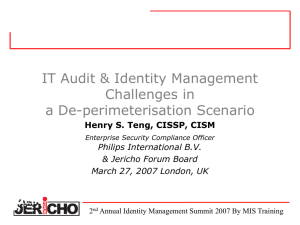
Metrics - The Open Group
advertisement

Welcome 1st Jericho Forum Annual Conference 26th April 2005 Riverbank Hotel, London Hosted by SC Magazine 1 Welcome Richard Watts Publishing Director, SC Magazine 2 Agenda 11:35: 11.45: 12.05: 12.25: 12.45: 13.00: 14.30: 14.50: 15.15: 15.45: 16:45 17:00 Welcome The Challenge YOU are facing What is Jericho? What has it achieved in the past year? What are we doing going forwards Lunch Mutually beneficial vendor involvement Where could Jericho take us? Break (Coffee & Teas) Panel Debate & Audience Questions moderated by Ron Condon Summing up the day Close 3 Welcome Ron Condon Editor in Chief, SC Magazine 4 The Challenge YOU are facing John Meakin Standard Charter Bank & Jericho Forum Board 5 Tearing Down the Walls: The Business Case for Jericho Agenda The Business Problem The Death of the Perimeter The Security Problem The Potential Solution Scenarios The Future 6 The Business Problem Business trends & needs breaking traditional network perimeter – – – – Cost effective networking Collaborative business Outsourcing Joint venturing For Standard Charter Bank: – Challenge of doing business in Africa • Network bandwidth availability – Challenge of grasping market opportunity • Eg Afghanistan, Iraq 7 Current Network Security Strategy “It’s all about the firewalls….” Premise: – – Control remote connectivity for: – – – – SCB internal network is “open” at network layer All restriction of access and protection of data occurs at higher layers (host, application, etc) off-network hosts/people via “trusted”/“untrusted” networks “trusted” third-parties via “trusted” third-party networks “trusted” third-parties via “untrusted” networks, ie Internet “untrusted” third-parties via Internet Maintain same level of trust at each layer in multi-layer boundary model Ensure that SCB network protected by “defence in depth” Provide range of cost-effective solutions for above scenarios Provide resilient connectivity as option where business transaction requirements specify 8 1BPN Illustrated Counter-party Authentication PSDC/PSAC Authentication Internet Requester Identification PSDC Channel - Tier 1 Boundary Auditing Auditing EDI - Tier 2 Boundary EDI Application SQL*net Logic Requester SOAP/ HTTP BPEC - Tier 1 Boundary User ID + Auth SOAP/HTTP PSDC Channel Third Party Network Identification Auditing HTTPS WWW Server Interface mediation BPEC Application Server ApplicationSQL*net Logic Application Server SQL*net SOAP/ HTTP Tier 2 (GWAN) Boundary SQL*net PSDC Channel Application DBMS Auth DBMS SOAP/ HTTP - Tier 3 (GWAN) Boundary Application DBMS Internal Application Server Internal Appl'n Brokerage ISIS Internal Appl'n Brokerage Auth DBMS Back Office System Tier 1’s Data Storage Tier 2’s Data Storage 9 Internal Application Server ISIS Back Office System Connectivity Scenarios Unit Costs ($k) Remote SCB Users Components Network Switches - Tier 1&2 Network Switches - Tier 3 Load Balancing Traffic Shaping Firewalls - Tier 1&2 - Central Firewalls - Tier 1&2 - Remote Firewalls - Tier 3 DNS Servers Proxy Servers Intrusion Detection Systems VPN Head-End VPN Client + Authenticator Authentication Servers (RADIUS & Ace) Remote Client Firewall Security S/w (eg URL blocking, Malw are Filtering) Application Web Servers Application Data Servers Application-Specific Proxy Servers Component-only Cost Total Implementation Manpower (inc build, OAT, SAT, etc) Build Cost Total Hardware Maintenance/yr Software Maintenance/yr Operating Manpower (1 yr) Penetration Testing Manpower (1 yr) Operating Cost Total Total Costs ($k) Firewalls - Tier 3 cost as % Total Firewalls cost as % Total Exchange Staff Data Internet Feed, ie Surfing, Small Remote (x1000) Office BPEC 14 15 Electronic Bank ing System, ie PSAC or ie HA-PSDC SS-PSDC ie PSAC 25 14 28 11 12 5 5 32 11 50 10 10 11 12 2 21 11 12 5 5 32 32 11 0 10 Customer Information Transfer, 25 2 28 14 21 12 7 4 43 40 10 10 ? ? ? ? ? ? ? ? 