Forensic Accounting Update Exam II Copyrighted 2002 D. Larry
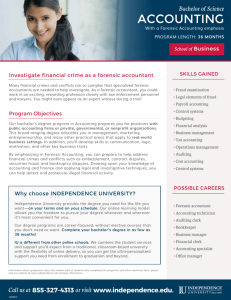
advertisement

© D.L. Crumbley Forensic Accounting: Some Strategies for Detecting & Preventing Fraud D. Larry Crumbley, CPA, CFF, Cr.FA, MAFF, FCPA KPMG Endowed Professor Department of Accounting 2833 Business Education Complex Louisiana State University Baton Rouge, LA 70803 225-578-6231 225-578-6201 Fax dcrumbl@lsu.edu Dr. Crumbley is the Editor of the Journal of Forensic and Investigative Accounting, free online, Former chair of the Executive Board of Accounting Advisors of the American Board of Forensic Accountants, Member of the NACVA’s Fraud Deterrence Board, and On the AICPA’s Fraud Task Force (2003-2004). A frequent contributor to the Forensic Examiner, Professor Crumbley is a co-author of CCH Master Auditing Guide, along with more than 50 other books and 350 articles. His book entitled Forensic and Investigative Accounting,5th edition, is published by Commerce Clearing House (800-2247477). Some of his 13 educational novels have as the main character a forensic accountant. His goal is to create a television series based upon the exciting life of a forensic accountant and litigation consultant. 1 © D.L. Crumbley Forensic Report 2 © D.L. Crumbley TALLY STICKS 3 © D.L. Crumbley Definition of Forensic Auditor Someone who can look behind the facade--not accept the records at their face value--someone who has a suspicious mind that the documents he or she is looking at may not be what they purport to be and someone who has the expertise to go out and conduct very detailed interviews of individuals to develop the truth, especially if some are presumed to be lying. Robert G. Roche, a retired chief of the IRS Criminal Investigation Division of the IRS 4 © D.L. Crumbley Narrow vs. Broad Definition • Narrow: Fraud Detection Is Major Area. • Broad: Employed to seek, interpret, and communicate transactional and reporting event evidence in an objective, legally sustainable fashion, not only in situations where there are specific allegations of wrongdoing, but also in situations where interested parties judge that the risk of loss from wrongdoing is such that proper prudence requires legally sustainable evidence to support the conclusion that no wrongdoing is occurring (James Edwards). 5 © D.L. Crumbley Narrow Approach Accounting Forensic Accounting Internal and External Auditing Planning Risk Assessment Internal controls Audit Evidence Reporting Accounting Litigation Matters and Investigations Fraud Prevention and Deterrence Detection Investigation Remediation U.S. Dept. of Justice, Education and Training in Fraud and Forensic Accounting: A Guide for Educational Institutions, Stakeholder Organizations, Faculty and Students, Draft Copy, December 23, 2005. 6 © D.L. Crumbley Broad Approach Bankruptcy Family law Auditing Valuation Fraud Antitrust matters Insurance claims Accounting Analyses Damages 7 © D.L. Crumbley Definition of Forensic Accounting Forensic accounting is the application of accounting, tax, auditing, finance, quantitative analysis, investigative and research skills, and an understanding of the legal process for the purpose of identifying, collecting, analyzing, and interpreting financial or other data or issues in connection with: 1) Litigation services: providing assistance for actual, pending or potential legal or regulatory proceedings before a trier of fact in connection with the resolution of disputes between parties, or 2) Non-litigation services: performing analyses or investigations that may require the same skills used in 1, above, but may 8 not involve the litigation process. Puff Adder © D.L. Crumbley 9 Short History © D.L. Crumbley 1. Late 1800’s – Find fraud 2. 1930’s- Puff Adder –encyclopedia 3. 1933-1934-independent audits 4. 1950’s-Eighth edition Montgomery auditing reduced formal stress on fraud detection. 5. January 1957- H.W. Bevis, AR, questioned the benefit of discovering minor employee thefts. 6. 1960s-auditors claimed no responsibility. 7. Financial audits: Consistency. 8. Audit surveillance: test of details (disappeared). 9. Stock market bubble 10.Panel on Audit Effectiveness (2000) 11.Enron/ WorldCom/ Parmalat/ HealthSouth 12.Sarbanes-Oxley/ PCAOB 13.SAS No. 99 10 © D.L. Crumbley Forensic Accounting Factors • Time: Forensic accounting focuses on the past, although it may do so in order to look forward (e.g., damages, valuations). • Purpose: Forensic accounting is performed for a specific legal forum or in anticipation of appearing before a legal forum. • Peremptory: Forensic accountants may be employed in a wide variety of risk management engagements within business enterprises as a matter of right, without the necessity of allegations (e.g., proactive). ----------------------------------------------With a single clue a forensic accountant can solve a fraudulent mystery. 11 One Small Clue © D.L. Crumbley A former Scotland Yard scientist tried to create the world’s biggest fraud by authenticating $2.5 trillion worth of fake U.S. Treasury bonds. When two men tried to pass off $25 million worth of the bonds in Toronto in 2001, a Mountie noticed the bonds bore the word “dollar” rather “dollars.” Police later raided a London bank vault and discovered that the bonds had been printed with an ink jet printer that had not been invented when the bonds were allegedly produced. Zip codes were used even though they were not introduced until 1963. Sue Clough, “Bungling Scientist Is Jailed for Plotting World's Biggest Fraud,” News.telegraph.co.uk, January 11, 2003. 12 © D.L. Crumbley Forensic Accounting Areas Investigative Auditing Litigation Support Forensic: Latin for “forum,” referring to a public place or court. Black’s Law Dictionary: Forensic, belonging to the courts of justice. Note: Corporate spooks are used to check on competitors. 13 © D.L. Crumbley Top Niche Services - 2013 1. State and Local Taxes 2. International Tax 3. Estate/Trust/Gift Tax Planning 80% 79% 78% 4. Business Valuations 5. Litigation Support 6. Attest Services 7. Forensic/Fraud 8. Industry specialization 9. Nonprofit Organizations 10. M & A 77% 74% 70% 65% 62% 59% 57% Source: Accounting Today 2013 14 © D.L. Crumbley Top Niche Services - 2013 Source: Accounting Today 2013 15 © D.L. Crumbley AICPA’s Position • Does not require auditors to carryout specific forensic procedures, but rather provide guidance on how to include forensic techniques within processes outlines in SAS 99. This combination will enhance the detection and prevention of fraudulent financial statement reporting and misappropriation of assets; thus protect investors and financial statement users. • Public accounting firms could use forensic accountants to help revise their approach to planning and fieldwork on all audits, while requiring forensic accountants only on high risk audit clients to aid in the interpretation of forensic testing results and preventive control enhancements. • The inclusion of audit procedures focused towards detecting misappropriation of corporate assets may lead to the identification of weaknesses within corporate governance or control weaknesses. Frauds that are identified which represent a material misappropriation of assets could significantly 16 impact public perception. © D.L. Crumbley AICPA’s Position (cont.) • Professional forensic accountants can best be used by ensuring such procedures are properly developed and executed in-line with internal audit and audit committee concerns. Forensic accountants could then be engaged in high-risk situations, or when a fraud is suspected. • Companies should not use the forensic services of their outside audit firm, unless it pertains to the annual audit. • Putting a price on a substantive test or forensic auditing procedure may be smart for business; however, the inherent risk is that short-cuts geared towards reducing audit costs may eventually cause investors to question the companies’ true financial position. AICPA – Discussion Memo Question Responses 17 © D.L. Crumbley Specialties Within Forensic and Investigative Accounting • Employee Crime Specialist. • Asset Tracing Specialist. • Litigation Services Specialist and Expert Witness. • Insurance Claims. • Valuation Analysis. • False Claims Act Violations. • Due diligence investigations. 18 © D.L. Crumbley Corruption on Steroids: Bell, California • Eight current and former employees, including mayor and ex-city manager • Ex-city manager, Rizzo, had a salary of $800,000. • Approximately 38,000 citizens. Average per capita income of $24,800. • Rizzo’s annual pension and benefit would have been $976,771, topping $1 million two years later. 19 © D.L. Crumbley Rita Crundwell - $53 Million Fraud • Former controller, city of Dixon, Illinois, since 1983. • SEC says she fraudulently stole $53 million. • Population of 15,733. Annual budget: $8$9 million. • Used monies to finance 311 quarter horses and lavish life style. • Bank account City of Dixon and RSCDA. • From 1990 to 2012, transferred funds from city bank accounts. • Created fictitious invoices purportedly from state of Illinois. John Metcalfe, Rita Crundwell v. Harriette Walters: Who Embezzled Better? The Atlantic Cities 20 Some Forensic Audits © D.L. Crumbley • Forensic audit of Geneseo, Illinois. • Florida GOP chairman’s promised forensic audit. • Forensic Audit needed at the National Library service • Summerville Town council will not go ahead with forensic audit. • Forensic audit of state spending would save money. • Forensic audit is growing in the Federal government. • Walling ford Housing Authority Board of Commissioners choose a forensic firm. • Mayor-elect Rahm Emanuel to order day-one forensic audit of all department. • Forensic Investigation Report, Cheyenne, and Arapaho Tribes. • School District audit to dig deeper. 21 Unclaimed Tax Refunds © D.L. Crumbley Love for an ex-boyfriend caused a Colorado Department Revenue Supervisor to steal $11 million in unclaimed tax refunds from Colorado state. Michelle was in love with the married Hysear Randell. Michelle Cawthra testified that she deposited unclaimed tax refunds and other money into Hysear Randell’s bank account over two years. She forged documents and created fake businesses. Michelle used computer passwords of other workers so she would not be detected. Source: http://www.baltimoresun.com/news/sns-ap-usodd-tax-refund-scam,0,... 