From CPA exam content specification
advertisement
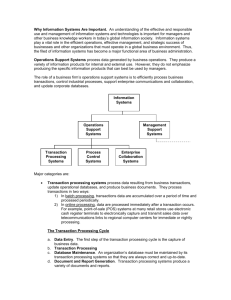
From Certified Public Accountant (CPA) exam content specification http://www.cpa-exam.org/download/CSOs%20for%20revised%20CPA%20Exam.pdf Auditing and Attestation I. Plan the engagement, evaluate the prospective client and engagement, decide whether to accept or continue the client and the engagement, and enter into an agreement with the client (22%–28%) J. Consider other planning matters 5. Electronic evidence 6. Risks of auditing around the computer II. Consider internal control in both manual and computerized environments (12%–18%) A. Obtain an understanding of business processes and information flows B. Identify controls that might be effective in preventing or detecting misstatements C. Document an understanding of internal control D. Consider limitations of internal control Business Environment and Concepts IV. Information technology (IT) implications in the business environment (22%– 28%) A. Role of business information systems 1. Reporting concepts and systems 2. Transaction processing systems 3. Management reporting systems 4. Risks B. Roles and responsibilities within the IT function 1. Roles and responsibilities of database/network/Web administrators, computer operators, librarians, systems programmers and applications programmers 2. Appropriate segregation of duties C. IT fundamentals 1. Hardware and software, networks, and data structure, analysis, and application, including operating systems, security, file organization, types of data files, and database management systems 2. Systems operation, including transaction processing modes, such as batch, on-line, real-time, and distributed processing, and application processing phases, such as data capture; edit routines; master file maintenance; reporting, accounting, control, and management; query, audit trail, and ad hoc reports; and transaction flow D. Disaster recovery and business continuity, including data backup and data recovery procedures, alternate processing facilities (hot sites), and threats and risk management E. Financial statement and business implications of electronic commerce, including electronic fund transfers, point of sale transactions, internetbased transactions and electronic data interchange From Certified Management Accountant (CMA) content specification outline http://www.imanet.org/ima/docs/2200/2127.pdf Part I - Business Analysis C. Internal Controls (15% - Level A) 1. Risk assessment and controls a. Internal control structure and management philosophy b. Internal control policies for safeguarding and assurance cc.. IInntteerrnnaall ccoonnttrrooll rriisskk dd.. U U..SS.. FFoorreeiiggnn C Coorrrruupptt PPrraaccttiicceess A Acctt iinntteerrnnaall ccoonnttrrooll rreeqquuiirreem meennttss.. 22.. IInntteerrnnaall aauuddiittiinngg aa.. R Reessppoonnssiibbiilliittyy aanndd aauutthhoorriittyy ooff tthhee iinntteerrnnaall aauuddiitt ffuunnccttiioonn bb.. TTyyppeess ooff aauuddiittss ccoonndduucctteedd bbyy iinntteerrnnaall aauuddiittoorrss cc.. IInntteerrnnaall aauuddiitt aassssiissttaannccee pprroovviiddeedd ttoo m maannaaggeem meenntt 3. Systems controls and security measures a. General accounting system controls b. Application and transaction controls c. Network controls d. Flowcharting to assess controls e. Backup controls f. Disaster recovery procedures Part 2 – Management Accounting and Reporting C. Information Management (15% - Level A) 1. Nature and purpose of an information system a. Business information systems b. Transaction processing systems c. Management information systems 2. Systems development and design a. Systems development life cycle b. Cost benefit analysis 3. Technology of information systems a. Data communications, networks, and client/server systems b. Database management systems c. Decision support systems d. Artificial intelligence and expert systems e. Spreadsheets f. Internet and intranet 4. Electronic commerce a. Electronic data interchange b. Business-to-business c. Other e-commerce technologies 5. Integrated enterprise-wide data model a. Enterprise resource planning (ERP) systems b. Data warehousing and data mining from Certified Internal Auditor (CIA) exam content specification http://www.theiia.org/iia/index.cfm?doc_id=4206 Part III - Business Analysis and Information Technology E. Information Technology (IT) 1. Control frameworks (e.g., eSAC, COBIT) 2. Data and network communications/connections (e.g., LAN, VAN, and WAN) 3. Electronic funds transfer (EFT) 4. e-Commerce 5. Electronic data interchange (EDI) 6. Functional areas of IT operations (e.g., data center operations) 7. Encryption 8. Information protection (e.g. viruses, privacy) 9. Evaluate investment in IT (cost of ownership) 10. Enterprise-wide resource planning (ERP) software (e.g., SAP R/3) 11. Operating systems 12. Application development 13. Voice communications 14. Contingency planning 15. Systems security (e.g. firewalls, access control) 16. Databases 17. Software licensing 18. Web infrastructure