Rogue Trading
How to successfully manage this risk
Informational presentation for our clients
February 2008
*connectedthinking
Strictly private and confidential
PwC
Contents
•
Point of view
•
Brief history
•
Some messages highlighted by recent events
•
SocGen—a recent rogue trading incident
•
Regulatory response to date
•
Financial Institution response
•
Firm qualifications
•
Appendix
– A sample of current control frameworks
– Lessons learned
– FINRA Regulatory Notice 08-18: Unauthorized Proprietary Trading
Point of view
• Rogue trading is common—On any given day, it is possible for traders to operate outside of the established rules of an
institution. The vast majority do not get caught. In fact, many are profitable as a result of their rogue trading, but they have
nonetheless not followed the rules and put the institution at risk by their actions. A few begin to lose money, are caught and
dismissed quietly. A much smaller group loses large amounts of money before they are caught. These are the ones that
make the headlines.
• “Tone at the top” is key—Recent examples of large losses from unauthorized trading emphasizes the need for additional
and consistent focus by management and boards on creating the proper culture, sound risk management practices and the
functioning of robust end-to-end controls.
• The risk profile of financial institutions has increased—Development of derivatives and growing sophistication of
electronic trading strategies has increased the risk profile of financial institutions.
• Rogue trading cannot be completely prevented—It has been a problem since the beginning of organized trading, but it
can be managed in an acceptable manner similar to other types of risks. It is very difficult to design preventive controls
absent real-time monitoring, which is under discussion at a number of institutions.
• Most fraudulent behavior is caught by the detective controls in place—Large failures tend to occur when controls are
not operating effectively.
• Emphasis should be placed on improving execution of controls—Most organizations have already implemented
controls over unauthorized trading.
• Understanding the history of large frauds is an important component of your risk mitigation strategy—This includes
scenarios known in the market and scenarios that your organization has experienced or may be susceptible to based on
your business.
• Management should make a practice of investigating performance outliers, positive and negative—Performance far
above goals is a risk indicator.
• Carefully calibrate your response—Improperly calibrated response (both from a review and implementation perspective)
can be counterproductive to a firm’s business and cost structure without appreciably reducing risk in the business. We see
a number of institutions potentially heading down this path.
Rogue trading: The root causes and how to protect your institution
2
PricewaterhouseCoopers
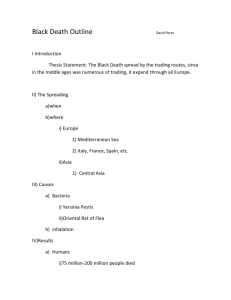
Brief history
Some historical patterns in the most recent well-known frauds are instructive (note: these patterns tend to exist at
some level in the smaller un-reported frauds that we have seen in our client base):
• Frauds occurred over a long period of time in
businesses where large positions are carried in the
course of normal business (mostly derivatives areas).
Terrible Traders
The writedown Societe Generale is attributing to one trader’s bad
bets dwarfs previous banks’ troubles.
• Frauds were all front office individuals (as opposed to
multiple persons) with knowledge and access to the
middle and back office systems and/or processes.
Corporate losses attributed to trades by:
Jerome Kerviel, SocGen (2008)
• Red flags were either dismissed, ignored or undetected
(e.g., lack of mandatory vacation policy/lack of
enforcement, working excessively outside trading hours
and operational and risk management irregularities).
• Structural issues existed, such as lack of segregation of
duties and proper oversight.
$7.16 billion
$6.6 billion
Brian Hunter, Amaranth (2006)
Chen Jiulin, China Aviation Oil (2004)
John Rusnak, Allied Irish Bank (2002)
Yasuo Hamanaka, Sumitomo (1996)
Nick Leeson, Barings Bank (1995)
Toshihide Iguchi, Daiwa (1995)
Juan Pablo Davila, Codelco (1994)
$550 million
$691 million
$2.6 billion
$1.3 billion
$1.1 billion
$170 million
Note: Amounts are converted to U.S. dollars at date reported.
Source: WSJ research
Rogue trading: The root causes and how to protect your institution
3
PricewaterhouseCoopers
Some messages highlighted by recent frauds
Some messages from these disasters include:
• It doesn’t take just complex derivatives to get an
institution into trouble
• It is vital to have an expert, robust and probing risk
management function that is capable of understanding,
identifying and measuring all key risks
• The size of the operations is not the issue—small
operations can create large losses
• People and cultural aspects are key
• Technological advances mean that the possibility of
real-time monitoring and surveillance are being
considered
• Very basic controls can fail and end to end reviews of
risk management and front, middle and back offices
must be undertaken regularly
• There should be direct supervision of traders and
unacceptable behaviors should be identified and
addressed
• Remuneration should be related to profit and levels of
risk taken
• Policies around taking an annual leave of at least a two
week period should be in place and enforced
• There should be clear accountability—who “owns” the
risk and who is accountable for implementing the risk
management framework
• It is important to heed and follow-up internal and
external warning signs
• Rapid, decisive action coupled with a good
communication strategy is key to effectively managing
the crisis
Rogue trading: The root causes and how to protect your institution
4
PricewaterhouseCoopers
SocGen—a recent rogue trading incident
It is early, but some facts and patterns appear to be emerging. Key facts derived from public sources include:
• $7.2 billion trading loss, the largest in history, was
committed by a 31-year old junior trader in the firm’s
Paris headquarters who had joined SocGen in 2000.