22 Number One: Harriette Walters © D.L. Crumbley • Supervisor of the Real Property Tax Adjustment Unit in Washington, D.C., Harriette Walters, used at least 92 payments to dummy corporations in a scam to obtain $31.7 million ($344,565 per refund). • Fraud was never noticed by city officials, internal, or external auditors. Auditors never examined why the city’s property tax refunds were steadily rising. • Sham companies’ bank accounts were controlled by Walters’ brother. • Many applications for refund were identical to prior ones. • In a FBI raid of her house, 100 pieces of jewelry, a mink coat, 90 designer purses, 68 pairs of shoes, designer luggage, Rolex watch, silver bar cart, and more were found. She had a $1.4 million in bills at Neiman Marcus on a $81,000 yearly government salary. 23 Refund Schemes © D.L. Crumbley • A television station’s former accounting director pleaded guilty to stealing more $1.8 million from her employees and spending it on jewelry, paintings, and fur coats. • She would overpay the station’s travel bills and divert the refunds to her own credit card bills and personal accounts. • She was sentenced to 7 ½ years in prison on a single count of theft from CBS affiliate WBBM – TV Source: AP, “Ex-Accountant at CBS Affiliate Sentenced,” Las Vegas Sun, November 5, 2003. 24 Governmental Fraud © D.L. Crumbley Where Is $9 Trillion? The U.S. Federal Reserve can not account for $9 trillion in off-balance sheet transactions. Also, no one at the Federal Reserve has any idea what are the losses on its $2 trillion portfolio. On May 12, 2009, Inspector General Elizabeth Coleman could not explain the $1 trillion plus expansion of the Federal Reserve’s balance sheet since September 2008. While testifying before Congress, Coleman said the IG does not have jurisdiction to audit the Federal Reserve.86 If a U.S. business lost $9 trillion or created $9 trillion on their balance sheet, they would suffer severe penalties. Source: Julie Crawshaw, “Federal Reserve Cannot Account for $9 Trillion,” Newsmax.com. May 12, 2009. http://moneynews.newsmax.com/financenews/feds_lost_ni ne_trillion/2009/05/12/213463.html 25 © D.L. Crumbley Finding Unreported Income/Hidden Assets 1. 2. 3. 4. Look at the lifestyles. Look at the expenses. Look at the cash flow. Look at the business operations. 5. Look at the industry ratios. 6. Consider using private investigators. 7. Use the net worth method. Mark Kohn, “Unreported Income and Hidden Assets,” Forensic Accounting in Matrimonial Divorce, Philadelphia: R.T. Edwards, 2005, pp.49-57. 26 © D.L. Crumbley Forensic Accountants “Rather than combing torn clothing,” forensic accountants “comb through corporate books, looking for oddities that could signal swindles,” says Bruce Dubinsky. Investigations can be extremely complex, with crates and crates of documents and thousands of computer files. Investigators look for flags or patterns that would not normally occur. Source: Mark Maremont, “Tyco Is Likely to Report New Woes,” Wall Street Journal, April 30, 2003, p. C-1. 27 © D.L. Crumbley Find It, or I’ll Sue Accountants must be attuned to detecting fraud at every level of service, including standard accounting services, compilations, reviews, and bank reconciliations. If there is fraud and you don’t detect it, you are going to be sued, and you will likely lose, as the public perception is the accountant is the watchdog. Robert J. DiPasquale, Parsippany, N.J. Source: H.W. Wolosky, “Forensic Accounting to the Forefront,” Practical Accountant, February 2004, pp. 23-28. 28 © D.L. Crumbley Forensic Accounting Knowledge Base LAW Criminology Investigative auditing Accounting Forensic Accountant Silk, Silk, Silk 29 © D.L. Crumbley Fraud Strategies Differ 1. 2. 3. 4. 5. Forensic Accountants Internal Auditors External Auditors Fraud Examiners Certified Fraud Deterrence Analysts (CFD) or CFFAs 6. Forensic CPA Society (FCPA) 7. Governmental Accountants 30 © D.L. Crumbley Predication • • • The ACFE group indicates that in the private sector fraud investigation should not be conducted without proper predication. Examples: Anonymous tips, complaints, audit inquires, conflict of interest. Thus, predication is the basis for undertaking a fraud investigation. 31 © D.L. Crumbley Forensic-Type Organizations • • • • • • • • • American College of Forensic Examiners (2750 E. Sunshine, Springfield, MO 65804; 800-423-9737; www.acfei.com. DABFA and Cr.FA; 2000) Certified Fraud Examiners (Association of CFEs, The Gregor Bldg., 716 West Avenue Austin, TX 78701; 800-245-3321; www.cfenet.com). Certified Insolvency and Reorganization Accountant (CIRAs). Accountants, lawyers, consultants included in insolvency and bankruptcy matters. 3-part exam. 4,000 hours. 541.858.1665. AIRA, 221Stewart Avenue, Suite 207, Medford, Or. 97501. aira@airacira.org Forensic CPA Society (FCPA); formed in July 2005, Spokane, WA. info@fcpa.org. Master Analyst in Financial Forensics (MAFF) (NACVA, Salt Lake City, Utah 84106; 801-486-0600). National Litigation Support Services Association (NLSSA, III East Wacker Drive, Suite 990, Chicago, IL 60601; 800-869-0491). Not-for-profit. About 20 firms. $1,825. Canadian Institute of Chartered Accountants (CICA) – CA.IFA – Alliance for Excellence in Investigative Accounting. Certified Forensic Investigator (CFI) – Canada Early 1980’s. www.homewoodave.com Certified Fraud Specialist (CFS), not-for-profit, educational antifraud corporation located in Sacramento, Calif., for those dealing in white-collar crime, fraud, and abuse issues. Association of Certified Fraud Specialists. http://acfsnet.org. 32 © D.L. Crumbley The Trillion Dollar Gorilla (in Billions) U.S. Business1 $256.32 Federal Government2 239.75 State Government3 354.21 Tax-exempts4 134.5 Local Government5 Annual Fraud (trillion) 68.4 $ 1.053 1. 2002 Statistics of Income, $1,281.6 trillion time 20%. 2. $2.3975 trillion budget times 10% 3. $3,542.1 million times 10% 4. $897 billion in revenue times 15%. 5. $684.6 billion times 10%. 33 © D.L. Crumbley Fraud Multiplier Employee Fraud = $ for $ reduction in net income Suppose $100,000 bottom line reduction. Suppose 20% profit margin How much new revenue needed to offset the lost income? $100,000 = $500,000 20% So ACFE says $652 billion lost per year (2006). $652 billion = $3.26 trillion needed revenue 20%. ----------------------------------------------------This amount lost to fraud and abuses is twice the size of the U.S. military budget. 34 © D.L. Crumbley Advantage of Compliance Spending General Counsel Roundtable says that each $1 of compliance spending saves organizations, on the average, $5.21 in heightened avoidance of legal liabilities, harm to the organization’s reputation, and lost productivity. Source: Jonny Frank, “Fraud Risk Assessments,” Internal Auditor, April 2004, p. 47. 35 Schemes Committed by Perpetrators in the Accounting Department – 367 Cases Source: 2012 Wells Report, ACFE. 36 Frequency of Anti-Fraud Controls* * ”External Audit of F/S” = independent external audits of the organization’s financial statements “Internal Audit / FE Department” = internal audit department or fraud examination department “External Audit of ICOFR” = independent audits of the organization’s internal controls over financial reporting “Management Certification of F/S” = management certification of the organization’s financial statements Source: 2012 Wells Report, ACFE. 37 Frequency of Occupational Fraud Schemes Source: 2010 Wells Report, ACFE. 38 Scienter Necessary © D.L. Crumbley • To prove any type of fraud, prosecutors must show that scienter was present. • That is, the fraudster must have known that his or her actions were intended to deceive. ------------------------------------------------The allure of numbers to most of us, is like the excitement of settling sand--a narcoleptic surety. Crafty criminals prey on this boredom. They pile on the numbers, spewing meaningless records in the false books. Cory Johnson 39 © D.L. Crumbley Certain Fraud is Increasing Source: KPMG Fraud Study 40 © D.L. Crumbley Occupational Fraud Per Industry Source: 2012 Wells Report, ACFE. 41 © D.L. Crumbley Comparison of Selected Fraud Surveys Type KPMG PwC ACFE Questionnaire Interview Questionnaire Time Period 2005-2006 2011 2012 Number of participants (population) 4,056 (6,797) 3,877 1,388 (34,275) Response 59.7% Unknown 4% Estimated fraud in U.S. Not given Not given $3.5 trillion (global) % of companies experiencing fraud 74% reporting misconduct 34% (Global) Unclear Highest fraud industry Public sector Communications Banking/ Financial Services Second highest fraud industry Global Manufacturers Insurance Govt. and Public Administration Top – Fraud detection – Tips Not given 18% 43.3%* Fraud detection – Internal audits Not given 14% 14.4% Fraud detection – by accident Not given 8% 7.0% Some recover of fraud Not given Unknown 51.3% [2012] Gender of perps - male Not given Not given 65.0% Likely age Not given Not given 41-45 Fraud by senior mgt. Not given 18% Not given Fraud by Accounting dept. Not given Not given 22.0% Fraud with undergraduate degree Not given Not given 36.9% Common control measure Suspicious Transaction Monitoring External audit Second common control measure Internal audits Code of Conduct *Management review, 14.6% 42 Missing Fraud © D.L. Crumbley Auditors will continue to miss fraud because much of their work is predicted on the assumption that separation of duties prevents fraud (i.e., one person hold the money and another person keeps track of it). The Equity Funding case shakes the foundations of auditing in that so much is based on the assumption that people don’t collude very long. These people work together as an efficient team for a very long time [9 years]. Lee Seidler ------------------------------------------“When the sun goes down, then the sneaks will play at night.” From Porter Wagoner “Sneaks Crawl at Night.” 