160 92 74 89 126 79 6 165 19 67 1 3 96 18 17 1 3 39 134.56 0.0% 21.2% 5 79 15 6 0 16 37 115.69 0.0% 39.4% 4 93 16 16 1 13 45 138.17 0.0% 18.9% 8 134 25 10 1 20 55 189.52 4.6% 28.7% 5 84 16 7 0 18 40 124.43 2.8% 23.6% 88 252.59 0.0% 10.3% 10 NOTE: This analysis ignores the combination of multiple solutions into a single firewall complex (typical for PSAC installations with Remote SCB Users/Internet Surfing/Email, etc). NOTE: Total cost for 1000 Remote Users Costs dependent on Application design Cost for HABPEC Is 22% more Cost for split-site HA-PSDC Is 35% more The Death of the Perimeter (Banking) Business is conducted over networks – Multitude of connection points – Multitude of traffic types (protocols, content) – Complication! Traditional perimeter security doesn’t scale: – For filtering of addresses or protocols – For management of multiple gateways Mobile & wireless technology (largely) ignores the perimeter control Most large corporates have leaky perimeters Perimeter security does nothing about data flow and residence 11 Fortress Firewall - Old Technology? 12 Terminology “De-perimeterisation” vs “Radical Externalisation” vs Shrinking Perimeters 13 The Challenge Business transactions – from any PC – on any network – anywhere – by anyone of a wide range of different personnel Direct to one/more small corporate “island” core(s) With fully “externalised” network 14 15 Increasing Management & Integration Required “Traditional” Internet B2B “Traditional” Trusted Third-Party Core to Core over Internet Branch Office to Core over Internet Rep Office to Core over Internet Third-Party Managed Office to Core Server to Server over Internet Home PC to Core over Internet Mobile Device to Core over Internet Kiosk PC to Core over Internet Shrinking Perimeter Scenarios Branch Office to Core: Site-Site VPN Printer Computer SCB GWAN VPN box Ethernet Internet VPN box Inner Firewall Server Firewall Outer Firewall Log Server 16 Firewall Managed Office 17 Cybercafe/Kiosk/Airport Lounge 18 The Security Problem The remote PC – Is it securely configured? – Is it infected with malware? – What about data stored locally? The network – What happens to my data passing over it? The island host – Who do I let in? – How to I exclude others? The management – How to manage ‘000s of points of control to the same standard with robustness 19 So What Do We Need to Do? Vendors claim they have the answer BUT! – Partial delivery – Proprietary solutions – No integration cross-vendors We need: – Definition of business scenarios – Standard Technology Requirements Definitions “Sell side” needs to listen – And integrate – Preferably cross their traditional boundaries! So what is Jericho? – Over to Paul…..! 20 What is Jericho? Paul Simmonds ICI Plc. & Jericho Forum Board 21 Agenda First, what actually is de-perimeterisation Then, the Jericho Forum – How the two are related – It’s composition – It’s relationship with the Open Group – It’s charter – It’s remit 22 So what is de-perimeterisation? It’s fundamentally an acceptance that; Most exploits will easily transit perimeter security – We let through e-mail – We let through web – We will need to let through VoIP – We let through encrypted traffic (SSL, SMTP-TLS, VPN), Your border has effectively become a QoS Boundary Protection has little/no benefit at the perimeter, That it’s easier to protect data the closer we get to it, That a hardened perimeter strategy is at odds with current and/or future business needs, That a hardened perimeter strategy is un-sustainable. 23 So what is it actually? It’s a concept; It’s how we solve the business needs for our businesses without a hardened perimeter, Its how businesses leverage new opportunities when there is no hardened perimeter, It’s a set of solutions within a framework that we can pick and mix from, It’s defence in depth, It’s business-driven security solutions It is not a single solution – it’s a way of thinking . . . Thus; There’s a need to challenge conventional thinking There’s the need to change existing mindsets 24 Why the Jericho Forum? Why now? No one else was discussing the problem Everyone was fixated on perimeter based designs Somebody needed to point out the “Kings new clothes” to the world Someone needed to start the discussion What’s in it for us? Ultimately, we need products to implement We need to stimulate a market for solutions to de-perimeterised problems 25 The Jericho Forum Composition Initial Composition Initially only consumer (user) organisations – – – – To define the problem space To create the vision Free from perception of taint from vendors With the promise of vendor involvement once the vision defined That point is here now, and we have our first vendor members But with safeguards to ensure independence; User members own the Forum, vote on the deliverables and run the Board of Managers Vendors have no voting rights on deliverables or the direction and management of the Forum. 