He was not a senior trader (annual salary is reportedly
€100,000) as in some of the other frauds. He moved to
the trading floor from the risk control group in 2006.
• Risk control specialists first discovered the suspicious
trades when investigating an outside trading partner of
the bank, whose account showed unusually high
finance levels. The client, when asked by the bank
about the account’s finances, denied knowing of it. The
full extent of the fraud was known within a day or two.
• His role was to hedge exposures using futures on
European stock-market indexes, including Euro Stoxx
50 ($50 billion daily volume), Germany’s DAX Index
and France’s CAC-40.
• The trader does not appear to have profited from the
fraudulent trades and his motivations are unclear.
• It has been reported that such trading raised
supervisory/risk management suspicions in the past,
• By the end of December, the positions were
but that the trader had successfully addressed any
significantly in the money, but became unprofitable after
questions/suspicions.
the market turmoil occurred at the beginning of 2008.
Rogue trading: The root causes and how to protect your institution
5
PricewaterhouseCoopers
SocGen—a recent rogue trading incident
According to the London Times, an independent report to SocGen’s Board includes the following information:
• SocGen missed 75 alerts between June 2006 and
January 2007 on the activities of rogue trader Jerome
Kerviel (JK).
• According to JK, by Christmas he was in profit by €1.4
billion but his activities were discovered on January 8,
fully identified by January 18 and SocGen was forced
to secretly unwind the positions between January 21
and 23 in falling markets, taking it to a €4.9 billion loss.
• Risk control procedures were followed correctly, but
compliance officers rarely went beyond routine checks
and did not inform managers of anomalies, even when
large sums were concerned. “No initiative was taken to
check JK’s assertions and corrections he suggested,
even when they lacked plausibility. . . When the
hierarchy was alerted, they did not respond”.
• The red flags that should have alerted bosses to the
rogue trades included:
- A trade with a maturity date that fell on a Saturday
- Bets without identified counterparties
- Trades with counterparties within SocGen itself
- Trades that exceeded the limits of counterparties
- Missing broker names and large increases in
broker fees
• The panel supported JK’s claim that he acted alone
and that he did not profit personally from the trades.
• The investigation found that JK started building up nonauthorized trading positions in 2005 and 2006 for small
amounts but the positions he took grew in size from
March 2007 onwards.
Rogue trading: The root causes and how to protect your institution
• There were also differences of up to €1.1 billion during
reconciliations of JK's trading books with SocGen's
online derivatives broker. The panel found seven false
emails sent by JK that attempted to explain his trading
and counterparties.
6
PricewaterhouseCoopers
SocGen—a recent rogue trading incident
Some of the conclusions derived from public sources include:
• Large speculative positions were concealed by equal and opposite fictitious trades, thus concealing the MTM effect
and market risk exposure.
• Unauthorized trades were possibly booked across a large number of either dormant or "dummy" accounts thus
were not necessarily monitored on a regular basis.
• As exchanges impose daily margining on all participants, this raises significant questions about SocGen's margin
process.
• The trader possibly entered into transactions with multiple large counterparties thus staying within PSE limits and
possibly benefiting from cross-product netting for margin.
• Massive open positions would have been rolled-forward to avoid settlements.
• The trader may have used cancels and/or amendments on the fictitious trades to maintain the real trades within
limits.
• In anticipation of periodic reviews by Risk Control, the trader may have used book-entry transfers to move the
massive real positions between accounts.
• The trader most likely had access to both front and back systems through potential ID/password theft and/or
sharing or continued access from his previous role in Risk Control that should have been terminated. Such access
could have enabled manipulation of credit, market risk and trade-size controls.
• Trader most likely did not take any vacation during this period and frequently worked late into the night or on
weekends.
• It remains possible, despite SocGen’s management’s declaration otherwise, that collusion with either external or
internal parties were involved. At a minimum, friendships established during years in risk management were
maintained and used to obtain information.
Rogue trading: The root causes and how to protect your institution
7
PricewaterhouseCoopers
Regulatory response to date
• Regulatory response to this issue is in the early days:
– SEC sent a letter to the major investment banks with a February 8th response date. Most firms are outlining in
broad terms their internal post-mortems and ongoing programs to manage this risk.
– The banking regulators have responded in a less consistent manner, with the OCC and the Fed appearing to be
the most active, posing similar questions as the SEC, however there has been no formal public pronouncements.
– Non-US regulators are also requesting responses to various questions/concerns.
• Regulators are likely to review the measures put in place by financial institutions to manage these risks.
• We believe that they are likely to raise questions regarding previous internal audit findings, review previous rogue
trading situations and to examine the effectiveness of controls as well as understand any projects (active, delayed
or cancelled) impacting these areas. We are advising our clients to be well-prepared to address these and other
questions that are likely to be raised by the regulators in the coming months.
• We also expect regulators to encourage clients to strengthen controls across the board in the trading areas and
execute on previously identified projects to remedy known weaknesses.
Rogue trading: The root causes and how to protect your institution
8
PricewaterhouseCoopers
Financial Institution response
Financial institution sentiments and responses have varied. Here are some key points:
• All clients agree “this could happen” to them and, in fact, has happened to many. They differ in the extent that
they are comfortable that they would be able to detect such activity and limit the losses.