43 © D.L. Crumbley How Fraud Is Detected 2012 2010 2008 46.2% 1. Tips 43.3% 40.2% 2. Management review 14.6% 15.4% 2. By accident 7.0% 8.3% 20% 3. Internal audit 14.4% 13.9% 19.4% 4. Internal controls NA NA 23.3% 5. External audits 3.3% 4.6% 9.1% 6. Notification by police 3.0% 1.8% 3.2% Source: 2012/ 2010/ 2008 Wells Reports, ACFE. 44 © D.L. Crumbley Kessler Survey (2001) • About 13% of employees are fundamentally dishonest. • Employees out-steal shoplifters. • About 21% of employees are honest. • But 66% are encouraged to steal if they see others doing it without repercussion. Source: “Studies Show 13% of employees are fundamentally dishonest,” KesslerNews, November 1, 2001, www.investigation.com/articles/library/2001articles. --------------------------------------------------------------------------------------- • 30% of people in U.S. are dishonest. • 30% situational dishonest. • 40% are honest all of the time. Source: R.C. Hollinger, Dishonesty in the Workplace, Park Rider, N.Y.: 45 London House Press, 1989, pp. 1-5. © D.L. Crumbley Financial Audit v. Forensic Audit The typical financial audit is a sampling activity that doesn’t look at every transaction and can therefore be exploited by someone who knows how to rig the books. Forensic accounting focuses on a specific aspect of the books and examines every digit. While the average accountant is trying to make everything add up, a forensic accountant is performing a detailed financial analysis to find out why everything doesn’t or shouldn’t add up. It’s a far more time-consuming enterprise and can be significantly more expensive than regular auditing work. Jake Poinier, “ Fraud Finder,” Future Magazine, Fall 2004, http://www.phoenix.edu/students/future/oldissues/Winter2004/fraud.htm 46 © D.L. Crumbley Two Major Types of Fraud Investigations • Reactive: Some reason to suspect fraud, or occurs after a significant loss. • Proactive: First, preventive approach as a result of normal operations (e.g., review of internal controls or identify areas of fraud exposure). There is no reason to suspect fraud. Second, to detect indicia of fraud. Source: H.R. Davia, “ Fraud Specific Auditing,” Journal of Forensic Accounting, Vol. 111, 2002, pp. 111-120 47 © D.L. Crumbley Proactive vs. Reactive Approaches Proactive approaches include Effective internal controls, Financial and operational audits, Intelligence gathering, Logging of exceptions, and Reviewing variances. Reactive detection techniques include Investigating complaints and allegations, Intuition, and Suspicion. Jack Bologna and Robert Lindquist, Fraud Auditing and Forensic Accounting, 2d Edition, New York: John Wiley, 1995, p. 137. 48 Proactive Is Best © D.L. Crumbley When the IRS began requiring banks to issue Form 1099s reporting interest, the reported interest income increased by $8 billion (even though for 3 years the IRS did not have computer matching capacity). When the IRS began to require taxpayers to list a social security number for dependents, the next year the number of reported dependents dropped by seven million. More than 11,000 of these taxpayers claimed seven or more dependents in 1986, but they claimed none in 1987. When the IRS began to require taxpayers to list a name, address, and social security number for babysitters, two years later 2.6 million babysitters disappeared. 49 © D.L. Crumbley Fraud Deterrence Better Than Fraud Investigation 1. Fraud deterrence less expensive. 2. Deterrence is more comprehensive. 3. Fraud deterrence produces greater savings. 4. Deterrence is faster. 5. Fraud deterrence promotes better customer relations. Daniel Finnegan, “Deterring Fraud,” Quality Planning Corporation, 1991. 50 Walkthroughs © D.L. Crumbley An auditor must perform a walkthrough of a company’s significant processes (each major class of transactions). Can not be achieved secondhand. According to PCAOB, in a walkthrough an auditor traces “company transactions and events – both those that are routine and recurring and those that are unusual – from origination, through the company’s accounting and information systems and financial report preparation processes, to their being reported in the company’s financial statements.” Auditors should perform their own walkthroughs which provides auditors with appropriate evidence to make an intelligent assessment of internal controls. 51 Source: PCAOB Briefing Paper, Proposed Auditing Standards, October 7, 2003. Wandering Around © D.L. Crumbley •Informal observations while in the business. •Especially valuable when assessing the internal controls. •Observe employees while entering and leaving work and while on lunch break. •Observe posted material, instructions, job postings. •Observe information security and confidentiality. •Observe the compliance with procedures. 52 © D.L. Crumbley Measures Helpful in Preventing Fraud 1. Strong Internal Controls (3.66) 2. Willingness of companies to prosecute (3.44) 3. Regular fraud audit (3.40) 4. Fraud training for auditors (3.33) 5. Anonymous fraud reporting mechanisms (3.27) 6. Background checks of new employees (3.25) 7. Established fraud policies (3.12) 8. Ethical training for employees (2.96) 9. Workplace surveillance (2.89) Source: 2004 Wells Report 53 Contrasting Auditing, Fraud Examination, & Forensic Accounting Source: G.S. Smith and D.L. Crumbley, “Defining a Forensic Audit,” Journal of Digital Forensics, Security, and Law, 2009, Vol. 4, No. 1, p. 69. Auditing is a macro process, and forensic accounting is a micro process. 54 Financial Audit v. Forensic Audit The typical financial audit is a sampling activity that doesn’t look at every transaction and can therefore be exploited by someone who knows how to rig the books. Forensic accounting focuses on a specific aspect of the books and examines every digit. While the average accountant is trying to make everything add up, a forensic accountant is performing a detailed financial analysis to find out why everything doesn’t or shouldn’t add up. It’s a far more time-consuming enterprise and can be significantly more expensive than regular auditing work. Jake Poinier, “ Fraud Finder,” Future Magazine, Fall 2004, http://www.phoenix.edu/students/future/oldissues/Winter2004/frau d.htm 55 © D.L. Crumbley Inexperienced Forensic Auditors • Find out who did it. Do not worry about all the endless details. • Be creative, think like the fraudster, and do not be predictable. Lower the auditing threshold without notice. • Take into consideration that fraud often involves conspiracy. • Internal control lapses often occur during vacations, sick outages, days off, and rest breaks, especially when temporary personnel replace normal employees. H. R. Davia, Fraud 101, New York: John Wiley & Sons, 2000, pp. 42-45. 56 © D.L. Crumbley Social Engineering Schemes • Dumpster diving – Sifting through companies’ dumpsters (Proctor & Gamble went through Unilever’s dumpster. 80 valuable documents). – Lock Dumpsters. – Use across-cut shredder. – Check dumpster outside client's building (e.g., restaurant). • Shoulder surfing (e.g., looking for passwords; then plant stuff on your computer). • Tailgating: following someone into a business behind someone with authorized access, then lost your identity badge. 57 Social Engineering Schemes (contd.) • Phishing – increasing. • Pretexting – assume the identity of an authority figure. Find a picture of an identity badge. • Phreaking – pretending to be in a position of authority to obtain information. © D.L. Crumbley Seven Investigative Techniques 1. Public document review and background investigation (nonfinancial documents). 2. Interviews of knowledgeable persons. 3. Confidential sources. 4. Laboratory analysis of physical and electronic evidence. 5. Physical and electronic surveillance. 6. Undercover operations. 7. Analysis of financial transactions. Source: R.A. Nossen, The Detection, Investigation and Prosecution of Financial Crimes, Thoth Books, 1993. 59 © D.L. Crumbley Forensic Accounting Tools/ Techniques • • • • • • • • • • • Chain of Custody. Questioned Documents (e.g. ink analysis). Continuous Controls. Timeline Analysis. Tracing Schedule. Link Analysis. Invigilation. Genogram. Proof of Cash. Entity Charts. Full - and False – Inclusion Tools. 60 © D.L. Crumbley Forensic Accounting Tools/ Techniques (cont.) • • • • • • • • • • • Aberrant pattern detection (e.g., Benford Analysis) Duplicate numbers test (Excel/Idea/Account payables) Rounded numbers test GAP analysis Lifestyle analysis Attributes sampling Document map[a separate pane that displays a list of headings in a document in order to quickly navigate through the document and keep track of your location on it Event analysis (e.g., attacks of hackers on a computer system) Stratification percentage comparison Net worth analysis, etc. Analytic techniques (e.g., horizontal, etc.) 61 © D.L. Crumbley GAP Analysis Use Gap Analysis to look for missing items that should be in numerical sequence: • Checks (even voided checks) • Credit memos • Invoices • Journal entries Voided checks may indicate misappropriation or written to a shell corporation. 62 © D.L. Crumbley Duplicate Numbers Test Duplicate numbers test identifies suspicious recurrences of specific numbers. • Invoice numbers • Check numbers • Dollar amounts 63 © D.L. Crumbley Round Numbers Red Flag Areas where rounded number should not be expected: Amounts on tax returns(T&E). Inventory counts. Regulatory filings. Accounts receivable balances. Journal entries. Any measure presumed to be exact. Shows Estimation, Approximation, or Fraud. XL Audit Commander, free, Excel add-on Http:// ezrstats.com 64 © D.L. Crumbley Chain of Custody • Just as in the movies or on a television show such as CSI, forensic accountants must safeguard evidence through a financial chain of evidence. • There must be a way to show that the evidence has not been tampered with or damaged. • If documents are seized, the forensic accountant should put his or her initials and date of the seizure on the back of each document. • Or put the document in a transparent envelope and write a description on the envelope. • Store the original and work only with a copy. 65 © D.L. Crumbley Enforcement Manual Enforcement Manual History and Custody of Documents U.S. Department of Labor Pension and Welfare Benefits Administration Date _______________________________ Case Number________________________ Case Name __________________________ 1. How were the documents obtained? ____ By consent (note any significant comments of the principal circumstances which occurred)? ____ By legal process (describe). 