mainframe users and groups in ASP.net
#1 of 6
Control access to sites, folders, or files
without using NTFS
Inspired by ASP.net URL authorization, but
designed for administrators
Rules are stored in .config files
Delegate control to store in web.config
Authorization rules are then portable
Xcopy and maintain security
Use Windows principles or .NET provider
Native to IIS 7
#2 of 6
IIS 7 integrates URLScan style rules
Very strong security feature
Prevent URLs that contain “any string”
Block URLs over “X” in length
Prevent delivery of “.config” or “/bin”
Easy to read rules stored in .config
Delegate control to store in web.config
Filtering rules are then portable
Cannot be edited in UI
New error codes track rejections
#3 of 6
• IUSR instead of IUSR_<servermame>
• IUSR is “built in”, not a local account
– Cannot logon to system with this account
– No password to worry about
– Same SID on all Vista/LH servers
– File ACLS are valid between servers
• Allow anonymous access & turn off IUSR:
– Use process identity for anon access when
enabled
– Disabled by default
IIS_WPG local group in IIS 6
All app pool identities must be in IIS_WPG
Creates administrative overhead
Adds complexity to hardening/pool isolation
IIS_IUSR replaces IIS_WPG
Built in group, not local
Well known SID means ACLS respected
Pool identities are automatically added
#4 of 6
New IIS 7 feature significantly improves
application pools isolation
Prevents attacker from reading secrets in
another pools config
Works automatically, and is transparent to
configuration and operation
Process identity is unchanged
Network Service by default
Note that application pools cannot ready
Applicationhost.config by default.
Each site is assigned to a unique pool
Occurs automatically with new site in UI
At runtime:
Unique SID for pool is “injected” into the
process’ list of SIDs
Does not change process identity
A “temp” config file is created that contains
only config settings for the pool
The temp config file is ACLd with unique SID
SID will be the same on other servers
#5 of 6
Additional steps for increasing security
Disable anon user
appcmd set config -section:anonymousAuthentication -userName:"" --password
All anon access will occur as process identity
Set content for access by App Pool unique
SID (with icacls)
Local content only, won’t work for UNC content
Create secure location for
ASP template cache
Compressed content
Create ASP.net temp file location for pool
appcmd set config "Default Web Site" -section:compilation tempDirectory:%systemdrive%\inetpub\temp\aspnettemp\site%1 /commit:webroot
Advanced Hardening
#6 of 6
Kernel Mode SSL
Improves performance
Reduces context switch to user mode
Kernel Mode Authentication
Improves performance
Kerberos functions when using custom
application pool identity!
No need to use SETSPN as access to DC
occurs as machine account
IIS 7 provides improvements and new
capabilities that increase security and
simplify administration
Feature
Beneft
Modular Design
Reduce Footprint, less exposure
Built in anonymous user
Can’t expire or lockout, no password to
manage
Disable anon user
Simplify ACLs on content
Integrated pipeline
User Forms authentication and .NET
role/membership providers
Request Filtering
Prevent malicious content from reaching
applications
URLAuthorization
Use file based rules instead of ACLs to
control access
Kernel Mode Authentication and SSL
No SETSPN with custom pool identities.
Faster SSL and auth.
Application Pool Sandbox
Improved isolation between pools
© 2007 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries.
The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it
should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation.
MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.
IIS 6 used different rules for local vs unc
IIS 7 rules are simplified to be consistent
Rule: If username and password is supplied
for a site or directory, they are used to all
content regardless of location.
Enable for
Delegation
Read/Write: If set, delegation is enabled
• Q: Where do I configure Read/Write
•
•
•
•
•
•
properties that were in IIS 6?
A: Handler properties
Q: How do I install a Certificate
A: Install a Self Signed Cert in the UI or use
wizard
A: What happened to Web Service
Extensions?
Q: Implemented as ISAPI and CGI restrctions
In the UI
Q: Do I need URLScan
A: No.
Difference
Rule evaluation
IIS7 User Interface
Configuration section
Module
Content
ASP.NET Url Authorization
Behavior
IIS7 Url Authorization
Behavior
Order:
a) Deny rules get
Order:
evaluated first starting at
a) Lower level first
the parent
going up to the parent
b) Allow rules starting
b) Order of appearance
at the parent.
in rule collection
c) Order of
appearance in rule
collection
"Authorization Rules" User
No IIS7 User Interface
Interface
system.webServer/security/a
system.web/authorization
uthorization
System.Web.Security.UrlAut %windir%\system32\inetsrv\
horization
urlauthz.dll
Applies only to content that
is mapped to a managed
handler (can be turned off
Applies to all content
via managedHandler
precondition)