• Senior management and boards are very sensitive regarding the effectiveness of controls and managing the
risk of large losses in this area in the wake of the subprime situation and lack of confidence in the financial system
post-SocGen.
• Most investment and sophisticated money center banks with large proprietary trading businesses appear
to be comfortable with their risk management capabilities and are undertaking their own investigations with
limited outside assistance. Many have had a number of rogue trading incidents over the last several years that
resulted in losses that were not material to the institution.
• Other Financial Institutions are generally less confident in their risk profile and some are seeking external
assistance in reviewing the quality of the control environment and recommending improvements.
• There is a general acknowledgement that improvements could be made in the control and technology
infrastructure and that projects that have either not been funded or fully committed to will be budgeted for and
executed. These programs are generally focused in the areas of automation of trading, risk management and
information security processes and systems.
Rogue trading: The root causes and how to protect your institution
9
PricewaterhouseCoopers
Financial Institution response
Even some of the most sophisticated financial institutions have modified their approaches after
consultation with the firm.
Examples of recent bank responses
Our Advice
Large Investment Bank
US Regional Bank
Global Money Center Bank
Overall
• Focus on front office
• Coverage of front, middle, back
office
• Coverage of front, middle, back
office
• Largely focused on front office
• Risk-based approach to
determining businesses covered
• All desks across the globe
• Leveraging self-assessment
process
• Calibrated according to risk
• Look at previous firm scenarios
• Not included
• Not included
• Not included
• Independent investigation lead
• Internal Audit/Risk Management • Risk Management
• Risk Management
Current Scenarios
• Dummy account review
• Not included
• Included
• Included
• Vacation policy/patterns
• Included
• Included
• Included
• Transfers to front office
• Not included
• Included
• Included
• Computer-savvy traders
• Not included
• Not included
• Not included
• Access rights
• Included
• Included
• Included
• Off-hours work patterns
• Not included
• Unknown
• Included
• High levels of cancels/corrects
• Not included
• Not included
• Included
• Include the treasury area
• Not included
• Not included
• Not included
• Unusual patterns
• Not included
• Not included
• Included
Other
Rogue trading: The root causes and how to protect your institution
10
PricewaterhouseCoopers
Financial Institution response
Risk review must consider a front office threat assessment, plus IT access/entitlements
“Front office” threat assessment
• Risk profile of each business and desk
• Incentives for rogue trading
• Management oversight practices
• Segregation of duties
• Risk management practices
IT access/entitlements
• Knowledge of middle, back office and
risk management processes and
systems
• Information technology capability
• Password strengths, access rights and
authorization
• Intrusion monitoring
• Pattern recognition
In addition to these areas above, poor detective controls plus lax enforcement of existing controls
compounds the risk of large fraud
Rogue trading: The root causes and how to protect your institution
11
PricewaterhouseCoopers
Financial Institution response
We are recommending that a focus on the front office risk profile, behavior and capabilities allows for a targeted
investigation of business practices to assess current risk levels and identify necessary enhancements to fraud
prevention controls.
Specific areas of focus will include:
• Average price accounts
• Syndicate accounts
• Error accounts
• Suspense accounts
• Inappropriate use of brokers (excessive volume to single broker)
• Rolled trades around period-end or trades done away from market prices
• Excessive cancelled and corrected or re-billed trades
• Unverified vendor payments
• Large numbers of client exceptions; cancelled trades, borrow issues, etc.
Ownership for these control objectives and processes span multiple departments across the organization. For
example:
• Entitlements—data owned by business unit, process owned by information security
• Risk monitoring—credit and market risk owned by business unit, operational risk owned and administered by
corporate department
• Fraud risk—detecting is owned by compliance, deterrence is owned by regulatory and audit
Rogue trading: The root causes and how to protect your institution
12
PricewaterhouseCoopers
Financial Institution response
We are also encouraging our clients to look at this issue on an end-to-end basis.
Performance
Management
Risk
Management
Operations
Management
• Incentive compensation of traders
and other front office management
based directly on P&L
• Limited insight into the activities
being executed by front office
personnel
• Performance measurement not
linked to risk profile of trading
account/activities
• Ineffective escalation of incidents
• Control not linked to risk or
performance objectives
• Limited authority to affect
transactional activities
• Operations unable to effectively
inform risk management of issues
• Controls needed not effectively
put in place by operations
• Controls not designed to
implement risk management
needs
• Front office regulatory and
compliance incentive based on
P&L
• Identification of risks not dynamic
or complete
Rogue trading: The root causes and how to protect your institution
13
• Controls overridden based on
performance
PricewaterhouseCoopers
Financial Institution response
The most sophisticated institutions are beginning to examine the current trading model in greater depth:
• Excessive profits are rarely examined—making money that is significantly above plan or market conditions may
not be good news and is a risk factor.
• Problems often start in the budget cycle—traders pressured to “make my numbers”, which may be unrealistic
and may lead to risky behavior. Hitting targets = my bonus.
• Trading managers are rarely trained in fraud detection or rogue trading behaviors—continual and consistent
hands-on interaction and management is critical.
• Functions within trading departments are often blurred—poor differentiation between market making and
dealer functions versus proprietary risk taking.
