Campus help desk gives tech service with a smile
advertisement

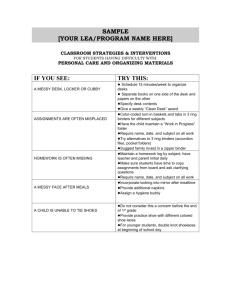
1 News from around UIT 4 NODE February 2014 Some of the help desk staff (from left): Daniel James, Kaysha Rytting, Christian Merrill, Steven Maloy, Angela McKee and Scott Lloyd Campus help desk gives tech service with a smile Staff takes pride in solving problems day in and day out Happy people don’t call help desks. But if Scott Lloyd has his way, people are happy by the end of the call. For the past 11 years, Lloyd has overseen the University of Utah’s campus help desk and various other call-center services. He understands that when someone calls the 16-person desk they expect a problem to be fixed quickly. But there’s more to it than dispensing technical advice. “We look for job applicants with a customer-service focus first, and then technology experience,” Lloyd says. “A lot of times we can teach them the technology. Customer service — that’s what we look really heavily on.” The help desk, situated alongside the University’s hospital service desk in 650 Komas, handled just shy of 40,000 incoming calls last year. Four full-time staff members and a dozen student employees answer calls, troubleshoot users’ IT issues, and open trouble tickets and work orders. On average, the caller was speaking with a live agent within 22 to pg. 5 Hawkins ge ts ne w post 11-year UIT veteran puts 35 years of experience to work as assistant director in Solution Planning and Design group. .03 More secure passwords There’s a handy way to create stronger passwords — and even the average user can remember them. .04 February 2014 Don’t let security reach an end-­‐of-­‐life stage, too Governance decisions At a glance Support Ser vices Ja n. 15 • Project priorities were discussed, and a list of the top 20 was compiled for consideration. Unified Communications items will be co-overseen with the Infrastructure Portfolio. Infrastructure Ja n. 15 • Peter Panos presented historical growth of UIT metrics and costs, showing a deficit of funding. Caprice Post updated the group on the voice RFI to streamline phone services. Mike Ekstrom reported on the external network review. The Teaching and Learning Portfolio will decide whether to adopt a campuswide virtual desktop infrastructure. Research Ja n. 14 • Chris Gregg discussed the capacity and performance needs of Genomics researchers. Steve Corbató shared the prospects for federal research funding. Downtown Data Center space-allocation decisions will be made by this group. Operational IT Comm . De c. 4 • The OITC reviewed many UIT resources to determine whether they were common resources or should become a fee-for-service offering. Decisions were made on most of the resources reviewed. The body considered suggestions for altering the membership of portfolios. Find po rtfo lio me m ber sh ip lists, ag en das and s um mar ies at c io .u tah.e du . All good things must come to an end, the saying goes. While there is certainly room to debate whether Windows XP falls into the “good” category, there’s no denying the second part. Come April, Microsoft will roll out the final patches and security updates and officially put XP to pasture. For IT professionals, there can be no long goodbye, no wishing for “just one more day.” This is a date for which attackers have long been waiting, and it is our job to make sure that when it comes to our users and our network, the wait has been in vain. “The very first month that Microsoft releases security updates for supported versions of Windows, attackers will reverse-engineer those updates, find the vulnerabilities and test Windows XP to see if it shares [them],” wrote Tim Rains, director of Microsoft’s Trustworthy Computing group. “If it does, attackers will attempt to develop exploit code that can take advantage of those vulnerabilities on Windows XP. Since a security Dan Bowden update will never become available for Windows Chief Information XP to address these vulnerabilities, Windows XP Security Officer will essentially have a zero-day vulnerability forever.” Any machine on the University of Utah’s network still using Windows XP after the end-of-support date must be considered a vulnerability. With systems containing valuable research data; private student, staff, and faculty records; and federally protected health information, there is no margin for error. The Information Security team is working to inventory all Windows XP devices connected to the network. These will be listed as high-risk devices, and an appropriate plan for replacing them or securing them will be implemented. The ISO team understands there may be some difficulty in transitioning older machines and systems away from XP, and there may be some instances where that just isn’t possible. My team and I are here to help. If you are aware of any physical machines or VMs on campus still running Windows XP, please take the necessary steps to mitigate risk and migrate them to supported operating systems. If you believe your circumstances do not lend themselves to migrating, please contact Colby Gray with the Information Security Office at colby.gray@utah.edu or 5871179 so that we may assist you in protecting your data from the inevitable threats to come. We owe it to ourselves, our users, our departments, and the University of Utah to ensure we provide not just a highly functional network, but a safe one as well. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 2 1 2 3 February 2014 Hawkins named SPD associate director Marv Hawkins has spent nearly 35 years helping customers bridge the gulf between their dreams and their reality with technology. With just shy of 11 years of experience at the University of Utah as an integration analyst and product manager in Administrative Computing Services and University Support Services, along with more than two decades of similar work at Salt Lake Community College, Hawkins was a natural fit to take the wheel as an associate director in Solution Planning and Design (SPD). He is working with other associate directors to determine how to handle requests for University Support Services. The Solution Planning and Design team will handle requests that are not addressed by the help desk, knowledge articles or the service catalog. Hawkins will make sure an initial analysis happens for business case development. If the scope of the request is large enough to warrant further approvals through the governance process, consultants will partner with the requester to provide governance with information to help make decisions. “We’ll actually be the advocate for that business case or that customer through the governance process if it needs to go to governance,” he said. “But we’ll do a lot of advising to set customer expectations to match up the business and technology roadmaps.” SPD director Paula Millington added that “the solution consultants and solution designers in the planning phase need to support the customer, but we hope the business cases and design packages for our ‘build’ and ‘run’ teams will really help add value to our solutions.” “As we create the plan-build-run Marv Hawkins model, we’re finding that very few educational institutions use that model,” said Hawkins. “In industry that’s a pretty common thing and we think it will be valuable for UIT, but we can’t look to others to see how they have actually put it into practice. Industry seems to have a lot more resources to throw at planning, and it will be a challenge for us to start small and perfect our craft.” Millington sees Hawkins offering valuable insight as that effort unfolds. “He has a proven track record in scoping and managing projects, gathering requirements, working ticket backlogs down from hundreds to tens, calming worried stakeholders and being able to provide just enough input to get a solution to engineering. We won’t have the resources to create tomes of business cases or design documents, so judging when less will be just as effective is really important. Marv is masterful at that.” Hawkins — who enjoys home improvement, cooking, and singing in his church praise group in his spare time — hopes to lay the groundwork for other UIT departments to embrace planning and design. “We’re starting with USS, building a model focused on application planning and design. We want to learn from our experience in a way that would eventually allow us to plan for all UIT service units. So if there’s a Teaching and Learning Technologies issue we could put it through the same kind of process.” Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 3 February 2014 Have your users been compromised? ‘Have I Been Pwned’ can answer that Hardly a week goes by without another major security breach being revealed by yet another big-name retailer, application or website. As massive data dumps continue to appear with sobering regularity, it is difficult to keep track of whose account credentials are in jeopardy. To make the task easier, haveibeenpwned.com makes it possible to find out whether a username or email has been compromised in any of several breaches. Simply plug it into the text box and hit enter to find out whether the email or username is among any of the nine breaches currently catalogued by Have I Been Pwned (see the photo below). To make things easier for system administrators, the site now offers full domain searches to uncover how many users may have been compromised. There are four ways to verify you are a domain admin: by email, by meta tag, by file upload, and by TXT record. Once you have proved you are a domain authority, you can check that domain name against the databases and warn your users that their accounts are at risk. Easily remember many secure passwords There may not be much you can do to prevent the bad guys from stealing your information, but there is a lot you can do to prevent them from guessing it. Researchers at Carnegie Mellon University suggest the easiest way to create complex, yet memorable passwords is to use the personaction-object method. The user creates a visual in his or her mind by equating a person with an unexpected action and object. CMU’s cited example was Bill Gates swallowing a bicycle. Passwords are then derived using some scheme based on that visual, such as BiGaswa2c. The user could then keep a picture of Bill Gates somewhere to act as a reminder for the cues. Choosing different images or schemes for each account will make it easier to maintain security even if one is compromised. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 4 4 2 3 February 2014 Help desk (continued from pg. 1) 30 seconds. If the wait time reaches even a minute, Lloyd says, people’s patience wears thin. “They just say, ‘Oh, I’ll call back later.’” Steven Maloy — a Tier 2 support agent who handles calls escalated from the initial Tier 1 agents — knows all too well how frustration and impatience can mix to create a perception that works against the organization. “People get upset because it’s not done immediately,” Maloy says. “Whereas if you look at what we do compared to what the national averages are, we answer our phones faster, we get stuff resolved quicker, a higher percentage of things get handled with a first-call resolution than the national average. In just about every aspect, we’re better than the national average.” The help desk keeps meticulous statistics on incoming calls, first-call resolutions, average calls per agent per shift, speed to answer, abandoned calls, and the like. It also collects data from surveys sent out after each ticket closes, asking Top 10 caller issues 1. Help desk information (firsttime login, call transfer, general university information) 2. Account management (account locks) 3. Network and wireless issues 4. Phone repair 5. Umail issues and configuration 6. Desktop and server support 7. System and application support 8. DNS, VPN and department network requests 9. OSL support 10. Email phishing attacks people to rate the quality of help they received and their overall experience. Lloyd meets with Maloy and Beth Sallay, a Tier 2 agent with more than 13 years of help desk experience, weekly to review the stats and ensure issues are documented and resolved. They also pinpoint problem areas to help other areas solve issues. As UIT adopts a new service- and incident-management platform, Lloyd is excited about the ability to track the desk’s progress in even more ways. “It’s got a lot more reporting; it’s faster. I think it’s going to be a lot more useful for my group,” he says. It will also allow customers to track their requests through the process in a more transparent way, hopefully alleviating some frustrations within the current system. Incoming calls The help desk handled about 40,000 incoming phone calls in 2013. Here’s a look at how many calls came in each month. A shifting user base Like every other area of information technology, the support function has had to adapt to the sea change of users’ abilities, devices, and expectations. Where a decade ago dozens of students would line up to get their desktop towers configured to connect to the network, now people are mostly concerned with connecting peripheral devices. Desktops gave way to laptops, which have ceded to tablets and smartphones. “Students receive all of their papers from their professors online, they gain access to all the library resources online,” Lloyd says. “They have to be connected to it. It’s critical to them.” Sallay says the help desk agents are friendly, and they can relate to users’ problems because they have been there themselves at times. “Whatever they’ve done, I have probably done something way worse that caused more problems,” she says. Maloy has been with the help desk for more than five years, starting as a first-line agent before moving to the second tier about a year ago. The U graduate has a degree in business information systems and has been at the school off and on since 1992 (in fact, his dad was an accountant in continuing education from 1980 until he retired a few years ago). “It’s rewarding to be able to help people,” Maloy says. “They call in See Help desk, pg. 6 Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 5 6 7 5 1 2 3 February 2014 From the inside: A student agent’s perspective B y Ch ristian M e rrill My experience on the campus help desk has been both enlightening and educational. Our goal is first and foremost to take care of our callers, even if we have no idea where they are coming from. This means that when we receive a call that we do everything we can to figure out their problem and find the best solution as quickly and efficiently as we can. It’s immensely satisfying to receive a call from someone who is stressed, burnt out, and just wants their problem alleviated, get them where they need to be, and have them end the call happy and relieved. As a student, we know how these problems go. We’ve been there, and it’s not fun. In this position, we can help and we can relate. It’s a valuable set of skills. What makes this possible are the exceptional employees with whom I work. Help desk (continued from pg. 5) needing help, and we’re able to take care of them and get them on their way. They’re able to get back to their classes or their work or whatever they need to do. They’re appreciative of it, and you feel good being able to do that. And it offers a