2. 3. or third party witness and any unusual What is the relationship between the documents and the person submitting them? Were manual transcripts or facsimile copies made of any part?. ______ Yes ______No If Yes, list documents copies. Manner of reproduction of the documents either in whole or in 4. Have all copies been compared with the original documents and identified? _____Yes _____No If No, why not? 5. Were the original documents described herein under your control or supervision at all times prior to their return to the principal, third party witness, or representative? _____Yes _____No If No, set forth circumstances of any transfer in control. 6. Did the principal, third party witness, or a representative request access to the documents during your custody? ___ Yes ___ No If Yes, who requested access and what action was taken? Signature ___________________ Title ________________________ 66 Continuous Monitoring © D.L. Crumbley • Correlation is well suited to environments where there are (a) a large number of audit units (departments, divisions, franchisees, or customers, etc.), (b) a series of timestamped revenues, expenses or loss amounts, and (c) the goal of developing a formal process to compare each audit unit against a valid benchmark. • Correlation and time-series analysis are techniques that could be used by forensic accountants in a monitoring role to find evidence of intentional or unintentional errors in situations where there are many audit units. • The techniques could be used to proactively search for errors without any preconceived belief as to their existence, magnitude, or pervasiveness, or where the forensic accountant seeks to provide additional evidence showing that such errors occurred after the errors were detected using some other detection method. • If intentional errors were discovered using other methods of discovery, then the techniques could be used by the forensic accountant to show that the revenue or expenditure or loss streams of an audit unit differed significantly from a valid benchmark. M. J. Nigrini, “Monitoring Techniques Available to the Forensic Accountant,” J. of Forensic Accounting, Vol. 7, 2006, pp. 321-344. 67 Continuous Monitoring • Management engages an independent outside supplier to install and manage software to continuously analyze every transaction within business applications to detect improper activities and anomalies that indicate errors, control overrides, and fraud [Oversight Systems]. • The software sorts incidents into errors, misuse, and fraud (a detective control). • Suspicious transactions can be identified and categorized for future follow-up. • Flag items such as manual income-increasing adjustments, adjustments made late in the year, large dollar amounts. • Large companies with revenues over $1 billion. • Over the course of a year monitoring each module (e.g., A/P, Sales, G/L) is designed to cost approximately the amount the company would pay for one fulltime internal auditor per module. • One company saved $2 million of external auditing fees for using C/M in the 404 area. D. R. Hermanson, B. Moran, C. S. Rossie, and D. T. Wolfe, “Continuous Monitoring of Transactions to Reduce Fraud, Misuse, and Errors,” J. of Forensic Accounting, Vol. 7, 2006, pp. 17-30. 68 © D.L. Crumbley Timeline Analysis • Timeline analysis (TA) may be used to show the timing of a dispute, and certain software tools can prepare trial exhibits. • Investigative analysis software can show all detail from the beginning of the event until the apprehension of the target. • TA helps forensic accountants communicate the timing of case related events and summarizes the investigation. • Each link of the timeline chart includes a reference to a source or a direct link to a database. An insurance fraud scheme timeline from i2 Inc is shown in the next Table: 69 © D.L. Crumbley Insurance Fraud Scheme 70 © D.L. Crumbley Tracing Schedule • A tracing schedule can be used to show the flow of funds from bank-to-bank, from bank-toentity, from entity-to-entity, or from person-to-person. • A tracing schedule is helpful in money laundering cases. 71 © D.L. Crumbley Link Analysis • Link analysis (LA) is a subset of network analysis which shows associations between people and data. • For example, a link analysis could compare the mailing addresses of company executives and the cell phone numbers that they have dialed during a given time frame. • LA provides crucial relationships between many objects of different types that are not apparent from isolated pieces of data. • Table 5.1 is an example of LA with respect to the primary suspect, David Hoover. Wikipedia, the free encyclopedia, en.wikipedia.org. Stuart Weiss, “Forensic Accounting Tools and Techniques,” The Value Examiner, January/ February, 2007, pp. 12-13. 72 © D.L. Crumbley Table 5.1 Link Analysis 73 © D.L. Crumbley Invigilation • Invigilation is a rather expensive investigating technique that can be used in potential fraud situations to discover the fraud and can later be used in the courtroom. • Here detailed records are kept before and after the invigilation period to determine the amount of fraud. • During the invigilation period strict controls are imposed (e.g., cameras) so that the fraud is virtually impossible. • Or the invigilation period could be while the suspect is on vacation. 74 © D.L. Crumbley Invigilation Technique No controls Controls or vacation No controls 14 days 14 days 14 days $67,000 lost $0 lost $62,000 lost 75 Genogram © D.L. Crumbley • A genogram is a pictorial display of personal relationships among related or unrelated parties. • There are software programs that are custom designed for genograms, such as GenoPro 2007 ($49 at www.genopro.com). • Simple symbols represent the gender (box for male and circle for female), with various lines to illustrate family relationships. • People who are not related would not be connected with a line, but could be placed on the genogram. • They can lead to determining the motive of a crime or provide evidence that the person had no direct involvement in the fraud. 76 © D.L. Crumbley Genogram 77 © D.L. Crumbley Tracking Small Sums • FAs can employ aberrant pattern detection using digital analysis. Benford’s Law is the DNA equivalent of numeric testing using geometric progressions against actual transactions. Another technique, full and false inclusion, is known as the yellow crime scene tape of forensic accounting. It insures that no extraneous data is included and no appropriate data is excluded. Another very interesting technique uses Genograms, which are visual representations of personal relationships. It is a tool that is been borrowed from family counseling. • First, FAs track people. Then the money is easy to find. The money takes different forms, of course: cash, accounts, hard assets such as real estate and automobiles, intangible assets like patents, copyrights, trademarks, promissory notes, betting records. Both money and people leave trails: phone records, voting records, even genealogy research. In fact, the trails left in a free society are very useful in catching terrorists who attempt to use our freedom to their advantage. • Source: Darrell Dorrell, Financial Forensics: The Body of Knowledge, John Wiley & Sons 78 © D.L. Crumbley Proof of Cash • The proof of cash procedure is similar to a bank reconciliation, except more detailed and extensive. • This procedure can be used to verify that cash accounts on the books are in agreement with the cash transactions recorded by the bank. • The Wyoming Department of Audit’s proof is shown as Table 5.2. 79 © D.L. Crumbley Table 5.2 80 Entity Charts © D.L. Crumbley • Entity charts show entities and owners with the relationship between them. • The charts can show how income and assets are diverted, particularly among seemingly unrelated parties and entities. • Microsoft Excel drawing tools may be used to prepare entity charts. • For example, an entity chart could show the creation date of off-shore bank accounts and the subsequent decrease in the target’s U.S. bank accounts. • Or identification of other unrelated parties may suggest additional investigation is needed. D. D. Dorrell and G. A. Gadawski, “Financial Forensics II,” May, 2005, Vol. 3, No. 3, p. 50. 81 Full – and – False Inclusion Tests • These tests are used to ascertain the proper universe of data under investigation, so that no appropriate data is excluded and no extraneous data is included. • Full-and-false inclusion tests may be helpful for finding hidden assets. • Yellow crime scene tape of FA, according to Darrell Dorrell. 82 Financial Models © D.L. Crumbley A financial model may be defined as “an abstract, simplified, mathematical construct related to a part of reality and created for a particular purpose.” AICPA Practice Aid 06-2 suggests a financial model could be used in these situations: • Reviewing or developing planning concepts in the client organization. • Selecting, gathering, compiling, validating, and assessing data required in the planning process. • Determining the relationships and interactions among the key factors in client operations and finances. • Reviewing financial, planning, and operating assumptions with the client. 83 Financial Models (cont.) • Constructing a formal model of key factors, relationships, and interactions. • Analyzing, testing, and presenting results produced by running the model using various combinations of assumptions, relationships, and activity levels. • Revising or updating the output as time passes using amended or incremental inputs. • Submitting the model to the client for future use and maintenance with appropriate documentation and training. Sources: Edward A. Bender, An Introduction to Mathematical Modeling (New York: John Wiley & Sons, 1978), p. 3. Preparing Financial Models, Practice Aid 06-2, New York: AICPA, 2006, pp.2-3. 