• Compensation models often give traders a “free option”—gains are rewarded with bonuses, but there is no
give back for losses.
• Trading managers trade rather than manage—maintaining a proprietary account focuses managers on their
account rather than oversight and involvement.
• Many institutions lack a true long term incentive model:
- Annual compensation cycle often leads to boom/bust results.
- Trading managers/departments need to understand and challenge how “their” capital is being allocated in the
market.
• Traders view internal risk management group as the bad cop—they can be a valuable tool in proactive risk
decision making.
Rogue trading: The root causes and how to protect your institution
14
PricewaterhouseCoopers
Financial Institution response
Financial institutions are beginning to consider the types of efforts they need to undertake to better manage these
risks, including:
• Better enforcement of existing controls
• Implementation of quick fixes where possible, sometimes in anticipation of longer term automation or control
improvement efforts
• Adjustment of internal audit and risk management team focus and plans
• Funding/acceleration of selected projects in the following areas:
– Information security
– Automation around trading
– Controls
– Risk management
– Monitoring technology
• Discussion of real time monitoring in some firms
Rogue trading: The root causes and how to protect your institution
15
PricewaterhouseCoopers
Firm qualifications
The firm has an outstanding track record of working with clients in investigating and responding to rogue trading
activities:
• Current response assistance at SocGen and several other institutions
• Provided our points of view and advice to a number of leading firms
• Historical investigation assistance regarding a number of prior trading scandals
• Numerous trading risk and control reviews with leading clients
• Deep implementation experience in key areas of client focus (e.g., IT risk, security, policy, governance, etc.)
• Publication a number of years ago of Generally Accepted Risk Principles (“GARP”) which includes a
comprehensive view of trading risk management and controls
Rogue trading: The root causes and how to protect your institution
16
PricewaterhouseCoopers
Appendix
A sample of current control frameworks
• How various banks have developed their control frameworks in response to
risk issues identified and past fraudulent activity
Lessons learned
• Some lessons learned by functional area
Regulatory Notice: 08-18 Unauthorized Proprietary Trading
• Sound practices for preventing and detecting unauthorized proprietary
trading
A sample of current control frameworks: Global Investment Bank A
Despite Bank A’s established controls throughout its operations, fraudulent activity resulting in approximately
$30MM in losses was identified between 2002 and 2007.
Summary (issues identified and
fraudulent activity found)
General
Front Office
• Plans of supervision
• Risk limits for select desks
• List of authorized brokers by trade and
Middle Office
• Loss of liquidity and disagreements about
• Segregation of duties between
• Market risk limit monitoring (tracking
Back Office
A review of established controls resulted in the
following issues identified in Q3 and Q4 2007:
Bank A manages risk through internal controls across all levels
• Margin process, monitoring of
model assumptions triggered an above
average level of margin disputes
• A backlog of unconfirmed trades
• Correlation exceeded market risk limits of both
European and US desks
• Price verification: significant growth of
unverified instruments as a percentage of total
inventory
Rogue trading: The root causes and how to protect your institution
• System entitlement reviews
front, middle and back offices
• Periodic password resets
• Mandatory vacation policy
• Trader mandates outlining approved
instruments and currencies
• Counterparty Review, including
monitoring
of market risk data quality)
• Counterparty credit monitoring
• Model validation process, including
monthly input review
disputed margins
• Confirmations
• Cash break monitoring
• Settlement reconciliation
18
KYC/AML
•
•
•
•
•
P&L Triggers
Off-market trade monitoring
Daily, monthly P&L analysis
Trade reconciliation
Account maintenance and monitoring
• Late trade booking/monitoring
• Tracking of trade modifications and
amendments
• Tracking of back dated adjustments
• Account set-up
PricewaterhouseCoopers
A sample of current control frameworks: Global Investment Bank B
Bank B has the controls listed below in place for each line of business. Potential control gaps have been identified,
though these controls have yet to be reviewed and issues have yet to be identified.
Summary(issues
(issuesidentified
identifiedand
and
Summary
fraudulentactivity
activityfound)
found)
fraudulent
General
Front Office
Middle Office
Back Office
Bank B has outlined the controls to be
reviewed and has created three metrics on
which to judge control effectiveness:
assessment of design, manual involvement
and effectiveness. In addition, Bank B has
identified the potential control gaps to
which they believe the Bank’s businesses
could be exposed. These include:
• Forging of books and records
• Password sharing
• System access entitlements conflicts
• Breach of limits
• Bypass of limit detection controls
• Creation of fictitious portfolios, dummy
counterparties, or “pending” trades
• Remote trading without supervision or
systems of record
• Fictitious trades/cancel and corrects
• Pending/unsettled transactions
• Confirmation suppression capabilities
• Segregation of duties over cash
movements
Bank B manages risk through internal controls across all levels
Rogue trading: The root causes and how to protect your institution
• Segregation of duties, between
• Mandatory 2 week vacation policy
front, middle and back offices
• Access and entitlements controls
• Information walls
• Change management controls
• Adequate system access/entitlements to • Reconciliations of risk systems, P&L
funds wiring systems
and balance sheet
• Trader mandates outlining approved
products and limits
• Risk limits and systematic feeds for
monitoring
• Counterparty/portfolio—set-up
• Price verification processes
controls
• Trade activities review—cancels and
corrects, as of, forward settlements,
off-premises
•
•
•
•
Straight-through processing
Counterparty confirmation controls
Internal trade confirmations
Manual journal entry control
requiring 4 people
19
• Internal/external system threat and
vulnerability controls
• Clearing and settlement controls
• Adequate Standard Settlements
Instructions Controls (SSI)
PricewaterhouseCoopers
A sample of current control frameworks: Global Investment Bank C
Bank C has the controls listed below in place for each line of business in both the Investment Bank and other
wholesale business units. These controls have yet to be reviewed and issues have yet to be identified.