challenge. All day long you’re being handed problem after problem.” The help desk agents have access to the same knowledge database as is available on the UIT site, but also have some internal Steve, Scott, Cody, Beth, Angela, and Chris have been here awhile and are all excellent mentors and friends. It’s not uncommon for an IT help desk to receive complicated, confusing, or vague issues, but it is uncommon to receive the kind of support we do. All of the above will stop what they are doing to help me find a solution, teach me how I can do things better, and never make me feel stupid or inadequate. resources that go beyond those available to the public. Another change is that students coming in are even more acquainted with technology than their predecessors. They are less likely to need assistance for some of the more basic issues than in the past, so a good deal of the support resources is focused on faculty and staff who have issues with calendar sync, phone repairs, server support, or DNS configurations. In other jobs you worry that you will get in trouble for not knowing everything, or will be talked down to and dealt with condescendingly. On the help desk they just laugh and help you figure it out. They aren’t rude, impatient, or derogatory about it in any way. They treat you like an equal and they treat you like a human being. It makes a stressful job a fun learning environment where I get to help people. At the end of the day, I work an occasionally stressful IT job. It’s my job to help people who need assistance — who are stressed, frustrated, and just want a solution, even if I wasn’t the right man to call. What makes it worth it is getting the person on the other side of the phone to breathe a sigh of relief and smile, because they know that we’re doing our best to take care of them, because it’s what we would want, too. A culture of service The help desk is staffed 24 hours a day thanks to a partnership with the Downtown Data Center to cover off-peak hours. During particularly busy periods, such as the beginning of the school year, the average agent handles nearly 50 calls in an eighthour shift. That’s a tough job, and one that requires extensive training to get See Help desk, pg. 7 Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 6 8 1 2 February 2014 Help desk (continued from pg. 6) right. Sallay, who has a bachelor’s in communications and a master’s in instruction design and educational technology, has worked hard to get much of the basic training put into Canvas courses. “Turnover is the most challenging issue right now,” she says. “That’s why I did the online training. We’re training all the time.” Maloy works closely with new student hires for about two weeks, teaching them the ins and outs of good service and solid technical help. It’s not for everyone. “Some won’t last two weeks,” Maloy says. “I think those who drop out within two weeks or shortly thereafter are the ones who have an expectation coming in that they’re going to be kind of a glorified data-entry person just transcribing the phone call into a ticket and they’re done. When we start going through the training and they start to see really how much we do here at the help desk, they kind of get overwhelmed with it.” Sallay appreciates the flexibility of the student workers, who help cover parts of a shift that might be understaffed otherwise. The ones who come out of training tend to stay about seven months in the 19-hour-a-week job, though a few will stay as much as two years. “For some it depends on their schoolwork,” Lloyd says. “Some will balance it out, and others will say, ‘You know what, I just have to focus on this schoolwork full-time.’ It just depends on what field of study they’re in.” But he is proud of the work the students do and is happy to help bring them along in a professional setting. “They’re working in an area where it will help them build their resume,” he says. “They’re working with a large group that has all sorts of parts and they may never have been able to do that before. We’re pretty well an enterprise application group and a networking group. So they get to see all those pieces and work with those groups, too.” Whether it be a student employee or a frustrated caller, Lloyd wants the same outcome: When someone finishes with the help desk, they are in a better place than when they began. Kudos & Congrats B rian Ha ymore did a wonderful job representing CHPC in discussions and making a wellreceived presentation at the Condo of Condos workshop at NCSA (University of Illinois, Urbana-Champaign). ~Steve Corbató Congrats to Paul B urro ws for working with Pat Hanna to conceptualize a way that requests to USS Portfolio would be handled. Some we will never do; some are no brainers; some need more analysis and scrutiny from the portfolio committee to determine priorities. The concept went to USSP in January and was endorsed with a few suggestions. ~ Paula Millington A big thank you to Micha el Da vis for his exemplary service to his co-workers and clients. He constantly and consistently goes above and beyond his expected job duties. ~ Cindy