26 The Open Group relationship Why the Open Group? – Experience with loose “groups” of companies and individuals – Track record of delivery – Regarded as open and impartial – All output is free and Open Source – Existing framework with a good fit – Existing legal framework – Global organisation 27 The Jericho Forum Charter & Remit What Jericho Is . . . There to start the discussion / change the mindset The arbiters of making de-perimeterised solutions work in the corporate space There to refine what are Jericho Architectural principals vs. Good Secure Design Building on the work in the visioning document To define key items aligned with the message that make this specifically Jericho There to clarify that there is not just one “Jericho solution” What Jericho is not . . . Another standards body A cartel – this is not about buying a single solution There to compete with “good security”. 28 Dating & Secure System Design When it comes to dating, at best you get to pick two out of the following three; – Clever – Beautiful / Handsome – Great Personality / Character Traits So, given budget & development timelines, at best you have to pick two out of the following three; – Fast (Speed to market) – Feature Rich – Secure With acknowledgement to Arian J Evans 29 Jericho Principals vs. Good Secure Design Fast Delivery COTS Secure Design Inherently Secure Systems, Protocols & Data De-Perimeterised Architecture Feature Rich Business Driven 30 The Jericho Forum Challenge We believe, that in tomorrow’s world the only successful e-transactions & e-businesses will utilise a de-perimeterised architecture Thus you only have two choices; Do you sit back and let it happen to you? Or Do you help design the future to ensure it fits YOUR business needs? 31 What has it achieved in the past year? Andrew Yeomans Dresdner Kleinwort Wasserstein & Chairman of the Jericho Technology & Standards Working Group 32 A year or so ago, a few good men…. ICI BP Standard Chartered Bank Royal Mail Met over a few drinks, and the odd meal, and pondered the meaning of life, but also why this security stuff they were buying wasn’t solving the problems they were encountering . . . 33 Got rather more (men and women) . . . ABN AMRO Bank Airbus Barclays Bank BAE SYSTEMS Boeing BBC BP Cabinet Office Cable & Wireless Credit Agricole Credit Suisse First Boston Deloitte Deutsche Bank Dresdner Kleinwort Wasserstein Eli Lilly Ernst & Young LLP GlaxoSmithKline HSBC ICI ING JPMorgan Chase KPMG LLP (UK) Lockheed Martin Lloyds TSB National Australia Bank Group (Europe) Pfizer Procter & Gamble Qantas Reuters Rolls-Royce Royal Mail RBS 34 Royal Dutch/Shell Standard Chartered Bank The Open Group UBS Investment Bank UKCeB (Council for eBusiness) Task Force Unilever University of Kent Computing Laboratory YELL = Founders ..with various roles… Chief Information Security Officers IT Security Directors/Managers Director’s of Global Risk Management Senior Information Security Engineers Enterprise Risk Services Managers Directors of Architecture Global Security Services Managers Forward thinking, highly respected security strategists 35 …worked up about this… Admin Customers Partners Suppliers Applicatio n Systems Everything runs on: • Same physical wires • Same logical network Genera l Users 36 • Joint ventures • Outsourcers • Offshore providers …and wider stakeholders and their goals… Board of Directors Executive Management Owners/ Investors Customers Community External Auditors Governance CISO / Security Team IT function Other functions Lines of Business Avoid/Contain Local/Personal Risks 37 Regulators Internal Auditors Demonstrate Account-ability and Compliance Achieve Control and Authority Avoid/Contain Enterprise Risks …or in words… The traditional model of a hard perimeter and soft centre is changing as : – Your people move outside the perimeter – They are not just ‘your’ people any more – Business partners move inside the perimeter The policy is out of sync… – too restrictive at the perimeter (default deny) – lacking in the core (default allow) 38 39 …with wider general consequences, e.g. Trust models – conventional thinking – Architecture-centric governance models lead us to federated identity management and trusted second/third parties – Stakeholder-centric governance models lead us to regulatory solutions and ‘industry’ initiatives, e.g. e-marketplaces – Both approaches may be constrained, if not doomed! Question What does a ‘corporate’ policy look like for a virtual organization? Answer The assumption of ‘organization’ breaks down: need granularity 40 …and we also agreed where we’re headed Secure buildings Personnel contracts Permissions/ Vetting Guards and gates 1980s 1990s Network firewalls Managed Networks Directories Single sign-on Perimeter Security ? Streetwise users Virtual Enterprises Virtual Security…? 