84 © D.L. Crumbley Questioned Documents Invoices and other documents may be fake or altered when • Font sizes or types are not consistent • No address is shown for the vendor or customer; this situation is especially suspicious if a vendor has not identified an address to which a check can be sent. • The document has no identifying numbers such as invoice number, purchase order number, or customer number. • All invoice numbers – on invoices from vendors – are numbered sequentially, with no numbers skipped. • No tax is shown for taxable items. • No shipping or freight cost is shown for items that would have been shipped at the purchaser’s expense. • Little or no detail is provided on the invoice or document. T. W. Golden, S. L. Skalak, and M. M. Clayton, A Guide to Forensic Accounting Investigation, Hoboken, N.J.: John Wiley & Sons, 2006, pp. 156-157. 85 Forensic Linguist © D.L. Crumbley According to the suit, Heebe enlisted a former FBI profiler to review 595 comments left by "Henry L. Mencken" below stories posted on NOLA.com. The comments were compared to legal filings made by federal prosecutors in their sweeping probe of the River Birch landfill, which is co-owned by Heebe and his fatherin-law. The profiler found striking similarities in the language, the suit says. The petition notes that "Mencken" uses obscure words, such as "dubiety" and "redoubt," that also appear in federal filings in the River Birch case. The suit says the analysis was conducted by forensic linguist James Fitzgerald whose work for the FBI "proved instrumental" in the arrest and successful prosecution of Ted Kaczynski as the Unabomber, following a lengthy investigation that included analysis of the mail bomber's writings. Gordon Russell, “Landfill owner Fred Heebe claims NOLA.com commenter is federal prosecutor”, NOLA.com, March 13, 2012 86 © D.L. Crumbley Social Media in Divorce • Attorneys report an increase in using social media in divorce and family law cases (e.g. Twitter, MySpace, YouTube, LinkedIn). • Facebook, especially, has been a gold mine for evidence in divorce disputes. • Facebook's relaxed privacy policies make investigations easier, some attorneys say. • Private investigators report a surge in demand for Facebook searches. Stephanie Chen, “Divorce attorneys catching cheaters on Facebook”, CNN, June 1, 2010 87 © D.L. Crumbley E-ZPass Catching Cheaters • E-ZPass and similar electronic toll collection systems are emerging as a new and powerful means to prove infidelity. • Generally mounted inside a vehicle's windshield behind the rearview mirror, the remote-sized, EZPass devices communicate with antennas at toll plazas, automatically deducting money from the tagholder's prepaid account and recording when and where the vehicle crossed the toll. • Many states provide electronic toll information in response to court orders for criminal and civil cases, including divorces, which are used to prove the defendant was not where he or she claimed to have been. • "E-ZPass is an E-ZPass to go directly to divorce court, because it's an easy way to show you took the off-ramp to adultery," said Jacalyn Barnett, a New York divorce lawyer who has used E-ZPass records a few times. Chris Newmarker, “E-ZPass records out cheaters in divorce court.” AP, 2007. 88 Carbon Dating Paper and Signatures • There are reports of using radioactive carbon dating and microscopy to prove the age of a document and the age of the signature differ by a matter of years. Dating the other writing on the paper further corroborates the allegation of forgery. • Sources have reported that in Atlanta, the procedure has been used on the “original” note produced in court by the pretender lender, proving the document was a forgery even though the borrower conceded the signature was authentic. • If a document is dated 5 years ago, and the signature, endorsement or assignment execution that is dated on the paper is more recent, or the actual signature is more recent than the rest of the document (the paper, the other writing etc.) then the signature was not on the document at or near the time of the document’s creation. FORENSIC FILES: CARBON DATING THE PAPER AND THE SIGNATURE TO PROVE FORGERY Neil Garfield, January 25, 2011 89 Carbon Dating Paper and Signatures • If it’s the borrower’s signature that has been technologically reproduced and introduced as an original, it means that the actual original note is somewhere else. It also raises the possibility that more “originals” are circulating in those fictitious “Trusts” or “pools” purporting to claim the obligation, note or mortgage. • If the signature or the paper that is presented as an assignment dated at or near the time of closing with the borrower, but either the paper, the signature, the witness signature or the notary signature or stamp does not coincide with the date of the purported document, the same analysis holds: it is a forgery. FORENSIC FILES: CARBON DATING THE PAPER AND THE SIGNATURE TO PROVE FORGERY Neil Garfield, January 25, 2011 90 © D.L. Crumbley A ` Perforation match Paper shreds demonstrating different optical properties under ambient and specialized lighting Inks of different intensities used on the same document 91 Forensic Information System for Handwriting (FISH) U.S. Department of Justice The document-part image is acquired by scanning the entire document and selecting the desired part by using a 6.5 x 6.5 cm ruled square. Once the block of writing is selected, the document is rescanned, producing an enlargement of the part on the screen. By adjusting the contrast between the writing and the paper surface to conform to that of the original document, the examiner can present features, such as tapered beginning and ending strokes or light connecting strokes, as they appear on the original document. The examiner may also remove unwanted features from the document image. The feature extraction process can being according to the type of writing indicated on the document-part data entry screen, The first step is the text-insensitive feature extraction (TIM), an automatic process in which FISH marks the exact center of the part and draws eight vectors out to the edges. The system then uses black-and-white pixel chain formations and auto-correlation functions to mathematically treat and store the writing, the TIM is then saved and isolation for selected features begins. This involves circling the desired letter or combination. The next extraction deals with tracing or line-following. A set of measurements then marks the height of the base ovals. At least 10 measurements are taken. After the interactively measured features are recorded a screen appears that lists the number of measurements taken, the median measurement, and the standard deviation for each category. 92 The Hitler Diaries Debacle (1980s) It was an analysis of the ink and paper used to write the diaries that revealed them as fakes. An ultraviolent-light examination revealed that the paper contained an ingredient that wasn't used in paper until 1954. Hitler died in 1945. Further forensic tests on the ink showed it had been applied to the paper within the last 12 months. As it turns out, though, the handwriting analysis was in fact correct – the person who’d written the diaries had also written the exemplars. Konrad Kujau, later found out to be an experienced con artist, had also forged the exemplars the police were using as comparison documents. Published by Sunday Times when Rupert Murdoch was executive editor. 93 Julia Layton, How Handwriting Analysis Works Who Uses IDEA? © D.L. Crumbley • External and Internal Auditors • Forensic Accountants/ Fraud Investigators • Financial managers • General and systems consultants • Educators • Statisticians • Information systems professionals 94 IDEA Benefits • • • • • • Sort Compare Manipulate Sample Extract data Mathematical testing • Exception reports • Aging © D.L. Crumbley • Statistics • Find missing data • Analytics • Convert test files to data base • Create summary reports 95 © D.L. Crumbley Using Data Mining • Match employee addresses against vendor addresses. • Sort vendor list by size to determine the most highly paid suppliers. • Review the structure of vendor names. • Uncover indications of ghost employees (e.g., N.O. Police dept.). • Fraudulent expense reports (even amounts, $6). • Repeated withdrawals of even amounts from petty cash. 96 © D.L. Crumbley Benford’s Law • • Distribution of initial digits in natural numbers is not random Predictable patterns: 0= ----1= 30.1% 2= 17.6% 3= 12.5% 4= 9.7% 5= 7.9% 6= 6.7% 7= 5.8% 8= 5.1% 9= 4.6% 12% 11.4% 10.9% 10.4% 10% 9.7% 9.3% 9% 8.8% 8.5% 10.2% 10.1% 10.1% 10.1% 10% 10% 9.9% 9.9% 9.9% 9.8% There is software to detect potentially invented numbers in many situations. Compare actual frequency with Benford’s frequency. 97 Benford’s Law Uses • • • • • • • • • • © D.L. Crumbley Investments sales/purchases Check register. Sales history/Price history. 401 contributions. Inventory unit costs. Expenses accounts. Wire transfer information. Life insurance policy values. Bad debt expenses. Asset/liability accounts. Source: Richard Lanza, “Digital Analysis- Real World Example,” IT Audit, July 1, 1999,pp. 1-9. 98 When Benford Analysis Is or Is Not Likely Useful When Benford Analysis is Likely Useful Examples Sets of numbers that result from mathematical combination of numbersResult comes from two distributions. Accounts receivable (number sold times price). Accounts payable (number bought times price). Transaction-level data – No need to sample. Disbursements, sales, expenses. On large data sets – The more observations, the better. Full year’s transactions. Accounts that appear to conform – When the mean of a set of numbers is greater than the median and the skewness is positive. Most sets of accounting numbers. When Benford Analysis Is Not Likely Useful Examples Data set is comprised of assigned numbers Check numbers, invoice numbers, zip codes. Numbers that are influenced by human thought. Prices set at psychological thresholds ($1.99), ATM withdrawals. Accounts with a large number of firmspecific numbers. An account specifically set up to record $100 refunds. Accounts with a built in minimum or maximum. Set of assets that must meet a threshold to be recorded. Where no transaction is recorded. Thefts, kickbacks, contract rigging. Source: Durtschi, Hillison, and Pacini, “The Effective Use of Benford’s Law to Assist in Detecting Fraud in Accounting Data,” J. of Forensic Accounting, Vol. V, 2004, p. 24. 