Summary (issues identified and
fraudulent activity found)
General
• Mandatory vacation policy
• Identification and follow-up on any
regulatory inquiries
• Identification of high risk access
• Password sharing review
• Review of transfers between front
and back office and associated
access rights
conflicts and users with this access
Back Office
Middle Office
There is both a front office focused work plan
and an operations, finance, and technology
focused work plan. The reviews are to be
conducted across the Bank’s various lines of
business (i.e., rates, commodities, equities)
within the Investment Bank and the other
wholesale business units (i.e., Asset
Management, Treasury Services).
Front Office
Bank C has outlined the controls to be
reviewed and plans to document the results of
the review, the issues and gaps identified, and
the action plan to remediate each issue.
Bank C manages risk through internal controls across all levels
Rogue trading: The root causes and how to protect your institution
• Risk Limits by Desk
• Review of trade activity by Desk Head
for appropriateness
• Trade Activity Review—
cancellations and amendments and
forward-dated trades
• Verification of P&L/positions sign-off
by appropriate person
• Confirmations review
• Affirmations review
• Month-end close/reversing trade
• Review of client valuations in
dispute with external counterparties
• Collateral movement review
• Review of dummy, blocked and
offline books not feeding to risk or G/L
• Review of cash wash items
entry reviews
• Nostro reviews
20
PricewaterhouseCoopers
A Comparison of Controls: Global Investment Bank D
Bank D is evaluating operational risk management’s self-assessment process to determine if significant control gaps
are appropriately identified. In addition, Bank D has mapped out what took place at SocGen relative to their control
objectives.
Summary
General
Front Office
Back Office
Middle Office
Bank D is in the process of conducting end-toend self assessments of its trading desks. The
Bank’s internal audit function will work to
provide feedback, review and testing of the
self-assessments. In addition, the Bank has an
independent firm doing external validation of its
assessment process. A report containing
details of the SocGen event, effectiveness of
the evaluation process and current state
findings will be provided to the Board upon
completion.
Bank D manages risk through internal controls across all levels
Rogue trading: The root causes and how to protect your institution
• Change management controls
• IT business continuity infrastructure
• Risk data classification to ensure to
allow identification of highly sensitive
data
• Risk Limits by Desk, including
counterparty, country, and product
exposures
• Confidential information
management and training
• Isolation of business units with
material non-public information
• Segregation of duties
• Due diligence requirements set by
Desk to ensure internal approvals,
conflicts of interest, and clients are
appropriate
• Limit monitoring
• Price verification processes
• Model validation and back-testing
• Product suitability management
• Client and transaction due diligence
•
•
•
•
• System access restrictions (need to
Transactions management review
Transactions documentation controls
Transactions processing reviews
Limit reporting
21
know basis)
• Reporting of modeled factors
PricewaterhouseCoopers
Lessons learned
A PwC recommended framework for trading and treasury operations.
Risk management strategy
• Risk management
philosophy
Risk measurement reporting
Risk management function
• Risk appetite
• Risk identification
• Risk culture
• Organisation
• Risk assessment
• Role of the Board
• Limits structure
• Risk measurement
• Reporting lines
• Exception reporting
• Roles and responsibilities
• Regulatory reporting
• Skills resources
Overall risk
management framework
Operations, systems and
controls
People and culture
• Robust operations and
• Recruitment and training
controls (front, middle,
back office)
• Transparency
• Integrity and accountability
• Adequate systems
• Reliable information
• Compliance
Communication
• Accounting
• Skills and resources
• Remuneration based on
risk and reward
Rogue trading: The root causes and how to protect your institution
22
PricewaterhouseCoopers
Lessons learned
Risk management strategy
• The Board of Directors must take responsibility for
- Overall culture
- Establishing risk strategy and appetite
- Ensuring that hard side of RM (policies, limits and systems) and soft side (people, culture and incentives)
receive equal attention
- Ensuring that management have mechanisms to identify, measure, capture and report risks
• The Board and its committees should be probing
Risk management function
• Dedicated function that has authority
• Clear lines of responsibility between function and BU
• Adequate skills
• Meaningful and comprehensive limits structure
• Stress testing
Rogue trading: The root causes and how to protect your institution
23
PricewaterhouseCoopers
Lessons learned
People and culture
• Recruitment policies
• Adequate training
• High performance culture, based on integrity and compliance
• Swift penalties for those who don’t comply with policies
• Star performers should not be given special treatment
Operations and systems
• Segregation of duties is a key operational risk control
• Robust operational controls must be in place in front, middle and back offices
• Ensure that the back office groups have real influence over trading activities
• Prices
- Off market prices should be a warning flag
- Systems should capture prices outside a range
- Models from third parties should always be sourced by BO
- Brokers from whom prices are obtained should be rotated
Rogue trading: The root causes and how to protect your institution
24
PricewaterhouseCoopers
Lessons learned
Risk management reporting and controls
• Risk reporting should be comprehensive, yet comprehensible
• No single measure adequately covers all eventualities and satisfies all management requirements
• A range of complementary measures should be used
• The escalation of bad news should be encouraged
• Audit reports should not be “dumbed down” by management. Issue reporting should be multi-dimensional
• All regulatory reports should be shared with the Board
Rogue trading: The root causes and how to protect your institution
25
PricewaterhouseCoopers
Regulatory Notice 08-18: Unauthorized Proprietary Trading
April 2008
Sound Practices for Preventing and Detecting Unauthorized Proprietary Trading
Executive Summary
In the wake of several recent cases involving allegations of unauthorized or “rogue” trading resulting in substantial losses by firms both in the United States and
abroad, many FINRA firms are undertaking comprehensive reviews of their internal controls and risk management systems designed to prevent such trading activity.