41 ? 21st Century Cyberspace road warriors …but – how soon will this hit us? “People often overestimate what will happen in the next two years and underestimate what will happen in ten. I’m guilty of this myself.” Attributed to Bill Gates 42 …the answer to which splits into these: What’s changing How soon…? Static, long term business relationships Dynamic, global business partnerships Assumption that threats are Threats are everywhere – external – perimeters perimeters defend a network, responsible for protecting but highly mobile devices all assets from all external must defend themselves: attacks defence in depth needed Traditional client server environment used by an office based workforce Growing use of multi-tier applications / services by an increasingly virtual user-base Operating System and Network based security controls Protection extended to applications and end user devices 43 …and led us to some initial conclusions… Impacts of the information age are now well known: Network externalities, disintermediation Power of globalisation Information Risks and their impacts We have lessons from other infrastructure changes (electricity, railways, etc) Tools such as Technology Road Mapping and Scenario Planning can be used to explore the impact of key drivers, trends and events IT products emerging in the next 3 -10 years are likely to be in today’s research labs …so this is about getting the right products in place 44 …plus some observations on root causes… Many IT ‘standards’ are broken in practice, e.g.: Certificate/CRL (non) processing in SSL Bug-compatible implementations of X.509 certificate extensions processing in crypto software Representing collaborating/cooperating organisations in X.500/LDAP; directory interoperability Re-inventing the wheel for security services for XML (Signatures, Encryption, Key Management…) Repeated technical standards initiatives with little or no ‘user’ / vendor dialogue: Vendors supposedly understand ‘user’ requirements ‘Users’ can’t and/or don’t articulate what they want… 45 …as well as lively debate on what to call it… De-Perimeterisation Re-Perimeterisation Radical Externalisation Security Without Frontiers Boundary-Less Information FlowTM 46 …with a key qualification on the “de-” Why would you still have a perimeter? – – – – – – – – Block external attacks in network infrastructure IP spoofing Block noise and control intranet Denial of service attacks Protection from random traffic Routing and network address management Legal barrier Evidence of corporate boundary Depending on business mission, criticality etc. 47 So, the Vision we agreed was: Vision To enable business confidence for collaboration and commerce beyond the constraint of the corporate, government, academic & home office perimeter, through; – Cross-organisational security processes and services – Products that conform to Open security standards – Assurance processes that when used in one organisation can be trusted by others Initial visioning whitepaper at: http://www.jerichoforum.org 48 …and the Mission and Milestones: Mission Act as a catalyst to accelerate the achievement of the Vision, by; – Defining the problem space – Communicating the collective Vision – Challenging constraints and creating an environment for innovation – Demonstrating the market – Influencing future products and standards Timetable A period of 3-5 years for the achievement of its Vision, whilst accepting that its Mission will be ongoing beyond that. 49 We established Working Groups . . . Meta Architecture Conceptual scope, structure, dependencies and Trust Models Future business requirements for identity Technology & Standards Intercepts with current/future vendor R&D and Requirements Future business requirements for information & Ontology management and security requirements management Management & Monitoring Future business requirements for operational security PR, Media & Lobbying Promotion of our programme in public affairs, relevant objectives for de-perimeterisation management and assurance product roadmaps management in de-perimeterised environments interest groups and regulatory/ legislative agendas; collaboration with these groups 50 . . . and defined an initial set of scenarios Provide