99 IDEA Exercise 100 © D.L. Crumbley Use IRS Form 1099 Threat • For fraudsters and embezzlers, use the threat of filling a Form 1099 for amounts stolen. • Ask for an installment payback. • If they stop payment, report them to the IRS on a Form 1099. 101 © D.L. Crumbley Look For Fraud Symptoms • Source Documents. • Journal Entries. • Accounting Ledgers. 102 © D.L. Crumbley Source Documents • • • • • • • • Cancelled Checks. Employee time cards. Sales invoices. Shipping documents. Expense invoices. Purchase documents. Credit card receipts. Register tapes. • • • • • Revenue Agent Reports. Loan documents. Forms 1099s/990s. Insurance documents. Brokerage account statements. 103 © D.L. Crumbley Source Documents Fraud Symptoms • Photocopies of missing documents. • Counterfeit/false documents. • Excessive voids/credits. • Second endorsements. • Duplicate payments/same payee. • Large numbers of reconciling items. • Older items on bank reconciliations. • Ghost employees. • Lost register tapes. • Lots of round numbers. • Too many beginning 9’s. • Overpayment of wages. • Bogus claims. • White outs and erasers. 104 © D.L. Crumbley Journal Entries Fraud Symptoms • Out-of-balance. • Lacking supporting documents. • Unexplained adjustments. • Unusual/numerous entries at end of period. • Written entries in computer environment. • Many round numbers. • Too many beginning 9’s. • Weekend entries. • Entries by unauthorized people. 105 © D.L. Crumbley Consideration of Fraud-AU Section 316 The characteristics of fraudulent entries or adjustments. Inappropriate journal entries and other adjustments often have certain unique identifying characteristics, including entries. PCAOB: A. Made to unrelated, unusual, or seldomused accounts; B. Made by people who typically do not make journal entries; C. Recorded at the end of the period or as post-closing entries that have little or no explanation or description; D. Made either before or during the preparation of the financial statements that do not have account numbers; or E. Containing round numbers or consistent ending numbers. 106 A Valid Contract? • • • • • • © D.L. Crumbley Offer/ Acceptance Lawful objective Capacity of parties to perform Something of value exchanged Appropriate form (e.g., in writing) Entered into freely 107 Breach of Contract © D.L. Crumbley • Breach of contract: a party fails to perform or says he/ she will not perform. Other party can sue for damages. • The intentional failure to perform a contract, however, does not necessarily constitute fraud. • Must show that the party did not intend to perform the contract and deliberately misled the other party. • Civil or criminal action: party knowingly and willfully that the contract (or statement) was false with the intent to deceive or defraud. • With this extra burden, may not be worthwhile to try to prove the fraud. Just get rid of the person because of a conflict of interest. 108 © D.L. Crumbley Some Contract/ Procurement Frauds 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. Bribes and Kickbacks. Bid Rigging. Defective Pricing. Phantom Vendors [www.picalo.org]. Product substitution. Conflict of Interests. False Claims. Cost Mischarging. Contract Specification Failures. Duplicate, false, or inflated invoices. Split purchases. Unnecessary purchases. Defective delivery. H.R. Davia et. al, Accountant’s Guide to Fraud Detection and Control, John Wiley, 2000, p.62. 109 Types of Bid Rigging 1. 2. 3. 4. 5. 6. © D.L. Crumbley Collective bidding. Exclusive bidders. Change order requests. Manipulation of bids. Leaking bid information. Unbalanced bidding. 110 Bribes/ Kickbacks Scenario © D.L. Crumbley Something of Value Later Influence an Official Act Cash Gifts Trips Entertainment Drugs Sexual favors Loans Credit cards Fees Spouse’s high salary Discounts (e.g., house) Awarding Selection Higher Prices Excessive Quantity Accepting Lower Quality No, Delayed, or Short Delivery Prove the corrupting influence circumstantially through factors on the right, or outsider received more and more business at the insider gets more and more value. 111 Some Bribery Red Flags • • • • • • • • • © D.L. Crumbley Lack of standard invoices. Requests for fund to be routed to a foreign bank. Requests for checks made payable to “cash” or to “the bearer.” Commission substantially higher than going rate. Requests for a large line of credit from a customer. Insistence by a government official that a certain third-party agent or supplier be used. Lack of staff or facilities to actually perform the service. Request by a local agent for a rate increase in the middle of negotiations. Suggested need to utilize more than on local agent. Source: M. T. Biegelman and J. T. Bartow, Executive Roadmap to Fraud Prevention and Internal Controls, John Wiley, 2006, pp. 325-326. 112 Duty to Cooperate © D.L. Crumbley 113 Audit Rights © D.L. Crumbley 1. Audits under clause 2 may be conducted of: a) b) c) d) e) f) the Contractor's practices and procedures as they relate to the Contract, including security procedures; the manner in which the Contractor performs its obligations under the Contract; the compliance of the Contractor's invoices and reports with its obligations under the Contract; the Contractor's compliance with all its obligations under the Contract; the Contractor's compliance with its confidentiality, privacy, security and Commonwealth policy obligations under the Contract; and any other matters determined by [Agency] to be relevant to the performance of the Contractor's obligations under the Contract. 2. Audits i. ii. iii. iv. v. vi. vii. viii. The Contractor must participate in audits of the Contract at the frequency and in relation to the matters specified by [Agency], (including on an ad hoc basis if requested by [Agency]), for the purpose of ensuring that the Contract is being properly performed and administered. [Agency] may appoint an independent person to assist in the audits. Audits may consider all aspects of the Contractor's performance including but not limited to any performance indicators, benchmarks or targets. The Contractor must participate promptly and cooperatively in any audits conducted by [Agency] or its nominee. Except for those circumstances in which notice is not practicable or appropriate (eg. caused by a regulatory request with shorter notice or investigation of theft or breach of contract), and without limiting any other right, recourse or remedy of [Agency], must give the Contractor reasonable notice of an audit and where reasonably practicable an indication of which documents and/or class of documents the auditor may require. Subject to any express provisions in the Contract to the contrary each party must bear its own costs of any audits. Subject to clauses 2.6 and 3.6, the requirement for, and participation in, audits does not in any way reduce the Contractor's responsibility to perform its obligations in accordance with the Contract. [Agency] must use reasonable endeavours to ensure that audits performed pursuant to clause 2.1 do not unreasonably delay or disrupt in any material respect the Contractor's performance of its obligations under the Contract. [Any amendments to the Contract resulting from audits must be effected by agreement in writing between the parties in accordance with the Contract amendment provisions of the Contract.] The Contractor must promptly take, at no additional cost to [Agency], corrective action to rectify any error, non-compliance or inaccuracy identified in any audit in the way the Contractor has under the Contract: (a) supplied any goods or services; or (b) calculated fees, or any other amounts or charges billed to [Agency]. 114 © D.L. Crumbley Purchasing Agent’s Kickback Checklist • • • • • • • • • • • • He or she doesn’t take time off. The purchasing agent has personal financial problems. The agent’s lifestyle is too extravagant for his or her income. Close personal relationship between purchasing agent and vendor. Favoritism toward one vendor. Excessive purchases from one vendor. Prices charged are higher than market average. Expenditures come in just under the review limit. Multiple purchases over a short period. Substandard products or services. Accelerated payment of invoices. Sole-source purchases of merchandise or services. Be sure different personnel handle the following duties: vendor approval, purchase requisitions, purchase approval, receiving, and payment (e.g., separation of duties). Source: J. T. Wells, “The Case of Pilfering Purchasing Manager,” Journal of Accountancy, May, 2004. 115 © D.L. Crumbley Red Flags for Phantom Vendors • • • • • • • • Invoices for unspecified consulting or other poorly defined services. Unfamiliar vendors. Vendors that have only a post-office-box address. Vendors with company names consisting only of initials. Many such companies are legitimate, but crooks commonly use this naming convention. Rapidly increasing purchases from one vendor. Vendor billings more than once a month. Vendor addresses that match employee addresses. Large billings broken into multiple smaller invoices, each of which is for an amount that will not attract attention. Source: J. T. Wells, “Billing Schemes Part I: Shell Companies That Don’t Deliver,” Journal of Accountancy, July, 2002. 116 © D.L. Crumbley More Phony Vendors Red Flags • • • • • • • • Ensure those involved in purchasing cannot approve vendors. Before approving a new vendor, evaluate its legitimacy by Obtaining its corporate records and other relevant documents. Checking its credit rating. Confirming that it is listed in telephone directories. Contacting its references from clients and others. Being particularly cautious about a vendor with a postoffice-box address or a name composed entirely of initials. Determining whether its business address matches any employee’s home address. Once the company approves a new vendor, the CPA should closely monitor the account by • • • Watching for increases in the amount or frequency of billings. Observing variances from budgets or projections. Comparing its prices with those charged by other sources. Source: J. T. Wells, “Billing Schemes Part I: Shell Companies That Don’t Deliver,” Journal of Accountancy, July, 2002. 