FINRA is issuing this Notice to highlight sound practices for firms to consider as they undergo that process. We also remind firms that even profitable unauthorized
trading can result in regulatory exposure if it involves falsification of the firm’s books and records, failures in supervisory control systems, market manipulation or
fraud. Therefore, internal control systems should be designed to address regulatory as well as business and reputational risk.
Questions regarding this Notice may be directed to:
• Laura Gansler, Associate Vice President, Emerging Regulatory Issues, at (202) 728-8275; or
• Rosemarie Fanelli, Surveillance Director, Risk Oversight and Operational Regulation, at (646) 315-8452;
• Kathryn Mahoney, Director, Emerging Regulatory Issues, at (212) 858-4101.
Background and Discussion
The risks associated with unauthorized proprietary trading by “rogue” traders are not new, and most firms that allow traders to commit the firms’ capital already have
policies and procedures in place designed to prevent unauthorized trading. In 1999, the SEC, NYSE and NASD issued a Joint Regulatory Notice 08-18 Statement on
Broker-Dealer Risk Management Practices that summarized weak and strong risk management practices identified through a survey of mid-sized and large firms.1 In
it, the regulators concluded that senior management must play a significant role in the adoption and maintenance of a comprehensive system of internal controls and
risk management systems, and that those controls and systems must be adequately funded, independent of revenue-generating activities, and updated as changes
in technology, the firm’s business activities or other circumstances warranted.
Since then, many firms have refined and strengthened their internal controls around unauthorized trading. However, recent events highlight the importance of
routinely reassessing the adequacy and effectiveness of those systems, particularly in light of the increasingly global nature of the financial services industry, the
highly competitive trading environment and the complexity of many of the products being traded. In particular, the immediacy required as a result of pervasive
electronic trading and market linkages has increased pressure on some firms to relax internal controls that might arguably affect a trader’s competitive advantage in
the short run, but protect the firm from undue risk in the long term.
Unauthorized trading under any circumstances, but especially in the case of proprietary trading, can pose significant risk from a business perspective, and it can
create serious regulatory risk as well, even when the trading generates profits for the firm. Substantial losses can affect financial viability and several recent incidents
appear to raise other regulatory concerns, including falsification of the firm’s books and records, lapses in supervisory controls and fraud. Moreover, it is sometimes
difficult to tell from early red flags whether suspicious trading activity is generating profits or losses; vigilance against regulatory exposure as opposed to simply
focusing on business risk can help protect the firm against both. Therefore, a firm’s internal controls around unauthorized proprietary trading should be designed to
deter and detect all unauthorized trading by the firm’s employees.2 This deterrence is important even when the firm profits from that trading; firms that “look the other
way” or reward profitable unauthorized trading are creating incentives for this prohibited behavior and the potential for future risk of loss.
Rogue trading: The root causes and how to protect your institution
26
PricewaterhouseCoopers
Regulatory Notice 08-18: Unauthorized Proprietary Trading
April 2008
Sound Practices
To assist firms in the process of reviewing and, where necessary, modifying, their current internal controls against unauthorized trading, we have recently solicited
input from a range of firms regarding their internal controls, as well as the preliminary results of internal reviews. We are publishing those practices now with the
expectation that doing so will help other firms as they undergo their own review process. While FINRA believes that these practices are worthy of consideration, we
understand that their relevance and feasibility will vary depending on a firm’s size and business model. We also note that this is not an exhaustive list, and is not
intended to create a safe harbor from regulatory exposure or to discourage firms from completing their own comprehensive internal audits.
Mandatory Vacation Policies
An increasing number of broker-dealers have identified “sensitive” jobs, and adopted mandatory policies requiring employees in those positions, including traders, to
be away from the office for a minimum amount of time, typically ten consecutive trading days. During that time away, the employee is barred from having physical or
electronic access to the firm, its facilities, or systems. The theory behind this policy, which has been common in the banking industry, is that if an employee has
engaged in unauthorized activity and is concealing it, the activity will likely be exposed in the firm’s trade reconciliation process within that time, because the
employee is not able to continue the concealment while away from the firm and its systems.