low-cost connectivity Support roaming personnel Allow external access Access over wireless/public networks Identity theft, phishing etc. Domain inter-working via open networks Standards complexity and lack of Phoning home from a hostile environment On-demand trust validation; Enable portability of identities and data Credentials, attribute/ policy based Application access by suppliers, distribution Poor integration of strategic applications Outsourced help desk access to internal Least privilege remote access Connect organisations using secure XML Standards complexity / inadequate trust Consolidate/ interconnect identity and access Incomplete interoperability standards Automate policy for controlled info sharing Securing the semantic web Harmonize identities and trust relationships ‘Individual-centric’ security agents or business partners systems Improve flexibility management with individuals 51 interoperability; IPv6 environment isolation/security access security (ERP/CRM etc) with security standards models …with ever-greater priorities Provide low-cost connectivity Support roaming personnel Allow external access Access over wireless/public networks 1.9 1.3 Domain inter-working via open networks 3.1 2.0 Phoning home from a hostile environment 2.1 1.6 Enable portability of identities and data 2.8 1.8 Application access by suppliers, 2.0 1.8 Outsourced help desk access to int. 2.8 2.5 Connect organisations using secure XML 2.6 1.9 Consolidate/ interconnect identity & 2.9 1.6 Automate policy for controlled info sharing 3.3 2.3 Harmonize identities and trust 2.6 1.8 distribution agents or business partners systems Improve flexibility access management relationships with individuals Score: 1 = high priority, 3 = medium, 5 = low priority 52 What are we doing going forwards Adrian Seccombe Eli Lilly & Chairman, Trust Model Working Group 53 Jericho Forum Way Forward Jericho will provide thought leadership on all aspects of de-perimeterisation Strategies being deployed; – – – – – – – Formal working groups within Jericho Foster academic links and research Continue evangelisation Promote independent discussion and research Competitions Conferences Expand Membership 54 Jericho Forum Working Groups Jericho Forum working groups will only exist for the necessary period of time To date two have been convened and disbanded as their work is complete; – Jericho Forum Management & Transition to Open Group – Visioning Working Group Six currently exist 55 Jericho Forum Working Groups . . . Meta Architecture Conceptual scope, structure, dependencies and Trust Models Future business requirements for identity Technology & Standards Intercepts with current/future vendor R&D and Requirements Future business requirements for information & Ontology management and security requirements management Management & Monitoring Future business requirements for operational security PR, Media & Lobbying Promotion of our programme in public affairs, relevant objectives for de-perimeterisation management and assurance product roadmaps management in de-perimeterised environments interest groups and regulatory/ legislative agendas; collaboration with these groups 56 What are Working Groups? Tried and tested model for cooperative working – Used by Open Group Products of working groups submitted for voting by Forum members Method of working: – Few meetings – workshops – Telephone conferences – Email Two current active working groups: – Trust Models – Technology & Standards 57 Work Group Participation Membership of Jericho Forum required Four Levels of participation identified: – Type 1 • Physically Engaged << Commitment to attend occasional TMWG meetings as well phone calls & email and being a Mentally Engaged Contributor – Type 2 • Mentally Engaged << Willingness to remotely engage in TMWG meetings as well as contributing outside the meetings – Type 3 • Contributor << Willingness to occasionally contribute – Type 4 • Observer 58 Trust Models Working Group Vision of Jericho Forum dependant on degree to which information requires to be trusted and protected Model will identify various entities or assets involved in flow of protected, trusted information Model will NOT attempt to define standards, or design solutions for these requirements 59 Why Model Trust? In the past Trust based on Human Interaction and Written Legal Contract Today information flows electronically at speeds that transcend these mechanisms New model for electronic trust required – accelerate