Hanson Congratulations to Er ic Y oung, student intern in USS / Content & Usability, who just graduated with a Bachelor of Science in Communication! ~ Debbie Rakhsha Thanks to W ayne B radfor d for shepherding CHPC’s unique research computational environment, for handling data with patient health information in compliance with HIPAA regulations and for being a coauthor (with former CHPC director Julio F acell i and other colleagues) on a paper describing this environment that was recently published in the Journal of the American Medical Informatics Association. ~ Steve Corbató Thanks to Jill B rinto n, Ryan Hine s and C ary Lopez for reaching out to deans and chairs to include them in process work analyzing Strategic Scheduling and Course Management. They united stakeholders in a desire to improve academic planning and were able to identify issues and their causes without offending anyone. Their work has been praised by Ruth Watkins and the process work has gathered 287 ideas for improvement. ~ Paula Millington We would like to acknowledge the phenomenal work the C IS Engine ering & O p erat ions group did during the first week of the semester. They are a talented, hard-working team. ~ Trevor Long and Jeff Hassett Thanks to Joe B reen , who spearheaded the development of the third pod of racks for research computing in the Downtown Data Center. ~ Steve Corbató Ma rv Ha wkins did a great job providing accurate and timely information to the USS Portfolio team on projects that are “in flight” and needed to be prioritized. He waded through many disparate priority lists and came up with the top 20 projects. The committee ranked them, and for the first time, the committee delivered a list of priorities to USS. ~ Paula Millington Submit Kudos Email praise for UIT colleagues to scott.sherman@utah.edu. Those recognized will be put into a drawing to win prizes. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 7 2 1 3 February 2014 UIT’s YouTube star marries at Grammys There are very few people who can say they were married by a “queen” with 20,000 in attendance and a television audience of 28.5 million, but UIT’s Spencer Stout is among them. The past few months have been an exciting time for Stout and Dustin Reeser. What started out as a marriage proposal going viral on YouTube has led to interviews with various media outlets, an appearance on the Ellen DeGeneres show, and ultimately a wedding featured live on the Grammy Awards. “I guess the hardest part was trying to keep it quiet,” said Stout, who works in the Solution Planning and Design group. He and Reeser were approached by the Grammys in October while they were looking for wedding venues in California. Initially, they were unsure about being married on television, but after signing a confidentiality agreement and learning the event was the Grammys, they decided to go for it. “We thought, when is this opportunity ever going to happen in our lifetimes?” said Stout. “The stressful part was everything being condensed to six weeks of planning.” They were able to keep it quiet, though, and finally got the call on Christmas Eve making it official. When they arrived a month later to the rehearsal, Stout said he was surprised and happy to find that the other couples to be married were also nice, everyday people. “They were just normal, awesome people of all kinds, colors, shapes, and sizes; it didn’t matter.” At the rehearsal, Stout remembers it being very emotional when Macklemore and Ryan Lewis’s song “Same Love” began. Click here to see Spencer Stout and Dustin Reeser’s proposal video “I had never really listened to the words of the song as closely as I did, and all of us were just in tears. It was just a really emotional, special time.” The day of the wedding was even more powerful. “The energy of that place filled with 20,000 people standing up and cheering, we couldn’t contain it,” said Stout. “You could hear on the third verse when Macklemore started singing, people just started to cheer right away, and that’s when we started to walk out.” Queen Latifah officiated the ceremony, with Macklemore, Mary Lambert and Madonna performing, and 34 couples were married that evening. As the ceremony ended, Stout remembered being congratulated by both Beyonce and Katy Perry as he walked by. It was a night they’re not likely to forget. “It’s been emotional and exhilarating and hard all at the same time,” Stout said. Stout and Reeser are incredibly excited to go on their dream honeymoon to Australia in a few weeks, but first, the couple has decided to host something more intimate back home in Salt Lake City. Since friends and family were unable to attend the Grammys event, they’re planning a ring ceremony where they’ll take time to exchange vows in front of loved ones. And the couple’s rise to fame is still paying off: Betty Who, the artist whose song inspired Stout’s flashmob proposal, will be in attendance and plans to sing at the ceremony. “It’s been a great ride,” said Stout. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 8 1 2 3 February 2014 Have You Seen It? It sort of looks like the laces of a football, doesn’t it? This photo was taken somewhere on campus. If you think you know where, email scott.sherman @utah.edu with your answer. Correct entries will be put in a drawing for free tickets, swag or gift certificates. Courses teach hacking, computer security IT professionals interested in furthering their security skills can do so with two classes being offered by the Technology Education program through Continuing Education. The Certified Ethical Hacker course aims “to equip information security professionals with the knowledge and skills to identify and correct weaknesses that make information systems vulnerable to attack.” Topics include scanning networks; system hacking; trojans and backdoors; viruses and worms; social engineering; denial of service; SQL injection; hacking wireless networks; cryptography; and penetration testing. The $2,599 weeklong class begins Feb. 24. Another course prepares students for the CompTIA Advanced Security Practitioner (CASP) Certification exam. It is expected to be offered again in the future, and teaches students how to set up multiple levels of defense to protect the confidentiality, availability and integrity of a company’s IT assets and information. For information about these courses and other learning opportunities, visit continue.utah.edu. CIO’s ‘five questions’ in EDUCAUSE University of Utah CIO Eric Denna often mentions his “five questions” when discussing why he and other UIT leaders are choosing to take the organization down a certain path. In the latest issue of EDUCAUSE Review, Denna shares a bit about how he arrived at those five questions, and how they can be used to maximum effect for assessing and strategically repositioning technology efforts in any kind of business or institution. The five questions are: 1. Whom do we serve, and what do they (those we intend to serve) want/need/have to do? 2. What services do we provide so that those we serve can do what they want/need/have to do? 3. How do we know we are doing a great job? 4. How do we provide the services? 5. How do we organize? “Often, when I share these questions with others and tell them that this is at the heart of what I do as a CIO, they look at me with a ‘that's it?’ expression,” Denna writes in the article. “I typically respond by saying: ‘Just try to answer the questions for yourself. If you are really brave, have your leadership team answer them, and then share the answers with one another.’ “My experience is that the first time team members answer the five questions and then share the answers with one another, inevitably a very interesting discussion ensues.” You can read the full article on EDUCAUSE’s website, www.educause .edu. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 9 1 2 February 2014 Get Node 4 updates in two new places Follow us on Twitter, and subscribe to the podcast feed on our iTunes U page Do you want to get the latest Node 4 podcast as soon as it becomes available? Now you can by subscribing to the Node 4 channel on iTunes U. Every podcast can be found under the University Information Technology page on the University of Utah’s main iTunes U page. New episodes will automatically download to subscribers’ iTunes accounts. To sign up, visit the Node 4 iTunes U page. Click here to hear the latest Node 4 podcast with Chief Information Security Officer Dan Bowden. Also of interest to information technology professionals at the U are audio recordings of previous IT Professionals meetings, as well as an archive of Mac Managers meetings (which can be found under the J. Willard Marriott Library page in the student computing section). Also, Node 4 can now be found on Twitter, @UITNode4. We’ll send out updates, ask for ideas, post interesting links, and do all that other fun Twitter stuff. Plus we may even give some things away. Follow us! On the agenda February March Thursday, Fe b. 6 Monday, Feb. 17 Tuesday, Mar. 4 Intro duct ion to C HPC• Learn about the resources available at the Center for High Performance Computing, 1-2 p.m., INSCC Auditorium (room 110) Presidents D ay Holida y •The University is closed for this holiday. W ork-in-Progress T alk • Matt Potolsky talks about his project “Secrecy Theory: A Defense of Secrets in an Age of Full Disclosure,” 12-1:30 p.m., Carolyn Tanner Irish Humanities Building, Room 143, free Monday, Fe b. 10 Resea rch Da ta M ana gement , Sha ring and O wner ship• Learn about University policies surrounding data ownership and management responsibilities. 2-4 p.m., HSEB 1750 Thursday, Fe b. 27 Go verning Regula tions for Gr ant s a nd Cont ract s •Learn rules regarding grants and contracts, 2-4 p.m., HSEB 1750, online registration required, free for faculty, staff and students Fr iday, Mar. 7 U IT All-Ha nds M eeting • Refreshments served, starts at 8:30 a.m., Saltair Room, A. Ray Olpin Union Node 4 is a monthly newsletter produced by UIT Strategic Planning and Communication. Contact communications specialist Scott Sherman at scott.sherman@utah.edu for information or to offer feedback and content ideas. Have a story suggestion for Node 4? Email scott.sherman@utah.edu. 10