117 Assess Financial Health © D.L. Crumbley Ratio Purpose Negative Indicator Financial Position: Unrestricted Net Assets Expenses Measures a government’s ability to provide basic government services Decreasing Financial Performance: Change in Net Assets Total Net Assets Measures a government’s financial performance during the current fiscal year by comparing the change in the Net Assets derived from the Statement of Activities to the total net assets. Decreasing (General Revenues + Transfers) / Expenses Measures the extent to which the cost of services are paid for out of general revenues. Decreasing Liquidity: (Cash + Current Investments + Receivables) / Current Liabilities Measures the extent to which current liabilities are covered by the more liquid current assets. Decreasing Solvency: Long-term Debt / Assets Measures a government’s longterm financial viability by comparing the extent to which assets are financed by incurring long-term debt. Increasing (Change in Net Assets + Interest Expense) / Interest Expense Measures the government’s ability to generate a stream of inflows sufficient to make interest payments. Decreasing Source: B.A. Chaney, D.M. Mead, and K.R. Schermann, “The New Governmental 118 Reporting Model,” Journal of Governmental Management, Spring 2002, p. 29. Early Warning Signals of Possible Trouble for Municipal Entities 1. Current year operating deficit 2. Two consecutive years of Operating Fund deficit 3. Current year operating deficit that is larger than the previous year’s deficit 4. A General Fund deficit in the current year – balance sheet – current position 5. A current General Fund deficit (two or more years in the last five) 6. Short-term debt outstanding at the end of the fiscal year, greater than five percent of main Operating Fund Revenues 7. A two-year trend of increasing short-term debt outstanding at fiscal year end 8. Short-term interest and current year-end service greater than 20 percent of total revenues 9. Property taxes greater than 90 percent of the tax limit 10.Debt outstanding greater than 90 percent of the debt limit 11.Total property tax collections less than 92 percent of total levy 12.A trend of decreasing tax collections – two consecutive years in a three-year trend 13.Declining market valuations – two consecutive years – threeyear trend 14.Expanding annual unfunded pension obligations Source: H.C. Grossman and T.E. Wilson, “Assessing Financial Health,” Handbook of Governmental Accounting & Finance, Somerset, N.J.: John Wiley & Sons, 1992, pp. 38-1 to 38-13. 119 Assess Financial Health of Governmental Units © D.L. Crumbley Ratios Negative Indicator Credit Industry Benchmark Cash and investments/current liabilities Decreasing Less than 1% Operating surplus (deficit)/total revenue Decreasing 5% or consecutive Elastic revenue (sales, utilities, other elastic taxes)/total revenue Decreasing Varies State and federal aid / total revenue Increasing Varies Current liabilities/total revenue Increasing 5% Uncollected property taxes/ current tax levy Increasing Greater than 8% Fixed costs/ total expenditures Increasing Varies Debt service/total revenue Increasing Greater than 20% Tax levy/tax limit Increasing Greater than 90% Debt outstanding/debt limit Increasing Greater than 90% Source: S.M. Winckler and Dewey Ward, “Can City Hall Go Broke? The Going Concern 120 Issue,” Journal of Accountancy, May 1984. © D.L. Office of New York State Comptroller Crumbley Indicator 1: Revenue and Expenditures Per Capita Recurring Revenues Per Capita a. Gross Revenues Population b. Gross Expenditures Population c. Recurring Revenues (Gross Revenues – One-Time Revenues) Population Negative Trend: Indicator 1b increasing faster than indicator 1a or 1c. Indicator 2: Real Property Taxes Receivable Real Property Taxes Receivable Real Property Tax Revenue Negative Trend: The percentage increases over time. Indicator 3: Fixed Costs – Personal Services and Debt Service a. Salaries and Fringe Benefits Gross Expenditures b. Debt Service Expenditures Gross Expenditures c. Salaries and Fringe Benefits + Debt Service Gross Expenditures Negative Trend: Percentages increasing over time. Some analysts use a variation of the 3b ratio based upon debt service expenditures as a percentage of revenues. A ratio of 25% for debt service expenditures to “own source” revenues is considered a danger signal.* 121 * J.R. Razek et. al, Introduction to Governmental and Not-For-Profit Accounting, Prentice-Hall, 2000, p. 412. © D.L. Office of New York State Comptroller Crumbley Indicator 4: Operating Surplus/Deficit a. Gross Revenues – Gross Expenditures Gross Expenditures b. Gross Revenues – Gross Expenditures – One-Time Revenues Gross Expenditures Negative Trend: Percentages decreasing over time. Indicator 5: Unreserved Fund Balance and Appropriated Fund Balance a. Unreserved Fund Balance Gross Expenditures b. Appropriated Fund Balance Gross Expenditures Negative Trend: Percentages decreasing over time. Deficits in major funds in excess of 1.5% of fund expenditures or $50,000 (whichever is greater) are generally causes for concern. Some analysts use a variation of this ratio: the budgetary cushion. Here the fund balance is compared to revenues. The greater the fund balance as a percentage of revenues, the more likely a local government may weather hard times. A good rule of thumb is that a fund balance should be at least 5% of revenues.[1] [1] J.R. Razek et. al, op. cit., p. 411. 122 Office of New York State Comptroller Indicator 6: Liquidity Cash and Investment as a Percentage of Current Liabilities Cash and Investments as a Percentage of Gross Monthly Expenditures a. Cash and Investments Current Liabilities b. Cash and Investments Gross Expenditures/12 Negative Trend: Percentages decreasing over time. A government should generally have year-end cash equal to about 50% of current liabilities and 75% of average monthly expenditures. A governmental accounting textbook states that this quick ratio (or acid test) omits receivables and amounts due from other funds because of difficulties converting them into cash. They suggest that a large state government should consider a quick ratio of less than 50 percent as an indicator of financial stress.* Indicator 7: Long-Term Debt Long-Term Debt Population Negative Trend: Percentage increase over time Note: An increase in #7 would likely trigger a future increase in #3 formula as well as a decrease in #8. Indicator 8: Capital Outlay Capital Outlay Gross Expenditures Negative Trend: Percentage decreasing over time Note: This eighth indicator is an early warning sign of financial stress. * Razek and Hosch, ibid., p.411. 123 Office of New York State Comptroller Indicator 9: Current Liabilities Current Liabilities Gross Revenues Negative Trend: Percentage increasing over time Indicator 10: Intergovernmental Revenues Intergovernmental Revenues Gross Revenues Negative Trend: Percentage increasing over time. Indicator 11: Economic Assistance Costs Economic Assistance Cost Gross Expenditures Negative Trend: Percentage increasing over time. 124 Office of New York State Comptroller Indicator 12: Public Safety Public Safety Cost Gross Expenditures Negative Trend: Percentage increasing over time Indicator 13: Tax Limit Exhausted Tax Levy Tax Limit Negative Trend: Percentage increasing over time The tax limit is the maximum amount of taxes that can be levied based upon some statutory authority. Indicator 14: Debt Limit Exhausted Total Debt Subject to Limit Debt Limit Negative Trend: Percentage increasing over time Debt limit is the maximum amount of debt that can be issued under applicable statutory authority. Compare this ratio with indicators 3 and 7. 125 Some Exercises © D.L. Crumbley 1. You have the following data for a city in the southwest. Calculate the quick ratio. Is this ratio favorable or unfavorable? Current Liabilities $28 million Cash $27 million Investments (current) $36 million Accounts Receivables $12 million Due from other funds $2.5 million 2. You have the following information about a mid-west city. Calculate the ratios of fund balance to revenues and determine if they are favorable or unfavorable. General Fund $62 million Unreserved Fund $54 million General Fund Revenues $401 million 3. You determine the following data about a local government in the southeast. Determine the ratios of unreserved fund balance and reserved fund balance to total revenues. Are these ratios favorable? Revenues from Property Taxes $36 million Unreserved Fund Balance $5 million Reserved Fund Balance $3.5 million 4. Assume the following facts about a local government. Determine the Tax Limit Exhausted and the Debt Limit Exhausted ratios. Tax Limit $11 million Debt Limit $13 million Tax Levy $8.5 million Total Debt subject to Limit $9 million 5. Assume that Debt Service Expenditures is $16.2 million and Total Revenues is $70.1 million. Calculate the Debt Service/total revenue ratio. Is the ratio favorable? 