development and ensure maintenance of trust in new electronic domain 60 Example Trust Model 61 Technology & Standards Work Group Working out the “nuts & bolts” for Jericho… Requirements Roadmap – Requirements based on Visioning White Paper – More explicit Business angle (What’s In It For Me) – More specific Threat landscape Technology Roadmap Short-term, 6-month & Long-term deliverables 2-way communication with other Jericho WGs – particularly Architecture, Trust Models, Requirements/Ontology Using outcomes from The Jericho Challenge – representative from TSWG involved to validate definition & evaluate criteria for assessing submissions 62 Foster academic links and research Jericho is providing assisted membership for suitable academic researchers To date three links have been approved by the Jericho Forum Management Board – University of Kent Computing Laboratory – Royal Holloway College (in progress) – University of Auckland (in progress) 63 Promote independent discussion & research Research into de-perimeterisation is not Jericho Forum exclusive territory; Other publications; – PITAC – Butler Group 64 Cyber Security: A Crisis of Prioritization Cyber Security: A Crisis of Prioritization (February 2005) http://www.itrd.gov/pitac/reports/20050301_cybersecurity/cybersecurity.pdf A broad consensus among computer scientists is emerging that the approach of patching and retrofitting networks, computing systems, and software to “add” security and reliability may be necessary in the short run but is inadequate for addressing the Nation’s cyber security needs. 65 Cyber Security: A Crisis of Prioritization Fundamentally New Security Models, Methods Needed – – – The vast majority of cyber security research conducted to date has been based on the concept of perimeter defence. This weakness of the perimeter defence strategy has become painfully clear. But it is not the only problem with the model. The distinction between “outside” and “inside” breaks down amid the proliferation of wireless and embedded technologies connected to networks and the increasing complexity of networked “systems of systems.” Security add-ons will always be necessary to fix some security problems, but ultimately there is no substitute for system-wide end-to-end security that is minimally intrusive. 66 April 2005 Butler Group Review “Deperimeterisation has become more than an interesting idea it is now a requirement for many organisations” “Vendors have shown an increasing willingness to listen to the user community, but in the absence of a coherent voice from the end-users themselves, may have been uncertain about to whom they should be listening.” “As long as Jericho can continue to build upon its foundations and successfully integrate vendor input into its ongoing strategies, then we see no reason why this community should not become a strong and valuable voice in the years ahead.” www.butlergroup.com/research 67 The Jericho Challenge In collaboration with Black Hat, this global competition challenges any team of technology experts to design a secure architectural solution that is open, interoperable, viable, and operates in a de-perimeterised environment alike to a top global corporation's existence on the Internet. Deadline for notifying intent to submit entries is May 1st, with full submissions by May30th by arrangement. Selected papers may be presented in July 2005. More information on the 'challenge', how to enter, prizes, etc. is available in the Jericho Forum website (www.jerichoforum.org). 68 The Jericho Forum USA conference Thurs-Fri, May 5-6, 2005 Hosted by Procter & Gamble Executive Conference Centre, Cincinnati, Ohio, USA Thurs May 5th: 10.30 Welcome 10.45 The challenge YOU are facing - the problem in business terms 11.15 What is Jericho? 11.30 What has Jericho achieved 12.00 Going forwards – roadmap & deliverables 12.25 How to join 14.00 Mutually beneficial vendor involvement 14.30 Jericho future 15.30 Panel discussion 69 Fri May 6th: 09.00 Review of Jericho Forum working groups – charters, activities 10.00 Breakout groups – parallel workshops 12.00 Plenary review – workshop feedback 12.30 Lunch 14.00 New breakout groups – parallel workshops 15.30 Summary – feedback & conclusions; next steps 16.00 Close Challenges Ahead How to keep up momentum? – Market wants to see tangible, usable deliverables Detailed work rooted in real-world experience – Balancing active participation with “the day job” Global working – Making effective use of phone & email But when it’s all done….. 