A mandatory vacation policy must be enforced in order to be effective. In at least one recent well-publicized case, the firm had such a policy, but the trader involved
had not taken the full, mandatory, consecutive vacation in several years. Exemptions should not be granted except in unusual circumstances and repeated requests
for exemptions should be considered a red flag warranting additional monitoring. Firms also should assure that their systems support blocking employees on
mandatory vacation from accessing firm systems.
A mandatory vacation policy may not be feasible or reasonable for all firms. However, we urge firms to consider it as part of their risk management procedures. If a
firm determines not to adopt such a policy, it should consider other methods of identifying and reviewing the trading activity of traders who have not taken an
extended vacation in the past year.
Heightened Scrutiny of Red Flags
As firms review their internal controls, they should pay attention to whether they are both adequately mining available trade data for red flags and following up on
those red flags where appropriate. Among other things, firms should monitor, and, when necessary, conduct heightened scrutiny of:
• Trading limit breaches. At least one firm surveyed recently has implemented a tool that allows for monitoring of limit breaches by a trading book or individual trades
in real-time, and can be set to generate alerts based on a range of parameters, including the notional value of a trade, share size (net/gross position), amount of
orders or traders per day and total dollar value per day.
• Unrealized profit and loss (P&L) on unsettled transactions. Trading desk managers and financial control managers should pay careful attention to sizeable amounts
of unrealized P&L and should understand the nature of the transactions creating these amounts.
• Unusual patterns of cancellations and corrections, particularly those involving multiple cancellations or corrections by the same trader or involving the same
counter-party. Certain firms prohibit a front-office trader or salesperson from entering cancels and corrects into the trading system and limit the entry of these
transactions to mid-office (e.g., those involved in risk management) or back-office (e.g., those involved in settlement services) personnel.
Rogue trading: The root causes and how to protect your institution
27
PricewaterhouseCoopers
Regulatory Notice 08-18: Unauthorized Proprietary Trading
April 2008
• Transactions in which confirmation and settlement do not occur on a timely basis, or where settlement is outside of normal cycles.
• Reports of aged unresolved reconciling items and aged outstanding confirmations.
• Reports of P&L that exceed a certain de minimis amount by traders who are supposed to be flat, or unusually large one-day P&L reports.
• The details underlying a trader’s Value at Risk (VaR), including the long and short positions, on a daily or intra-day basis, as appropriate. Firms should also
consider other risks associated with a trader’s positions, such as liquidity risk, the adequacy of hedges and the risks associated with imperfect hedges. This
includes understanding and reviewing the valuation of all positions, particularly positions in exotic instruments or instruments that have little or no market.
• Repeated or unusual requests by a trader to relax existing controls, including position or P&L limits.
• Trading in products that are outside of a trader’s known expertise, without prior approval.
• Any other unusual or significant differences between a trader’s account positions and the account activity, such as might be detected by comparison of gross
and/or net position to the cash flows of positions; i.e., margin/collateral calls to and from counterparties to the trades.
• A pattern of aged fails to deliver for long or short sales.
Whether these data points are reviewed manually, or with the use of automated surveillance tools, or some combination, a firm’s controls should not just note
deviations from normal trading patterns as red flags that might signal proprietary business risk, but as signals of possible regulatory risk as well. And, to the extent
that firms use automated surveillance tools to identify such items, their internal control systems should include adequate and routine maintenance and testing of
those systems.
Protection of Systems and Risk Management Information
In some cases, rogue traders have been able to falsify a firm’s books and records to conceal illicit trading activity due to lapses in password security and other
systems protections. Firms should make certain that each employee’s access to systems is limited strictly to what is appropriate for the employee’s function within
the firm. This control should not be limited to traders; it should be in place for any employee whose role includes access to trading systems. If an employee’s function
changes within the firm, the firm should make sure that the employee’s access changes accordingly. For example, if an employee moves from the back office to a
trading desk, that employee’s access should be changed to reflect his or her new role, and access to the back-office functions should be revoked. Firms should also
make sure that access is suspended during any mandatory vacation period and cancelled promptly if the employee leaves the firm.
Firms also should protect information about surveillance or monitoring systems and procedures that might help employees circumvent those systems. For example,
knowledge that the firm divides responsibility for reviewing certain trade monitoring functions by product type might help a trader who is creating fictitious trades to
avoid detection by creating trades involving different products, so that the trades would not all be reviewed by the same personnel. In at least one recent case, a
trader’s intimate knowledge of back-office procedures and risk management procedures, including what would—and what would not—trigger heightened scrutiny,
may have allowed him to avoid detection for a much longer period than he otherwise might have. Therefore, firms should limit knowledge about the details of their
risk management procedures and systems to the extent possible and consider modifying them in response to personnel changes, such as a back office employee
becoming a trader. Firms also should consider whether there are appropriate mechanisms in place to review all activity of a given trader.
Rogue trading: The root causes and how to protect your institution
28
PricewaterhouseCoopers
Regulatory Notice 08-18: Unauthorized Proprietary Trading
April 2008
Firms may want to consider more than a single password to allow access to certain systems. More sophisticated systems require three-factor authentication before
access is allowed, including not only a password but also a security card or other I.D. such as a token ring, and a unique identifier such as a fingerprint. Firms need
to weigh both the inconvenience and the cost of these additional security measures in determining which controls are appropriate.