126 Some Exercises © D.L. Crumbley 6. Determine if the following situations are negative indicators of the financial health of a government unit. a. Cash and investments divided by current liabilities ratio is decreasing over several years. b. Current liabilities divided by total revenues ratio is decreasing. c. Fixed costs divided by total expenditures ratio is increasing. d. Real Property Taxes Receivables divided by Real Property Tax Revenue ratio is increasing over time. e. Debt Service expenditures as a percentage of revenues is greater than 25%. f. Debt Service Expenditures divided by Gross Expenditures ratio is decreasing over time. g. Gross Revenues – Gross Expenditures : Decreasing over time. Gross Expenditures h. The debt service expenditures as a percentage of revenues is 25% or larger. i. A fund balance is greater than 10% of revenues. j. Unreserved fund balance divided by gross expenditures ratio is decreasing over time. k. The quick ratio of a large state government is 2.2 to 1. l. Long-Term Debt divided by population ratio is decreasing over time. m.Current Liabilities divided by Gross Revenues ratio is increasing over time. n. Tax Levy divided by Tax Limit ratio is decreasing over time. 127 Exercise Answers © D.L. Crumbley Favorable 128 Exercise Answers © D.L. Crumbley 6. Determine if the following situations are negative indicators of the financial health of a government unit. a. Cash and investments divided by current liabilities ratio is decreasing over several years. Negative b. Current liabilities divided by total revenues ratio is decreasing. Positive c. Fixed costs divided by total expenditures ratio is increasing. Negative d. Real Property Taxes Receivables divided by Real Property Tax Revenue ratio is increasing over time. Negative e. Debt Service expenditures as a percentage of revenues is greater than 25%. Negative f. Debt Service Expenditures divided by Gross Expenditures ratio is decreasing over time. Positive g. Gross Revenues – Gross Expenditures : Decreasing over time. Gross Expenditures Negative h. The debt service expenditures as a percentage of revenues is 25% or larger. Negative i. A fund balance is greater than 10% of revenues. Favorable j. Unreserved fund balance divided by gross expenditures ratio is decreasing over time. Negative k. The quick ratio of a large state government is 2.2 to 1. Favorable l. Long-Term Debt divided by population ratio is decreasing over time. Favorable m.Current Liabilities divided by Gross Revenues ratio is increasing over time. Negative n. Tax Levy divided by Tax Limit ratio is decreasing over time. Favorable 129 Acquisition/Payment Cycle From 62 standard audit procedures, external and internal auditors judged these 20 procedures to be more efficient is detecting fraud in the acquisition and payment cycle (in descending order). • Examine bank reconciliation and observe whether they are prepared monthly by an employee who is independent of recording cash disbursement or custody of cash. • Examine the supporting documentation such as vendor’s invoices, purchase orders, and receiving reports before signing of checks by an authorized persons. • Examine the purchase requisitions, purchase orders, receiving reports, and vendors’ invoices which are attached to the vouchers for existence, propriety, reasonableness and authenticity. •Examine internal controls to verify the cash disbursement are recorded for goods actually rendered to the company. •Discuss with personnel and observe the segregation of duties between accounts payable and custody of signed checks for adequacy. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 204-205 130 Acquisition/Payment Cycle (Contd.) • Confirm inventories in public warehouse and on consignment. •Examine internal controls to insure the vendor’s invoices, purchase orders, and receiving reports are matched and approved for payment. • Examine internal controls for the following documents: vendor’s invoices, receiving reports, purchase orders, and receiving reports. • Trace a sample of acquisitions transactions by comparing the recorded transactions in the purchase journal with the vendor’s invoices, purchase requisitions, purchase orders, and receiving reports. • Establish whether any unrecorded vendors’ invoices or unrecorded checks exist. • Examine the internal control to verify the proper approvals of purchase requisitions and purchase orders. • Reconciled recorded cash disbursement with disbursements on bank statements. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 204-205 131 Acquisition/Payment Cycle (Contd.) • Discover related party transactions. • Examine the internal control to verify the approvals of payments on supporting documents at the time that checks are signed. • Discuss with personnel and observe the procedures of examining the supporting documentation before the signing of checks by an authorized person. • Examine canceled checks for authorized signatures, proper endorsements, and cancellation by the bank. • Account for the numerical sequence of prenumbered documents (purchase orders, checks, receiving reports, and vouchers). • Trace a sample of cash payment transactions. • Trace resolution of major discrepancy reports. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 204-205 132 Sales/Collection Cycle These 10 audit procedures were judged as being more effective for detecting fraud in the sales and collection cycle (in descending order) • Observe the proper and appropriate segregation of duties. • Review monthly bank reconciliation and observe independent reconciliation of bank accounts. • Investigate the difference between accounts receivable confirmation and customer account receivable balances in the subsidiary ledger and describe all these exceptions, errors, irregularities, and disputes. • Review sales journal, general ledger, cash receipts journal, accounts receivable subsidiary ledger, and accounts receivable trial balance for large or unusual amounts. • Verify accounts receivable balance by mailing positive confirmations. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 209 133 Sales/Collection Cycle (Contd.) • Examine internal controls to verify that each cash receipts and credit sales transactions are properly recorded in the accounts receivable subsidiary ledger. • Examine subsequent cash receipts and the credit file on all accounts over 120 days and evaluate whether the receivable are collectible. • Compare dates of deposits with dates in the cash receipts journal and the prelisting cash receipts. • Examine copies of invoices for supporting the bills of lading and customers’ orders. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 209 134 Inventory/Warehouse Cycle These 14 standard audit procedures were judged by external and internal auditors as being more effective for detecting fraud in the inventory and warehousing cycle 9in descending order): • Discover related party transactions. • Follow up exceptions to make sure they are resolved. • Review major adjustments for propriety. • Review inventory count procedures: a. Accounting for items in transit (in and out); b. Comparison of counts with inventory records; and c. Reconciliation of difference between counts and inventory records. • Review adequacy of physical security for the entire inventory. • Confirm inventories in public warehouse. • Review procedures for receiving, inspecting, and storing incoming items and for shipments out of the warehouses. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic 135 Accounting, Vol. 4, 2003, p. 206-207 Inventory/Warehouse Cycle (Contd.) • Trace shipments to sales records, inventory records, and bill of lading (shipping documents). • Determine if access to inventory area is limited to approval personnel. • Observe the physical count of all location. • Recount a sample of client’s counts to make sure the recorded counts are accurate on the tags (also check descriptions and unit of count, such as dozen or gross) • Trace inventory listed in the schedule to inventory tags and the auditor’s recorded counts for existence, descriptions, and quantity. • Trace shipments to sales journal. • Perform compilation tests to insure that inventory listing schedules agrees with the physical inventory counts. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic 136 Accounting, Vol. 4, 2003, p. 206-207. Payroll/Personnel Cycle These 12 audit procedures were judged the more effective for detecting fraud in the payroll and personnel cycle (in descending order): • Sample terminated employees and confirm that they are not included on subsequent payrolls and confirm propriety of termination payments. • Observe the actual distribution of payroll checks to the employees. • Observe the duties of employees being performed to insure that separation of duties between personnel, timekeeping, journalizing payroll transactions, posting payroll transactions, and payroll disbursement exists. • Examine internal controls to verify that hiring, pay rates, payroll deductions, and terminations are authorized by the personnel department. • Sample personnel files and physically observe the presence of personnel in the work place. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic 137 Accounting, Vol. 4, 2003, p. 208. Payroll/Personnel Cycle (Contd.) • Examine internal control over payroll records to verify that payroll transactions are properly authorized. • Discover related party transactions. • Review the files of new hires for appropriate approvals, pay rates, and dates of accession. • Review the payroll journal, general ledger, and employee individual pay records for large or unusual amounts. • Examine internal controls to verify that unclaimed payroll checks are secured in a vault or safe with restricted access. • Examine internal controls to verify that employee time cards and job order work tickets are reconciled. Glen D. Moyes and C. Richard Baker, “Auditors’ Beliefs About the Fraud Detection Effectiveness of Standard Audit Procedures,” Journal of Forensic Accounting, Vol. 4, 2003, p. 208. 138 © D.L. Crumbley Exercises 1. 2. 3. 4. 5. You receive a tip on the company’s hot line that there has been some fraud in the collections area. What five audit steps would you suggest using in order to find the fraud? During a brainstorming session, a suggestion is made that the most likelihood of fraud in a particular division is in the area of acquisition and payment cycle. Outline five audit steps to help find any potential fraud. While auditing a company you notice an employee in payroll who is living beyond his means (e.g., clothes, automobiles, housing). His wife does not work. Suggest six audit steps to help satisfy you there is no fraud in the payroll and personnel cycle. An anonymous e-mail is sent to an internal auditor that there is fraud in the inventory/ warehousing cycle. Suggest some appropriate audit steps. What is meant by the hockey stick pattern? 139 © D.L. Crumbley 140 © D.L. Crumbley The End Is Here 141