70 Lunch Lunch 71 Mutually beneficial vendor involvement Paul Simmonds ICI Plc. & Jericho Forum Board 72 Agenda Why has the Jericho Forum opened up to vendors? Why become a vendor member? Rights of vendor members vs. user members How to engage – What Forum membership is not – How to get best value from membership 73 Vendor membership of a user forum? – What’s that about? Jericho Forum fundamental principle is to be user driven to get break-thorough in: – Solving problems that existing perimeter-based solutions were not addressing – Interoperability and integration of security across vendors – Giving vendors a user-community driven business case That principle has not changed and the Forum remains user owned and driven 74 Vendor membership of a user forum? – What’s that about? Users don’t build solutions – Engage with vendors to solve the problems we are defining We invite vendors to join with us; – Get to grips with the difficult problems – Propose open standards to base products on – Propose new solutions – Change existing thinking & join the debate Users will approve the standards. 75 Why become a vendor member? 1. Making customers successful A CISO gets a daily flood of solutions and most are rejected out of hand – why? – Too many solutions use ‘FUD’ – Claim to be the latest miracle cure – They may be bought in ignorance rather than reasoned analysis – Disappointment is likely - not exactly a repeatable business model! – HIPPA! SOX! Phishing! Falling Sky! Of those that solve real problems; – – – – Too many are not integrated Too proprietary, with limited architecture At some point they will be thrown away Perhaps along with the CISO buying them? 76 Why become a vendor member? 2. Position in the Marketplace There is uncertainty in the market - CNet, March 05: "Security, ultimately, will not be a standalone market," said one investment banker ….. "It will just be just another layer of the infrastructure stack. It's no longer about just making the security products work together." Software, services and hardware companies in the security sector will pull in $52.2 billion in sales in 2008, compared with $22.8 billion in 2003, predicts market research firm IDC. That makes those businesses attractive targets for acquirers in the networking, communications and systems management industries, among others. Major CISO: “There are a few very successful security vendors, the remainder find a small niche and/or sell a few small pilots where expectations are far in excess of reality.” 77 What’s in it for me Access to the thinking of leading security users in one place No need to organise numerous strategy workshops with users Access to Jericho thinking, ahead of it being published Opportunities to grasp new markets ahead of the competition Meet and understand where integration with other Jericho vendor members will enhance both offerings 78 What’s in it for me Better opportunity for a larger take-up of customers at faster rate: – ‘viral’ effects of interoperability, users require it of one another – faster sales-cycle as customers will already understand the concepts & benefits of a particular security capability. Do open standards give-away competitive advantage? – No – Jericho Forum requires open standards in interoperability. ‘Inside the box’ capability and specific functionality can still be competitive issues. 79 Rights of vendor members vs. user members User members own the Forum, work in the working groups, vote on the deliverables and run the Board of Managers Vendors may; – Join in the work groups and contribute to design items and open standards – Have full access to Jericho materials – Elect their own representative onto the vendor council that represents vendor interests to the Board of Managers Vendors have no voting rights on deliverables or the direction and management of the Forum. 