Supervision and Accountability
Certain financial services companies have established matrix management structures such that employees may have both direct and dotted line reporting to multiple
managers. While matrix management may make sense for an organization, it is important for employees to understand who they report to and what they are held
accountable for in their day-to-day job responsibilities. Correspondingly, both the dotted line and the direct manager must have a clear sense of who is responsible
for each aspect of the business. It is critical that responsibility for supervision of each aspect of the business be allocated to a specific manager and that these
managers have frequent communications to understand their respective businesses. Documenting these supervisory responsibilities in writing is recommended.
Intercompany Transactions
Many FINRA firms are part of larger, complex financial services organizations. The FINRA member firm generally conducts a large number of intercompany
transactions with its affiliates. Often the basic controls that are in place for third parties, including controls around credit risk and market risk, are waived for affiliated
transactions. In light of the recent cases of unauthorized trading, firms may want to reevaluate whether certain third-party controls that limit their exposure would be
appropriate for affiliated transactions. Further, reconciliations of intercompany transactions and balances should be performed on a regular basis.
Compliance Culture
As recent events have demonstrated, even the most rigorous internal controls and risk management procedures can fail if they are not effectively enforced and the
effectiveness of that enforcement is directly related to the “tone at the top.” A corporate culture that marginalizes the individuals or departments responsible for trade
reconciliation and risk management will undermine the effectiveness of even the most elaborate policies and procedures. In reviewing the adequacy of their internal
controls around unauthorized proprietary trading by individual traders, firms should pay attention to any systemic or cultural dynamics that may undermine the
effectiveness of those systems. For example:
• Do mid- and back-office functions have sufficient independence, clout and profile within the organization? To whom do they report?
• Are mid- and back-office personnel adequately trained and encouraged to raise issues about suspicious activity, even if it involves successful traders or activity
that is generating profits for the firm, or doesn’t technically violate any limits?
• If operations, compliance or internal audit personnel receive a questionable or inadequate response by a trader, are they encouraged to challenge such a response
and/or raise the issue to their supervisors where appropriate?
• If the firm operates in a global context, do its internal controls take into account any cultural differences that might discourage adequate internal oversight or
reporting? For example, anonymous reporting might be appropriate in certain environments.
Rogue trading: The root causes and how to protect your institution
29
PricewaterhouseCoopers
Regulatory Notice 08-18: Unauthorized Proprietary Trading
April 2008
• Do traders who have incurred losses have incentives to disclose them and limit the damage because they understand that the failure to disclose will be considered
an egregious violation of the firm’s policies and procedures and dealt with accordingly, or are they encouraged, even implicitly, to incur more risk in order to avoid
disclosure?
• Are internal control functions adequately funded, and are those who perform them adequately compensated, in relation to the role that they are asked to perform
within the firm?
Conclusion
As firms review their internal controls around unauthorized trading in the wake of recent incidents, FINRA urges them to consider the practices described above, and
to rigorously examine the broader compliance culture within which those controls are enforced. FINRA also reminds firms of the importance of ensuring that program
areas tasked with detecting and preventing unauthorized trading possess sufficient independence, clout and funding, especially during challenging market conditions.
Endnotes
1 See NASD NTM99-92 (November 1999) and NYSE Information Memo 99-42 (September 1999).
2 FINRA member firms that are also members of the NYSE are subject to incorporated Rules 342.21 and 351(e), which require firms to review proprietary, employee
and employee related trading in NYSE-listed securities and related financial instruments, and to conduct “internal investigations” of trades that may violate securities
laws and rules prohibiting insider trading and manipulative and deceptive devices. Members and member organizations are further required to file with the Exchange
reports relating to such internal investigations pursuant to Rule 351(e).
Rogue trading: The root causes and how to protect your institution
30
PricewaterhouseCoopers
www.pwc.com
The information contained in this document is for general guidance on matters of interest only. The application and impact of laws can vary widely based on the specific facts involved. Given the
changing nature of laws, rules and regulations, there may be omissions or inaccuracies in information contained in this document. This document is provided with the understanding that the
authors and publishers are not herein engaged in rendering legal, accounting, tax, or other professional advice and services. It should not be used as a substitute for consultation with
professional accounting, tax, legal or other competent advisers. Before making any decision or taking any action, you should consult a PricewaterhouseCoopers professional.
Although we believe that the information contained in this document has been obtained from reliable sources, PricewaterhouseCoopers is not responsible for any errors or omissions, or for the
results obtained from the use of this information. All information in this document is provided "as is", with no guarantee of completeness, accuracy, timeliness or of the results obtained from the
use of this information, and without warranty of any kind, express or implied, including, but not limited to warranties of performance, merchantability and fitness for a particular purpose. In no
event will PricewaterhouseCoopers, its related partnerships or corporations, or the partners, principals, agents or employees thereof be liable to you or anyone else for any decision made or
action taken in reliance on the information in this document or for any consequential, special or similar damages, even if advised of the possibility of such damages.
© 2008 PricewaterhouseCoopers LLP. All rights reserved. “PricewaterhouseCoopers” refers to PricewaterhouseCoopers LLP or, as the context requires,
the PricewaterhouseCoopers global network or other member firms of the network, each of which is a separate and independent legal entity.
*connectedthinking is a trademark of PricewaterhouseCoopers LLP (US).
PwC