80 How to engage What Forum membership is not – A direct sales opportunity – Access to a mailing list – A chance to brand all products ‘Jericho approved’ Best value from membership – Get involved in the working groups – Have technical contributors like your CTO be the one who joins – Support open interoperability – Spread the word 81 Where could Jericho take us? David Lacey Royal Mail Plc. & Jericho Forum Board 82 Thinking beyond Einstein … “I never think about the future. It comes soon enough” Einstein 83 Preparing for a different future … We know only one thing about the future or, rather, the futures: “It will not look like the present” Jorge Luis Borges Author 84 The importance of Security increases … Increasing Threats from viruses, hackers, fraud, espionage Increasing Expectations from customers, partners, auditors, regulators 85 Increasing Exposure greater dependence on IT, increasing connectivity As organisations continue to change … Strong “Organism” External relationships Trend “Machine” Weak ‘Soft’ Internal relationships 86 ‘Hard’ And existing solutions break down … ASP JV JV Service provider Intranet Extranet Partner Outsource ASP JV JV Intranet Service provider Extranet Partner Outsource ASP JV JV Service provider Intranet Extranet Partner Outsource 87 As we experience the first security paradigm shift of the 21st Century … 88 Technology will transform our world … Exploding connectivity and complexity (embedded Internet, IP convergence) Machine-understandable information (Semantic Web) De-fragmentation of computers into networks of smaller devices Wireless, wearable computing Ubiquitous digital rights management Biometrics and novel user interfaces From deterministic to probabilistic systems 89 There are consequences for security … Slow death of network perimeters Continuing blurring of business and personal lifestyles Security migrates to the data level New languages and tools needed to express, translate and negotiate security policies Intelligent monitoring systems needed to maintain control of complex, networked systems Uncertain security - no guarantees Manage incidents as opportunities 90 How will we respond? The loss of perimeter security will force us to shrink perimeters to clients, applications and ultimately data IP Convergence will accelerate this process by challenging existing network security architectures We will realise that securing our own backyard is no longer sufficient, and work together to develop federated solutions to secure data across boundaries The Jericho Trust models will underpin this migration 91 Further developments … We will agree common policy languages to support cross-organisational processes, including federated identity and access management This work will underpin the automation of security countermeasures and enable the exploitation of the Semantic Web We will use the Semantic Web to interpret and secure data in context across organisations Jericho Technology and Standards will deliver the underpinning architecture Jericho Requirements and Ontology models will enable its exploitation 92 We will increasingly design our own future … “The best way to predict the future is to invent it” Alan Kay 93 Using the power of our imagination … “Imagination is more important than knowledge.” Einstein 94 As we look ahead to the second paradigm shift of the 21st Century … 95 A world of increasing openness and complexity … Exploding surveillance opportunities Limited opportunities for privacy-enhancing technologies Proliferating data wakes and pervasive circumstantial data about personal behaviour Intelligent monitoring software can highlight unusual behaviour Data fusion, mining and visualisation software can extract intelligence out of noise Exploitable for business, security, fraud or espionage 96 Visibility & understanding will be key Understanding and interpreting data in context Exploit data mining, fusing and neural networks to crunch through complexity Employ computational immunology to differentiate good transactions from bad Data visualisation technology to enhance human understanding 97 Break Coffee & Tea Served 98 Panel Debate & Audience Questions Panel David Lacey John Meakin Paul Simmonds Shane Tully Andrew Yeomans Moderator: Ron Condon 99 Wrap-up Ron Condon Editor in Chief, SC Magazine 100 The Jericho Forum USA conference Thurs-Fri, May 5-6, 2005 Hosted by Procter & Gamble Executive Conference Centre, Cincinnati, Ohio, USA Thurs May 5th: 10.30 Welcome 10.45 The challenge YOU are facing - the problem in business terms 11.15 What is Jericho? 11.30 What has Jericho achieved 12.00 Going forwards – roadmap & deliverables 12.25 How to join 14.00 Mutually beneficial vendor involvement 14.30 Jericho future 15.30 Panel discussion 101 Fri May 6th: 09.00 Review of Jericho Forum working groups – charters, activities 10.00 Breakout groups – parallel workshops 12.00 Plenary review – workshop feedback 12.30 Lunch 14.00 New breakout groups – parallel workshops 15.30 Summary – feedback & conclusions; next steps 16.00 Close Jericho Forum Shaping security for tomorrow’s world www.jerichoforum.org 102